The document provides excerpts from various storyboard interactions that can be used for eLearning including:
- Click and reveal tabs to view corresponding content in an accordion style.
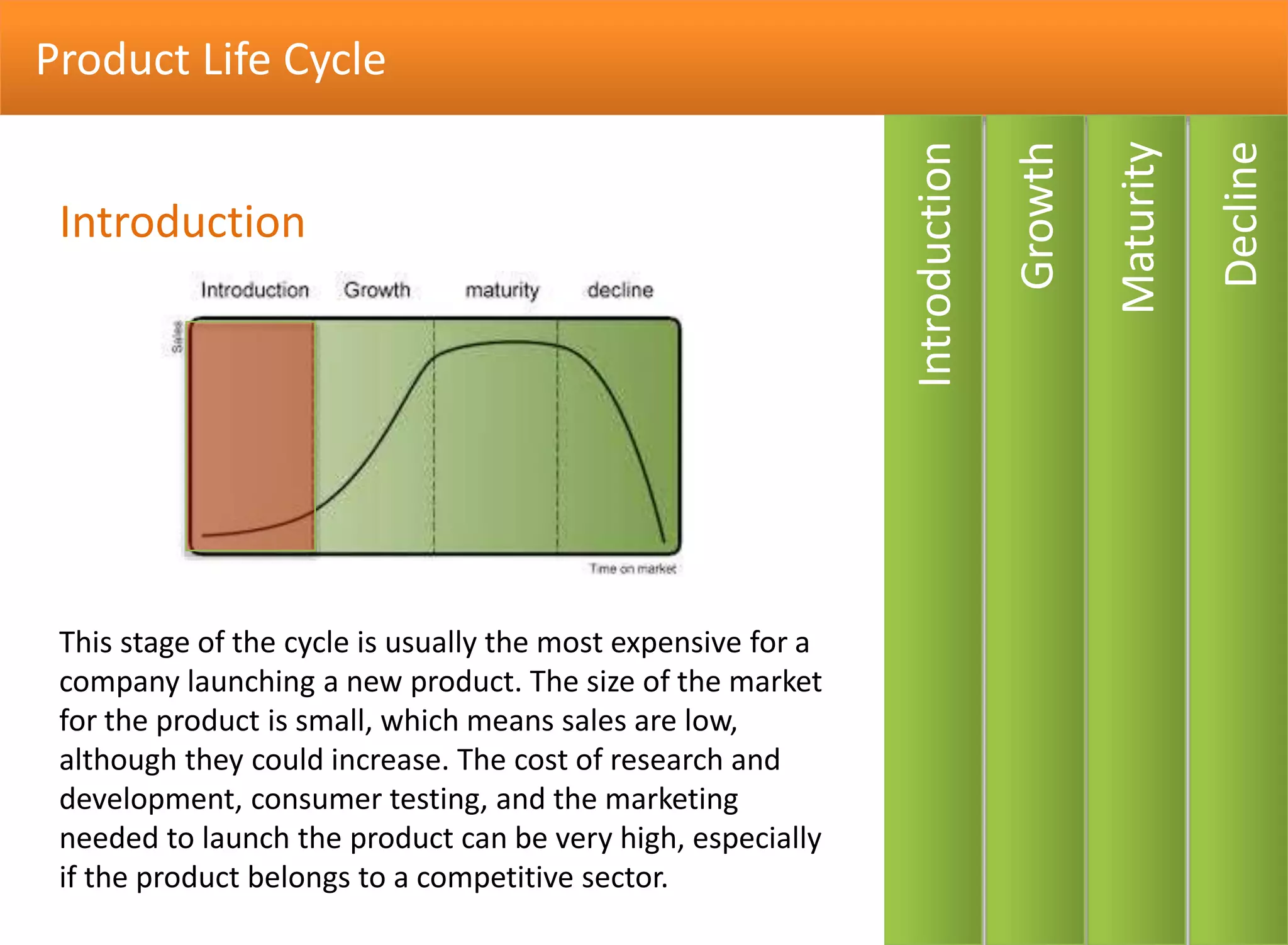
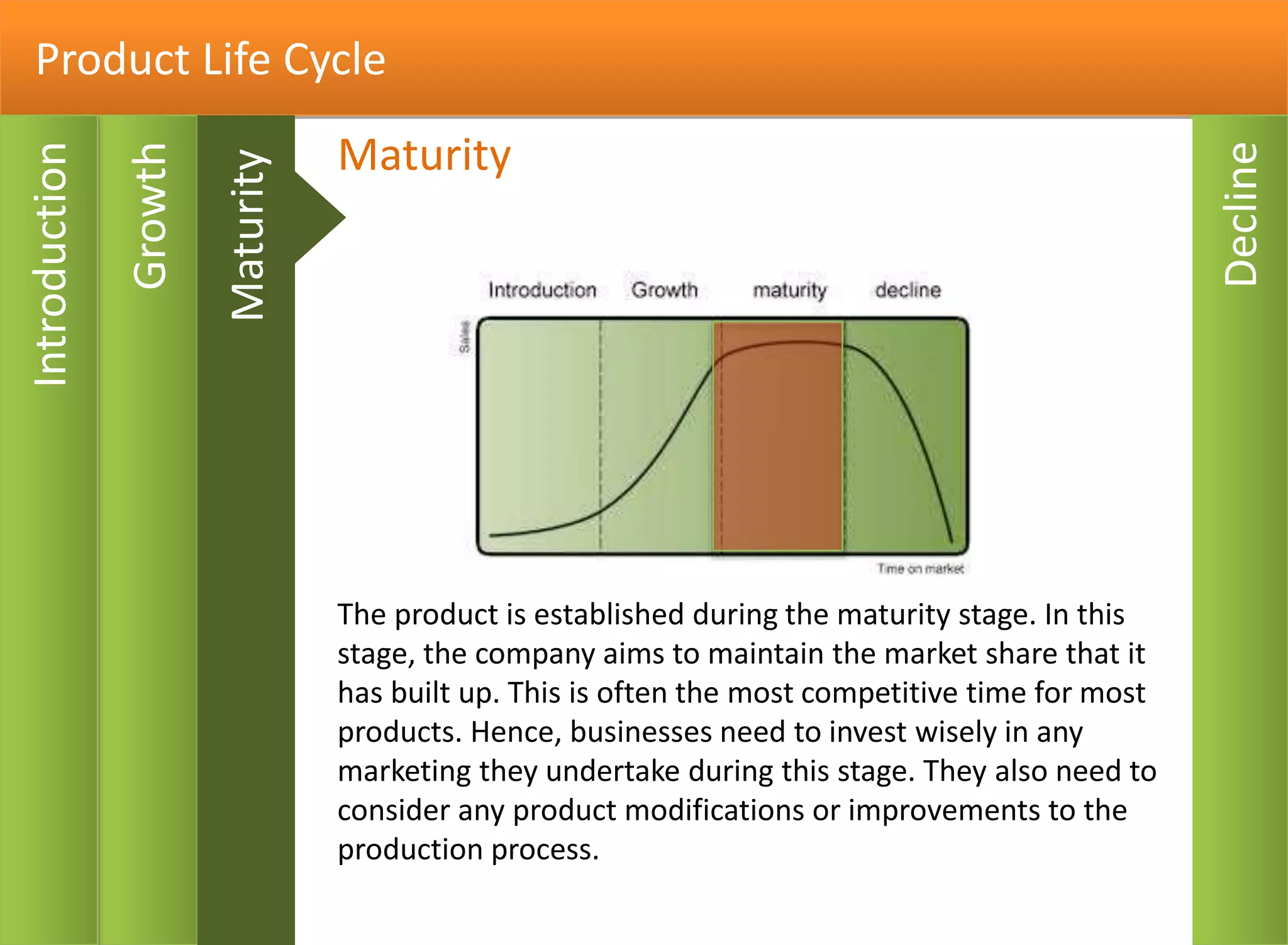
- A product life cycle storyboard that describes the introduction, growth, maturity, and decline stages.
