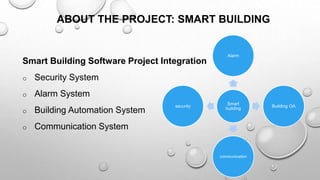
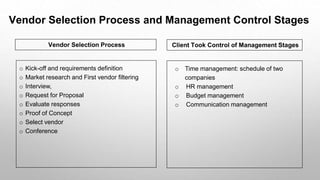
The document examines a sole-supplier relationship between a small telecommunications client, Smart Telecom, and a medium-sized software vendor, Hsoft, focusing on a smart building software project. It utilizes autoethnography methodology to capture personal experiences and reflections during the vendor selection and project management process. Key phases include vendor filtering, negotiations, and implementing the project while managing time, budget, and communication effectively.