The document contains information about cryptography tools and commands for OpenSSL including:
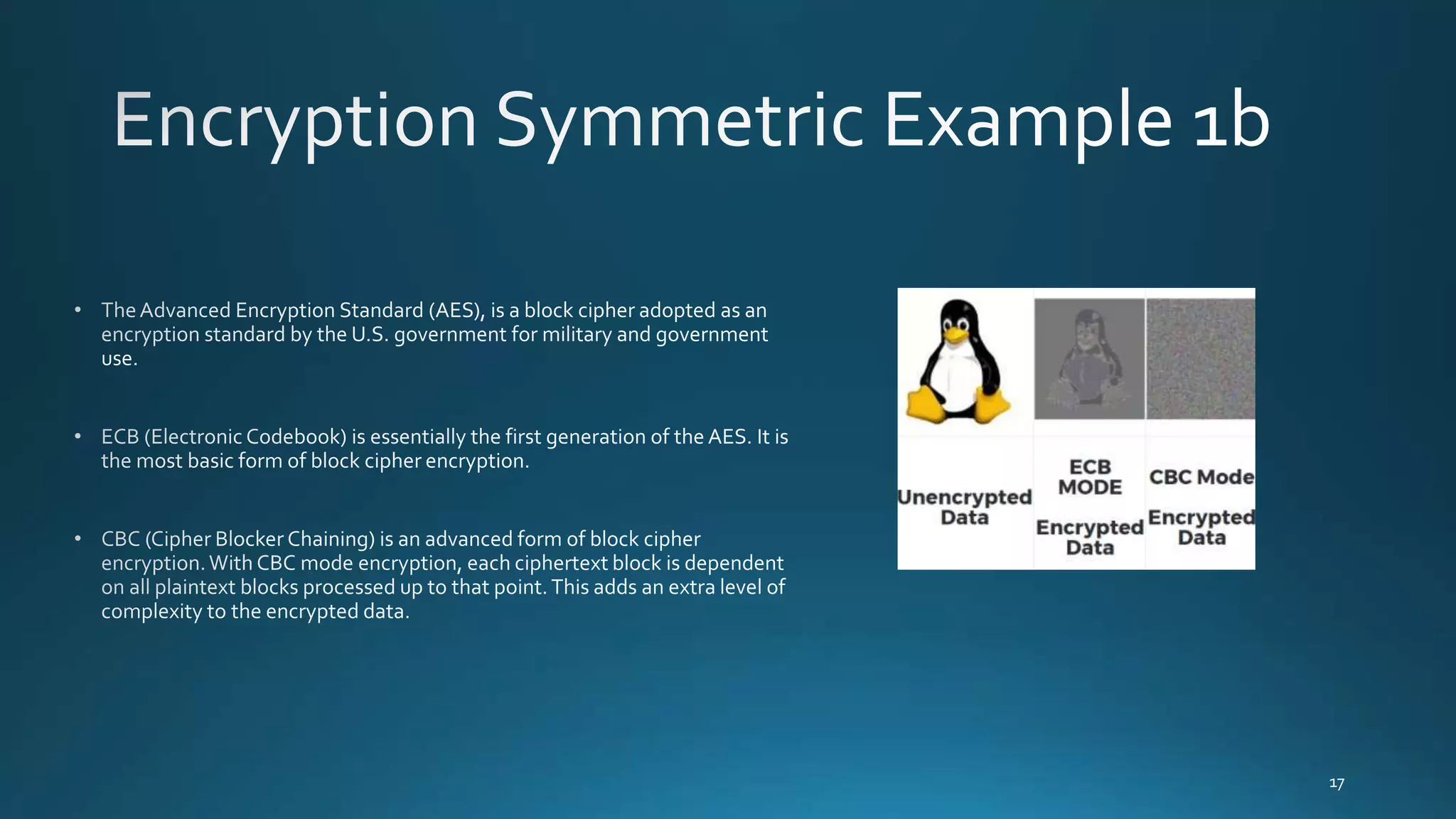
- Links to documentation pages for OpenSSL, SHA-2, RSA, and AES algorithms.