- A click hotspot interaction to learn about employees in different departments.
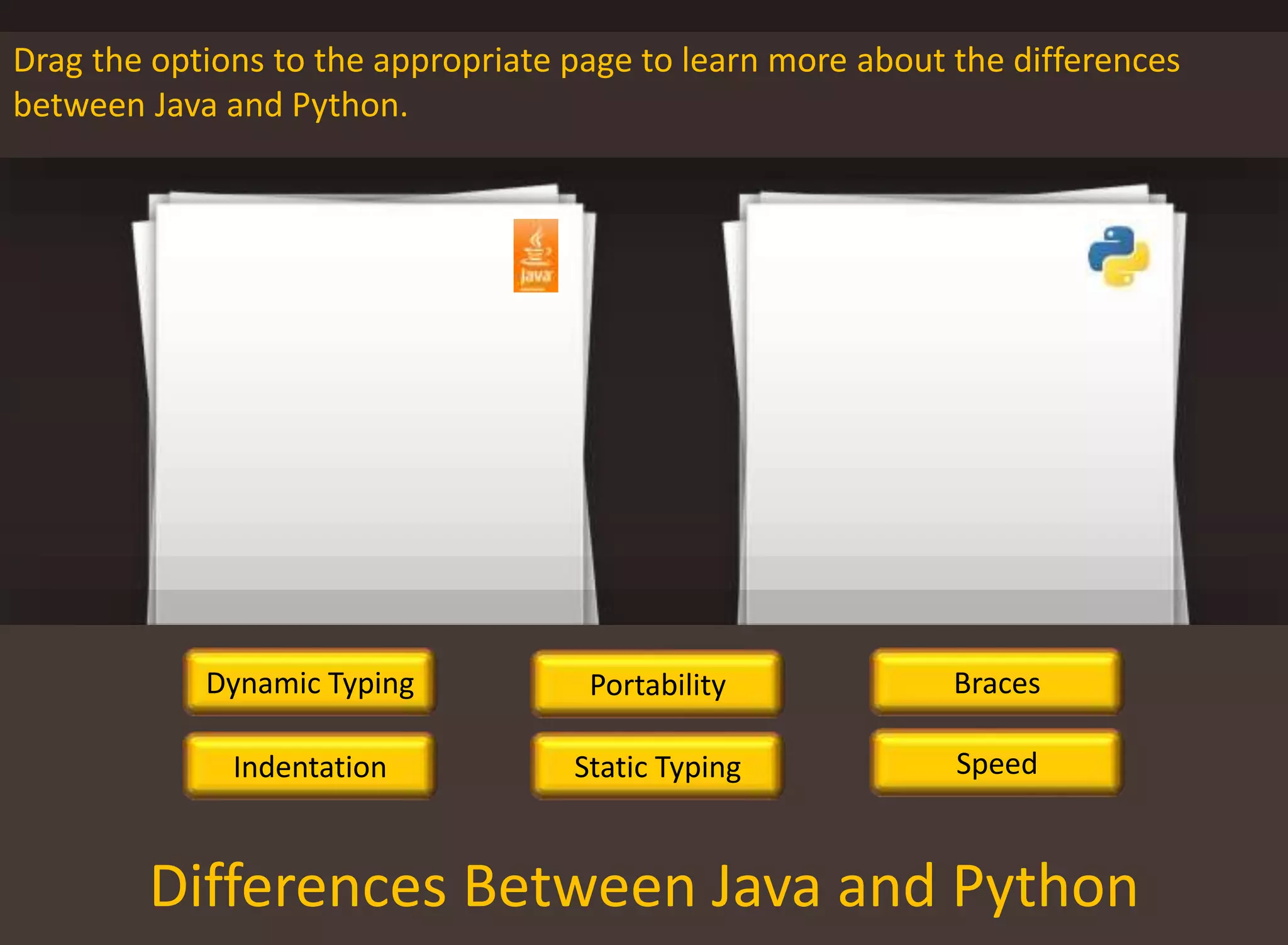
