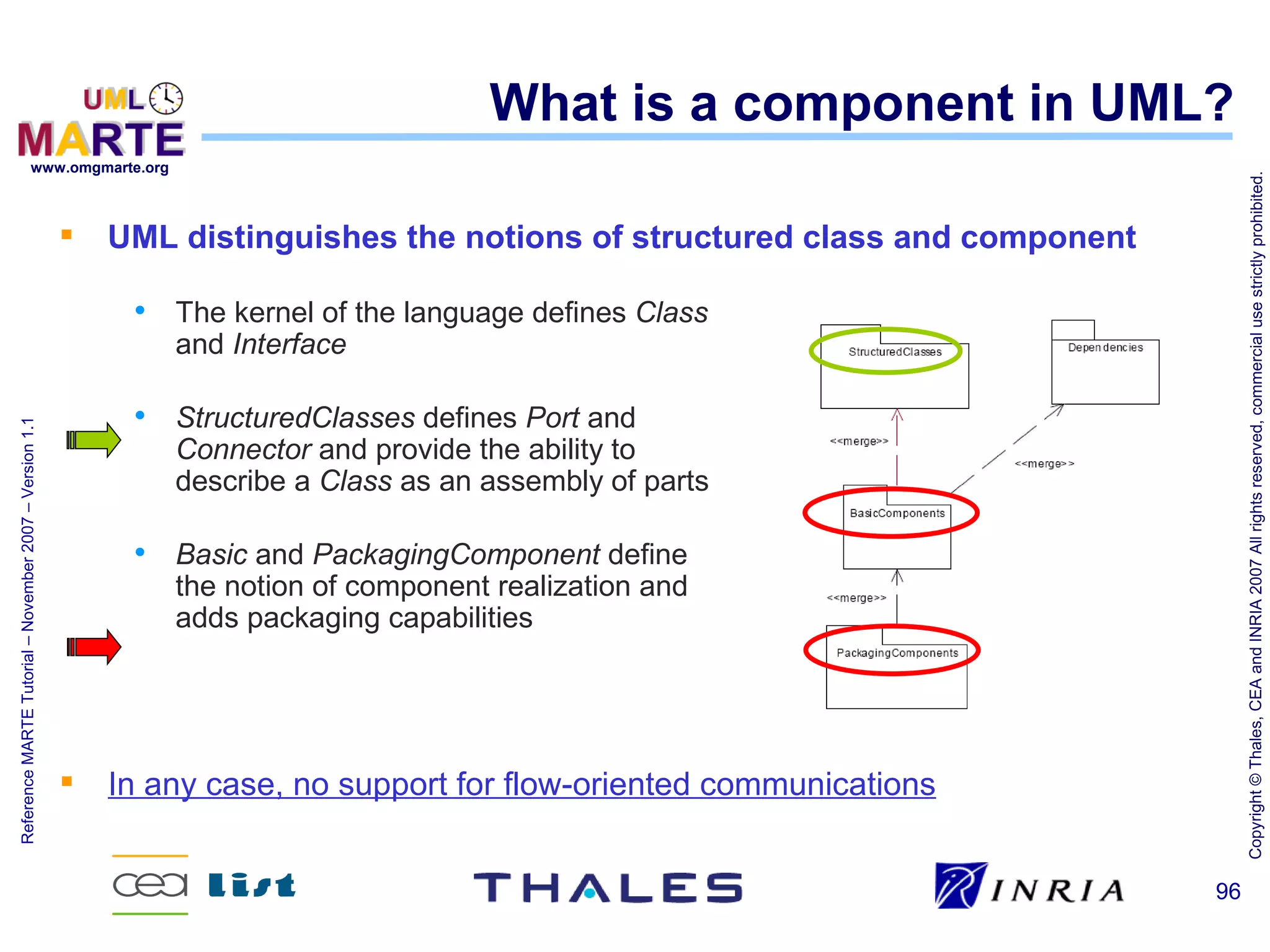
