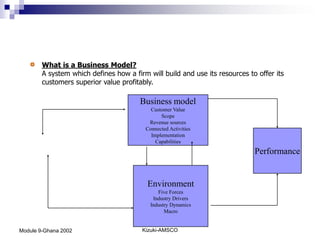
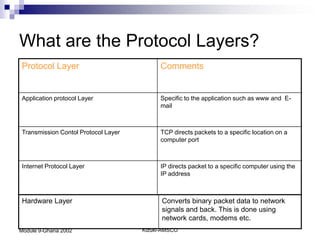
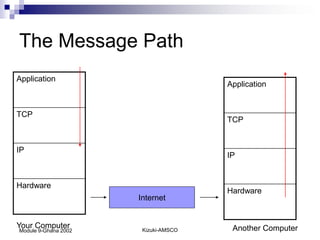
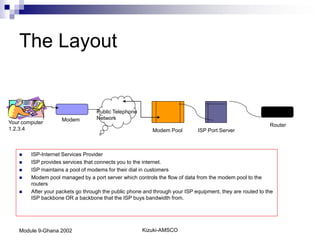
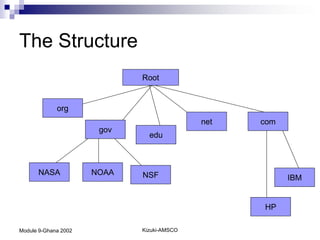
The document discusses several topics related to business-to-business (B2B) models and technology infrastructure. It describes common B2B models including types of business webs, agora, aggregation, value chains, and alliances. It also covers computer networking protocols, internet infrastructure, domain name resolution, and application protocols like HTTP, SMTP, and how computers communicate over the internet.