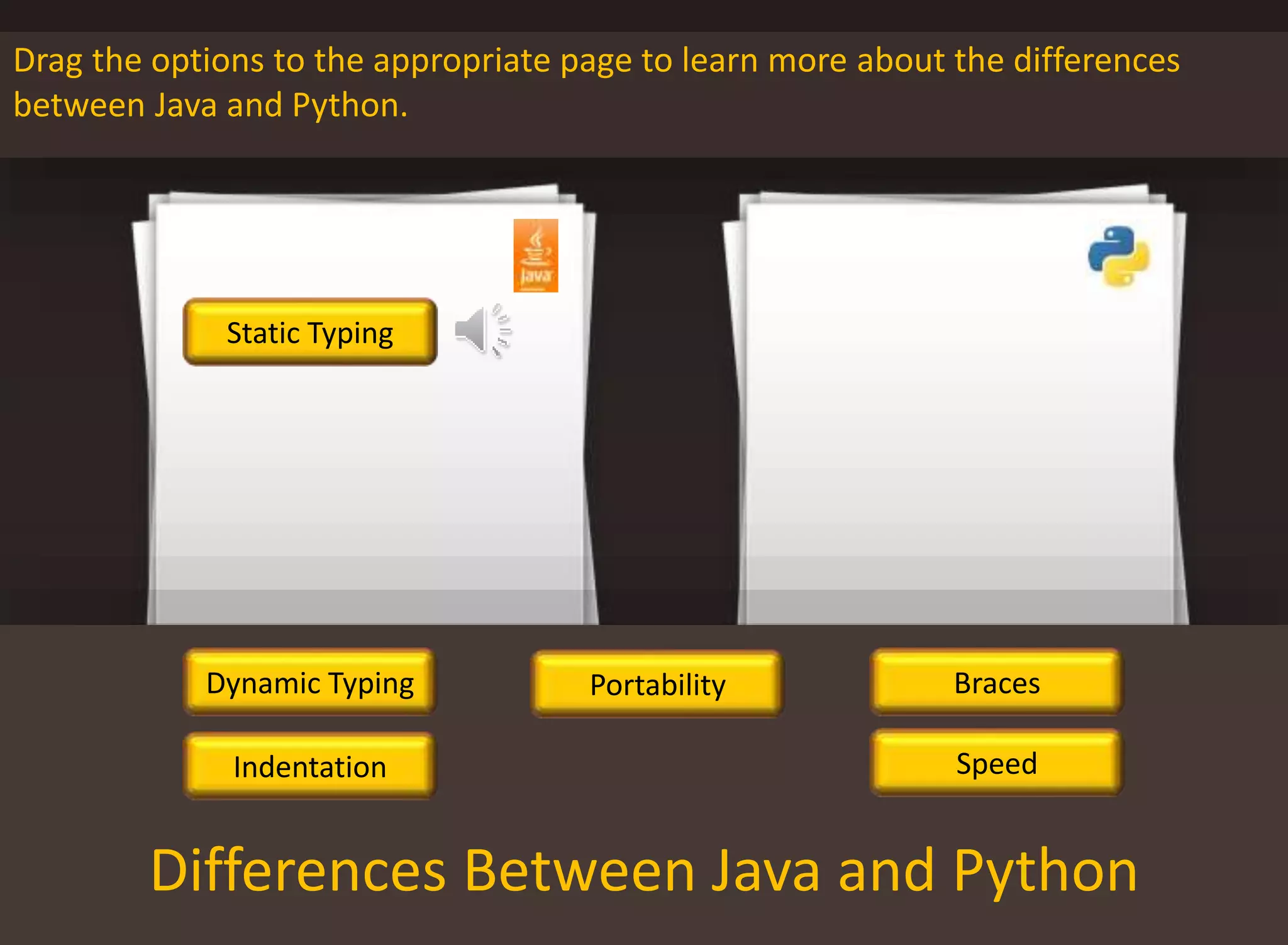
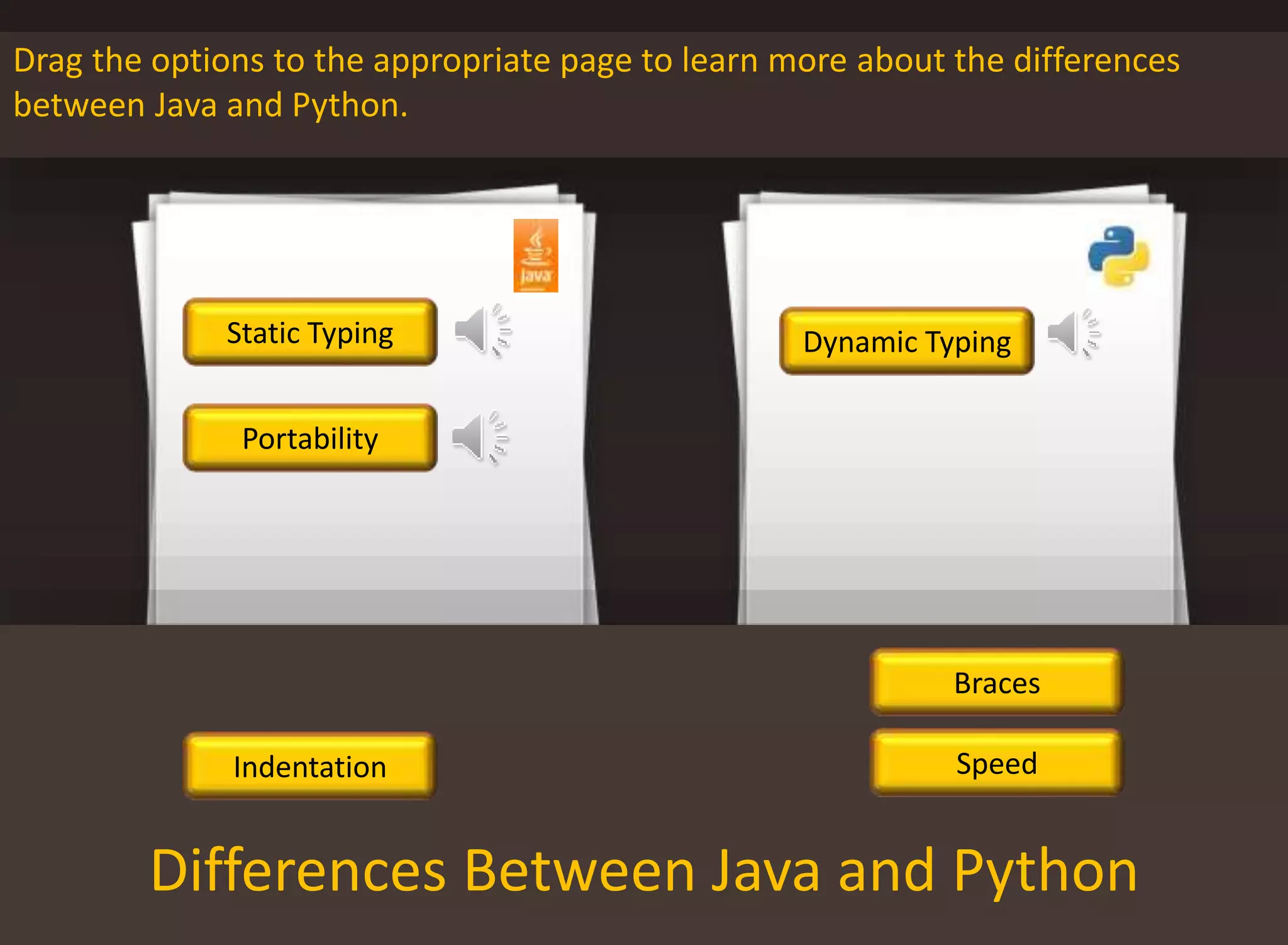
- A drag and drop text interaction to learn about differences between Java and Python by dragging options to pages.
