ICTY Codebits 2014
•
2 likes•741 views
This document discusses how mobile devices can leak information about their users through WiFi signals, allowing others to potentially track individuals. It describes how an attacker can collect WiFi probes from devices to identify previously connected networks ("ESSIDs") and potentially link them to users. The document outlines the low-cost hardware and open-source software needed to conduct such tracking passively or aggressively. It provides metrics on the number of unique devices observed and those leaking ESSID information in certain locations. Finally, it discusses privacy and surveillance concerns raised by the passive collection of such wireless information from devices.
Report
Share
Report
Share
Recommended
Cyber Raksha - by Vanshit Malhotra

CHRIST College, Bangalore ! ️ Cyber Raksha - Talk on Cyber Security and Awareness. Delivered Seminar to MBA Final Year On Importance of Cyber Security for the Corporates !
My Initiative Cyber Raksha Aims is to Build a Culture of Cyber Safety education specially in Colleges, Schools and Corporates.
Lets Transform Digital India into a SECURE DIGITAL INDIA ️
[+] Buy and Implement Secure Technology
[+] Train Employees on Cyber Security - Don’t Spend all money on Secure Technology, train employees on Cyber Security.
[+] Use Secure Development frameworks for developing applications
[+] Understand how your application can be attacked.
Short Video of my Talk : https://youtu.be/z-sanhJsXtc
#CyberRaksha #Hackdoor #VanshitMalhotra #CyberSecurity #Infosec #SecureDigitalIndia #CyberSecurityAwareness #CyberSecurityTraining
The Mobile Device: The New Center of the Fraud Prevention Universe with Aite ...

iovation joins Aite Group to explore the emerging opportunities for businesses to:
* Leverage the mobile device to not only better secure mobile channel transactions but also add mobile security and enhance the user experience in all other channels.
* Harness valuable bank data and convert it into actionable intelligence.
* Plan for continued investment in remote channel security.
Creating a Winning Experience While Battling Online Fraud

You have a business with a big online presence and have dealt with fraud before - very likely in many forms and at many different customer touch points. Fraudsters are smart, so you must outsmart them.
At the same time, to ensure the success of your online presence, it's critical that you create the best and most engaging experience possible for your customers, attract new customers, retain those who are already loyal, and encourage all of them to spend more with you.
How can you do all of this while keeping fraudsters out to minimize your fraud losses?
With emerging technologies such as predictive, adaptive transaction scoring using real-time machine learning and device intelligence, along with frictionless customer authentication, it's easier than you think.
Cyber Warfare - Milan 2015

A short overview on communications. Which factors should affects your decisions?
How to choose the best secure communications suite that fits your needs?
Ecurity city pa solution

Security City PA Solution-MAG6000
This is a network public address solution powered by MAG6182.MAG6000 network is a multi-functional digital broadcasting system based on DSPPA contract and compatible with TCP/IP contract. With the supporting accessories of MAG6406 and MAG6408, the MAG6000 system can be installed in the public spaces of the city to reinforce the public security.
Application: street, station square, tourist spot, community, etc.
Features:
Use the network to transfer signal, combine the network together to set up an outdoor interaction alarm system.
Apply the Unicast technology, spot-to-spot transmission, reinforce the reliability of the network.
The control host is compatible with terminals with different functions, responds respectively to different demands of each terminal, provides characteristic service.
The control host can respond to the emergency demand of the terminals in time, set up the data transmission between the emergency terminal and the appointed monitor terminal to fulfill the real-time speech between the the emergency terminal and the monitor spot.
There are warning light, status indicator, microphone, loudspeaker and SOS button on the outdoor emergency terminals.
They can be found and used easily.
The outdoor emergency terminals have waterproof function.
The outdoor emergency terminals have voice alert function.
Apparatus:
MAG6182—Network Public Address Center
MAG6406—Emergency terminal in box formation
MAG6408—Emergency terminal in column formation
MAG6588—Network paging microphone
MAG6588 is a network full digital signal processor Hi-Fi paging station based on TCP/IP protocol. With dual network interface design, it can be connect to anywhere the network reaches. Able to paging to up to 1000 zones, running stable, low failure rate; Digital signal transmission and intelligent control; With 7 inch true color LCD display, touch panel, customer-friendly operation interface; With aux input and output, make it possible for amplifier extension; Built-in player developed by DSPPA, realize local monitoring of system center program.
Features:
● Support up to 1000 zones, with one-touch all-zone-on function
● Support zone paging and group paging; view zones status
● TCP/IP transmission protocol, compatible with WAN/LAN shared network
● 7 inch TFT LCD screen with graphical interface display and touch screen control panel
● Built-in program player, program sources of host can be local monitoring
Recommended
Cyber Raksha - by Vanshit Malhotra

CHRIST College, Bangalore ! ️ Cyber Raksha - Talk on Cyber Security and Awareness. Delivered Seminar to MBA Final Year On Importance of Cyber Security for the Corporates !
My Initiative Cyber Raksha Aims is to Build a Culture of Cyber Safety education specially in Colleges, Schools and Corporates.
Lets Transform Digital India into a SECURE DIGITAL INDIA ️
[+] Buy and Implement Secure Technology
[+] Train Employees on Cyber Security - Don’t Spend all money on Secure Technology, train employees on Cyber Security.
[+] Use Secure Development frameworks for developing applications
[+] Understand how your application can be attacked.
Short Video of my Talk : https://youtu.be/z-sanhJsXtc
#CyberRaksha #Hackdoor #VanshitMalhotra #CyberSecurity #Infosec #SecureDigitalIndia #CyberSecurityAwareness #CyberSecurityTraining
The Mobile Device: The New Center of the Fraud Prevention Universe with Aite ...

