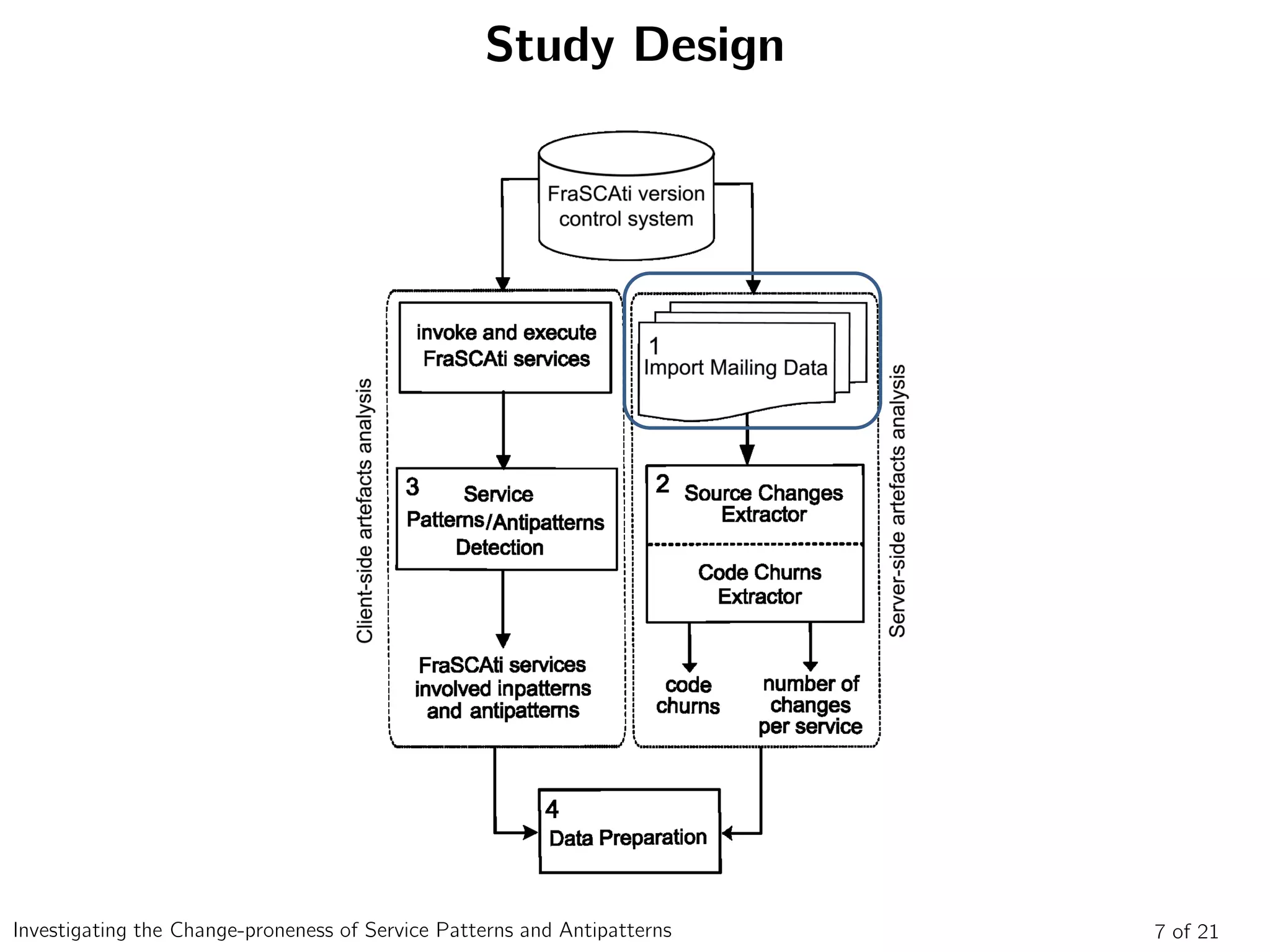
This commit modifies files in the FraSCAti system and contains refactoring. Specifically, it modifies two Java files, copies one Java file by changing its package, and removes two package paths. The commit log indicates it contains "More refactoring".
![Study Design: FraSCAti Commit
[[frascati-commits]] [1196] trunk/tinfi: More refactoring.
Subject: [[frascati-commits]] [1196] trunk/tinfi: More refactoring.
From: Lionel.Seinturier@xxxxxxx
Date: Sat, 13 Dec 2008 21:41:32 +0100 (CET)
Delivered-to: frascati-commits@xxxxxxx
Title: [1196] trunk/tinfi: More refactoring.
Revision
1196
Author
seintur
Date
2008-12-13 21:41:32 +0100 (Sat, 13 Dec 2008)
Log Message
More refactoring.
