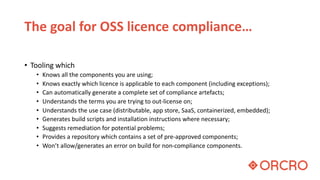
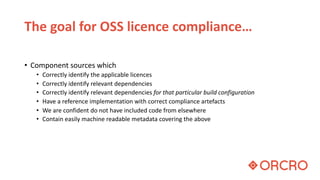
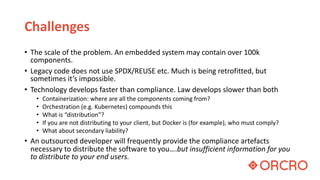
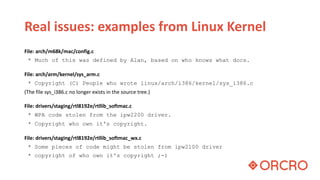
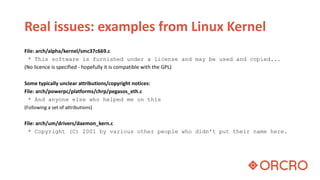
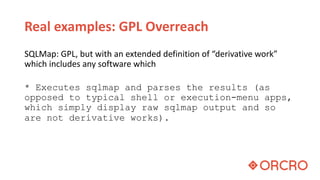
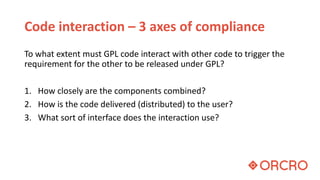
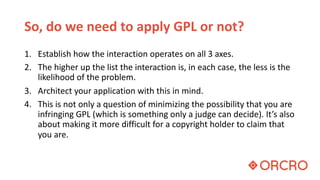
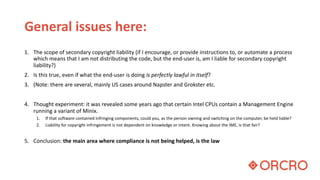
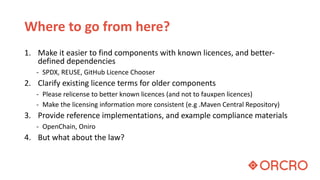
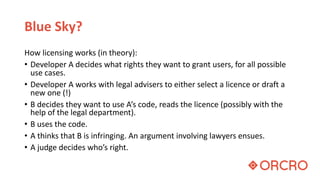
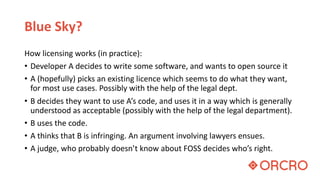
The document discusses the complexities of open source software (OSS) license compliance, emphasizing the need for accurate tooling, component identification, and compliance artifacts amidst rapidly evolving technology and legal frameworks. It highlights real-world examples of compliance challenges and the ambiguities in copyright attribution, especially when dealing with legacy code and new software delivery methods like containerization. Ultimately, the text suggests that while progress is being made in compliance automation, the process remains partially subjective and requires continual refinement to simplify interactions and clarify licensing terms.