How to Install an Ethernet Driver Without Internet Access.pdf
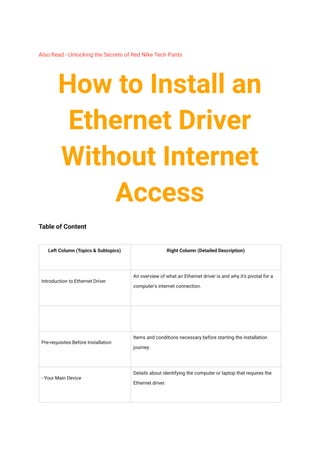
- 1. Also Read - Unlocking the Secrets of Red Nike Tech Pants How to Install an Ethernet Driver Without Internet Access Table of Content Left Column (Topics & Subtopics) Right Column (Detailed Description) Introduction to Ethernet Driver An overview of what an Ethernet driver is and why it's pivotal for a computer's internet connection. Pre-requisites Before Installation Items and conditions necessary before starting the installation journey: - Your Main Device Details about identifying the computer or laptop that requires the Ethernet driver.
- 2. - Backup Device Information about another device with active internet connectivity. - USB Magic Stick Guidance on using a USB drive or external storage as the transfer medium. Step-by-Step Installation Guide A thorough walkthrough to guide users on each installation phase: - Finding Out What Your Computer Speaks Instructions to open the 'Device Manager', locate 'Network adapters, and identify the network hardware name and model. - Grabbing the Fix from the Web Steps to download the correct Ethernet driver from an official website using a different device. - Passing the Magic Spell to Your Computer How to transfer the downloaded driver from the storage device to the computer that needs it. - Activating the Magic Spell Guidance on executing the driver installation, ensuring it's done with admin rights, and following the setup prompts. - Power Up and Double-Check Steps to restart the computer post-installation and verify that the driver has been installed and is functioning correctly. Troubleshooting Common Issues Expert solutions to standard challenges users might face:
- 3. - Mismatched Game Version Handling compatibility problems between the driver and the operating system. - Corrupted Game Save Addressing scenarios where the driver doesn't function even after installation. - Vanishing Gear Solutions when the hardware isn't recognized or is missing in 'Device Manager'. FAQ: Quick Answers to Burning Questions A compilation of frequently asked questions surrounding Ethernet drivers: - What's an Ethernet driver anyway? A simple explanation of the Ethernet driver's role in computer connectivity. - Why can't I just skip the driver step? Elaboration on the significance of drivers for network functionality. - I got the driver, but it's not working. Why? Common reasons why a recently installed driver might not operate correctly. - What if my computer doesn't recognize the USB? Tips for ensuring the computer detects the USB or external storage device. - The driver's installed, but my internet's still not working. Help? Steps to identify and address post-installation connectivity issues. - How often should I update my Ethernet driver? Recommendations on the frequency of driver updates.
- 4. - Is it safe to download drivers from the internet? Safety guidelines when downloading drivers online. In the world of connectivity, one might wonder, "How can I install an Ethernet driver when I don't have internet access?" Fear not. We are here to guide you step by step through this crucial process.
- 5. The Importance of an Ethernet Driver Think of an Ethernet driver as the translator between your computer and the big world of the internet. It's what lets your computer chat with other devices, sort of like how you need to know a language to chat with a friend from another country. Without this "translator," your computer wouldn't understand or be able to talk to the internet at all. It's like trying to play a multiplayer online game without being connected; you just can't join in on the fun! So, having an Ethernet driver is like having a golden ticket to a massive online party. Getting Ready to Start Hey there! Before we jump into the cool techy stuff, let's make sure we've got all our gear lined up. Here's what you're gonna need: 1. Your Main Device: This is the computer or laptop that's acting a bit tricky right now. It's probably having a hard time connecting to the internet because its Ethernet driver is acting up or just went missing. Imagine it's like a car without a radio; it can drive, but you can't jam to your favorite tunes. 2. Backup Device: Now, grab another gadget that's online. This could be your friend's laptop, your sibling's computer, or even a school computer—just something that can browse the web. Think of it as calling in a buddy when your favorite game gets tough. 3. USB Magic Stick: Last but not least, you'll need a USB drive or some sort of external storage. It's like a backpack for your digital stuff. We're going to use it to carry the Ethernet driver from the backup device to your main device. Got all that? Sweet! You're all set to dive into the action.