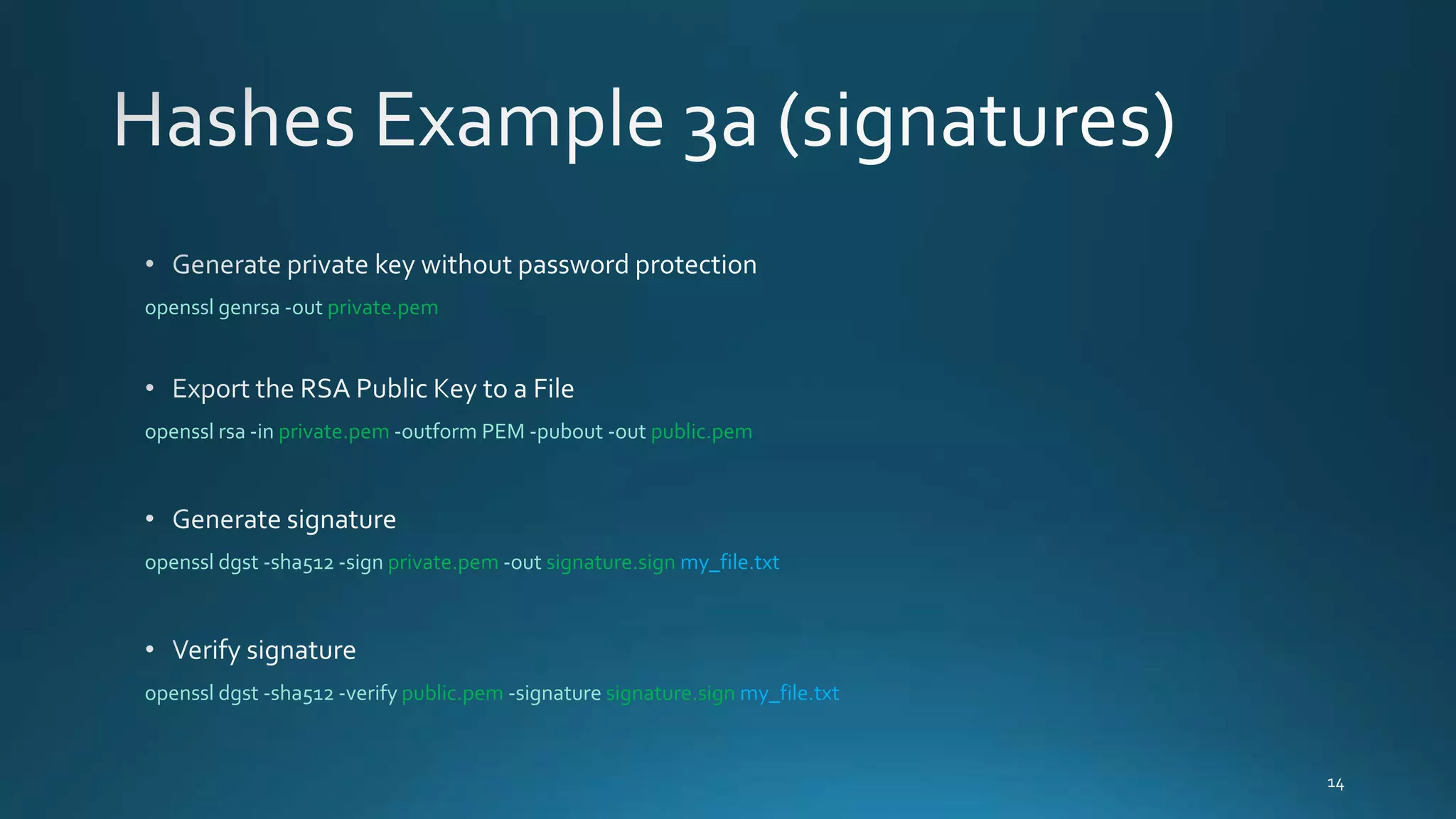
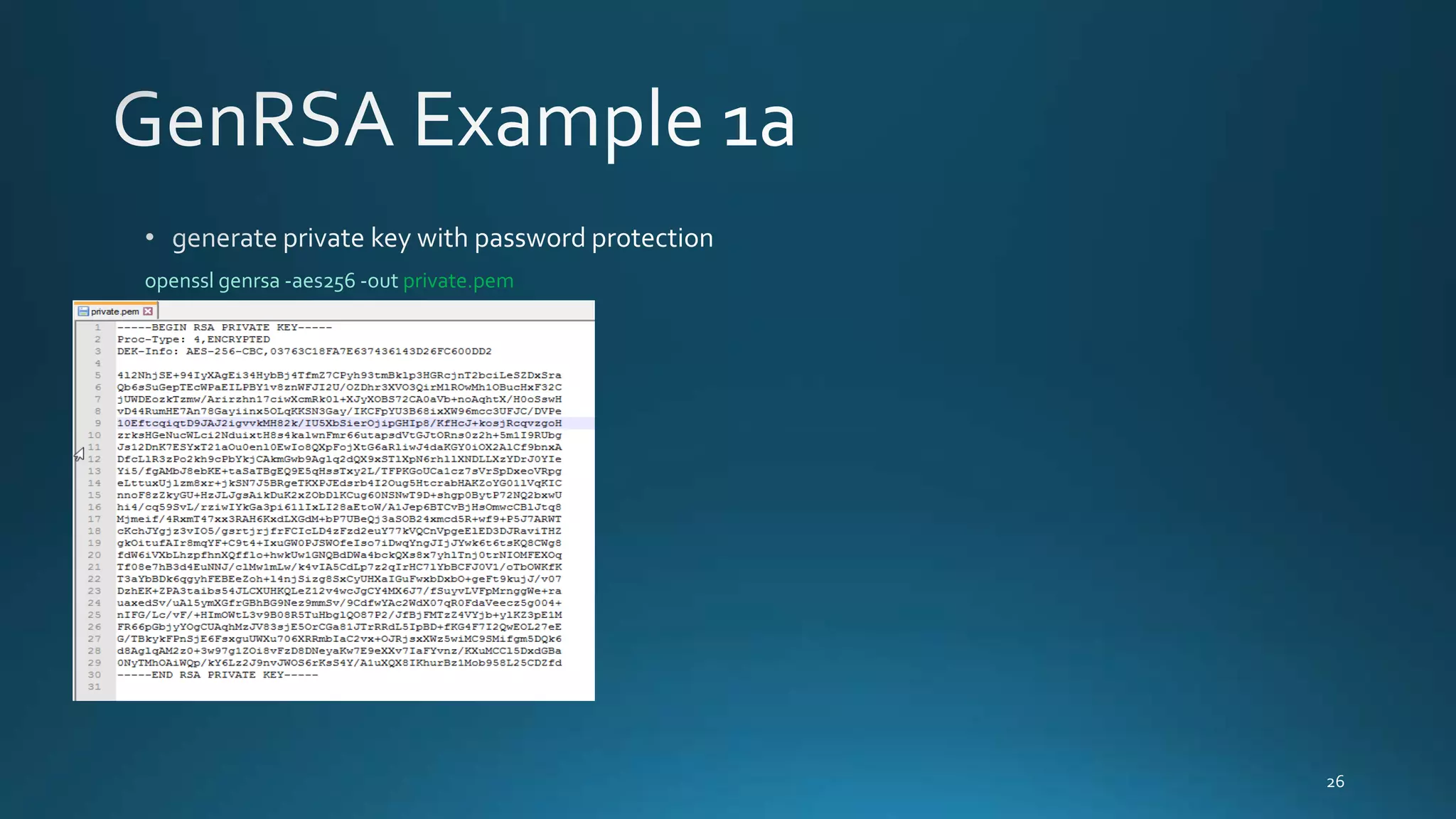
