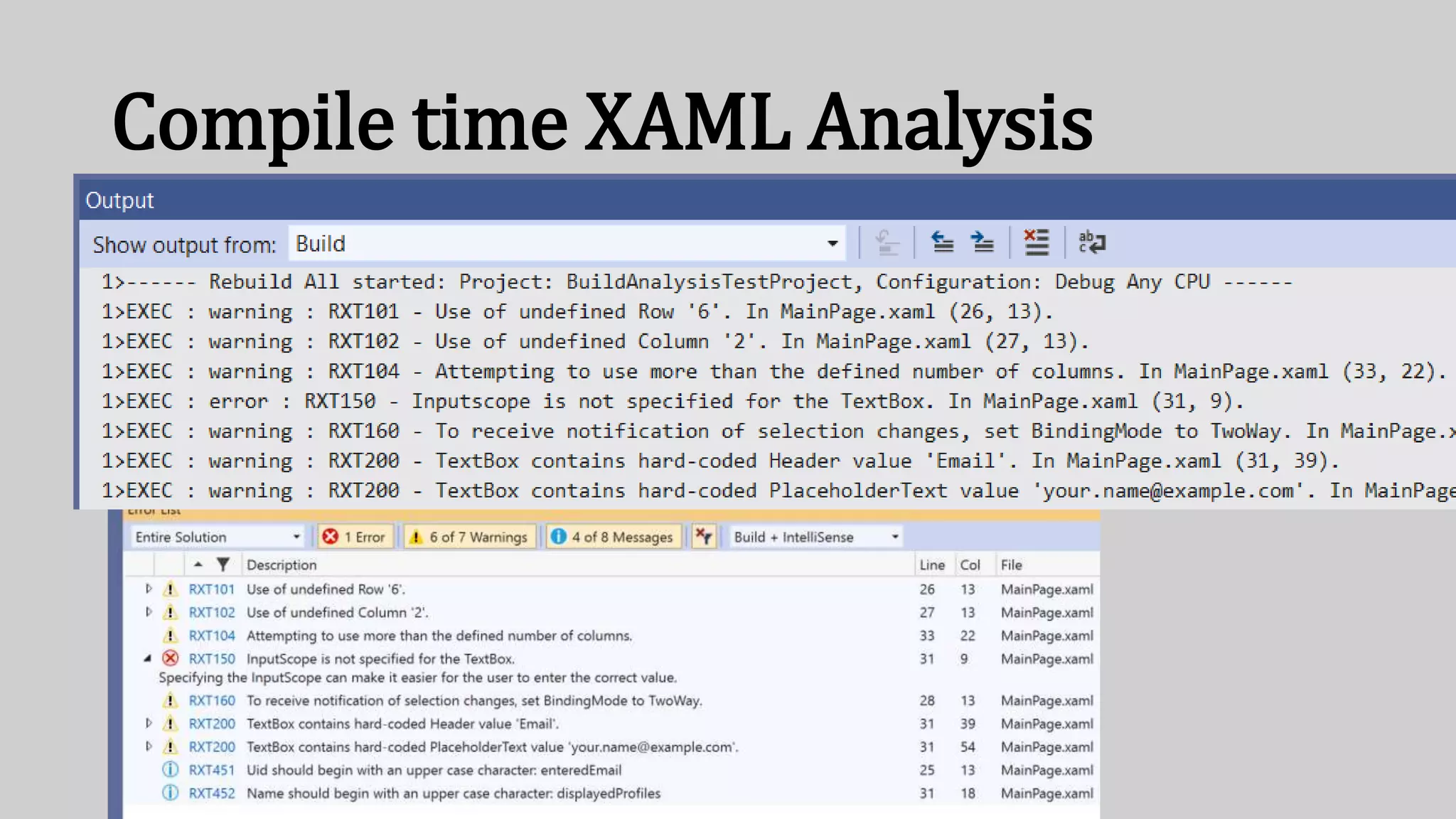
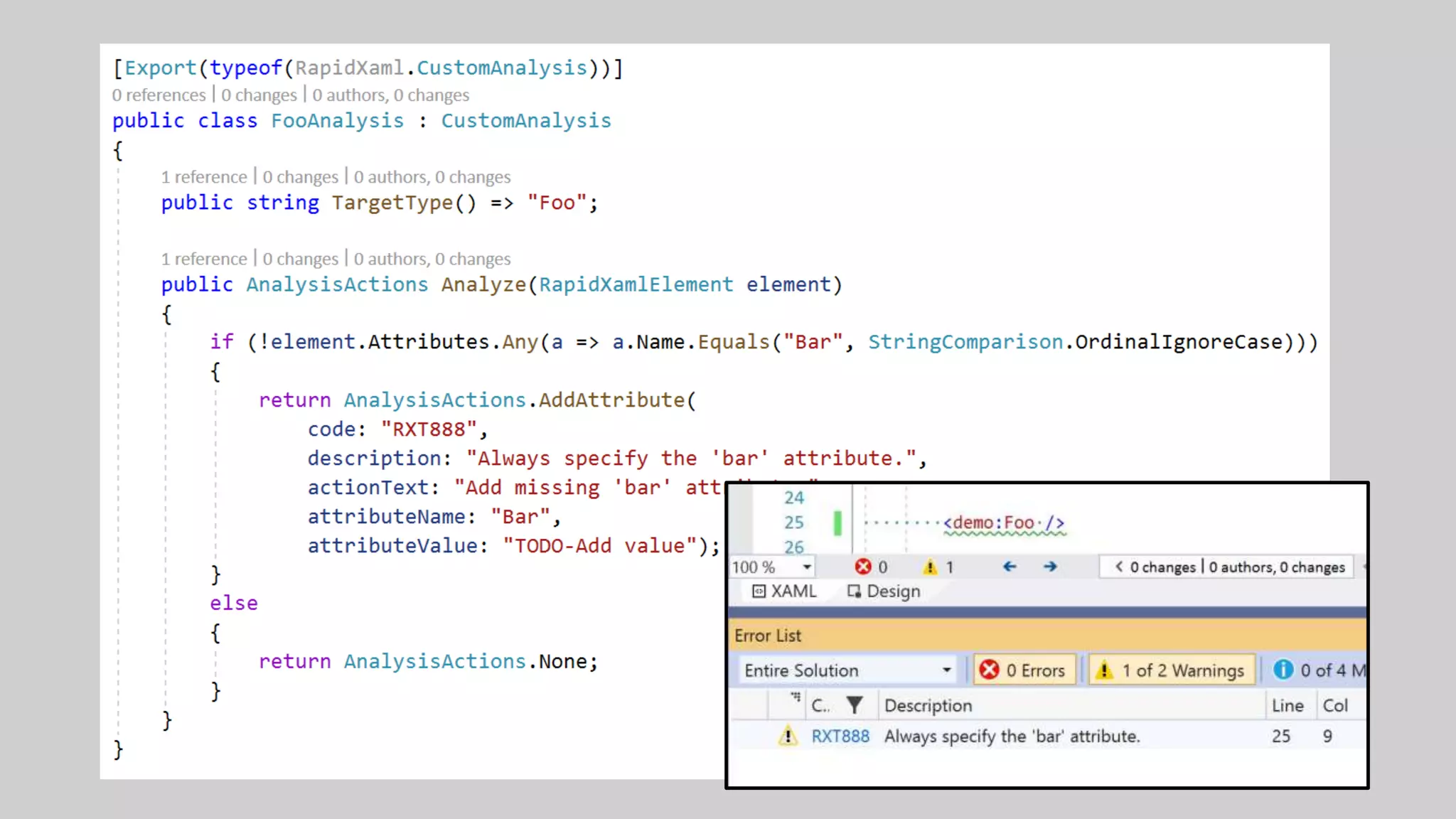
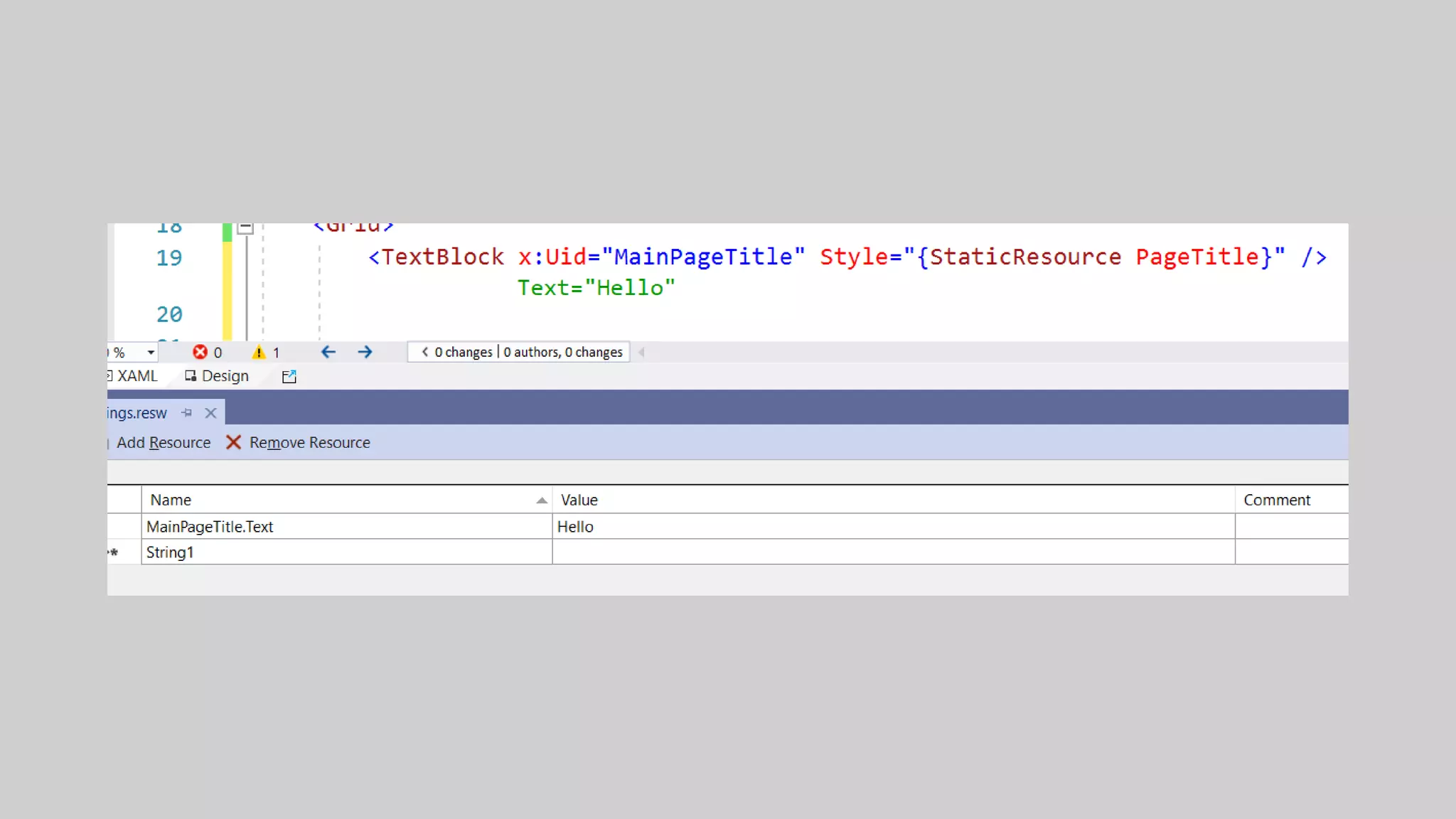
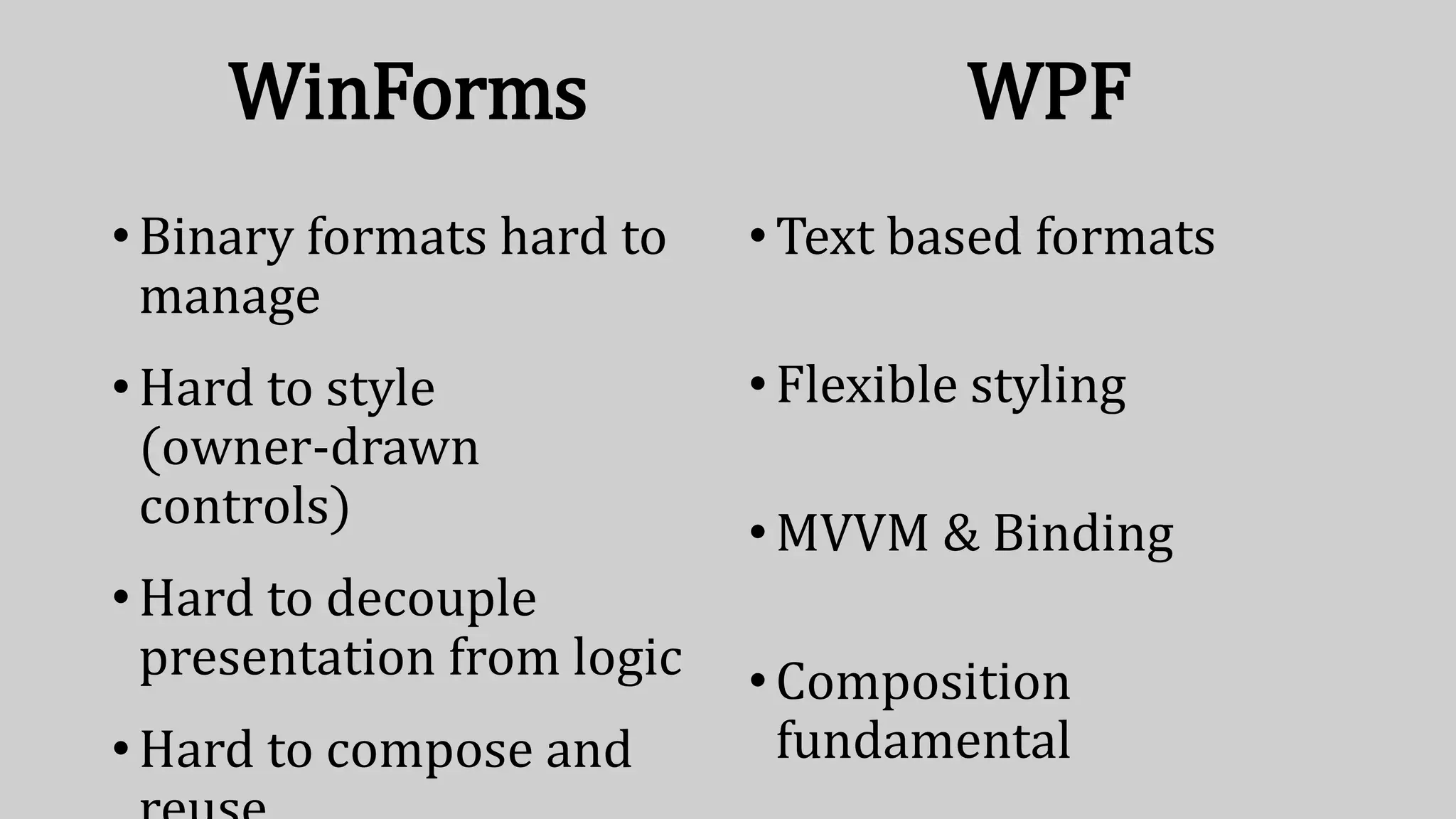