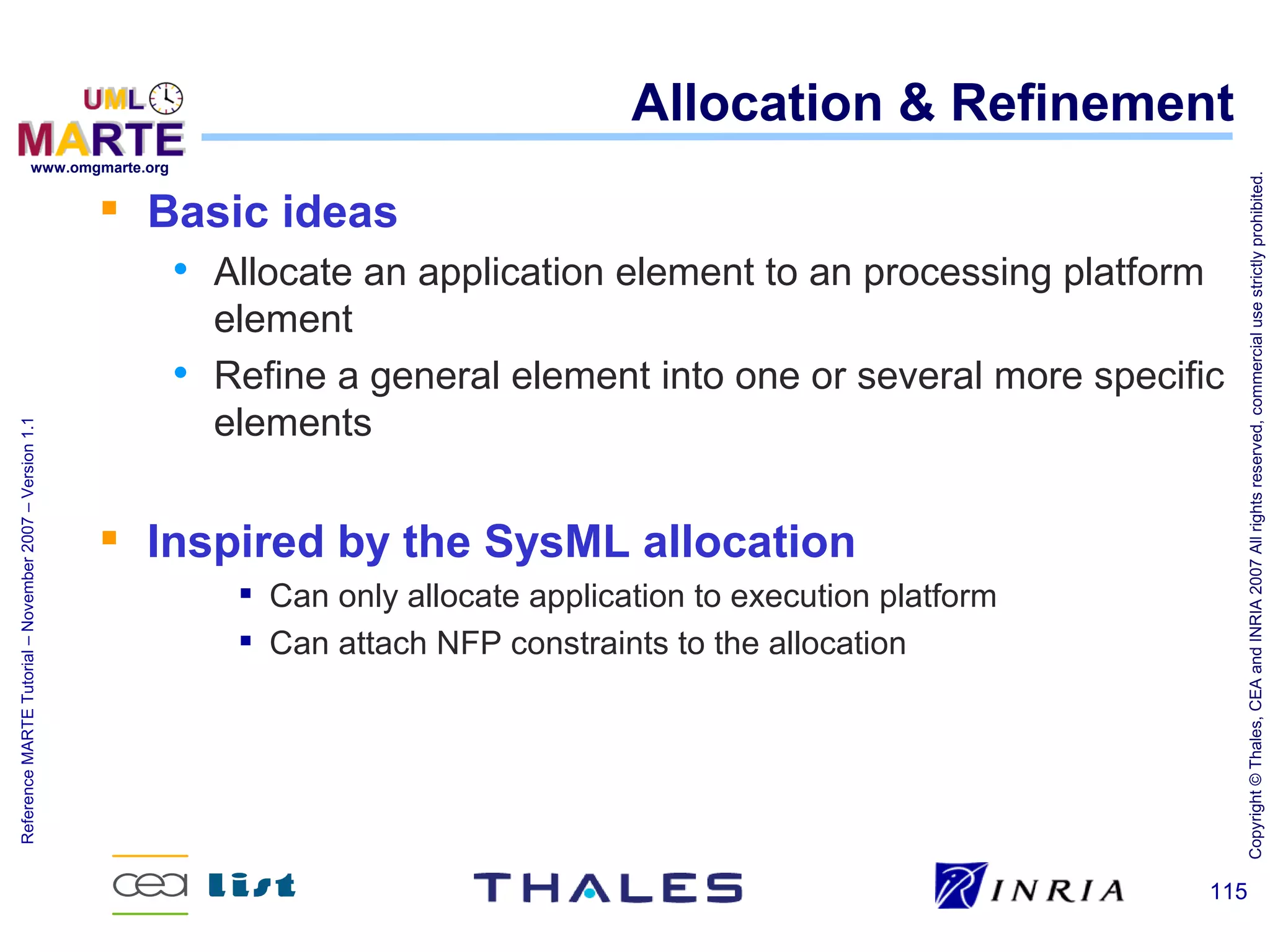