iovation joins Aite Group to explore the emerging opportunities for businesses to:
* Leverage the mobile device to not only better secure mobile channel transactions but also add mobile security and enhance the user experience in all other channels.
* Harness valuable bank data and convert it into actionable intelligence.
* Plan for continued investment in remote channel security.
Creating a Winning Experience While Battling Online Fraud

You have a business with a big online presence and have dealt with fraud before - very likely in many forms and at many different customer touch points. Fraudsters are smart, so you must outsmart them.
At the same time, to ensure the success of your online presence, it's critical that you create the best and most engaging experience possible for your customers, attract new customers, retain those who are already loyal, and encourage all of them to spend more with you.
How can you do all of this while keeping fraudsters out to minimize your fraud losses?
With emerging technologies such as predictive, adaptive transaction scoring using real-time machine learning and device intelligence, along with frictionless customer authentication, it's easier than you think.
Cyber Warfare - Milan 2015

A short overview on communications. Which factors should affects your decisions?
How to choose the best secure communications suite that fits your needs?
Ecurity city pa solution

Security City PA Solution-MAG6000
This is a network public address solution powered by MAG6182.MAG6000 network is a multi-functional digital broadcasting system based on DSPPA contract and compatible with TCP/IP contract. With the supporting accessories of MAG6406 and MAG6408, the MAG6000 system can be installed in the public spaces of the city to reinforce the public security.
Application: street, station square, tourist spot, community, etc.
Features:
Use the network to transfer signal, combine the network together to set up an outdoor interaction alarm system.
Apply the Unicast technology, spot-to-spot transmission, reinforce the reliability of the network.
The control host is compatible with terminals with different functions, responds respectively to different demands of each terminal, provides characteristic service.
The control host can respond to the emergency demand of the terminals in time, set up the data transmission between the emergency terminal and the appointed monitor terminal to fulfill the real-time speech between the the emergency terminal and the monitor spot.
There are warning light, status indicator, microphone, loudspeaker and SOS button on the outdoor emergency terminals.
They can be found and used easily.
The outdoor emergency terminals have waterproof function.
The outdoor emergency terminals have voice alert function.
Apparatus:
MAG6182—Network Public Address Center
MAG6406—Emergency terminal in box formation
MAG6408—Emergency terminal in column formation
MAG6588—Network paging microphone
MAG6588 is a network full digital signal processor Hi-Fi paging station based on TCP/IP protocol. With dual network interface design, it can be connect to anywhere the network reaches. Able to paging to up to 1000 zones, running stable, low failure rate; Digital signal transmission and intelligent control; With 7 inch true color LCD display, touch panel, customer-friendly operation interface; With aux input and output, make it possible for amplifier extension; Built-in player developed by DSPPA, realize local monitoring of system center program.
Features:
● Support up to 1000 zones, with one-touch all-zone-on function
● Support zone paging and group paging; view zones status
● TCP/IP transmission protocol, compatible with WAN/LAN shared network
● 7 inch TFT LCD screen with graphical interface display and touch screen control panel
● Built-in program player, program sources of host can be local monitoring
Facebook Cheat Sheet 

This is a handy reference tool especially for the designers who need to know image sizes for Facebook fan pages. Use this cheat sheet infographic and you’ll never have to guess the dimensions again!
Top 10 Google Chrome Extensions for Your Social Media Strategy

Our Social Media Executive, Ollie Whitfield shares his favourite 10 Chrome extensions for rocking your social media strategy.
Captiv8 Top 25 Tips for Social Media

Presented at the Launch Scale Conference in 2015
Channels Covered
Instagram
YouTube
Vine
Wrangle the tech!

Learn about web-based tools to help you manage your day-to-day. Some of these tools have been around for a while, some are still new, but all are helpful! If you're trying to increase your productivity, take a look. Most of these tools are web-based, many are free. Presented at the Hawaii Library Association 2014 Conference.
13 Eye-popping facts about Facebook 

Facebook marketing is extremely important in the present day with 7 digit numbers in statistics about users, revenue and other stats on Facebook.
Creating Living Style Guides to Improve Performance

Refactoring Trulia’s UI with SASS, OOCSS, and handlebars. My slides from jsconf 2013. Lot's of yummy details about the performance improvements we were able to make.
14 Really Useful Websites

Want to save time, money, the environment, and your sanity? Here are some really useful websites to do all of that and more!
Content With Intent

Content is one of those things that you hear banded around a lot. Nowadays, much of it is distributed via social, including video, animation, images, infographics, and the list goes on.
Developing a method for approaching content planning, production, distribution, and optimization is critical for every brand. This presentation introduces Content NOW, a three-part process designed to drive results through content, and discusses:
- How content tripled six figure sales targets for one client
- How content production techniques are increasing in store footfall
- How content created one of the largest increase in brand love score since records began
Teaching Cloud to the Programmers of Tomorrow

Academic case study from RGU on using cloud services in teaching and research.
Google Tips and Tricks - "I didn't know I could do that in Google!"

