- Bruno Borges is a Principal Cloud Developer Advocate at Microsoft who has been a Java developer since 2001 and focuses on developer relations.
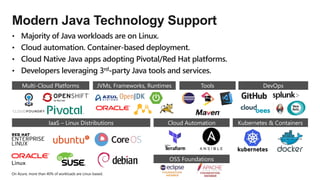
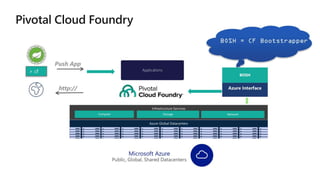
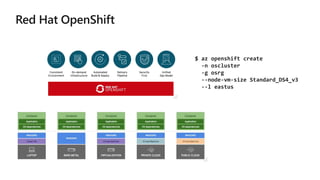
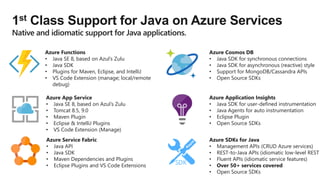
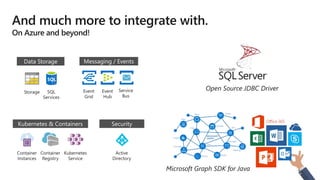
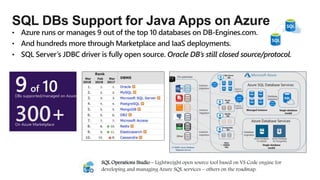
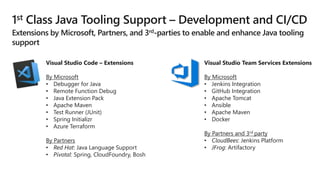
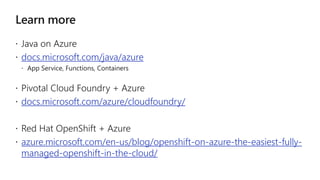
- The document discusses support for Java applications on Microsoft Azure, including infrastructure options like virtual machines, containers, and serverless computing. It also outlines first-class support for Java technologies and frameworks on various Azure services.