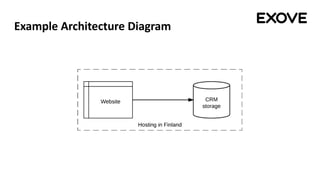
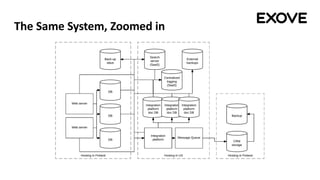
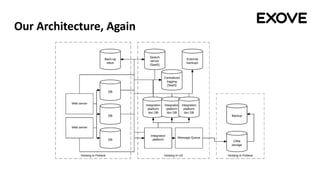
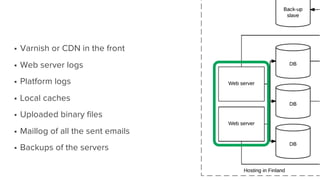
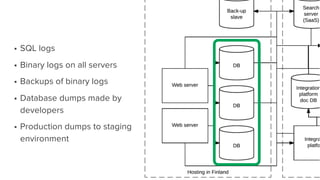
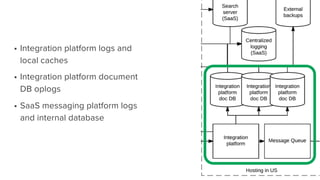
The document provides an overview of GDPR requirements for developers working with content management systems (CMS). It discusses key GDPR concepts like data controllers, processors and individual rights. It notes CMS pose specific challenges around structured vs unstructured data, content, analytics, logs and digital marketing. The document emphasizes existing systems may not fully document where personal data is stored and retained, and full deletion may not be technically possible. Thorough auditing of storage is needed to ensure compliance.