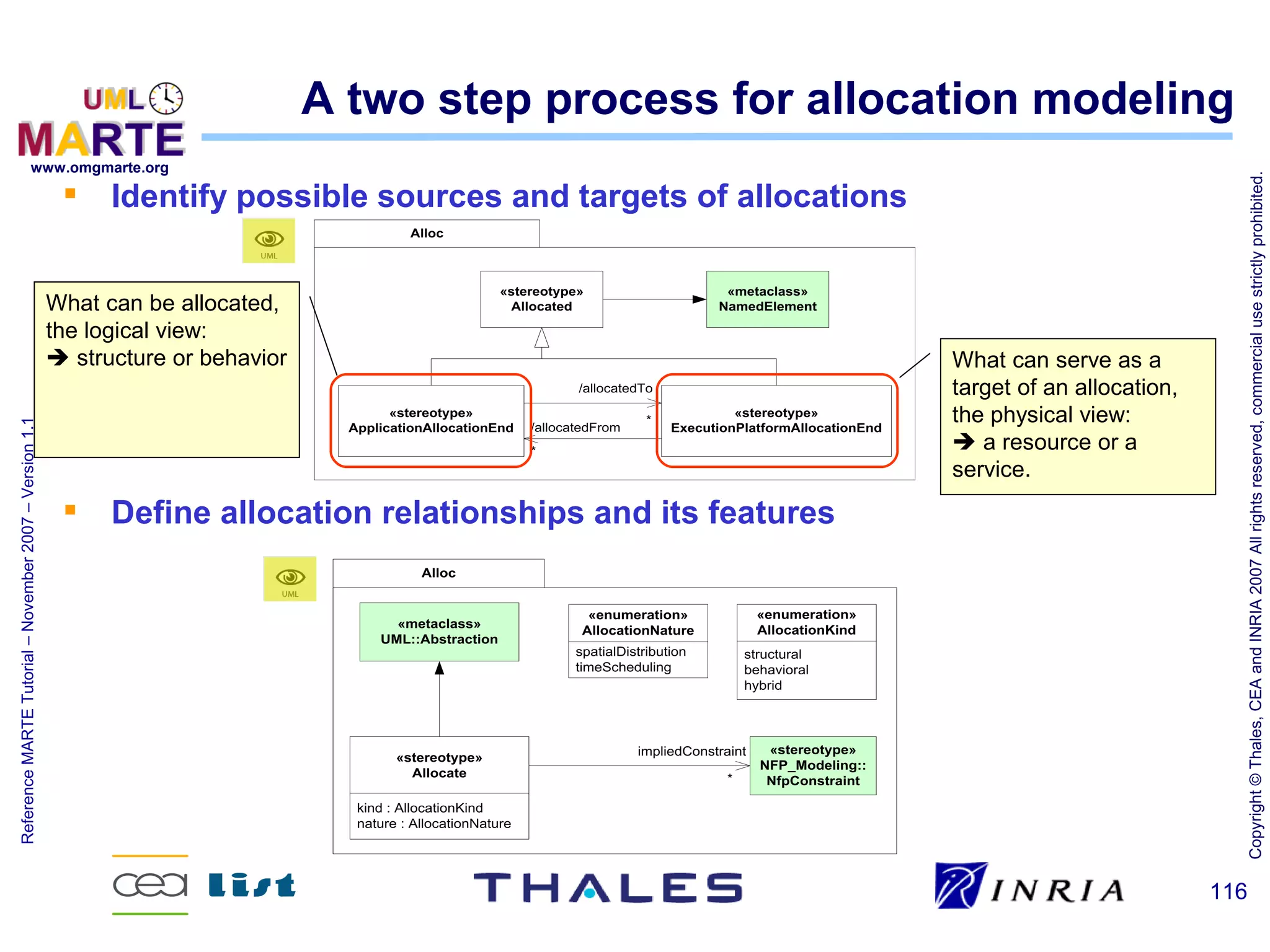
