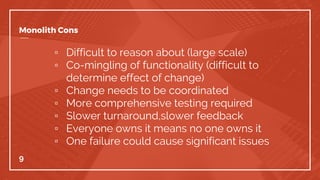
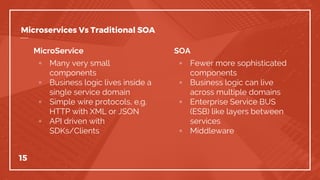
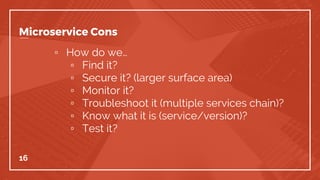
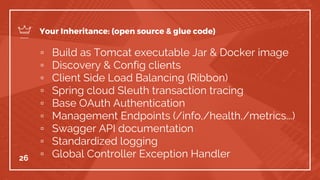
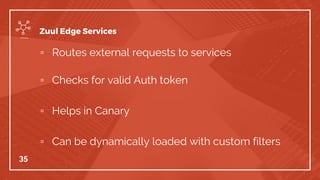
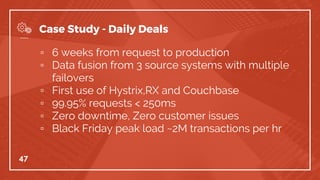
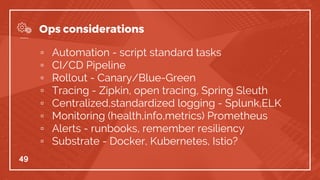
The document outlines the transition from monolithic architecture to microservices, emphasizing the need for improved efficiency, faster feature delivery, and enhanced security. It describes the microservices framework developed by the authors, detailing its components, principles, and operational considerations. Additionally, it provides insights into the challenges faced during implementation and cultural changes required for successful adoption.