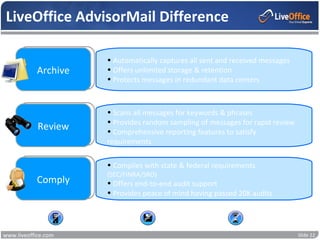
The document outlines the importance of email compliance for investment advisers and broker-dealers, emphasizing the need for effective supervision of electronic communications in order to meet regulatory requirements set by organizations like SEC and FINRA. It categorizes risk areas that require supervision, including performance advertising, safeguarding confidential client information, anti-money laundering, and conflicts of interest. Additionally, rules and best practices for managing captured email are discussed, alongside considerations for compliance and documentation.