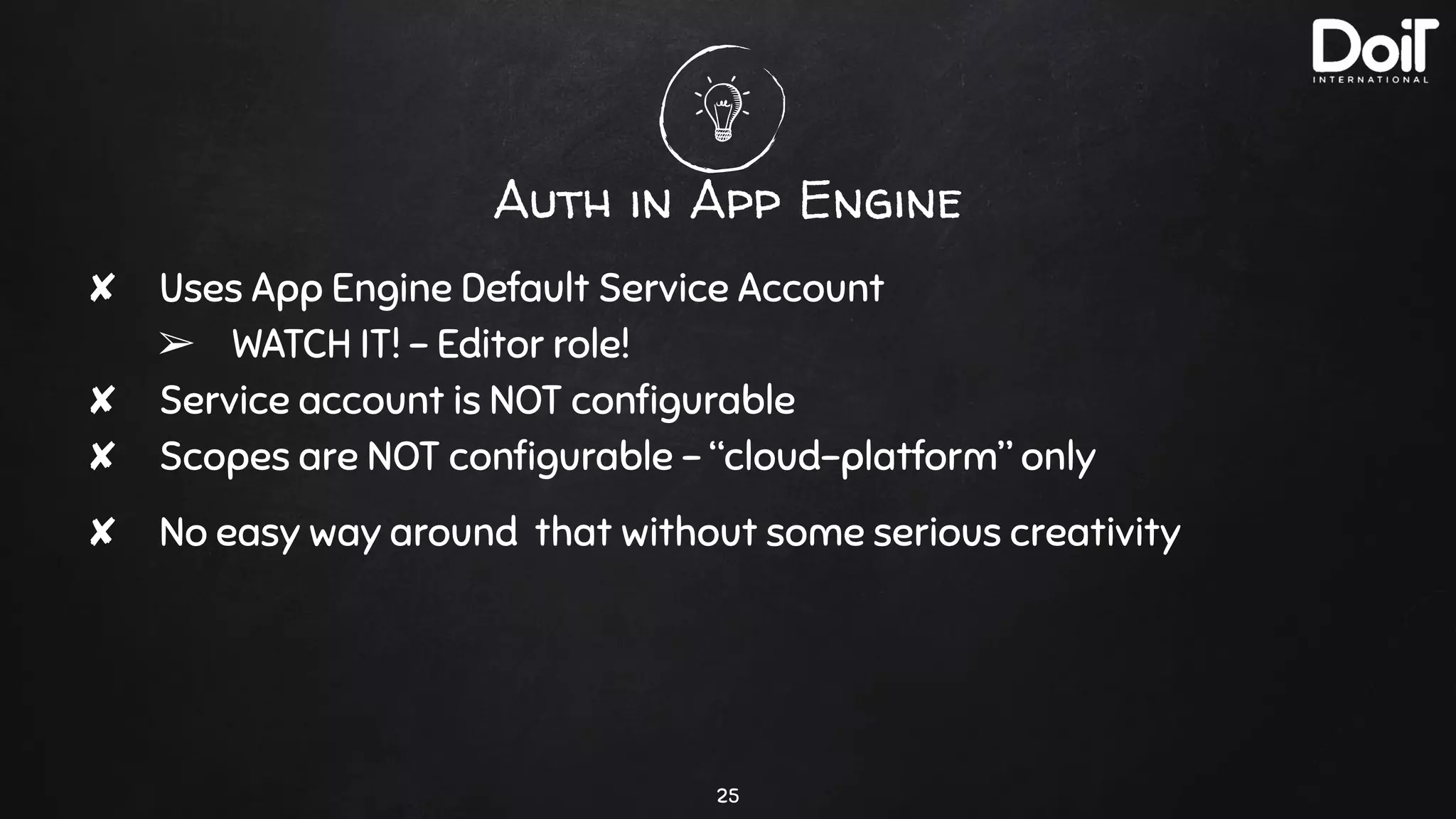
The document discusses Google authentication using OAuth 2.0, detailing the importance of scopes and IAM for access control in Google Cloud Platform (GCP). It highlights examples of authentication flows, how service accounts and scopes work in various GCP services like Google Drive and App Engine, and discusses the limitations associated with default service accounts. Additionally, it provides insights into configuring custom service accounts and scopes for different GCP environments like GKE and Cloud Run.