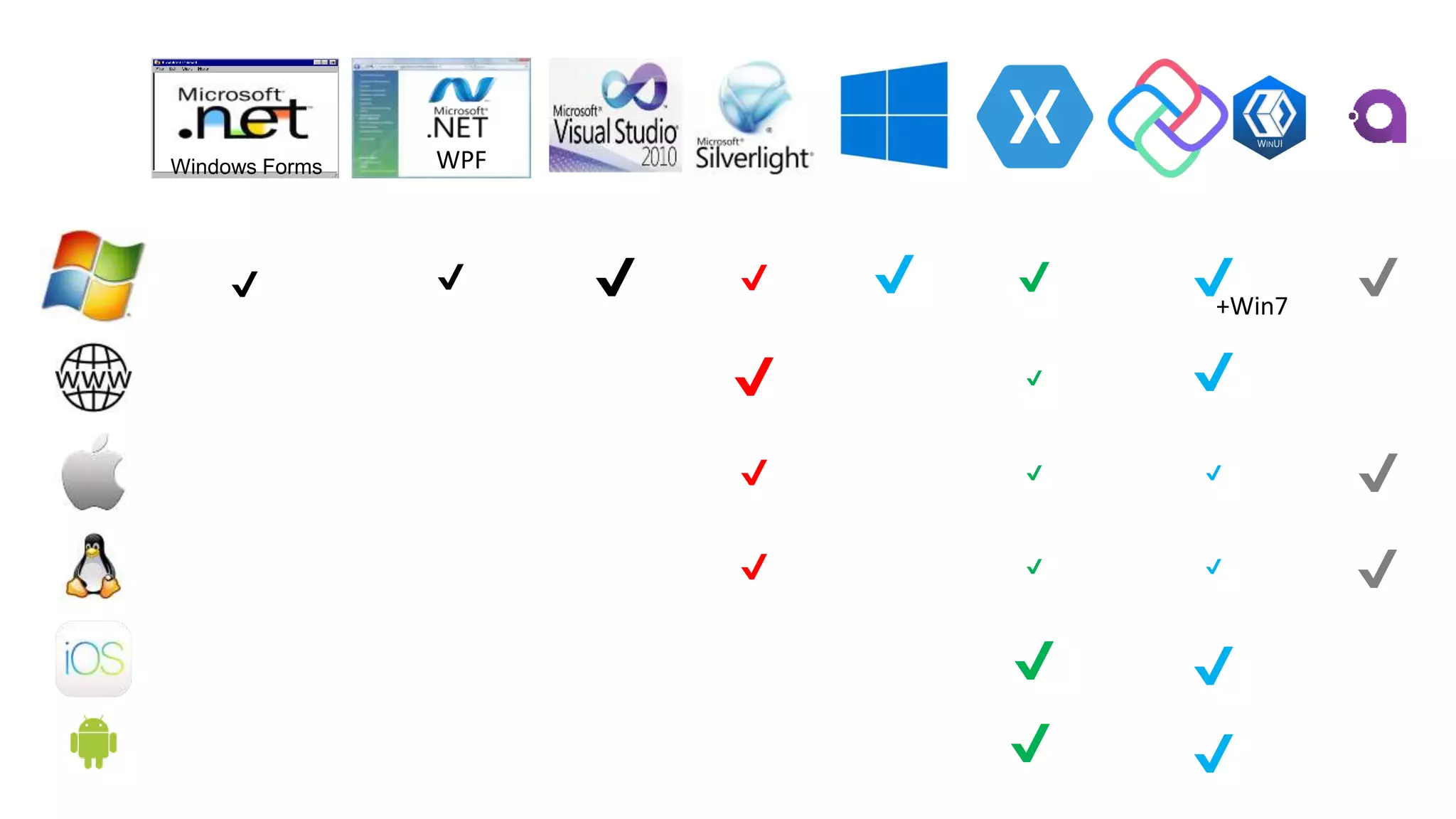
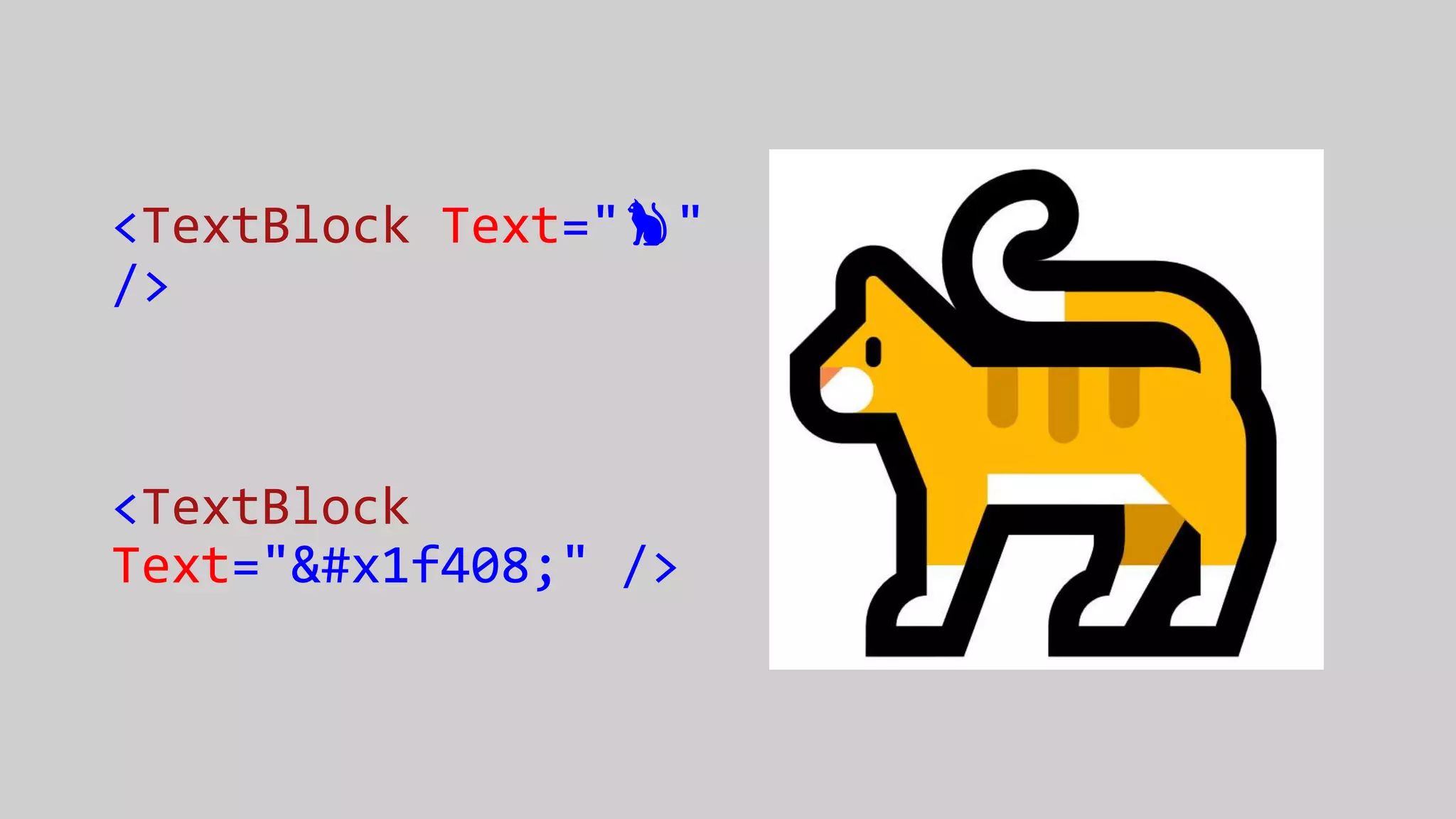
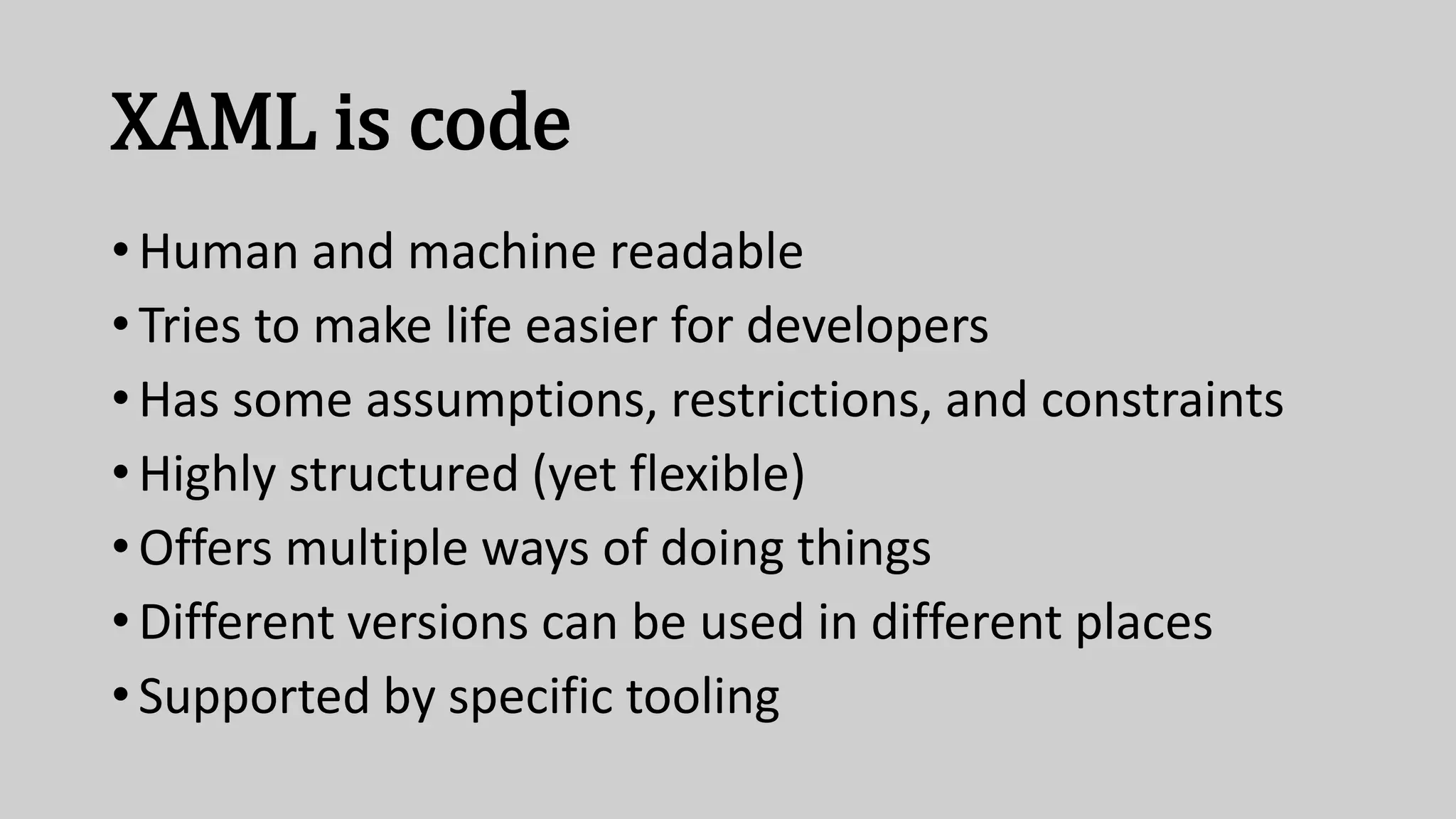
