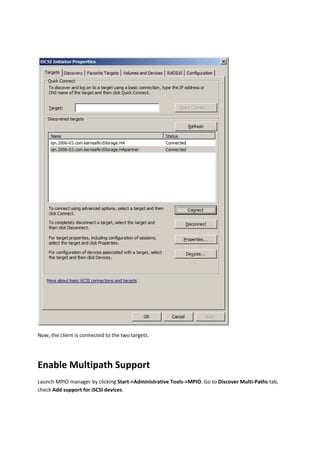
The document provides a comprehensive guide for configuring the Kernsafe iStorage server on Windows Server 2008, detailing steps for creating high availability (HA) storage, establishing applications, and connecting clients. It outlines the essential features of the iStorage server, including support for iSCSI targets, RAID-1, and multipath I/O. Additionally, it includes instructions for preparing HA storage on two servers and steps to connect and configure client systems.