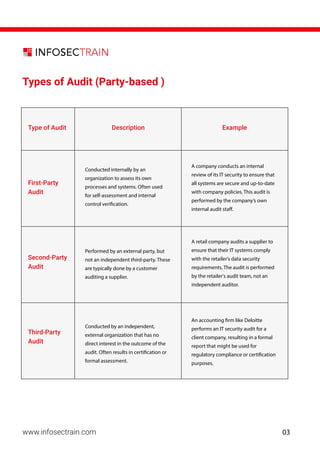
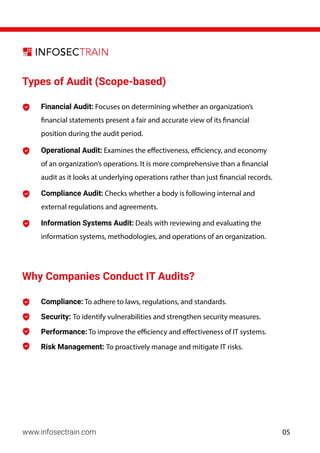
The document is a comprehensive guide on becoming an IT auditor, covering key objectives, types of audits, necessary skills, and career progression. It details the importance of IT audits for compliance, risk management, and operational efficiency, as well as the qualifications and certifications needed for the role. Additionally, it outlines typical audit processes, interview preparation tips, and a general daily workflow of an IT auditor.