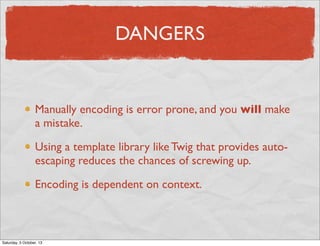
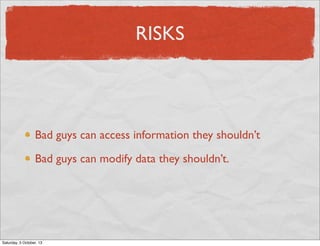
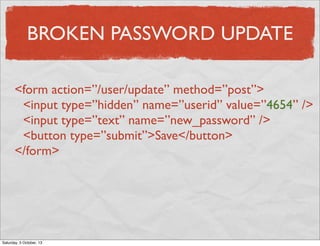
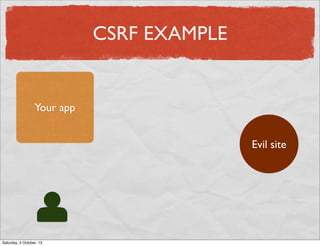
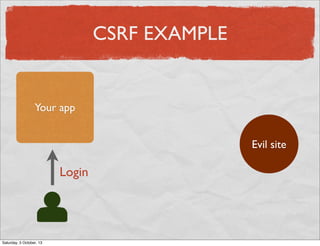
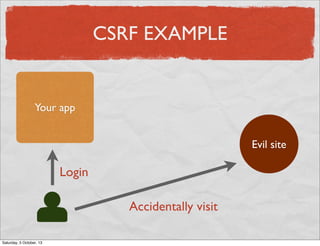
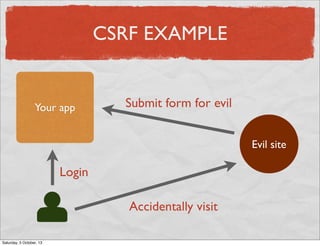
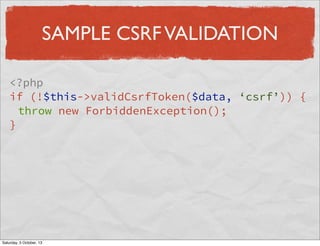
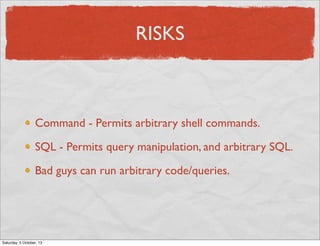
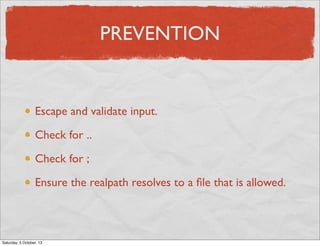
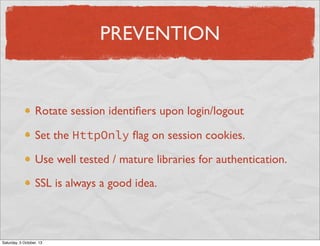
This document discusses the OWASP Top 10 security exploits and provides prevention strategies. It covers injection flaws like SQL injection and command injection, broken authentication and session management, cross-site scripting (XSS), insecure direct object references, security misconfiguration, sensitive data exposure, missing access controls, cross-site request forgery (CSRF), using outdated components with known vulnerabilities, and unvalidated redirects/forwards. The document emphasizes input validation, output encoding, access control, secure configurations, encryption, and updating components to avoid these common vulnerabilities.