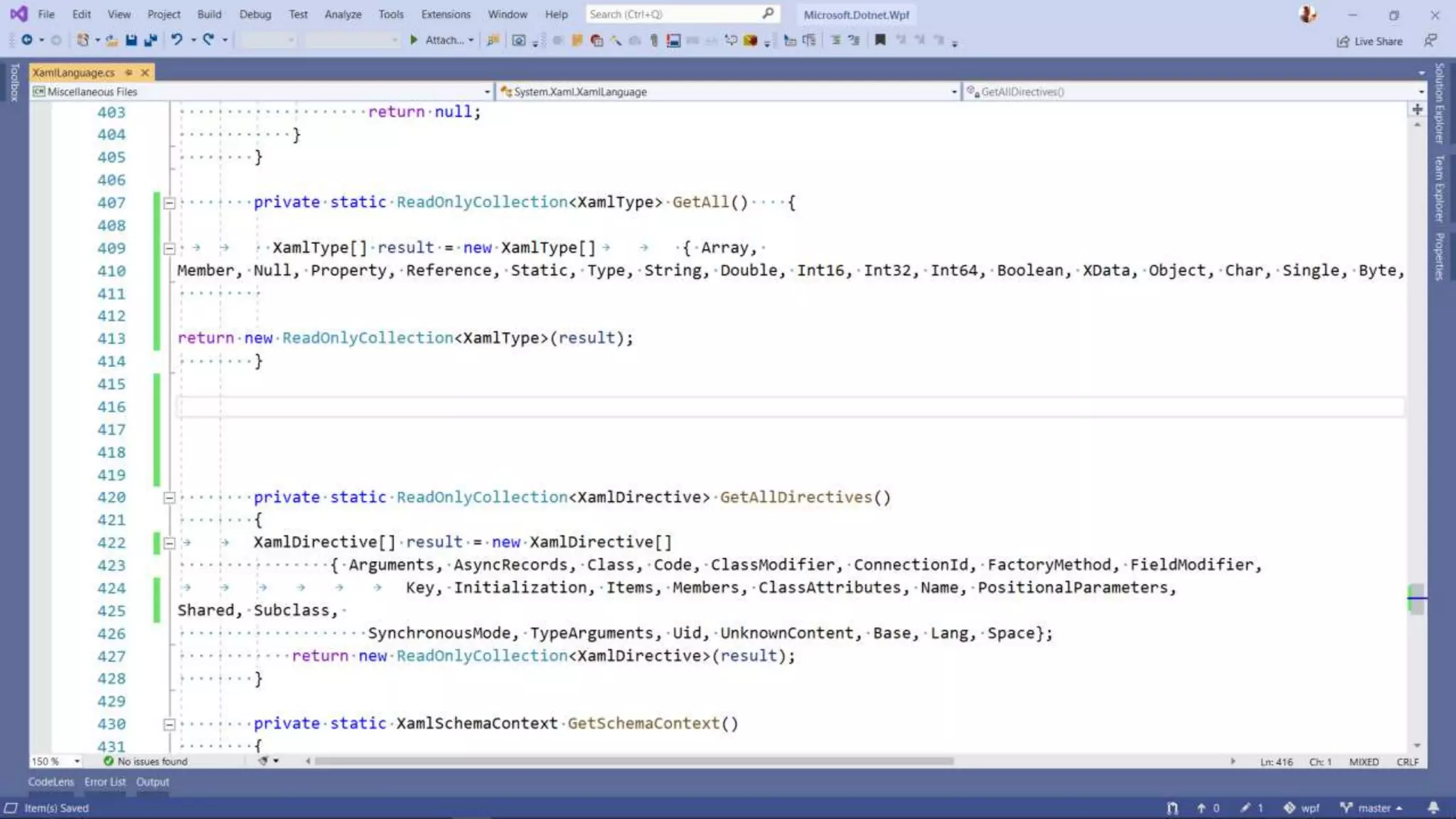
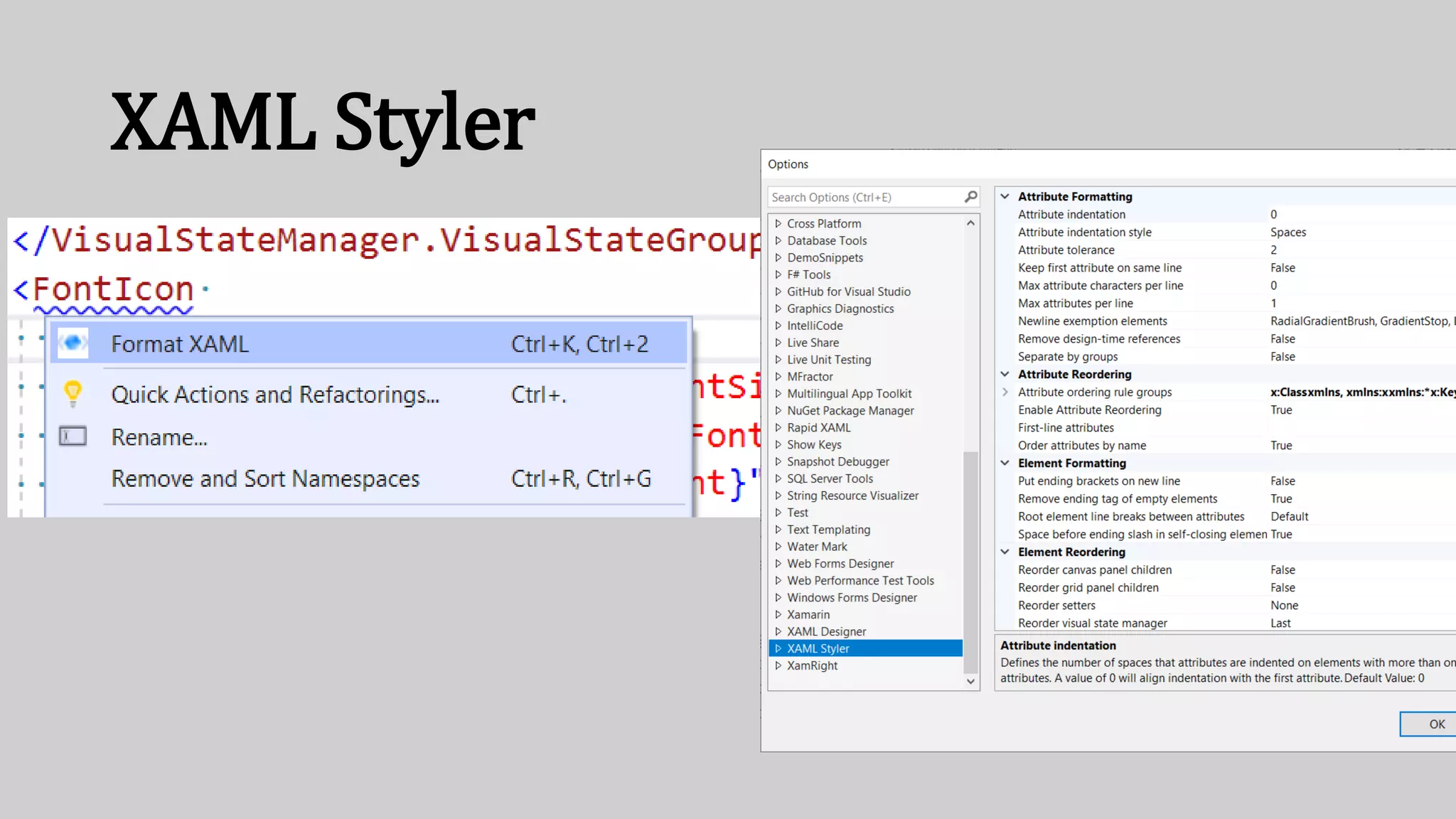
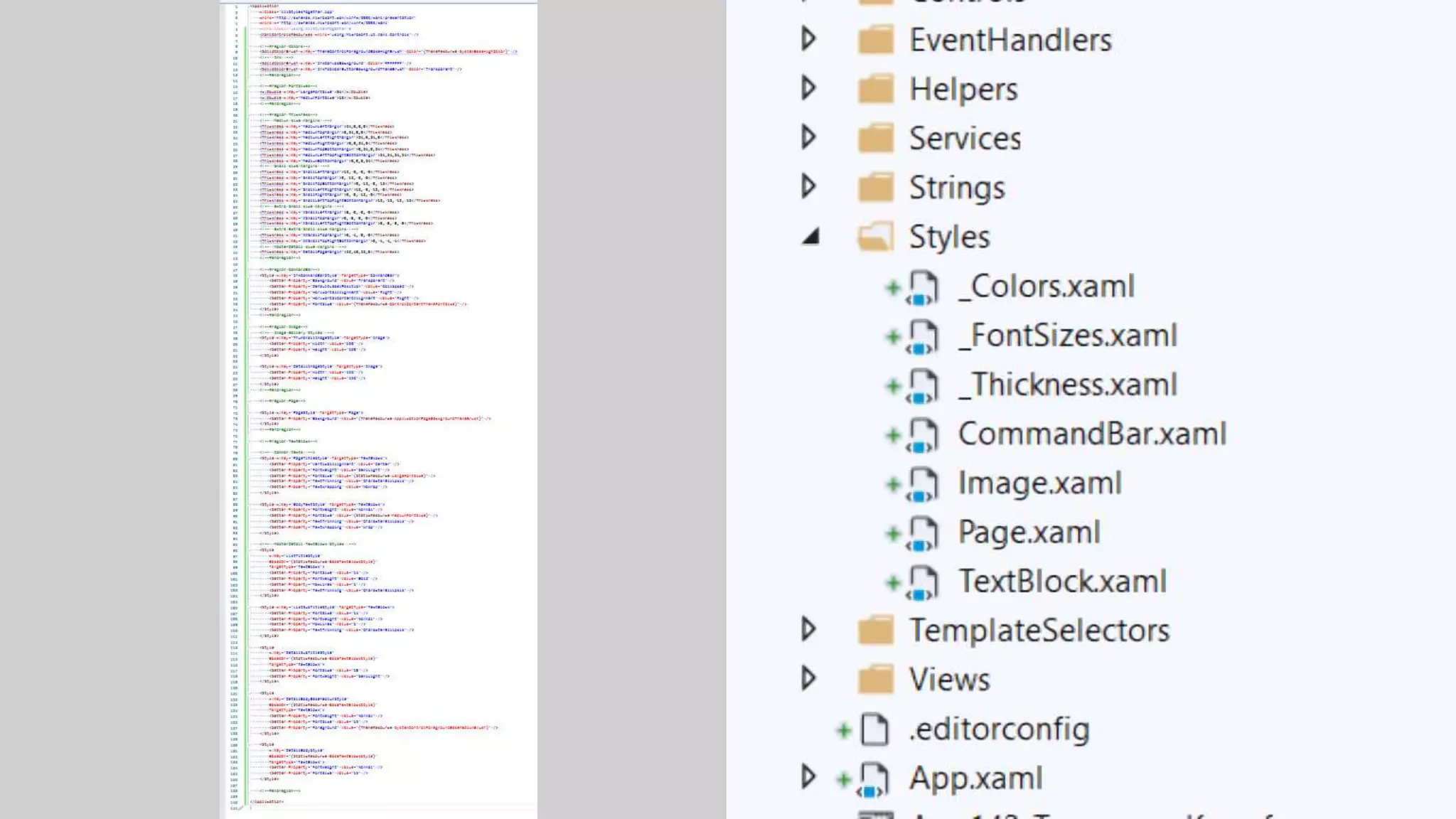
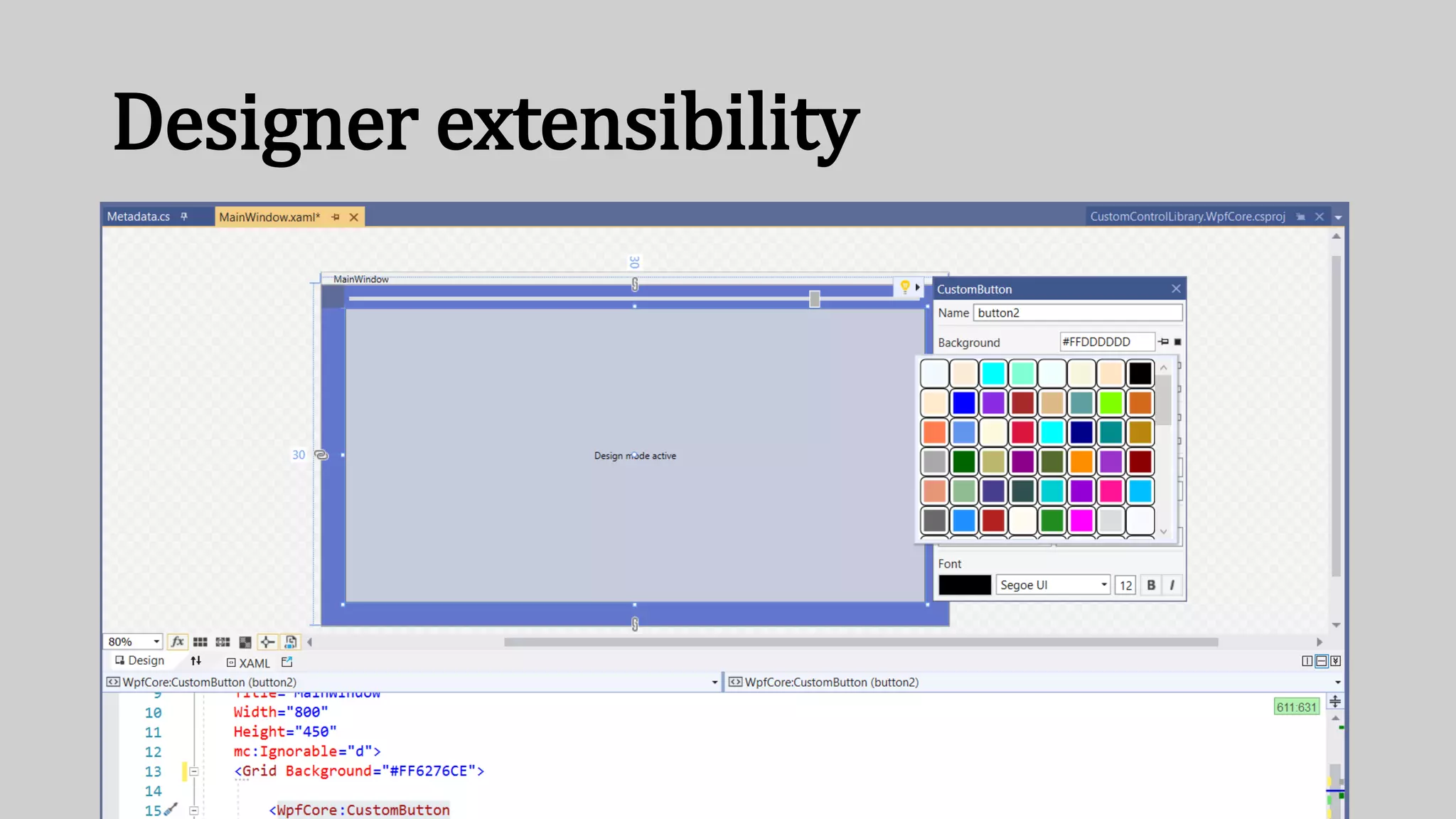