- 7. Your Step-by-Step Guide to Fixing the Internet Connection Alright, champ! So, you're ready to get your computer back online, but it's missing this thing called an Ethernet driver. No stress! Let's break it down into easy steps so you can be the tech hero of the day. Step 1: Finding Out What Your Computer Speaks Your computer, just like every superhero, has its own unique identity. We need to figure out what kind of network gear it uses to connect to the internet. Here's how: 1. Venturing into the Device Kingdom: On your computer, there's this place called 'Device Manager'. Think of it as the backstage area where all the techy magic happens. To get there, just search for 'Device Manager' on your computer and open it up! Also read :Ethernet Drivers Unlocked: A Gamer's Guide to Staying Connected 2. Finding the Network Crew: Inside the Device Manager, you'll see a bunch of categories. It's like scrolling through your game library but for computer parts. What you're looking for is a group labeled 'Network adapters'. Give that a click! 3. Spotting the Unique Tag: Now, under 'Network adapters', you'll see some names pop up. This is your computer's way of telling you the type and model of its network gear. Jot it down or snap a pic! It's kind of like when you need to know the name and version of a game before you download an update or a mod for it.
- 8. With this info, you're one step closer to getting your computer back in the online gaming arena! Stay tuned for the next steps. Step 2: Grabbing the Fix from the Web Alright, now that you've got the name and model of your computer's network gear, it's time to find its lost magic spell (the Ethernet driver) on the internet. Don't worry; it's like fetching a saved game from the cloud. Here's how you do it: 1. Hop onto Buddy's Device: Remember when your game console needed an update, and you had to borrow your friend's Wi-Fi? Well, we're doing something similar. Grab any gadget around you that's happily surfing the web. This could be your sibling's phone, your tablet, or any other tech toy with the internet. 2. Heading to the Source: Each piece of tech gear has a home base on the web. It's like how every game has an official website. Using your buddy's device, search for the official website of the company that made your computer's network gear. 3. The Great Search: Once you're on their website, you'll usually find a search bar. It's like the one you use to find cool skins or mods for your games. Pop the name and model of your computer's network gear into this search bar. 4. Grab the Treasure: After the search, you'll get a list of downloads. What you're hunting for is the Ethernet driver that matches your computer's operating system. It's like choosing the right version of a game for your console. Once you've found it, hit that download button! Sweet! You've now got the magic spell (aka Ethernet driver) that your computer needs. Just one more step, and you'll be back online, ready to dominate the leaderboards! Step 3: Passing the Magic Spell to Your Computer
- 9. Okay, gaming legend, you've got the precious Ethernet driver, our magic spell, downloaded and ready. Now, it's like when you've collected a rare item in a game, and you need to transfer it to your main character. Here's how you'll move this digital treasure to your computer: 1. Plug in the Flashy Backpack: Grab your USB stick or whatever external storage you have (think of it like a cool, magical backpack for files). Connect it to the device where you downloaded the driver. It'll pop up on the screen, ready to store some goods. Also read :Comprehensive Buying Guide: Where to Find the Best Deals on Owlet Socks in 2023 2. Storing the Magic Spell: Navigate to where the downloaded Ethernet driver (our magic spell) is saved. Once you find it, it's time to drag and drop (or copy and paste) that file onto your USB or external storage. It's like moving a character from one slot to another in a game. 3. Unplug with Care: Before you yank out your USB or storage device, make sure you do it safely. On the screen, there's usually an option to 'eject' or 'safely remove' the device. It's a bit like saving a game before turning off your console—you don't want to risk any data getting lost or corrupted! 4. Time for the Handover: With the driver safely tucked away in your USB or storage device, connect it to your main computer—the one that's missing its connection to the internet.
- 10. And boom! You've successfully transported the magic spell to where it's needed most. You're almost at the finish line, ready to restore your computer's internet power! 🌐🎮 Step 4: Activating the Magic Spell Epic! Now that you've got the magic spell (our Ethernet driver) on your computer, it's time to activate it. It's kinda like equipping a special item in a game to level up your character. Let's get that internet power unlocked: 1. Find the Magic in Your Backpack: First, open up the USB stick or external storage (your digital backpack) on your computer. Dig around until you spot the Ethernet driver you transferred. It's like finding that rare item you just added to your game inventory. 2. Unleashing the Power: Once you've located the driver file, give it a right-click. A menu will pop up. From this list, choose 'Run as administrator'. This step is super important—it's like using a cheat code with admin privileges to make sure everything runs smoothly. 3. Follow the Quest Markers: After you've started the installation, some instructions will appear on your screen. Think of these as quest markers guiding you on your mission. Just follow them step by step, and you'll be golden. If there are options to choose from, usually the default ones work best for most players. By the end of this step, your computer will have its internet superpowers back! Just like how a game character feels all charged up after equipping a new piece of gear. Great job, tech warrior! 🚀🎉
- 11. Step 5: Power Up and Double-Check Alright, superstar! You've almost completed the game. Now it's like when you've just upgraded your game character, and you need to reboot the game to see all the cool new abilities in action. Let's make sure everything's working perfectly: Also read :Ethernet Drivers Unlocked: A Gamer's Guide to Staying Connected 1. Hit the Reboot Button: After installing the magic spell (that Ethernet driver), you'll want to restart your computer. It's like giving your computer a short nap to wake up with its new powers. Click on that restart button and let the magic unfold!
