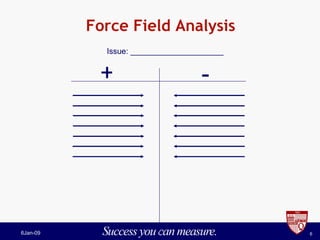
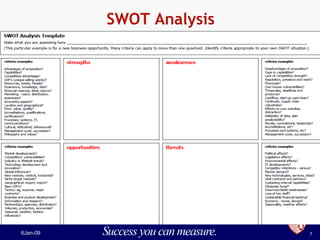
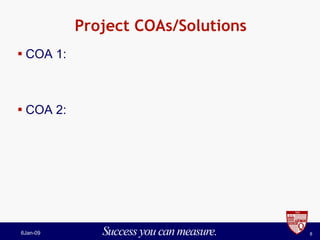
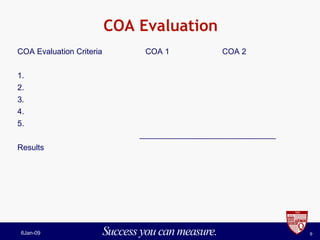
The document outlines the assignment requirements for a project presentation in the HSM 700BL course on principles and applications in homeland security and defense. It includes instructions on team assignments, project analysis methodologies (like SWOT and force field analysis), evaluation criteria, and submission guidelines. Additionally, it prompts students to reflect on integrating course concepts into future homeland security practices.