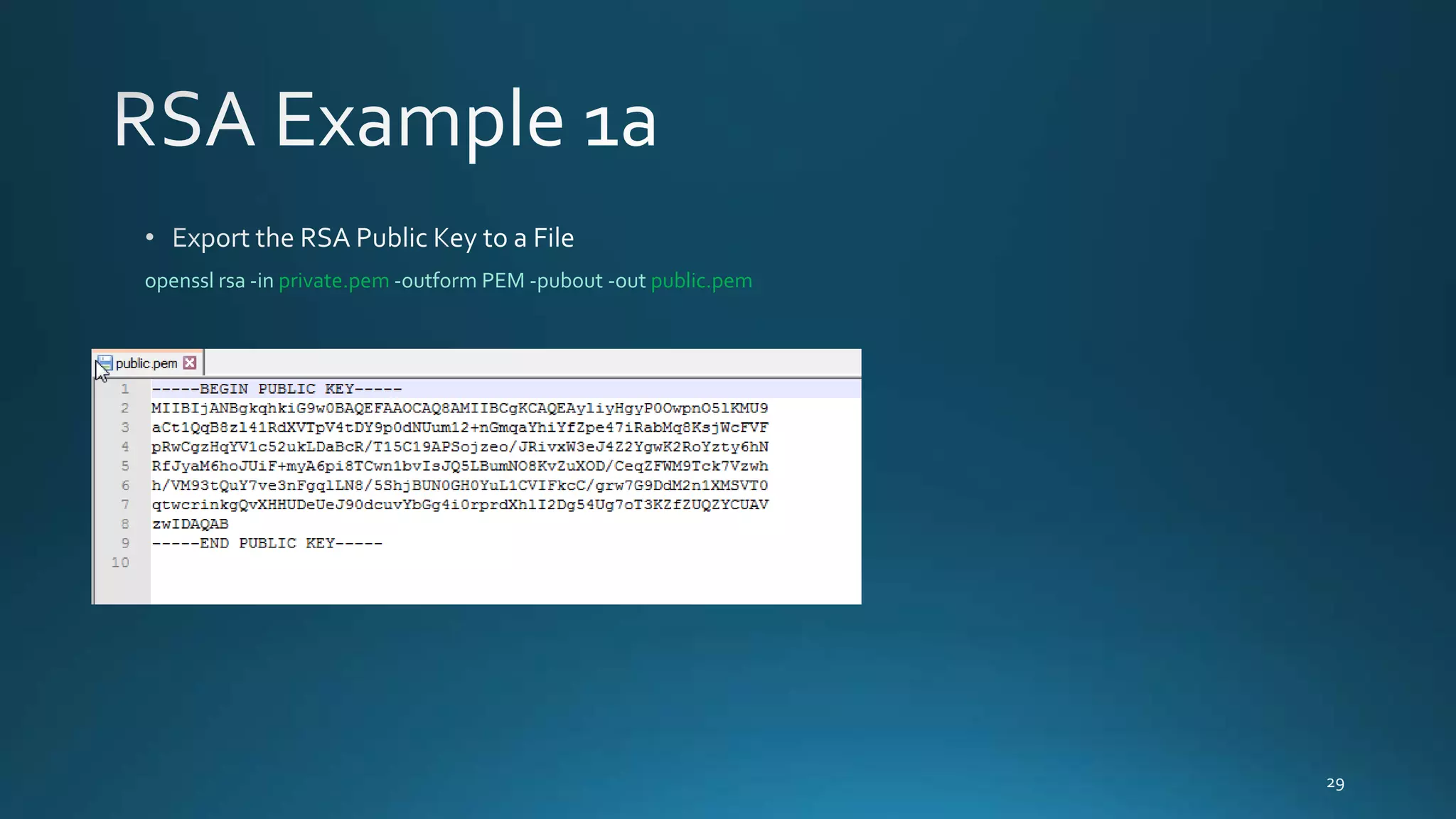
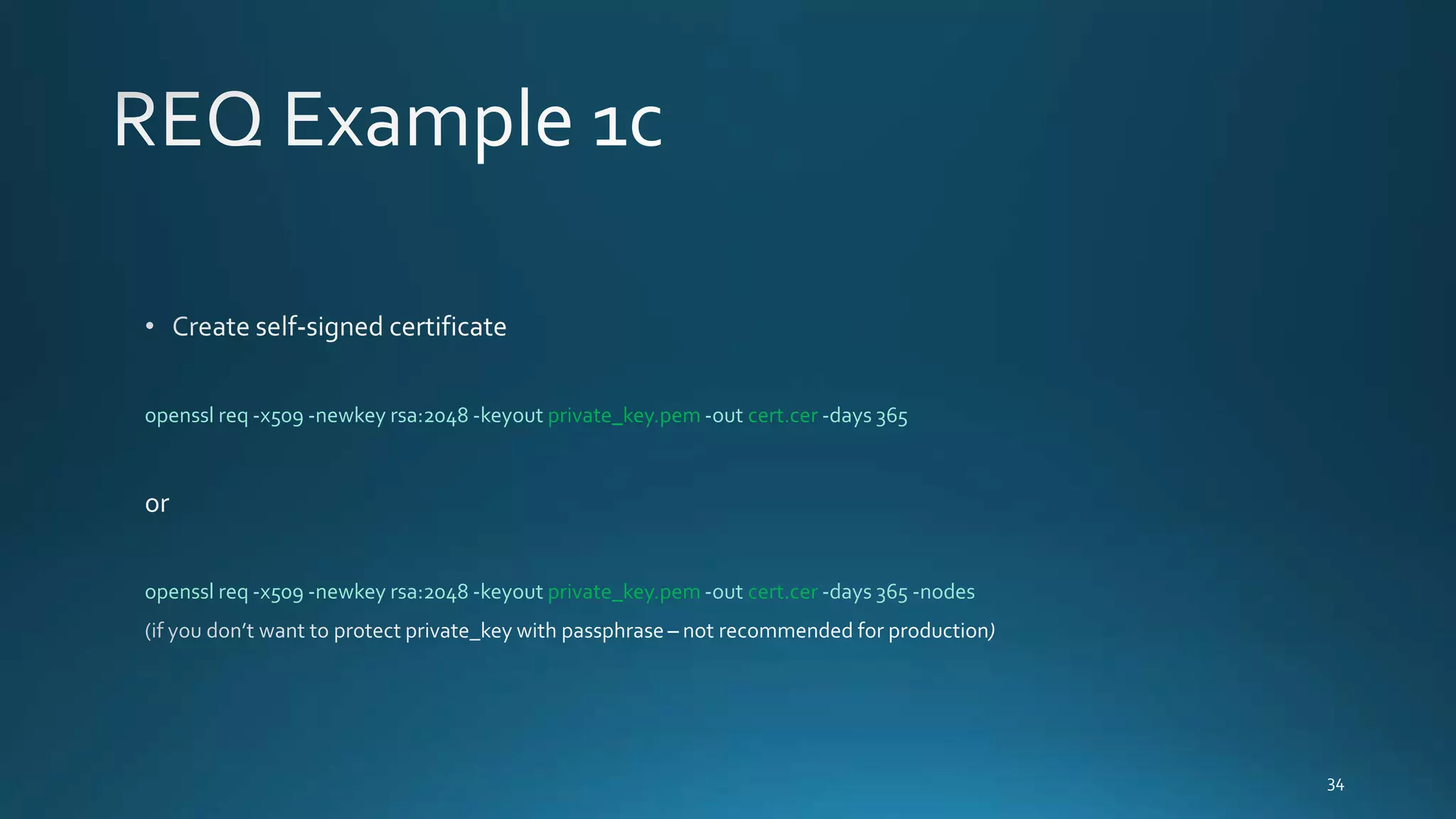