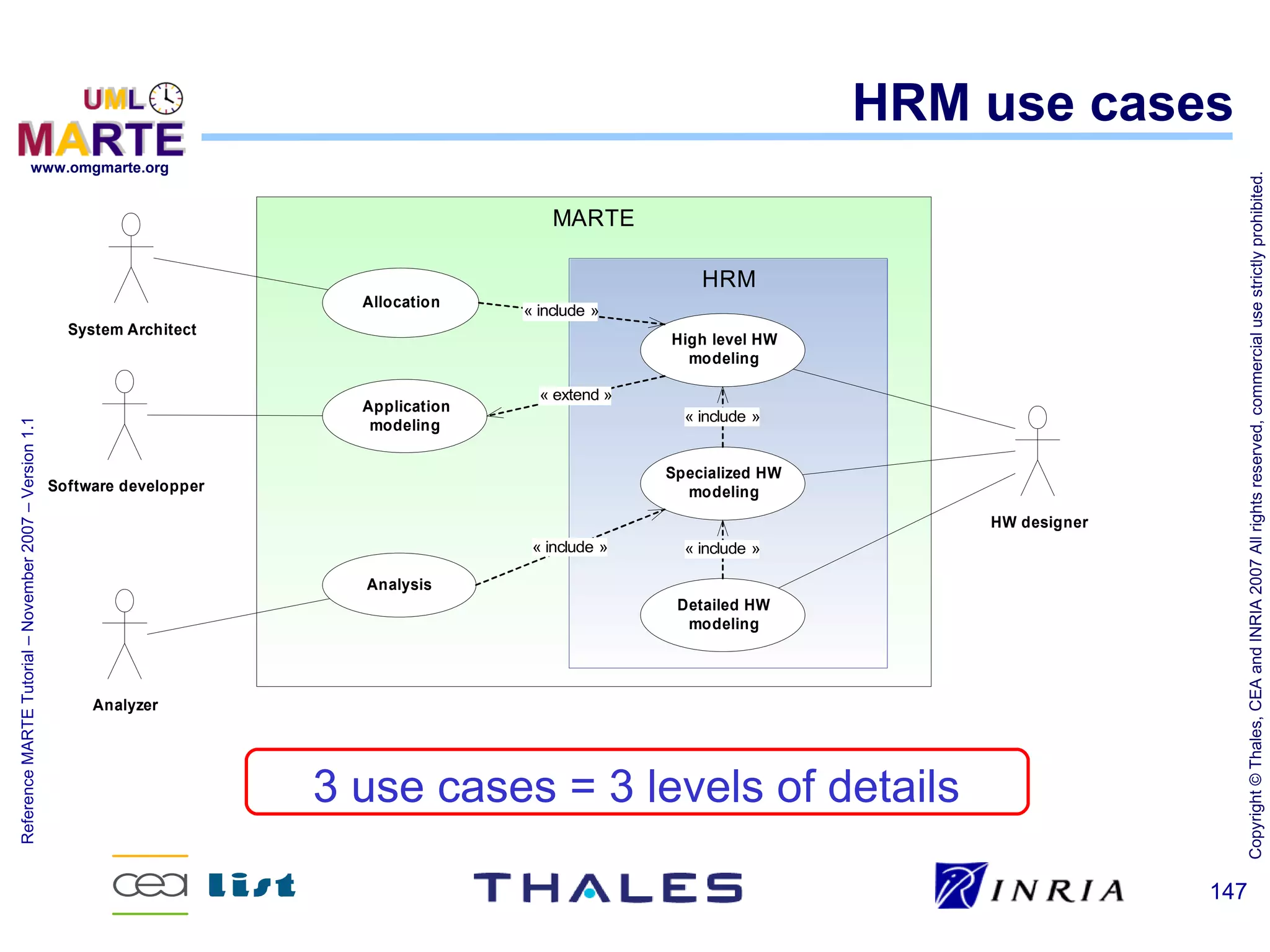