![SQL INJECTION EXAMPLE
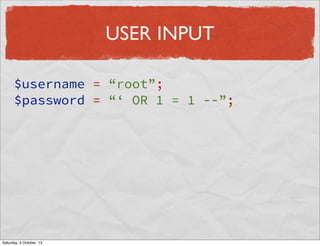
$username = $_POST[‘username’];
$password = $_POST[‘password’];
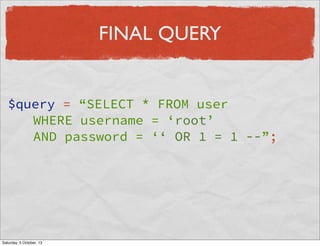
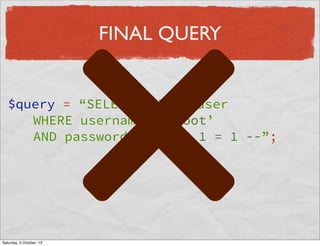
$query = “SELECT * FROM user
WHERE username = ‘$username’
AND password = ‘$password’”;
$user = $db->query($query);
Saturday, 5 October, 13](https://image.slidesharecdn.com/markstory-avoidingtheowasp-140129054743-phpapp01/85/2013-Mark-story-Avoiding-the-Owasp-9-320.jpg)
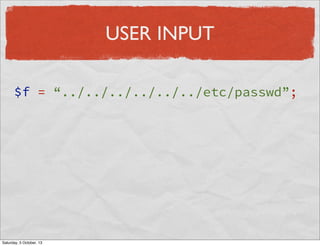
![COMMAND INJECTION
$file = $_POST[‘file’];
$res = file_get_contents($file);
echo $res;
Saturday, 5 October, 13](https://image.slidesharecdn.com/markstory-avoidingtheowasp-140129054743-phpapp01/85/2013-Mark-story-Avoiding-the-Owasp-15-320.jpg)
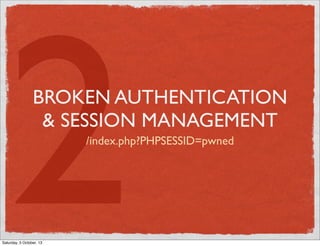
![SESSION FIXATION EXAMPLE
<?php
session_start();
if (isset($_GET[‘sessionid’]) {
session_id($_GET[‘sessionid’]);
}
Saturday, 5 October, 13](https://image.slidesharecdn.com/markstory-avoidingtheowasp-140129054743-phpapp01/85/2013-Mark-story-Avoiding-the-Owasp-20-320.jpg)
![SESSION FIXATION EXAMPLE
<?php
session_start();
if (isset($_GET[‘sessionid’]) {
session_id($_GET[‘sessionid’]);
}
Saturday, 5 October, 13](https://image.slidesharecdn.com/markstory-avoidingtheowasp-140129054743-phpapp01/85/2013-Mark-story-Avoiding-the-Owasp-21-320.jpg)
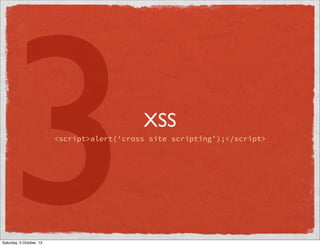
![XSS EXAMPLE
<p>
<?php echo $user[‘bio’]; ?>
</p>
Saturday, 5 October, 13](https://image.slidesharecdn.com/markstory-avoidingtheowasp-140129054743-phpapp01/85/2013-Mark-story-Avoiding-the-Owasp-25-320.jpg)
![XSS EXAMPLE
<p>
<?php echo $user[‘bio’]; ?>
</p>
Saturday, 5 October, 13](https://image.slidesharecdn.com/markstory-avoidingtheowasp-140129054743-phpapp01/85/2013-Mark-story-Avoiding-the-Owasp-26-320.jpg)
![EXAMPLE
<p>
<?php echo htmlentities(
$user[‘bio’],
ENT_QUOTES,
‘UTF-8’
); ?>
</p>
Saturday, 5 October, 13](https://image.slidesharecdn.com/markstory-avoidingtheowasp-140129054743-phpapp01/85/2013-Mark-story-Avoiding-the-Owasp-30-320.jpg)