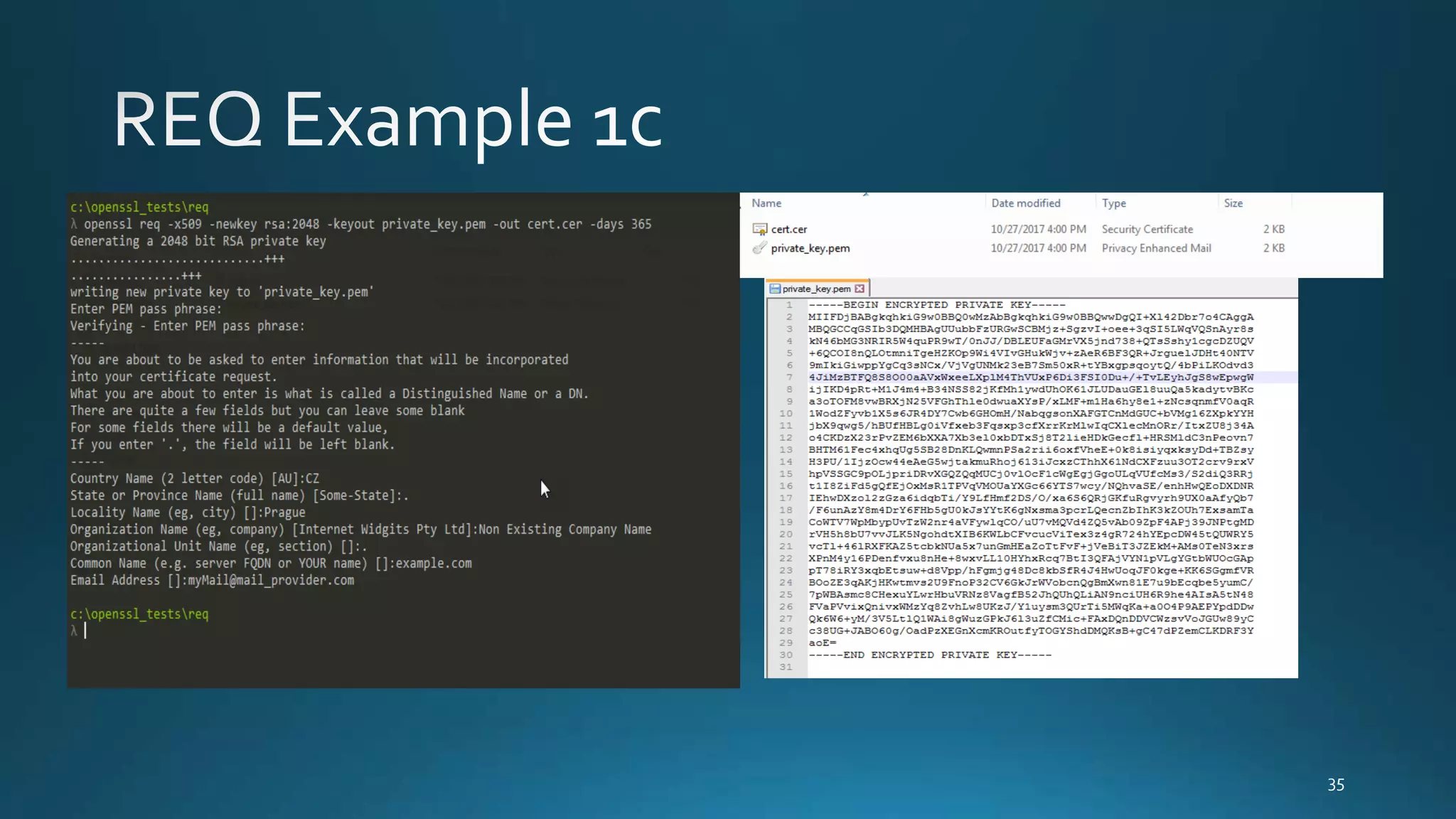
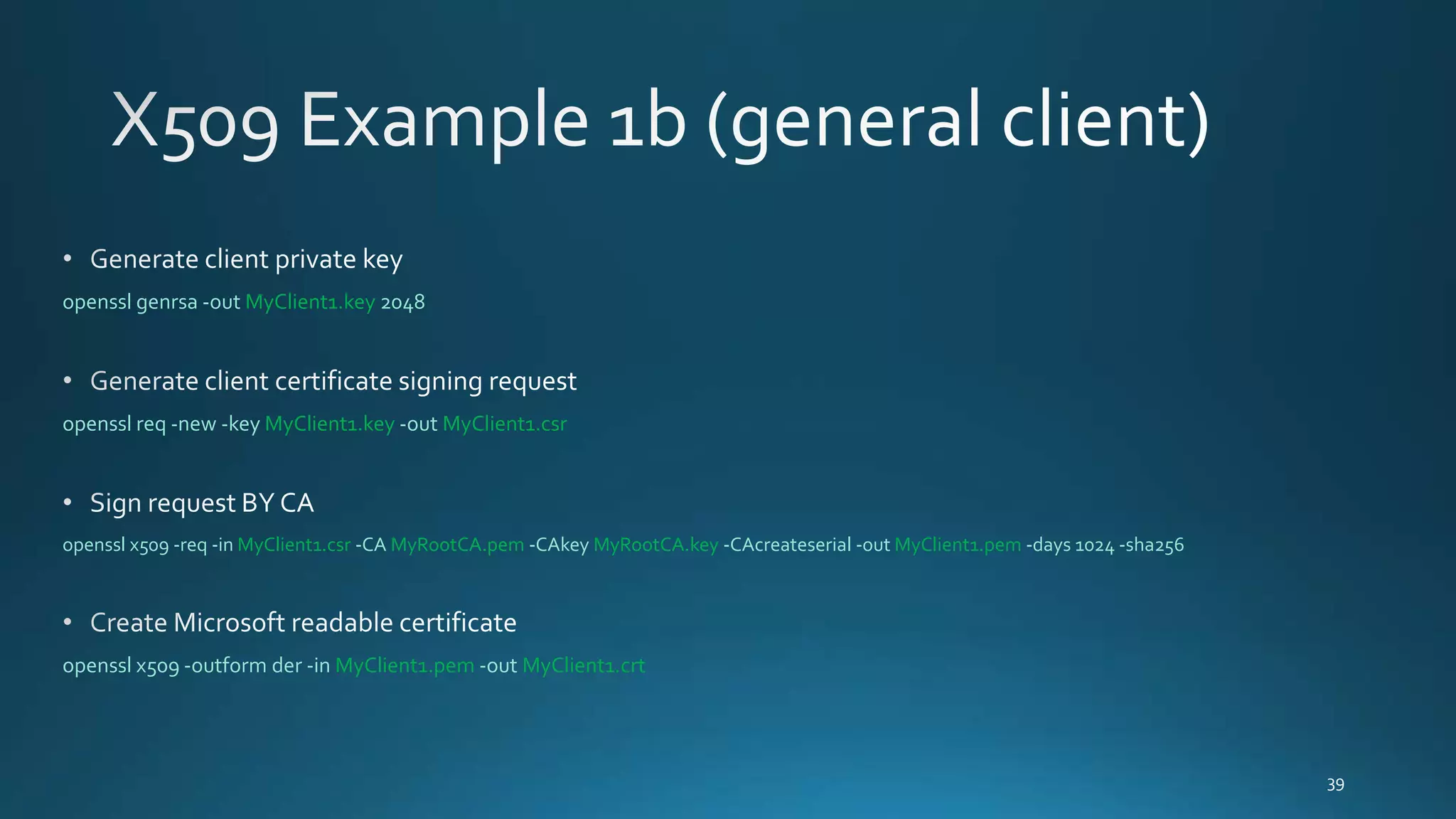
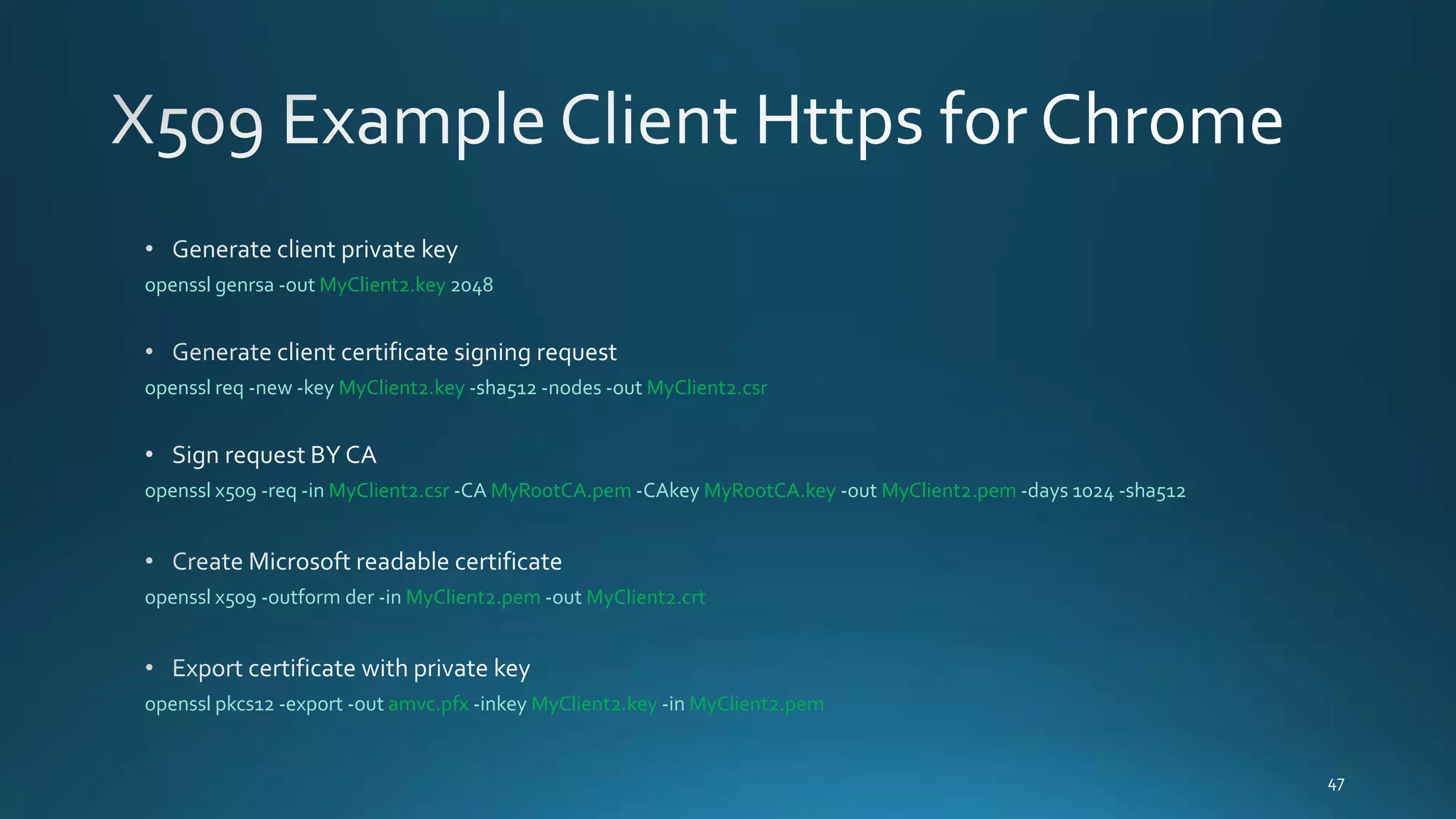
- Examples of OpenSSL commands to generate keys, sign and verify files, encrypt and decrypt files, create certificates, and export certificates to PKCS#12 format.
