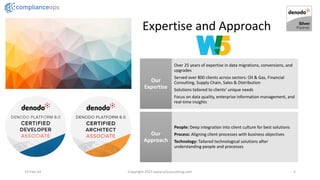
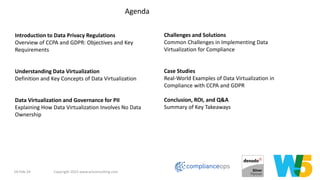
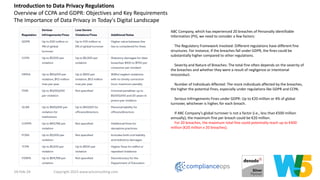
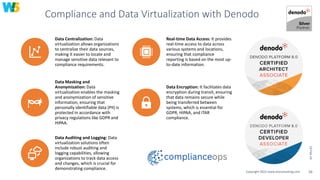
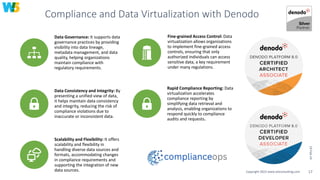
W5 Consulting focuses on empowering businesses through advanced data management and compliance solutions, emphasizing the importance of data privacy regulations such as CCPA and GDPR. The company offers expertise in data virtualization, ensuring seamless compliance by centralizing data management while minimizing risks and costs associated with breaches. Through tailored solutions and extensive experience, W5 Consulting helps organizations achieve operational excellence and effective governance in handling sensitive data.