Google tips and tricks presentation to educators on Nov. 6, 2014 at BIT14 (ECOO) in Niagara Falls Ontario Canada.
199 Social Media and Content Marketing Tools

The life of a social media manager, content creator, or overall online marketer can be a stressful one. There's so much to do and so much to think about it can get a bit hectic.
Luckily, there's software out there that can help us get our jobs done faster, easier, and more efficiently. These tools organize our lives, automate our jobs, and maximize the ROI of our efforts.
Here are 199 content and social media marketing tools. Are there any we missed that you love?
50 Connected Devices - How Mobile and the Internet of Things Will Affect You

What happens when everything we touch is connected to the Internet? Welcome to the Internet of Things (IoT). At Crittercism, we live and breathe mobile. Browse this presentation to learn about the connected devices all around you – in your pocket, on your kitchen counter, in your backyard.
Want to learn more about how Crittercism can help your connected devices and IoT strategy? Visit http://bit.ly/OptimizeIoT today
Object Oriented CSS

How do you scale CSS for millions of visitors or thousands of pages? The slides from Nicole's presentation at Web Directions North in Denver will show you how to use Object Oriented CSS to write fast, maintainable, standards-based front end code. Adds much needed predictability to CSS so that even beginners can participate in writing beautiful, standards-compliant, fast websites.
Bad SEO Habits Meetup

In our Bad SEO Habits Meetup, seasoned digital marketing experts discuss a variety of SEO mistakes, dangerous habits to avoid, as well as give many helpful tips and tricks on improving your SEO strategy!
Peter Mead covers the most important ins and outs of Wordpress SEO.
Sha Menz continues with a super informative review on How To Beat Bad SEO Habits Before They Appear.
Tim Capper closes with a great presentation on developing a successful Local SEO strategy.
TIME's 50 Best Websites of 2014

Created with Haiku Deck, presentation software that's simple, beautiful and fun. Learn more and get Haiku Deck: www.haikudeck.com
7 Must-try Marketing Strategies for 2017

2017 has arrived - the time has never been better to give your marketing campaigns a face-lift.
Join WordStream founder, Larry Kim, as he reveals 7 Must-try Marketing Strategies for 2017.
This live webinar will cover:
- How to get better placement with lower cost per click on Google AdWords
- How and why to build engagement ads
- How to target your competition's target audiences
91 Free Twitter Tools and Apps to Fit Any Need

We’ve collected a great bunch of free tools for Twitter - all the tools we’ve found helpful and many more that we’re excited to try. If there’s a free Twitter tool out there, you’re likely to find a mention here in our list.
20 Facebook, Twitter, Linkedin & Pinterest Features You Didn't Know Existed (...

Learn about some of the lesser-known features on your favorite social networks.
Privacy is an Illusion and you’re all losers! - Cryptocow - Infosecurity 2013

Privacy is an illusion and you’re all losers!
or how 1984 was a manual for our panopticon society
By Cain Ransbottyn - @ransbottyn
More Related Content
Viewers also liked
Facebook Cheat Sheet 

This is a handy reference tool especially for the designers who need to know image sizes for Facebook fan pages. Use this cheat sheet infographic and you’ll never have to guess the dimensions again!
Top 10 Google Chrome Extensions for Your Social Media Strategy

Our Social Media Executive, Ollie Whitfield shares his favourite 10 Chrome extensions for rocking your social media strategy.
Captiv8 Top 25 Tips for Social Media

Presented at the Launch Scale Conference in 2015
Channels Covered
Instagram
YouTube
Vine
Wrangle the tech!

Learn about web-based tools to help you manage your day-to-day. Some of these tools have been around for a while, some are still new, but all are helpful! If you're trying to increase your productivity, take a look. Most of these tools are web-based, many are free. Presented at the Hawaii Library Association 2014 Conference.
13 Eye-popping facts about Facebook 

Facebook marketing is extremely important in the present day with 7 digit numbers in statistics about users, revenue and other stats on Facebook.
Creating Living Style Guides to Improve Performance

Refactoring Trulia’s UI with SASS, OOCSS, and handlebars. My slides from jsconf 2013. Lot's of yummy details about the performance improvements we were able to make.
14 Really Useful Websites

Want to save time, money, the environment, and your sanity? Here are some really useful websites to do all of that and more!
Content With Intent

Content is one of those things that you hear banded around a lot. Nowadays, much of it is distributed via social, including video, animation, images, infographics, and the list goes on.
Developing a method for approaching content planning, production, distribution, and optimization is critical for every brand. This presentation introduces Content NOW, a three-part process designed to drive results through content, and discusses:
- How content tripled six figure sales targets for one client
- How content production techniques are increasing in store footfall
- How content created one of the largest increase in brand love score since records began
Teaching Cloud to the Programmers of Tomorrow

Academic case study from RGU on using cloud services in teaching and research.
Google Tips and Tricks - "I didn't know I could do that in Google!"