Modified Paths
trunk/tinfi/runtime/oo-dyn/src/main/java/org/ow2/frascati/tinfi/Tinfi.java
trunk/tinfi/runtime/oo-dyn/src/main/java/org/ow2/frascati/tinfi/TinfiBootstrapComponentImpl.java
Added Paths
trunk/tinfi/opt/comp/src/main/java/org/ow2/
trunk/tinfi/opt/comp/src/main/java/org/ow2/frascati/
trunk/tinfi/opt/comp/src/main/java/org/ow2/frascati/tinfi/
trunk/tinfi/opt/comp/src/main/java/org/ow2/frascati/tinfi/juliac/
trunk/tinfi/opt/comp/src/main/java/org/ow2/frascati/tinfi/juliac/FCCompCtrlSourceCodeGenerator.java
trunk/tinfi/opt/comp/src/main/java/org/ow2/frascati/tinfi/juliac/InitializerCompCtrlSourceCodeGenerator.java
Removed Paths
trunk/tinfi/opt/comp/src/main/java/org/scorware/
trunk/tinfi/runtime/oo-dyn/src/main/java/org/scorware/
Property Changed
trunk/tinfi/tinfi-mixed/
Diff
Copied:
trunk/tinfi/opt/comp/src/main/java/org/ow2/frascati/tinfi/juliac/FCCompCtrlSourceCodeGenerator.j
ava (from rev 1186,
trunk/tinfi/opt/comp/src/main/java/org/scorware/tinfi/juliac/FCCompCtrlSourceCodeGenerator.jav
a) (0 => 1196)
---
trunk/tinfi/opt/comp/src/main/java/org/ow2/frascati/tinfi/juliac/FCCompCtrlSourceCode
Generator.java (rev 0)
+++
trunk/tinfi/opt/comp/src/main/java/org/ow2/frascati/tinfi/juliac/FCCompCtrlSourceCode
Generator.java 2008-12-13 20:41:32 UTC (rev 1196)
@@ -0,0 +1,167 @@
+package org.ow2.frascati.tinfi.juliac;
+
+import java.io.IOException;
+
+import org.objectweb.fractal.api.control.AttributeController;
+import org.objectweb.fractal.api.type.InterfaceType;
+import org.objectweb.fractal.julia.control.attribute.CloneableAttributeController;
+import org.objectweb.fractal.julia.type.BasicInterfaceType;
+import org.objectweb.fractal.juliac.InitializerClassGenerator;
+import org.objectweb.fractal.juliac.Juliac;
+import org.objectweb.fractal.juliac.JuliacConfig;
+import org.objectweb.fractal.juliac.proxy.AttributeControllerClassGenerator;
+import org.objectweb.fractal.juliac.proxy.InterfaceImplementationClassGenerator;
+import org.objectweb.fractal.juliac.proxy.ProxyClassGenerator;
+import org.objectweb.fractal.juliac.ucf.UnifiedClass;
+import org.osoa.sca.annotations.Callback;
+
+/**
+public class FCCompCtrlSourceCodeGenerator
+extends org.objectweb.fractal.juliac.opt.comp.FCCompCtrlSourceCodeGenerator {
+
+ public FCCompCtrlSourceCodeGenerator() {
+ super();
+ }
+
+
+ // -----------------------------------------------------------------------
+ // Implementation of the OptLevelSourceCodeGenerator interface
+ // -----------------------------------------------------------------------
+
....
....
....
Modified: trunk/tinfi/runtime/oo-dyn/src/main/java/org/ow2/frascati/tinfi/Tinfi.java (1195 => 1196)
--- trunk/tinfi/runtime/oo-dyn/src/main/java/org/ow2/frascati/tinfi/Tinfi.java
2008-12-12 18:10:44 UTC (rev 1195)
+++ trunk/tinfi/runtime/oo-dyn/src/main/java/org/ow2/frascati/tinfi/Tinfi.java
2008-12-13 20:41:32 UTC (rev 1196)
@@ -21,7 +21,7 @@
* Author: Lionel Seinturier
*/
+package org.ow2.frascati.tinfi;
import org.objectweb.fractal.api.Component;
import org.objectweb.fractal.api.Type;
Modified: trunk/tinfi/runtime/oo-
dyn/src/main/java/org/ow2/frascati/tinfi/TinfiBootstrapComponentImpl.java (1195 => 1196)
--- trunk/tinfi/runtime/oo-
dyn/src/main/java/org/ow2/frascati/tinfi/TinfiBootstrapComponentImpl.java 2008-12-
12 18:10:44 UTC (rev 1195)
+++ trunk/tinfi/runtime/oo-
dyn/src/main/java/org/ow2/frascati/tinfi/TinfiBootstrapComponentImpl.java 2008-12-
13 20:41:32 UTC (rev 1196)
@@ -21,7 +21,7 @@
* Author: Lionel Seinturier](https://image.slidesharecdn.com/soca2014-160415202714/75/Investigating-the-Change-proneness-of-Service-Patterns-and-Antipatterns-18-2048.jpg)
![Study Design: FraSCAti Commit
[[frascati-commits]] [1196] trunk/tinfi: More refactoring.
Subject: [[frascati-commits]] [1196] trunk/tinfi: More refactoring.
From: Lionel.Seinturier@xxxxxxx
Date: Sat, 13 Dec 2008 21:41:32 +0100 (CET)
Delivered-to: frascati-commits@xxxxxxx
Title: [1196] trunk/tinfi: More refactoring.