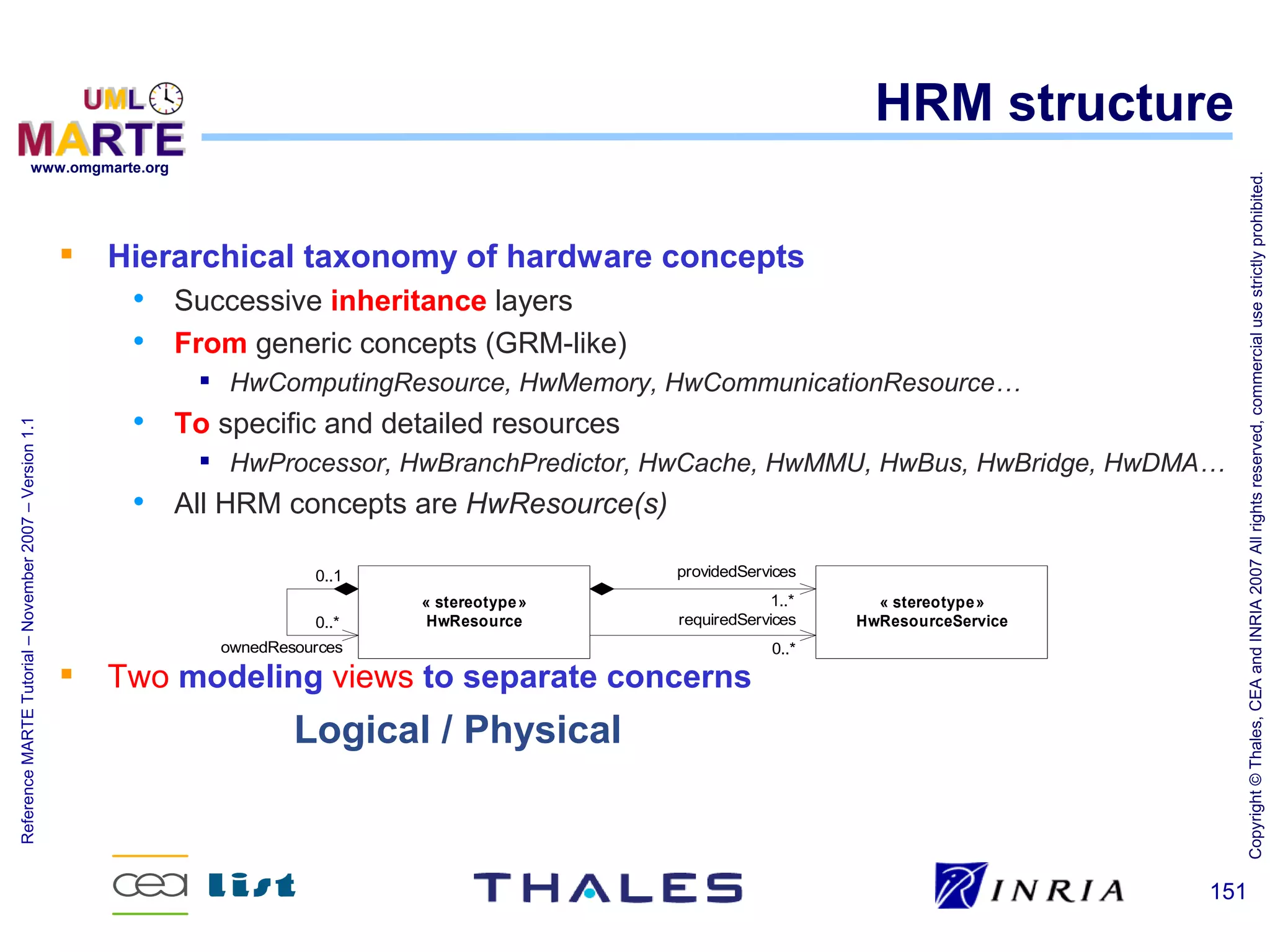