Google tips and tricks presentation to educators on Nov. 6, 2014 at BIT14 (ECOO) in Niagara Falls Ontario Canada.
199 Social Media and Content Marketing Tools

The life of a social media manager, content creator, or overall online marketer can be a stressful one. There's so much to do and so much to think about it can get a bit hectic.
Luckily, there's software out there that can help us get our jobs done faster, easier, and more efficiently. These tools organize our lives, automate our jobs, and maximize the ROI of our efforts.
Here are 199 content and social media marketing tools. Are there any we missed that you love?
50 Connected Devices - How Mobile and the Internet of Things Will Affect You

What happens when everything we touch is connected to the Internet? Welcome to the Internet of Things (IoT). At Crittercism, we live and breathe mobile. Browse this presentation to learn about the connected devices all around you – in your pocket, on your kitchen counter, in your backyard.
Want to learn more about how Crittercism can help your connected devices and IoT strategy? Visit http://bit.ly/OptimizeIoT today
Object Oriented CSS

How do you scale CSS for millions of visitors or thousands of pages? The slides from Nicole's presentation at Web Directions North in Denver will show you how to use Object Oriented CSS to write fast, maintainable, standards-based front end code. Adds much needed predictability to CSS so that even beginners can participate in writing beautiful, standards-compliant, fast websites.
Bad SEO Habits Meetup

In our Bad SEO Habits Meetup, seasoned digital marketing experts discuss a variety of SEO mistakes, dangerous habits to avoid, as well as give many helpful tips and tricks on improving your SEO strategy!
Peter Mead covers the most important ins and outs of Wordpress SEO.
Sha Menz continues with a super informative review on How To Beat Bad SEO Habits Before They Appear.
Tim Capper closes with a great presentation on developing a successful Local SEO strategy.
TIME's 50 Best Websites of 2014

Created with Haiku Deck, presentation software that's simple, beautiful and fun. Learn more and get Haiku Deck: www.haikudeck.com
7 Must-try Marketing Strategies for 2017

2017 has arrived - the time has never been better to give your marketing campaigns a face-lift.
Join WordStream founder, Larry Kim, as he reveals 7 Must-try Marketing Strategies for 2017.
This live webinar will cover:
- How to get better placement with lower cost per click on Google AdWords
- How and why to build engagement ads
- How to target your competition's target audiences
91 Free Twitter Tools and Apps to Fit Any Need

We’ve collected a great bunch of free tools for Twitter - all the tools we’ve found helpful and many more that we’re excited to try. If there’s a free Twitter tool out there, you’re likely to find a mention here in our list.
20 Facebook, Twitter, Linkedin & Pinterest Features You Didn't Know Existed (...

Learn about some of the lesser-known features on your favorite social networks.
Viewers also liked (20)
Top 10 Google Chrome Extensions for Your Social Media Strategy

Top 10 Google Chrome Extensions for Your Social Media Strategy
Creating Living Style Guides to Improve Performance

Creating Living Style Guides to Improve Performance
Google Tips and Tricks - "I didn't know I could do that in Google!"

Google Tips and Tricks - "I didn't know I could do that in Google!"
50 Connected Devices - How Mobile and the Internet of Things Will Affect You

50 Connected Devices - How Mobile and the Internet of Things Will Affect You
The Human Body in the IoT. Tim Cannon + Ryan O'Shea

The Human Body in the IoT. Tim Cannon + Ryan O'Shea
20 Facebook, Twitter, Linkedin & Pinterest Features You Didn't Know Existed (...

20 Facebook, Twitter, Linkedin & Pinterest Features You Didn't Know Existed (...
Similar to ICTY Codebits 2014
Privacy is an Illusion and you’re all losers! - Cryptocow - Infosecurity 2013

Privacy is an illusion and you’re all losers!
or how 1984 was a manual for our panopticon society
By Cain Ransbottyn - @ransbottyn
iParanoid: an IMSI Catcher - Stingray Intrusion Detection System

The goal is the research and development of Intrusion Detection System related with Cell Networks.
Mainly this App will check the status of some Cell Network variables (e.g. Cellid, LAC, A5 Encryption, etc.) subsequently update a local DB and check if the information about the cell networks around the users are valid or if there could be a risk (e.g. possible interception, possible impersonation, etc.).
World of Signals - Devices - Connectivity - Signals - RF - Cyber Security.

This is a simple presentation I did towards a non-technical audience as part of a seminar on Cyber Security in Malaysia - Kuala Lumpur. It covers a wide range of specific topics relating to cyber security issues. We are all connected to a huge amount of devices and the attack vector is growing, widening. Building walls and fences is not enough. There is a lack of On The Ground Cyber Security...
Perfect Information - How IoT empowers you to know anything, anytime, anywhere

The Internet of Things (IoT) is the largest source of data in human history. How will you use the information it provides?
IoT: Entering an Era of Perfect Information

How the Internet of Things empowers you to know anything, anytime, anywhere.
Simon Harrison RWE - Chain of Things 010616 final

Opening presentation from a Blockchain/IoT event in London on 1st June 2016
How the Internet of Things (IoT) Works for Business

Brief introduction to the Internet of Things in the context of a tool for business -- specifically tech startups.
Internet of things - what is really happening

An attampt to map the current status of Internet of Things markets and technologies
Is there such a thing as the internet of things !