Revision
1196
Author
seintur
Date
2008-12-13 21:41:32 +0100 (Sat, 13 Dec 2008)
Log Message
More refactoring.
Modified Paths
trunk/tinfi/runtime/oo-dyn/src/main/java/org/ow2/frascati/tinfi/Tinfi.java
trunk/tinfi/runtime/oo-dyn/src/main/java/org/ow2/frascati/tinfi/TinfiBootstrapComponentImpl.java
Added Paths
trunk/tinfi/opt/comp/src/main/java/org/ow2/
trunk/tinfi/opt/comp/src/main/java/org/ow2/frascati/
trunk/tinfi/opt/comp/src/main/java/org/ow2/frascati/tinfi/
trunk/tinfi/opt/comp/src/main/java/org/ow2/frascati/tinfi/juliac/
trunk/tinfi/opt/comp/src/main/java/org/ow2/frascati/tinfi/juliac/FCCompCtrlSourceCodeGenerator.java
trunk/tinfi/opt/comp/src/main/java/org/ow2/frascati/tinfi/juliac/InitializerCompCtrlSourceCodeGenerator.java
Removed Paths
trunk/tinfi/opt/comp/src/main/java/org/scorware/
trunk/tinfi/runtime/oo-dyn/src/main/java/org/scorware/
Property Changed
trunk/tinfi/tinfi-mixed/
Diff
Copied:
trunk/tinfi/opt/comp/src/main/java/org/ow2/frascati/tinfi/juliac/FCCompCtrlSourceCodeGenerator.j
ava (from rev 1186,
trunk/tinfi/opt/comp/src/main/java/org/scorware/tinfi/juliac/FCCompCtrlSourceCodeGenerator.jav
a) (0 => 1196)
---
trunk/tinfi/opt/comp/src/main/java/org/ow2/frascati/tinfi/juliac/FCCompCtrlSourceCode
Generator.java (rev 0)
+++
trunk/tinfi/opt/comp/src/main/java/org/ow2/frascati/tinfi/juliac/FCCompCtrlSourceCode
Generator.java 2008-12-13 20:41:32 UTC (rev 1196)
@@ -0,0 +1,167 @@
+package org.ow2.frascati.tinfi.juliac;
+
+import java.io.IOException;
+
+import org.objectweb.fractal.api.control.AttributeController;
+import org.objectweb.fractal.api.type.InterfaceType;
+import org.objectweb.fractal.julia.control.attribute.CloneableAttributeController;
+import org.objectweb.fractal.julia.type.BasicInterfaceType;
+import org.objectweb.fractal.juliac.InitializerClassGenerator;
+import org.objectweb.fractal.juliac.Juliac;
+import org.objectweb.fractal.juliac.JuliacConfig;
+import org.objectweb.fractal.juliac.proxy.AttributeControllerClassGenerator;
+import org.objectweb.fractal.juliac.proxy.InterfaceImplementationClassGenerator;
+import org.objectweb.fractal.juliac.proxy.ProxyClassGenerator;
+import org.objectweb.fractal.juliac.ucf.UnifiedClass;
+import org.osoa.sca.annotations.Callback;
+
+/**
+public class FCCompCtrlSourceCodeGenerator
+extends org.objectweb.fractal.juliac.opt.comp.FCCompCtrlSourceCodeGenerator {
+
+ public FCCompCtrlSourceCodeGenerator() {
+ super();
+ }
+
+
+ // -----------------------------------------------------------------------
+ // Implementation of the OptLevelSourceCodeGenerator interface
+ // -----------------------------------------------------------------------
+
....
....
....
Modified: trunk/tinfi/runtime/oo-dyn/src/main/java/org/ow2/frascati/tinfi/Tinfi.java (1195 => 1196)
--- trunk/tinfi/runtime/oo-dyn/src/main/java/org/ow2/frascati/tinfi/Tinfi.java
2008-12-12 18:10:44 UTC (rev 1195)
+++ trunk/tinfi/runtime/oo-dyn/src/main/java/org/ow2/frascati/tinfi/Tinfi.java
2008-12-13 20:41:32 UTC (rev 1196)
@@ -21,7 +21,7 @@
* Author: Lionel Seinturier
*/
+package org.ow2.frascati.tinfi;
import org.objectweb.fractal.api.Component;
import org.objectweb.fractal.api.Type;
Modified: trunk/tinfi/runtime/oo-
dyn/src/main/java/org/ow2/frascati/tinfi/TinfiBootstrapComponentImpl.java (1195 => 1196)
--- trunk/tinfi/runtime/oo-
dyn/src/main/java/org/ow2/frascati/tinfi/TinfiBootstrapComponentImpl.java 2008-12-
12 18:10:44 UTC (rev 1195)
+++ trunk/tinfi/runtime/oo-
dyn/src/main/java/org/ow2/frascati/tinfi/TinfiBootstrapComponentImpl.java 2008-12-
13 20:41:32 UTC (rev 1196)
@@ -21,7 +21,7 @@
* Author: Lionel Seinturier](https://image.slidesharecdn.com/soca2014-160415202714/75/Investigating-the-Change-proneness-of-Service-Patterns-and-Antipatterns-19-2048.jpg)