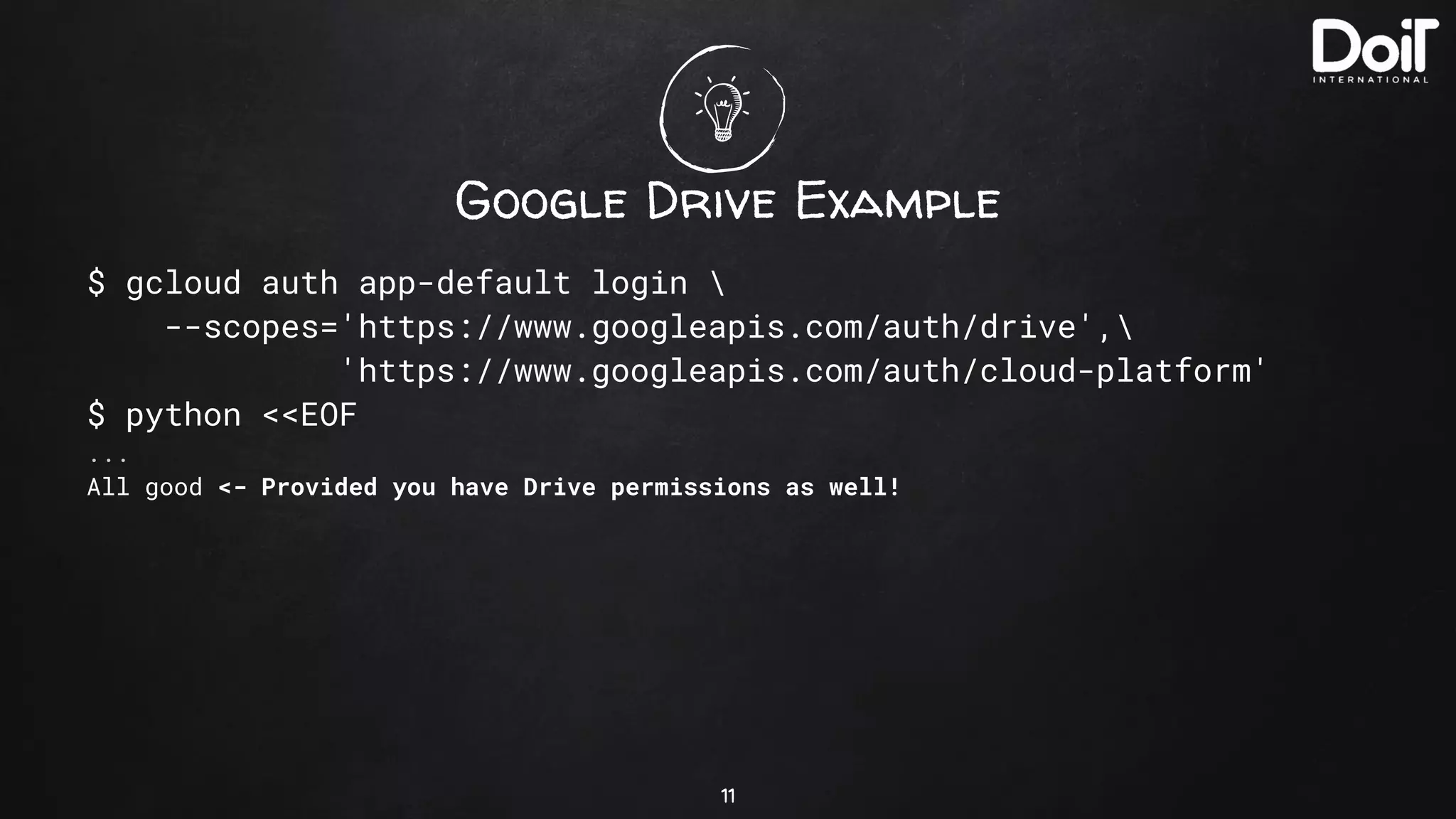
![Google Drive Example
$ gcloud auth app-default login
--scopes='https://www.googleapis.com/auth/drive',
'https://www.googleapis.com/auth/cloud-platform'
$ python <<EOF
...