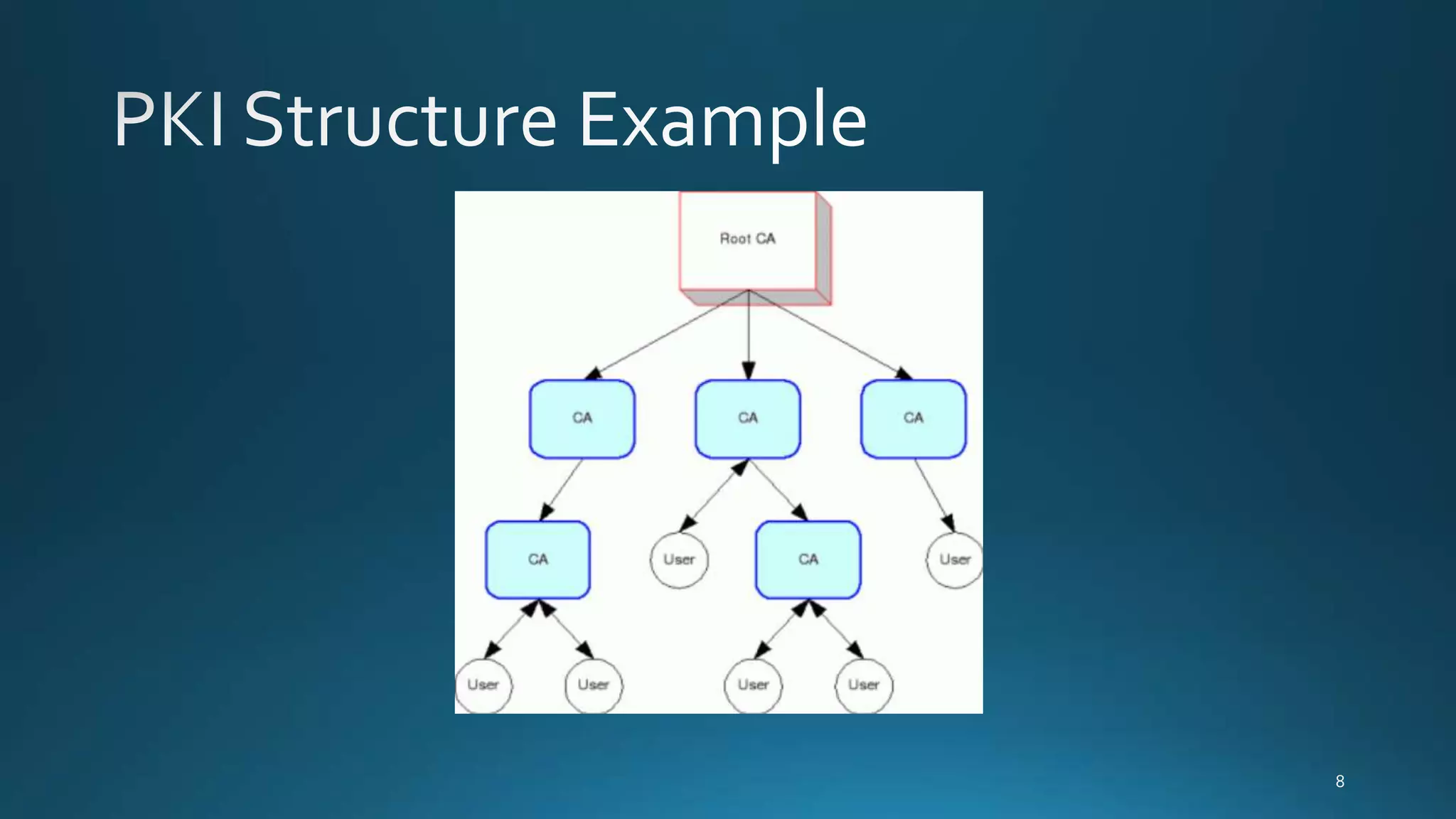
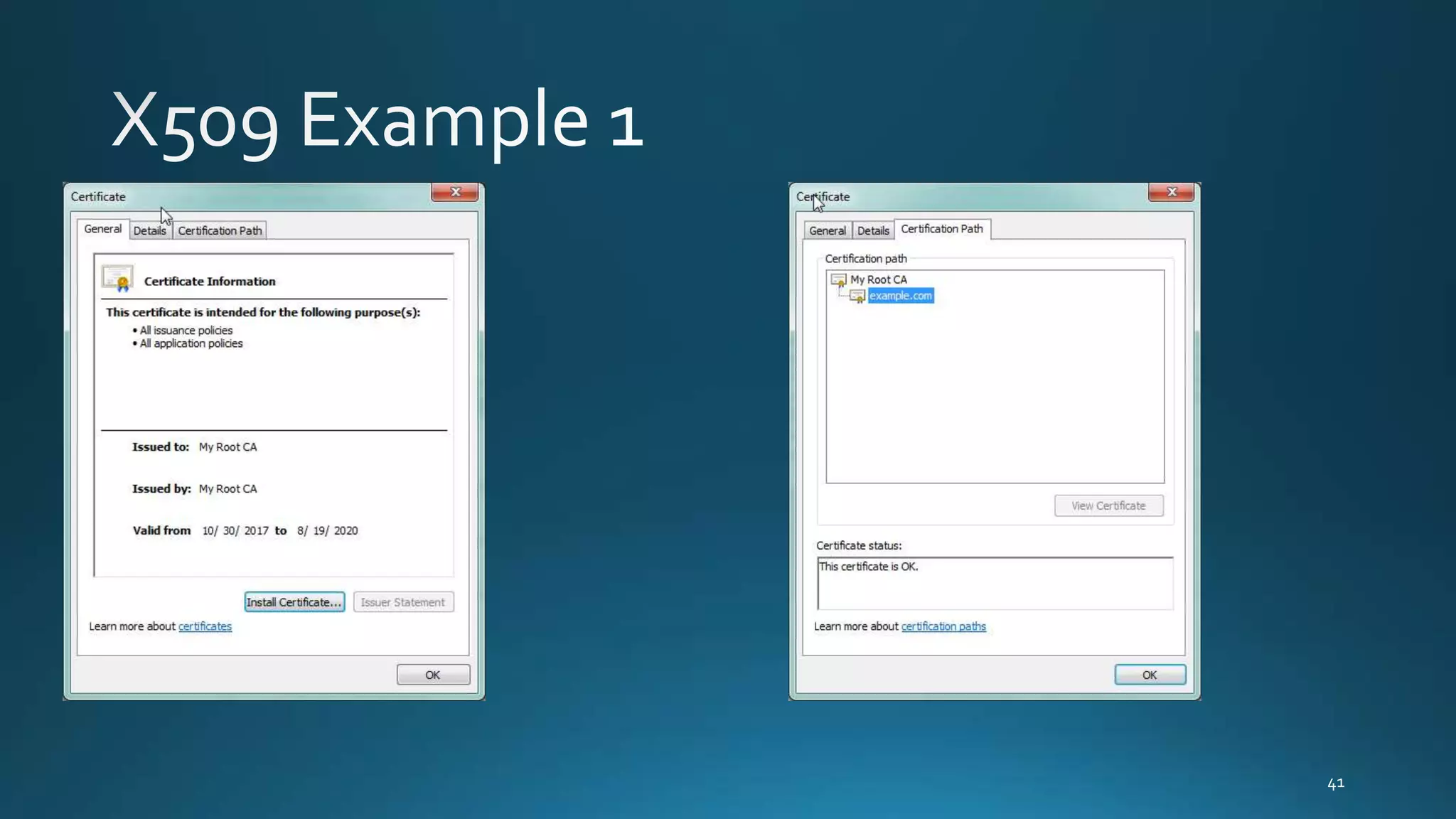
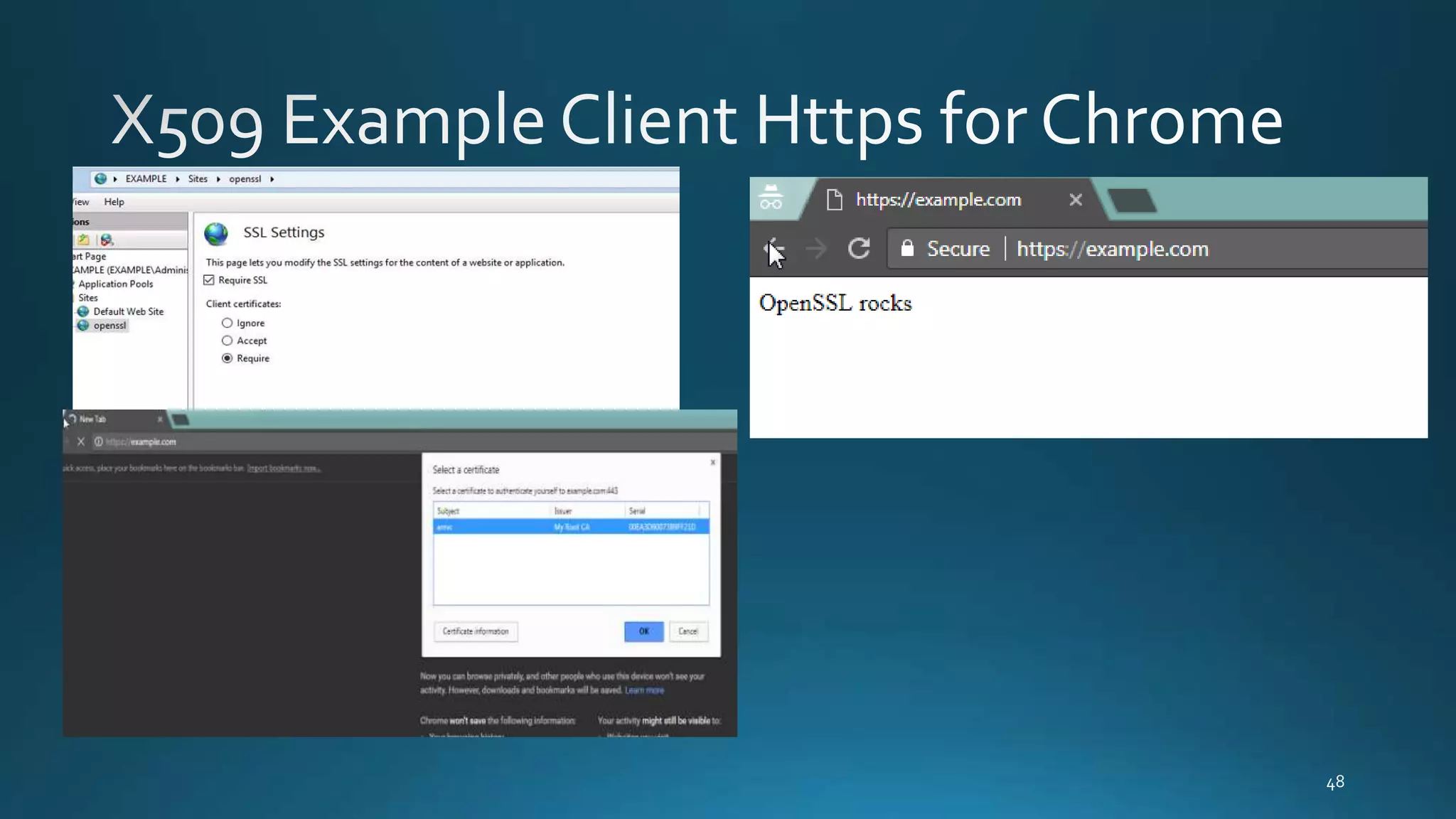
- Information on generating root CAs, client certificates signed by the CA, and exporting certificates.