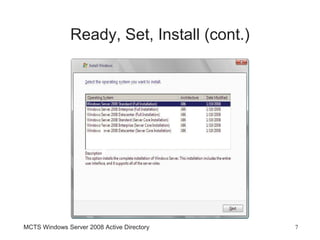
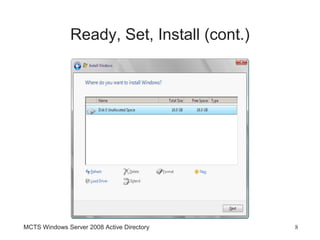
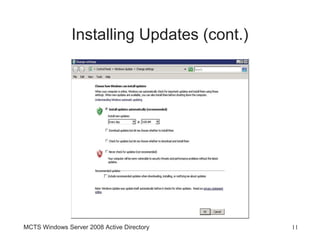
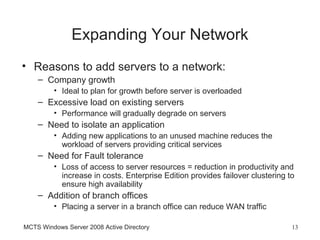
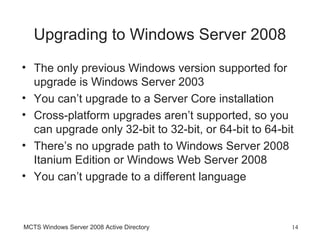
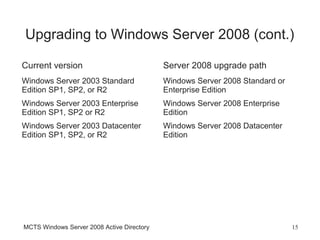
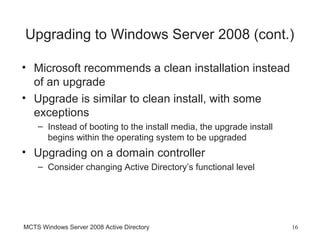
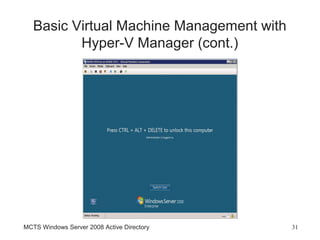
The document discusses planning a Windows Server 2008 installation including hardware requirements, installing the server, and post-installation tasks. It also covers expanding networks by adding domain controllers, member servers, or standalone servers. Server Core installations and virtualization with Hyper-V are described.