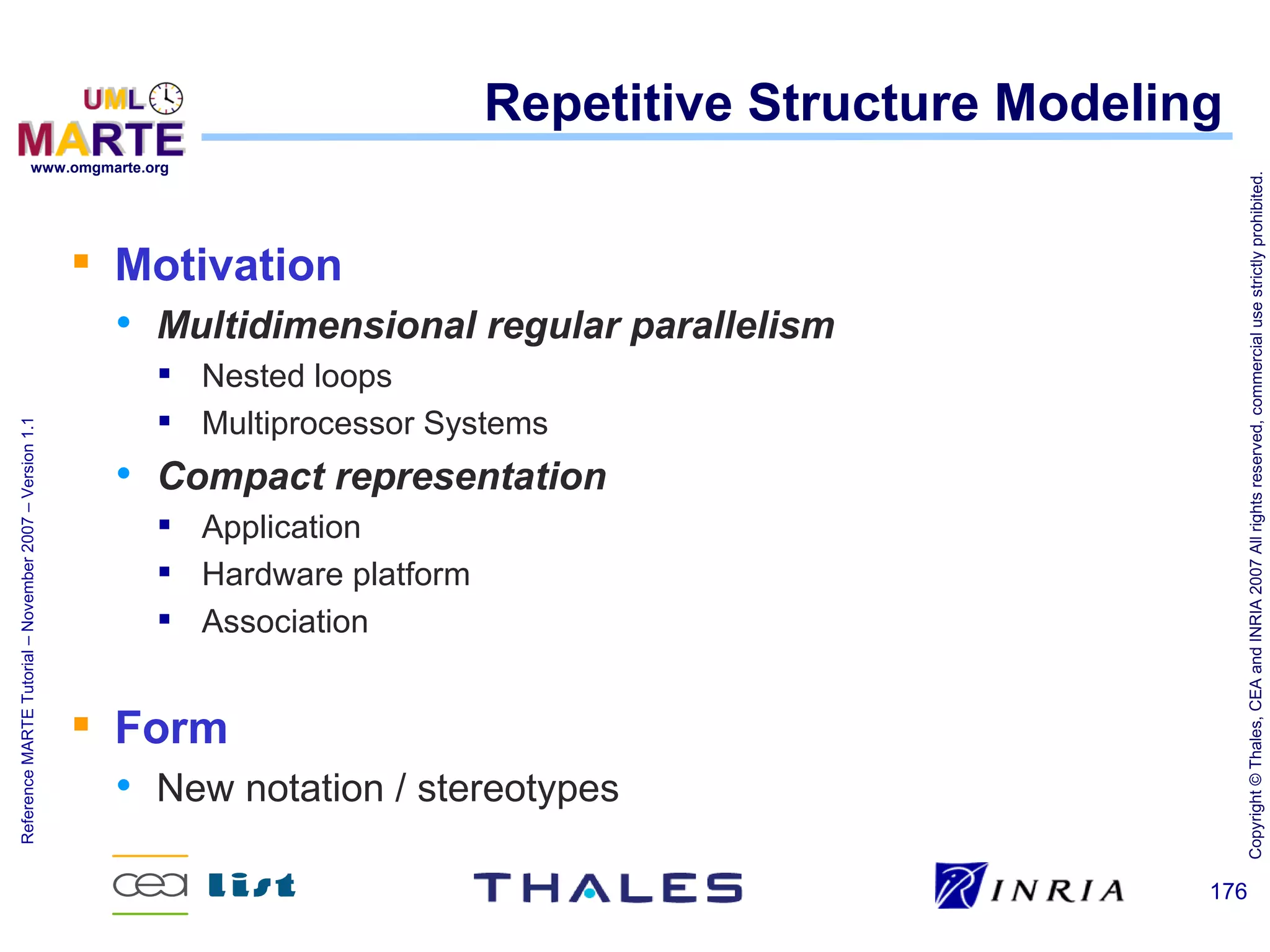
