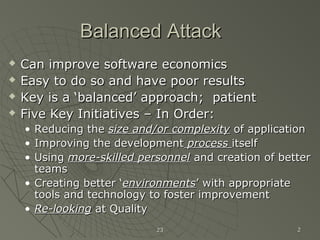
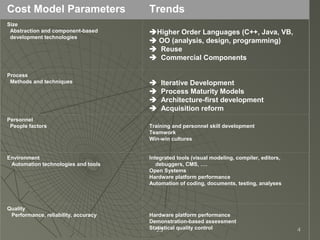
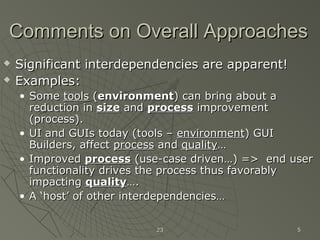
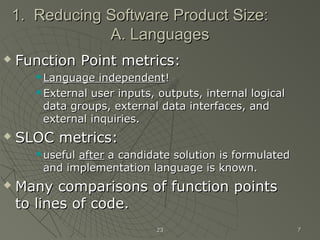
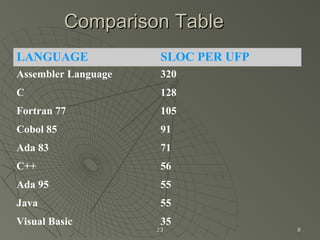
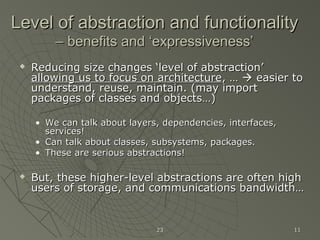
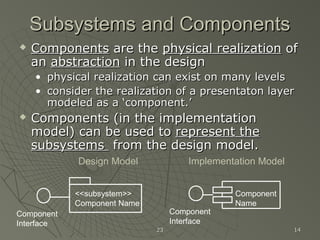
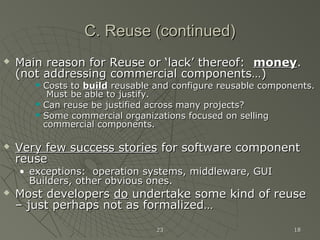
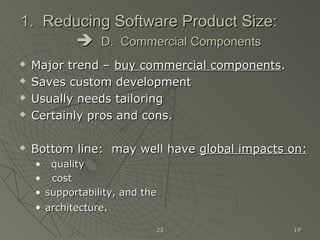
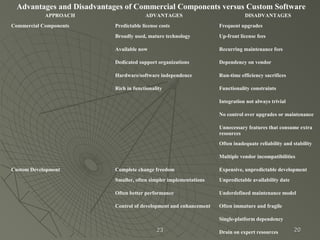
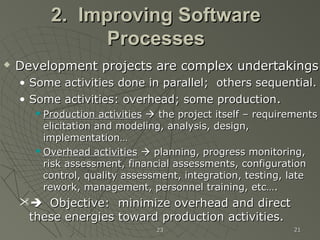
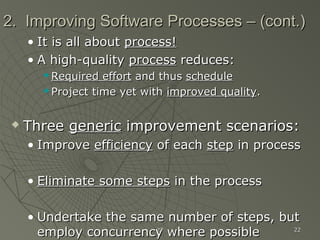
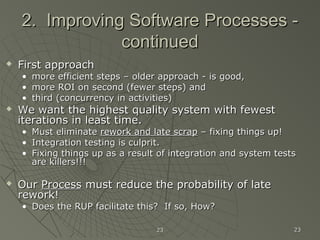
This document discusses improving software economics through a balanced approach of reducing application size and complexity, improving development processes, using skilled personnel, creating better environments, and focusing on quality. It focuses on reducing size, particularly through using higher-level programming languages, object-oriented methods and visual modeling, reuse, and commercial components. It also discusses improving software processes by making each step more efficient, eliminating unnecessary steps, and employing concurrency where possible.