Embed presentation
Download as PDF, PPTX

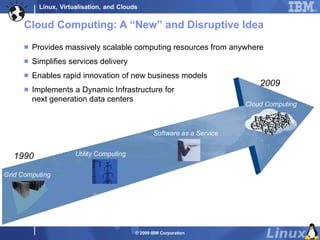
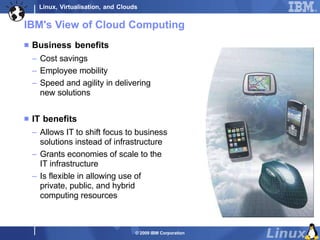
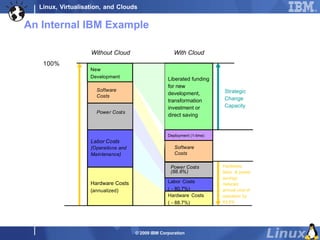
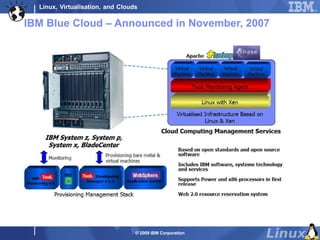
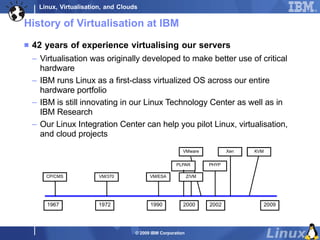
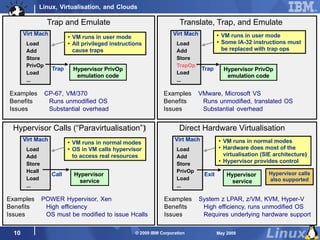


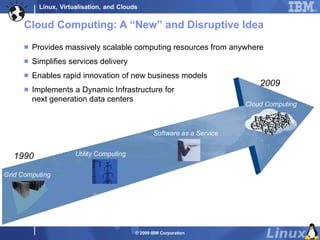
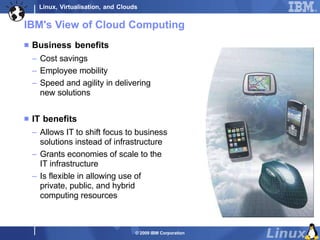
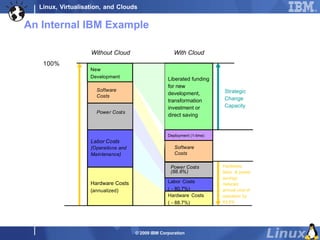
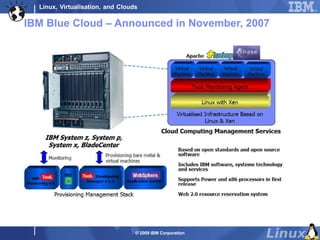
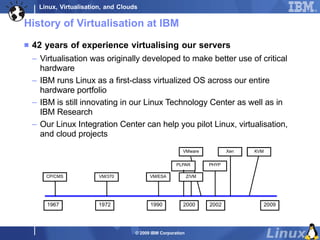
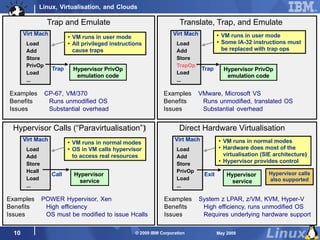
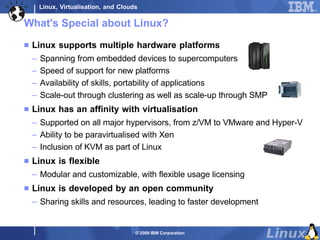
The document discusses the relationship between Linux, virtualization, and cloud computing, highlighting how virtualization increases efficiency and flexibility in data centers. IBM's viewpoint is provided, emphasizing business benefits like cost savings and improved IT agility, alongside the historical context of virtualization technologies. It suggests that Linux's open and adaptive nature positions it well for future developments in cloud computing.