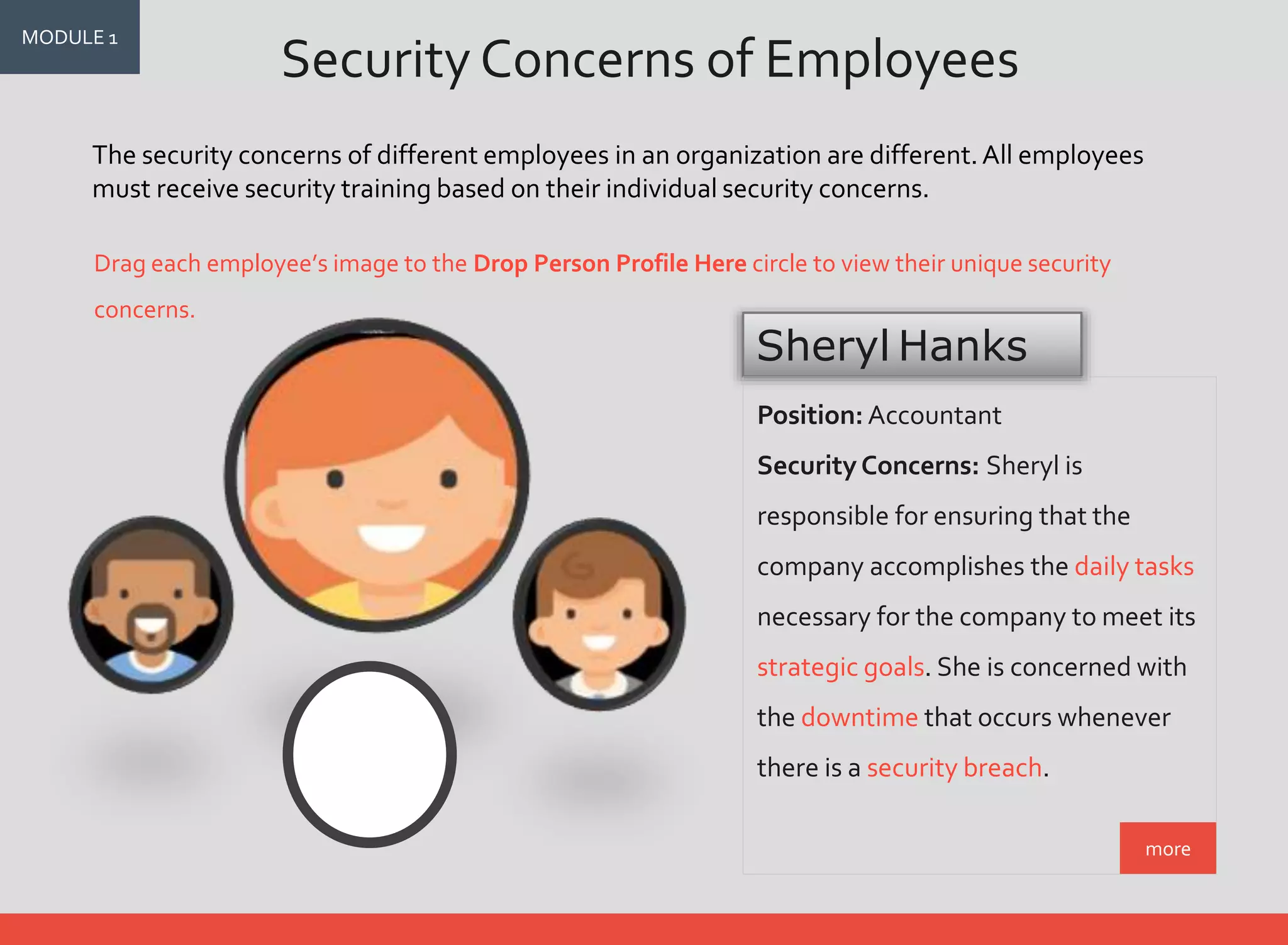
- A drag and drop image interaction where dragging employee images reveals their unique security concerns.