Is there such a thing as the internet of things, a keynote given during the "Forum Same" at Sophia-Antipolis, October 2nd, 2014 - English
Witness Angel Initiative (PyConFr 2019)

The Witness Angel is your judicial testimony, irrefutable and inviolable.
It acts like a digital memory, but which can never be accessed outside a proper judicial complaint.
Thanks to its innovative write-only encryption, it overcomes the opposition between protection of privacy and recording of judicial proofs.
Discover here how it works, with some technical details on its first implementation.
IoT Mobility Forensics

The Internet of Things (IoT) comes with great possibilities as well as major security and privacy issues. Although digital forensics has long been studied in both academia and industry, mobility forensics is relatively new and unexplored. Mobility forensics deals with tools and techniques that work towards forensically sound recovery of data and evidence from mobile devices [1]. In this paper, we explore mobility forensics in the context of IoT. This paper discusses the data collection and classification process from IoT smart home devices in details. It also contains attack scenario based analysis of collected data and a proposed mobility forensics model that fits into such scenarios.
Cite: K. M. S. Rahman, M. Bishop, and A. Holt, “Internet of Things Mobility Forensics,” INSuRE Conference, 2016.
Ethics in development of Information Technology

When people are asked to give their opinion about technology as a whole, they seem to think in a more of a black-and-white way, a binary approach. Many people express that technology is more of a ‘job-destroyer’, ‘something which enslaves humans by making them dependent on itself’, some also say that it ‘makes us lazy and equips us with God-ly powers’, etc. However, in contrast to these points, other people claim that it’s ‘something which induces progress into the society’, ‘something that saves human lives and feeds the starving and the poor’, ‘which increases the standard of living’, and ‘which creates interesting and rewarding jobs’.
Speaking about the development, we, as people who are studying Information Technology, have learnt that the enormous field of Internet of Things (IoT) focusses on developing internet-connected applications which will make our lives easier and comfortable. In addition to the principles and practices which are expected to be followed during the development of the applications, there are some lesser emphasized facts too. These facts include an important factor of ETHICS.
Humans are accustomed to follow some ethics right from our birth, rather we are induced these ethics by our elders. The reason is quite simple – for the betterment of the society and to avoid any evil exploitation of the lesser intelligent people. However, modern capitalism tends to bend the traditional ethics. People resort to ease and comfort over what is right.
A lot of subtopics fall under the wide section of Ethics. They include:
1. Characterizing the Internet of Things
2. Privacy (Of the users as well as their valuable data)
3. Control (Who actually controls the collected data)
4. Environment (Concerns about the environment and practices)
5. Solutions (for the preservation of the principle of Ethics)
In this slide show, we are going to emphasize on the initial couple of topics.
Behavioral Analytics with Smartphone Data. Talk at Strata + Hadoop World 2014...

Joerg Blumtritt, Datarella, at Strata+Hadoop World 2014, Barcelona
Smartphones are the most common wearable devices. In every single smartphone, more than 20 sensors continuously track all kind of behavioral and environmental data, from geo-location to even remote influences like magnetic field and local gravitation.
To develop meaningful models of users’ behavior, we need to put the technical measurements into context. This is done via interactions with an app. We at Datarella trigger the interactions on the phone by geo-fencing (coming near a pre-defined location, e.g. a retailer’s outlet), and other “complex events” using an Event Processing Language (EPL) and a Complex Event Processing Engine (CEPE).
We want also show best practices how to deal with privacy and informational self-determination, and how to give users a fair deal and transparancy to the data, that we collect by their cooperation in our projects.
Get the Strata + Hadoop World in Barcelona 2014 Complete Video Compilation here: http://strataconf.com/strataeu2014/public/sv/q/608
Internet of Things.pptx

The Internet of things describes physical objects with sensors, processing ability, software, and other technologies that connect and exchange data with other devices and systems over the Internet or other communications networks.
Digital Footprint in our world

A person's “digital footprint” reflects how he or she actively participates in the digital universe, including use of the Internet and social networks, e-mail, cell phones, digital cameras and credit cards.
Similar to ICTY Codebits 2014 (20)
Privacy is an Illusion and you’re all losers! - Cryptocow - Infosecurity 2013

Privacy is an Illusion and you’re all losers! - Cryptocow - Infosecurity 2013
iParanoid: an IMSI Catcher - Stingray Intrusion Detection System

iParanoid: an IMSI Catcher - Stingray Intrusion Detection System
World of Signals - Devices - Connectivity - Signals - RF - Cyber Security.

World of Signals - Devices - Connectivity - Signals - RF - Cyber Security.
Perfect Information - How IoT empowers you to know anything, anytime, anywhere

Perfect Information - How IoT empowers you to know anything, anytime, anywhere
How the Internet of Things (IoT) Works for Business

How the Internet of Things (IoT) Works for Business
Behavioral Analytics with Smartphone Data. Talk at Strata + Hadoop World 2014...

Behavioral Analytics with Smartphone Data. Talk at Strata + Hadoop World 2014...
Exploring the Opportunities of Internet of Things (IoT)

Exploring the Opportunities of Internet of Things (IoT)
Recently uploaded
History+of+E-commerce+Development+in+China-www.cfye-commerce.shop

History+of+E-commerce+Development+in+China-www.cfye-commerce.shop
一比一原版(SLU毕业证)圣路易斯大学毕业证成绩单专业办理

SLU毕业证原版定制【微信:176555708】【圣路易斯大学毕业证成绩单-学位证】【微信:176555708】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
◆◆◆◆◆ — — — — — — — — 【留学教育】留学归国服务中心 — — — — — -◆◆◆◆◆
【主营项目】
一.毕业证【微信:176555708】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【微信:176555708】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分→ 【关于价格问题(保证一手价格)
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
学历顾问:微信:176555708
急速办(bedfordhire毕业证书)英国贝德福特大学毕业证成绩单原版一模一样

原版纸张【微信:741003700 】【(bedfordhire毕业证书)英国贝德福特大学毕业证成绩单】【微信:741003700 】学位证,留信认证(真实可查,永久存档)offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原海外各大学 Bachelor Diploma degree, Master Degree Diploma
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
一比一原版(CSU毕业证)加利福尼亚州立大学毕业证成绩单专业办理

CSU毕业证原版定制【微信:176555708】【加利福尼亚州立大学毕业证成绩单-学位证】【微信:176555708】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
◆◆◆◆◆ — — — — — — — — 【留学教育】留学归国服务中心 — — — — — -◆◆◆◆◆
【主营项目】
一.毕业证【微信:176555708】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【微信:176555708】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分→ 【关于价格问题(保证一手价格)
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
学历顾问:微信:176555708
This 7-second Brain Wave Ritual Attracts Money To You.!