All good
✘ Note that the following wouldn’t work:
creds, project_id = google.auth.default(scopes=[
'https://www.googleapis.com/auth/cloud-platform',
'https://www.googleapis.com/auth/drive',
])
12](https://image.slidesharecdn.com/googleauth-dispellingthemagic-210212131934/75/Google-auth-dispelling-the-magic-12-2048.jpg)








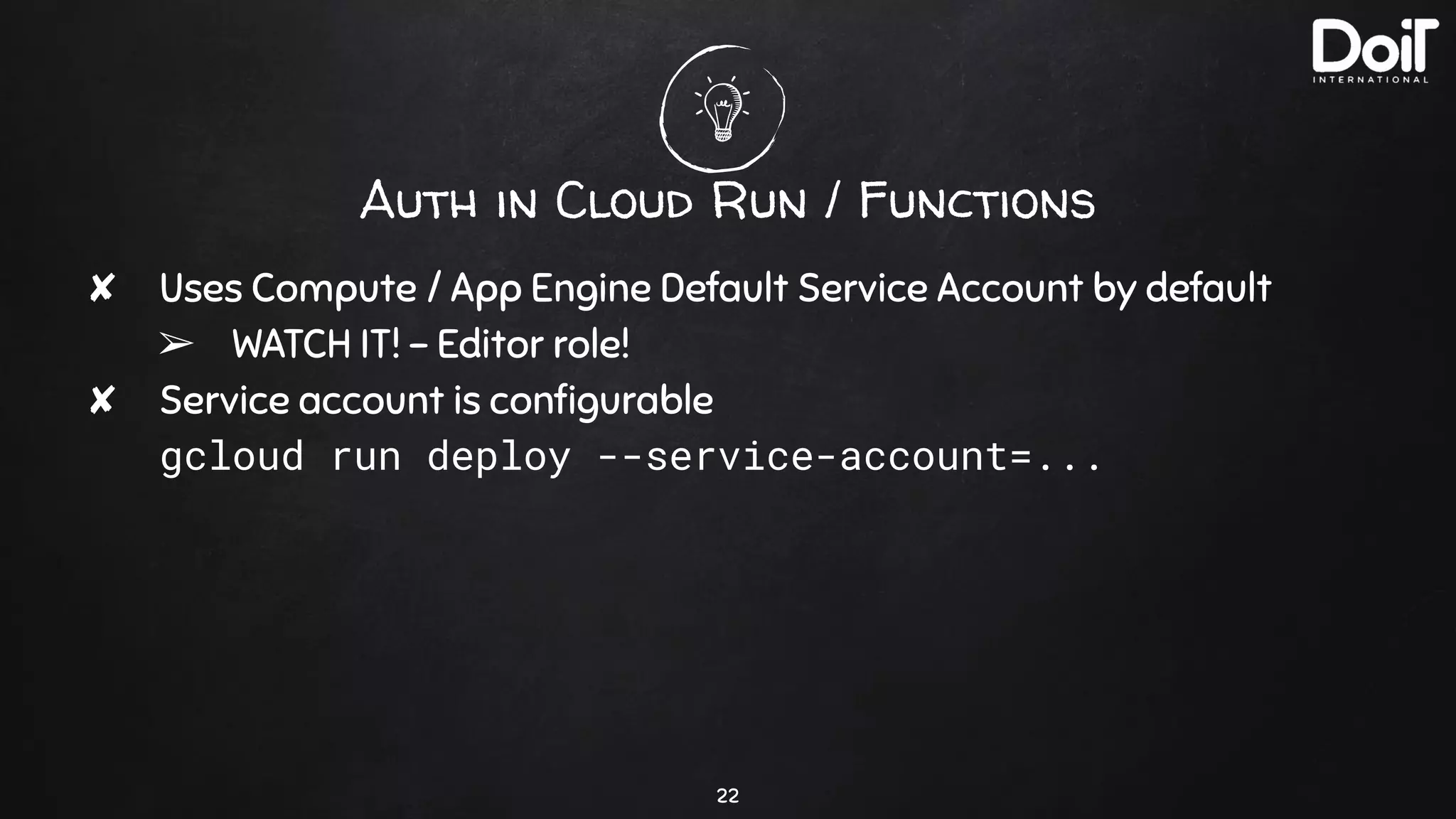
![Auth in Cloud Run / Functions
✘ Uses Compute / App Engine Default Service Account by default
➢ WATCH IT! - Editor role!
✘ Service account is configurable
✘ No scope limitations! Just use:
creds, project_id = google.auth.default(scopes=[
'https://www.googleapis.com/auth/cloud-platform',
'https://www.googleapis.com/auth/drive',
])
23](https://image.slidesharecdn.com/googleauth-dispellingthemagic-210212131934/75/Google-auth-dispelling-the-magic-23-2048.jpg)