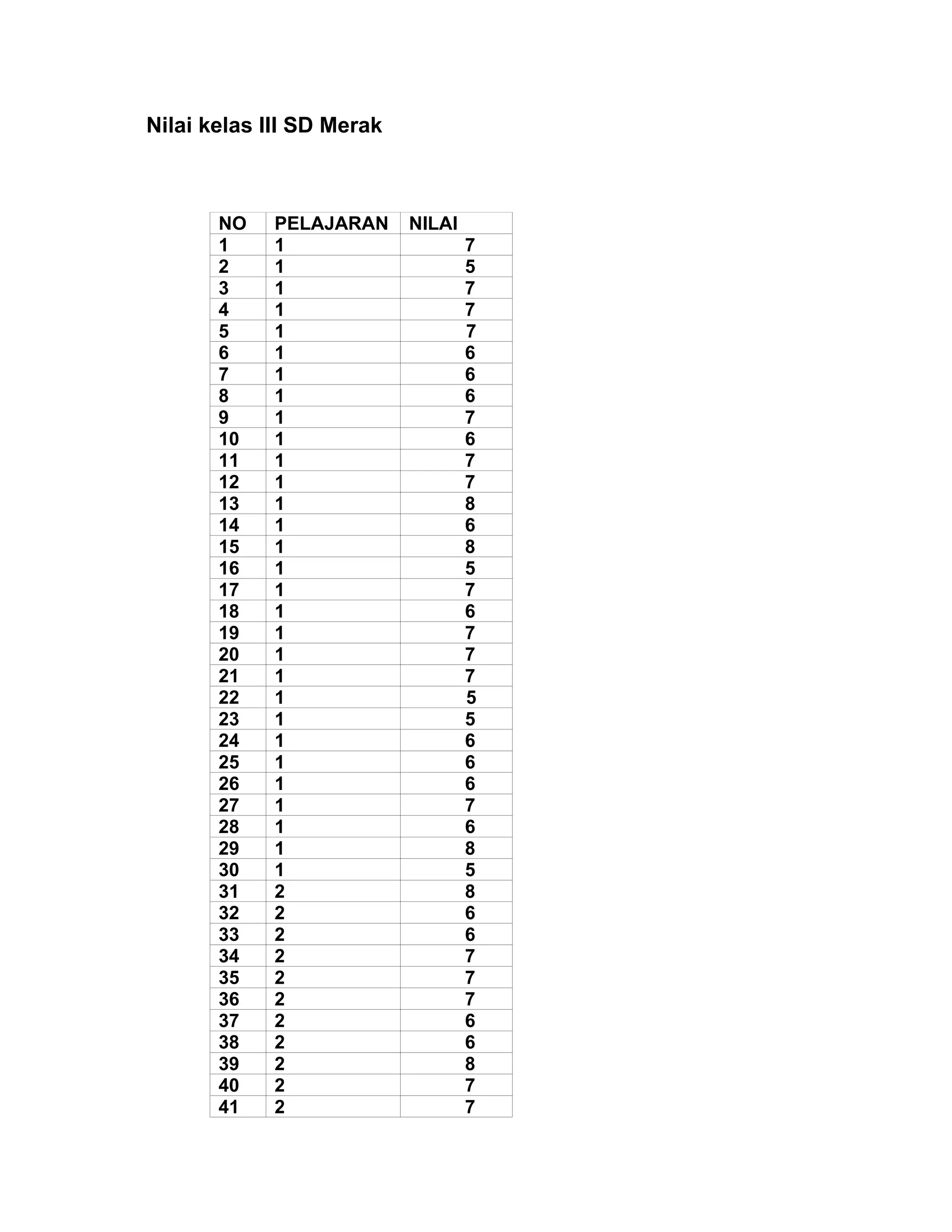
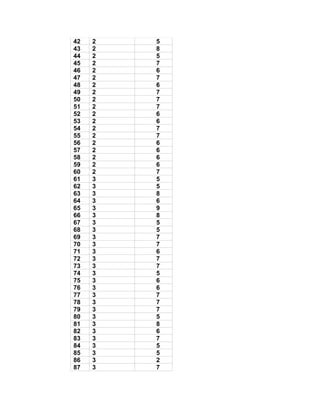
This document contains the test scores of 31 third grade students from SD Merak in three subjects: science, social studies, and math. Based on an ANOVA analysis, there were no statistically significant differences in average scores between the three subjects. Post hoc tests confirmed that all subject pairs were homogeneous subsets.