Discover the power of a simple 7-second brain wave ritual that can attract wealth and abundance into your life. By tapping into specific brain frequencies, this technique helps you manifest financial success effortlessly. Ready to transform your financial future? Try this powerful ritual and start attracting money today!
Multi-cluster Kubernetes Networking- Patterns, Projects and Guidelines

Talk presented at Kubernetes Community Day, New York, May 2024.
Technical summary of Multi-Cluster Kubernetes Networking architectures with focus on 4 key topics.
1) Key patterns for Multi-cluster architectures
2) Architectural comparison of several OSS/ CNCF projects to address these patterns
3) Evolution trends for the APIs of these projects
4) Some design recommendations & guidelines for adopting/ deploying these solutions.
1比1复刻(bath毕业证书)英国巴斯大学毕业证学位证原版一模一样

原版纸张【微信:741003700 】【(bath毕业证书)英国巴斯大学毕业证学位证】【微信:741003700 】学位证,留信认证(真实可查,永久存档)offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原海外各大学 Bachelor Diploma degree, Master Degree Diploma
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
APNIC Foundation, presented by Ellisha Heppner at the PNG DNS Forum 2024

Ellisha Heppner, Grant Management Lead, presented an update on APNIC Foundation to the PNG DNS Forum held from 6 to 10 May, 2024 in Port Moresby, Papua New Guinea.
How to Use Contact Form 7 Like a Pro.pptx

Contact Form 7 is a popular plugins for WordPress. This is an introduction into its features and usage.
原版仿制(uob毕业证书)英国伯明翰大学毕业证本科学历证书原版一模一样

原版纸张【微信:741003700 】【(uob毕业证书)英国伯明翰大学毕业证】【微信:741003700 】学位证,留信认证(真实可查,永久存档)offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原海外各大学 Bachelor Diploma degree, Master Degree Diploma
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
Bridging the Digital Gap Brad Spiegel Macon, GA Initiative.pptx

Brad Spiegel Macon GA’s journey exemplifies the profound impact that one individual can have on their community. Through his unwavering dedication to digital inclusion, he’s not only bridging the gap in Macon but also setting an example for others to follow.
1.Wireless Communication System_Wireless communication is a broad term that i...

Wireless communication involves the transmission of information over a distance without the help of wires, cables or any other forms of electrical conductors.
Wireless communication is a broad term that incorporates all procedures and forms of connecting and communicating between two or more devices using a wireless signal through wireless communication technologies and devices.
Features of Wireless Communication
The evolution of wireless technology has brought many advancements with its effective features.
The transmitted distance can be anywhere between a few meters (for example, a television's remote control) and thousands of kilometers (for example, radio communication).
Wireless communication can be used for cellular telephony, wireless access to the internet, wireless home networking, and so on.
Internet-Security-Safeguarding-Your-Digital-World (1).pptx

# Internet Security: Safeguarding Your Digital World
In the contemporary digital age, the internet is a cornerstone of our daily lives. It connects us to vast amounts of information, provides platforms for communication, enables commerce, and offers endless entertainment. However, with these conveniences come significant security challenges. Internet security is essential to protect our digital identities, sensitive data, and overall online experience. This comprehensive guide explores the multifaceted world of internet security, providing insights into its importance, common threats, and effective strategies to safeguard your digital world.
## Understanding Internet Security
Internet security encompasses the measures and protocols used to protect information, devices, and networks from unauthorized access, attacks, and damage. It involves a wide range of practices designed to safeguard data confidentiality, integrity, and availability. Effective internet security is crucial for individuals, businesses, and governments alike, as cyber threats continue to evolve in complexity and scale.
### Key Components of Internet Security
1. **Confidentiality**: Ensuring that information is accessible only to those authorized to access it.
2. **Integrity**: Protecting information from being altered or tampered with by unauthorized parties.
3. **Availability**: Ensuring that authorized users have reliable access to information and resources when needed.
## Common Internet Security Threats
Cyber threats are numerous and constantly evolving. Understanding these threats is the first step in protecting against them. Some of the most common internet security threats include:
### Malware
Malware, or malicious software, is designed to harm, exploit, or otherwise compromise a device, network, or service. Common types of malware include:
- **Viruses**: Programs that attach themselves to legitimate software and replicate, spreading to other programs and files.
- **Worms**: Standalone malware that replicates itself to spread to other computers.
- **Trojan Horses**: Malicious software disguised as legitimate software.
- **Ransomware**: Malware that encrypts a user's files and demands a ransom for the decryption key.
- **Spyware**: Software that secretly monitors and collects user information.
### Phishing
Phishing is a social engineering attack that aims to steal sensitive information such as usernames, passwords, and credit card details. Attackers often masquerade as trusted entities in email or other communication channels, tricking victims into providing their information.
### Man-in-the-Middle (MitM) Attacks
MitM attacks occur when an attacker intercepts and potentially alters communication between two parties without their knowledge. This can lead to the unauthorized acquisition of sensitive information.
### Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS) Attacks
The+Prospects+of+E-Commerce+in+China.pptx