- 12. 2. Backstage Check-up: Once your computer's awake and ready, dive back into the 'Device Manager'. It's like reopening your game settings to make sure all your new upgrades are there. In the manager, click on 'Network adapters' again. 3. Spot the Upgrade: In the list, you should now see the Ethernet driver you just installed. It's like seeing your game character equipped with that shiny new armor piece. Make sure it doesn't have any weird symbols or errors next to it, which would mean it's ready for action! There you go, gaming genius! Your computer is now fully equipped and connected, all thanks to you. Time to celebrate and jump back into your favorite online games! 🎉🎮🏆 Game Glitches & Fixes: What to Do When Things Get Wonky Okay, ace gamer, sometimes even the best of us face a few glitches in our quest. It's like when your game lags or freezes, super annoying, right? But no worries! We've got some cheat codes to get past these pesky bumps: 1. Mismatched Game Version: Imagine trying to play a game on a console it wasn't designed for. Weird glitches, right? The same goes for drivers. If you downloaded one that doesn't match your computer's operating system (think of it as its gaming console), it won't work properly. Double-check to make sure the driver is made for your system. If not, head back online and grab the right version! 2. Corrupted Game Save: Sometimes, even if you've downloaded the right thing, it just won't work. Maybe the file got a bit messed up during the download. Think of it like a game save that didn't store correctly. The fix? Delete the wonky driver and download it again. Then, give the installation another shot!
- 13. 3. Vanishing Gear: Ever had a situation in a game where a key item or character just... disappears? Super frustrating! In our techy quest, this is like the hardware playing hide and seek in the 'Device Manager'. First, double-check all connections to make sure your network gear is securely plugged in. If it's still MIA, give your computer another quick restart. Sometimes, that's all it takes to get things back on track. Remember, every great gamer faces challenges. But with these fixes in hand, you've got the upper edge. Keep going, and you'll conquer this tech quest in no time! 🎮🔧🌟 FAQ: Your Quick-Go Guide to All Things Ethernet Driver Hey, gamer! If you've got some burning questions about this whole Ethernet driver mission, you're in the right place. Dive into our FAQ to level up your knowledge: 1. What's an Ethernet driver anyway? Think of it like a translator. Your computer speaks one language, and the internet speaks another. The Ethernet driver helps them understand each other so you can game, stream, and surf without any hiccups! Also read :Comprehensive Buying Guide: Where to Find the Best Deals on Owlet Socks in 2023 2. Why can't I just skip the driver step? Skipping the Ethernet driver is like trying to play an online game without a game server. You need it to connect and get things rolling. Without it, your computer won't know how to talk to the internet. 3. I got the driver, but it's not working. Why? A couple of things could be happening. Maybe the driver isn't the right version
- 14. for your computer. Or, perhaps the download got a bit glitchy. Recheck the compatibility and try downloading it again if needed. 4. What if my computer doesn't recognize the USB I'm using? It might be like when a game doesn't recognize a new controller. Try a different USB port or use another storage device. Also, make sure your USB isn't locked or write-protected. 5. The driver's installed, but my internet's still not working. Help? Let's troubleshoot! Double-check if the drivers appear in the 'Device Manager'. If it's there, make sure there are no error symbols next to it. If you're still facing issues, reach out to the hardware manufacturer or a tech-savvy buddy. 6. How often should I update my Ethernet driver? Just like games have updates and patches, drivers get updates too. It's a good idea to check for updates every few months or if you notice any connection issues. 7. Is it safe to download drivers from the internet? Totally! But always make sure you're downloading from the official website of the hardware manufacturer. It's like grabbing a game from the official store—way safer than some random site. Hope these answers clear up your quest! If you're still puzzled about something, don't stress. The tech world is vast, and there's always more to learn. Game on! 🎮🔍🌐