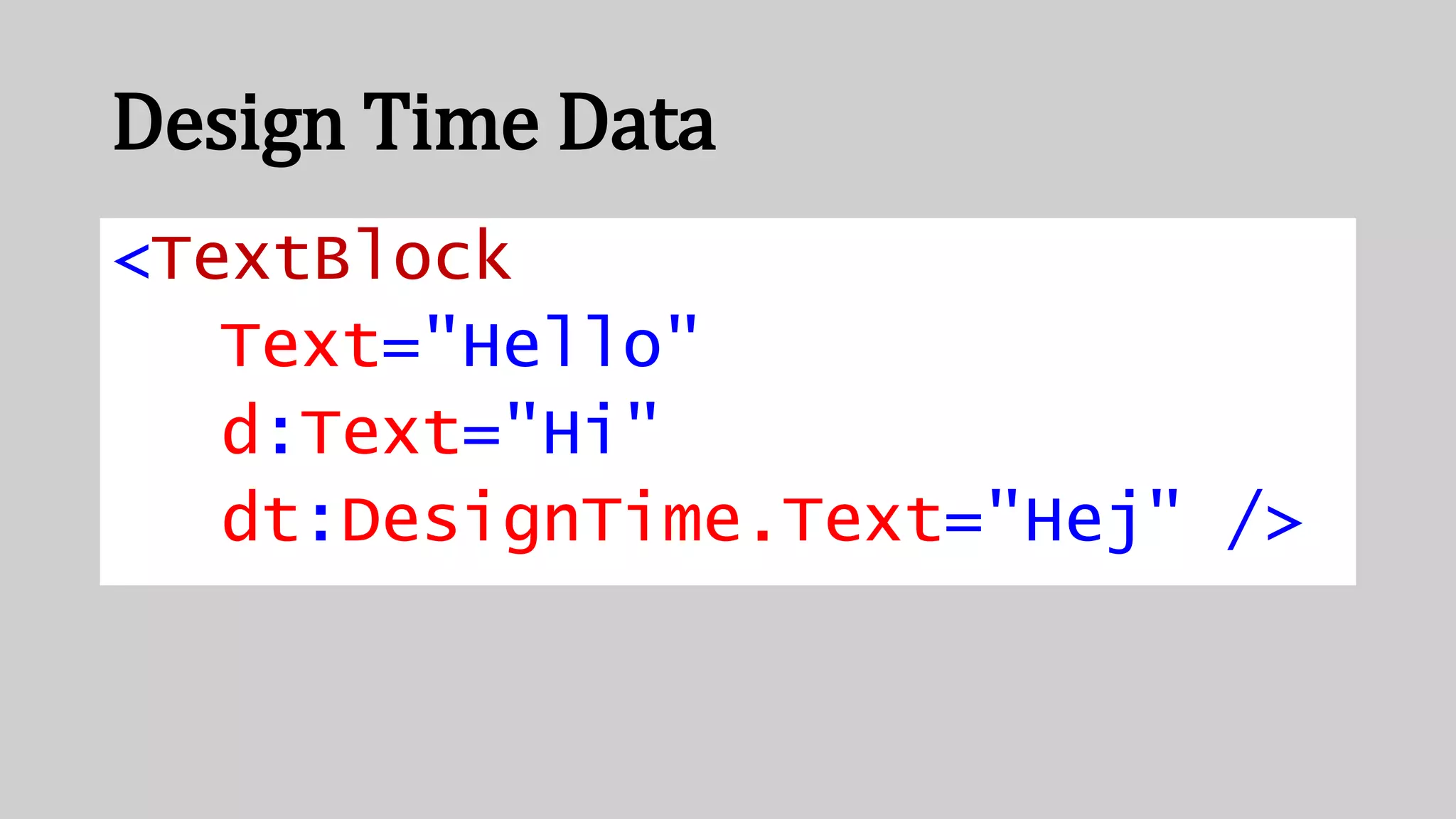
The document presents a talk by Matt Lacey on modern XAML development, covering the evolution of tools and key differences between WinForms and WPF. It emphasizes the flexibility of XAML as both human and machine-readable code, supported by various tools and advancements in Microsoft and community contributions. The session concludes with assurance that XAML is actively evolving and not dead, despite competition from C#.





![3 ways to bind
Text="{Binding Item}"
Text="{x:Bind Item}"
[assembly:
XamlCompilation(XamlCompilationOptions.Compile)]](https://image.slidesharecdn.com/modern-xaml-dev-shared-200210114958/75/Modern-XAML-Development-Matt-Lacey-35-2048.jpg)