The Prospects of E-commerce in China,www.cfye-commerce.shop
一比一原版(LBS毕业证)伦敦商学院毕业证成绩单专业办理

LBS毕业证原版定制【微信:176555708】【伦敦商学院毕业证成绩单-学位证】【微信:176555708】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
◆◆◆◆◆ — — — — — — — — 【留学教育】留学归国服务中心 — — — — — -◆◆◆◆◆
【主营项目】
一.毕业证【微信:176555708】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【微信:176555708】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分→ 【关于价格问题(保证一手价格)
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
学历顾问:微信:176555708
Recently uploaded (20)
History+of+E-commerce+Development+in+China-www.cfye-commerce.shop

History+of+E-commerce+Development+in+China-www.cfye-commerce.shop
This 7-second Brain Wave Ritual Attracts Money To You.!

This 7-second Brain Wave Ritual Attracts Money To You.!
Multi-cluster Kubernetes Networking- Patterns, Projects and Guidelines

Multi-cluster Kubernetes Networking- Patterns, Projects and Guidelines
guildmasters guide to ravnica Dungeons & Dragons 5...

guildmasters guide to ravnica Dungeons & Dragons 5...
APNIC Foundation, presented by Ellisha Heppner at the PNG DNS Forum 2024

APNIC Foundation, presented by Ellisha Heppner at the PNG DNS Forum 2024
Bridging the Digital Gap Brad Spiegel Macon, GA Initiative.pptx

Bridging the Digital Gap Brad Spiegel Macon, GA Initiative.pptx
1.Wireless Communication System_Wireless communication is a broad term that i...

1.Wireless Communication System_Wireless communication is a broad term that i...
Internet-Security-Safeguarding-Your-Digital-World (1).pptx

