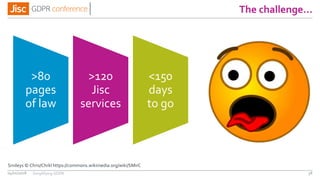
This document summarizes a presentation on getting to grips with the General Data Protection Regulation (GDPR). It discusses the challenges organizations face in complying with GDPR, which takes effect in May 2018. The presentation provides tips on where to get help with GDPR compliance, how to conduct an audit of personal data holdings, and the top 10 actions organizations should take now to prepare, such as forming an implementation task force and reviewing privacy policies and consent procedures. It emphasizes that May 25, 2018 marks the beginning of GDPR compliance obligations.











![Privacy notices
Master Notice
» Retention, transfers, exports,
security, exercising rights
»For each of
› “service you’ve requested”
› “identify problems or
improvements”
› “you asked us to”
› “operating service for 3rd party”
Jisc service approach, pending regulator guidance
04/01/2018 56
Per-service notice
(at point of collection)
» Purpose(s), link to master
» [Recipients/countries, directories,
ISO27001, DPIA, other options]
»For each of
› Transaction-based (eg helpdesk)
› Relationship-based (eg subscription)
› Consent-based (eg survey)
jisc.ac.uk/website/privacy-notice
Simplifying GDPR](https://image.slidesharecdn.com/gdprconferencefinalslidedeck-180104153201/85/Jisc-GDPR-conference-55-320.jpg)
![Possible employee privacy notices
Work-in-progress…
04/01/2018 59
Master Notice
» Retention, transfers, exports,
security, exercising rights
»For each of
› “purposes of employment”
› “law requires us to”
› Vital interests
› “identify problems or improvements”
› “you asked us to”
Per-service notice
(at point of collection)
» Purpose(s), link to master
» [Other options]
»Not (only) at point of collection
› That could be many years ago
› Probably a role for context-awareness
› eg reminders on communications?
jisc.ac.uk/website/privacy-notice
Simplifying GDPR](https://image.slidesharecdn.com/gdprconferencefinalslidedeck-180104153201/85/Jisc-GDPR-conference-58-320.jpg)










![I must recognise … that the [Data
Protection] Act [1998] is of notorious
obscurity…”
Lindsay J. in Douglas v. Hello! Ltd (No.7) (2004)
“Hold our beer…”
The GDPR & UK Data Protection Bill](https://image.slidesharecdn.com/gdprconferencefinalslidedeck-180104153201/85/Jisc-GDPR-conference-125-320.jpg)