Internet-Security-Safeguarding-Your-Digital-World (1).pptx
ICTY Codebits 2014
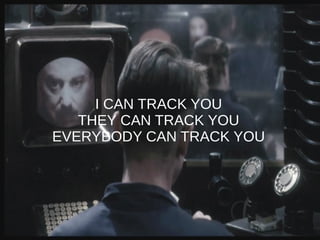
- 1. I CAN TRACK YOU THEY CAN TRACK YOU EVERYBODY CAN TRACK YOU
- 2. whoami Miguel Mota Veiga – 29 years old; – Infosec “Pro” since 2006; ● @Dognædis; ● Pen Testing, Security Audits, Forensic Analysis, Malware Analysis, Incident Handling, System Administration, Perl... ● Financial & IT, Telco, Government, Defense; – Security/Privacy Lover; – Three “...er”s guy: ● Traveller, Backpacker, Geocacher;
- 3. What we'll talking about...
- 4. What this presentation is about ● How Mobile Devices can leak information; ● How an adversary can exploit it; ● How people can track you; ● Metrics and Results;
- 5. What this presentation is **NOT** ● Evidence on the court (hopefully); ● Mobile Phone Tracking 101; ● A cry out to do illegal stuff;
- 6. Warning Any actions and or activities related to the material contained within this presentation is solely your responsibility. The misuse of this information, can result in criminal charges brought against the person(s) in question. The author will not be held responsible in the event any criminal charges be brought against any individuals misusing the information contained. This presentation contains materials that can be potentially damaging or dangerous. If you do not fully understand something, then DON'T DO IT! Refer to the laws in your country before using, or in any other way utilizing these materials. These materials are for educational and research purposes only. Do not attempt to violate the law with anything contained here.
- 7. 2004 - 2014
- 8. ● 3.5 millions; ● >50% per year; ● 40% of the mobile phone users; Smartphones by numbers (2013)
- 9. Smartphones by numbers (2013) Roaming: ~23% SMS: ~90% Internet: ~45% Email: ~33% Banking: ~5% Social Network: ~30%
- 10. Smartphones by numbers (2013) Sex – Male : 55% – Female : 45% Age – 10/14 : 8% – 15/24 : 25% – 25/34 : 25% – 35/44 : 20% – 45/54 : 12% – 55/64 : 7% – >64 : 3% Social Class – Low/Low Middle : 44% – Middle : 31% – High/Middle High : 25% Region – Lisbon : 23% – Oporto : 12% – Litoral North : 17% – Litoral Center : 15% – South : 10% – Islandss : 5%
- 11. “Just because something is publicly accessible does not mean that people want it to be publicized”- “Making Sense of Privacy and Publicity“
- 12. Let's talk... There have been plenty of initiatives from numerous governments to legalize the monitoring of citizens Internet based communications. Several private organizations have developed technologies claiming to facilitate the analysis of collected data with the goal of identifying undesirable activities. Whether such technologies are used to identify such activities, or rather to profile all citizens, is open to debate. I will show how can be done (using IEEE 802.11).
- 13. Wifi
- 14. Wifi As per the RFC5418 documentation (i.e. not down to individual vendors) client devices send out 'probe requests' looking for networks that the devices have previously connected to (and the user chose to save).
- 15. A device
- 17. A Link to a Person 9C:20:7B:8E:F7:E7
- 18. Wifi tracking ● iOS : Saves the last 3 connected essid, and leak it out; ● Android : Depend on vendors / versions; ● Windows Phone : Don't have any data;
- 19. Examples Mac: 10:68:3F:79:XX:XX, ESSID: HOMEnetwork,ZON-03B0,MEO-983B37,MEO_CASA1,AndroidAP,PT- WIFI,NSN-BYOD,FreeWiFiCentroVascodaGama,Cabovisao-FCF5,CasaZero Mac: 50:46:5D:1B:XX:XX, ESSID: ZON-D7C0,Thomson274A16,SAPO-ZL71193,Thomson4E835C,ZON- 7A9C,MEO-6A9F51,MEO-08D1E6,MEO-45CBBD,ZON-6520 Mac: D0:51:62:E6:XX:XX, ESSID: MEO-8E8341,PROFESSORES,ZON-7760,PROFESSORES3
- 20. ESSID? ● People tend to connect to networks that they can trust; – Home, Workplace, Restaurants, Bars; ● They tend to be unique – Thomson-<random>, MEO-<random> etc. (ignore Zon-FON, PTWIFI or any public wifi networks); ● ESSID + GPS data = Profit (Google Maps, Google Street View);
- 21. Analysis "Hmm, you've previously connected to mcdonalds_wifi, and elCheapoAirlines_wifi - you must be an average Joe" vs "Hmm, you've previously connected to "BA_firstclass, ExpensiveRestaurant_wifi, etc - you must be a high roller".
- 22. Examples
- 23. “You already have zero privacy. Get over it.” - Scott G. McNealy CEO of Sun Microsystems
- 24. ESSID
- 25. ESSID
- 26. ESSID
- 27. ESSID
- 28. ESSID ● Cheap laptop (250€); – OpenSource Apps; ● Kismet and Airodump supports GPSd; ● GPS dongle (30€); ● Bag (20€); ● Hiking shoes/boots (30€);
- 29. Mac Address Mac Address are unique. If we match it to a person, then GAME OVER. – List of ESSID and information about is geolocation; – Can determine if he's at range; – Deploy drones and stalk him.
- 30. Architecture - Passive ● Linux; ● Kismet / Airodump-ng; ● GPSd; ● MySQL;
- 31. Attacks ● Evil Twin Attack; – Create a rogue AP with an known ESSID of your target; ● Man In The Middle; ● Data Interception; – Social Networks, Email, any kind of identifier; ● Code Injection; – Malicious code; ● Tactical Exploitation; – List of contacts, SMS, etc.
- 32. Evil twin
- 33. Evil Twin “...Evil twin is a term for a rogue Wi-Fi access point that appears to be a legitimate one offered on the premises, but actually has been set up to eavesdrop on wireless communications....” - Wikipedia
- 34. Architecture - Aggressive ● DHCP Server; ● Bind; ● Squid; ● Airodump-ng; ● Beef / (Kar)Metasploit / sslstrip; ● Mysql Database; ● Drone(s) – Laptops, Android, Raspberry Pi
- 35. “We know where you are. We know where you’ve been. We can more or less know what you’re thinking about.” - Eric Schmidt
- 36. Usage ● Collecting anonymized statistics; ● Identify and follow criminals; ● Track a single individual; ● Track us all;
- 37. Architecture
- 38. Metrics ● Several devices probes were collect at: – Lisbon Airport; – Traffic Jams; – Subway Stations; – Malls; – Tourist Spots; ● 1200-1500 unique devices per hour;
- 39. Metrics ● 8790 unique devices; ● 2296 leak at least 1 ESSID; – ~26% of the Smartphone Universe; ● 706* vulnerable to the Evil Twin Attack – ~8% of the Smartphone Universe; – * Only counted the most common Open ESSID, this number should be more high...
- 40. Protect Yourself "I don't believe society understands what happens when everything is available, knowable and recorded by everyone all the time;"
- 41. Protect yourself ● Turn off your Wifi; ● Erase all the saved ESSID; ● Randomize your Mac Address;
- 42. Finish ● This is not new; ● Something quite similar was made by SensePost in London in 2013; ● Some drones/raspberrypi were deployed on several main streets/places; ● Check out the Snoopy Framework;
- 43. Future(?) ● Any Wireless technology that can be used to identify “any” citizen: – Bluetooth; – Wifi; – GSM; – GPS; – NFC; – RFID;
- 44. Future(?) HEX l2_data_out_B:296 Format Bbis (RR, MM or CC) 000: d6 a7 b5 cf 29 6f 38 ff - ea 55 55 bc e2 b8 80 d6 001: 83 59 cf 2d ef 38 d7 ea - 55 55 bc e2 b9 40 d0 73 002: 38 e2 ac f1 69 d5 61 e3 - 8f c3 78 80 0: d6 1------- Direction: To originating site 0: d6 -101---- 5 TransactionID 0: d6 ----0110 Radio Resouce Management 1: a7 0-100111 RRpagingResponse 1: a7 -x------ Send sequence number: 1 (...) 6: 38 ----1--- SoLSA Capability: supported 6: 38 ------0- A5/3 not available 6: 38 -------0 A5/2: not available 8: ea -----010 Type of identity: IMEI 9: 55 -------- ID(254/odd): E5555CB2E8B086D3895FCD2FE837DAE5555CB2E9B040D37832ECA1F965D163EF83C8 708
- 45. Demo
- 46. Demo
- 47. Demo
- 48. Thank you for your time! Any QUESTIONS? miguelmotaveiga@gmail.com