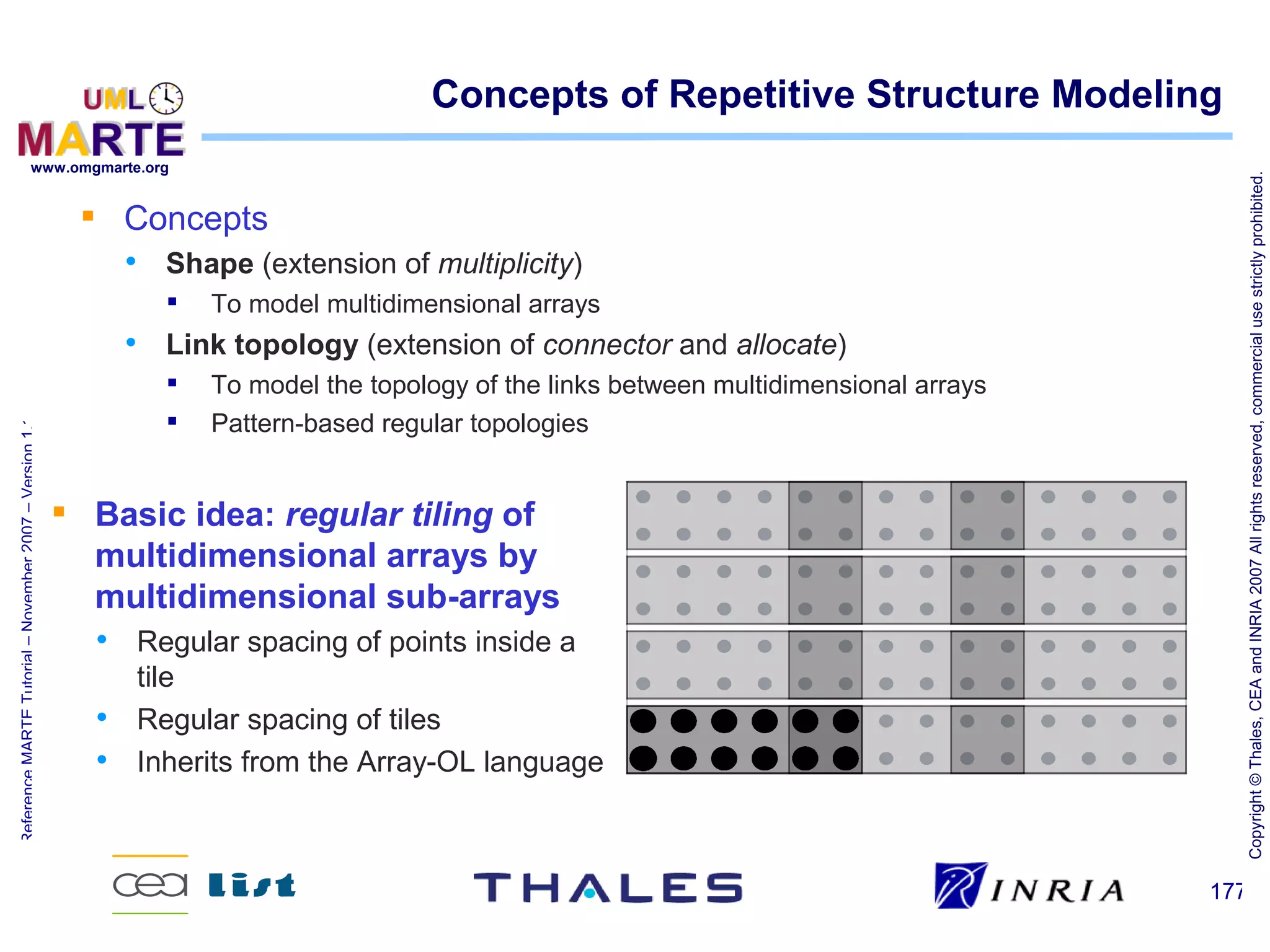
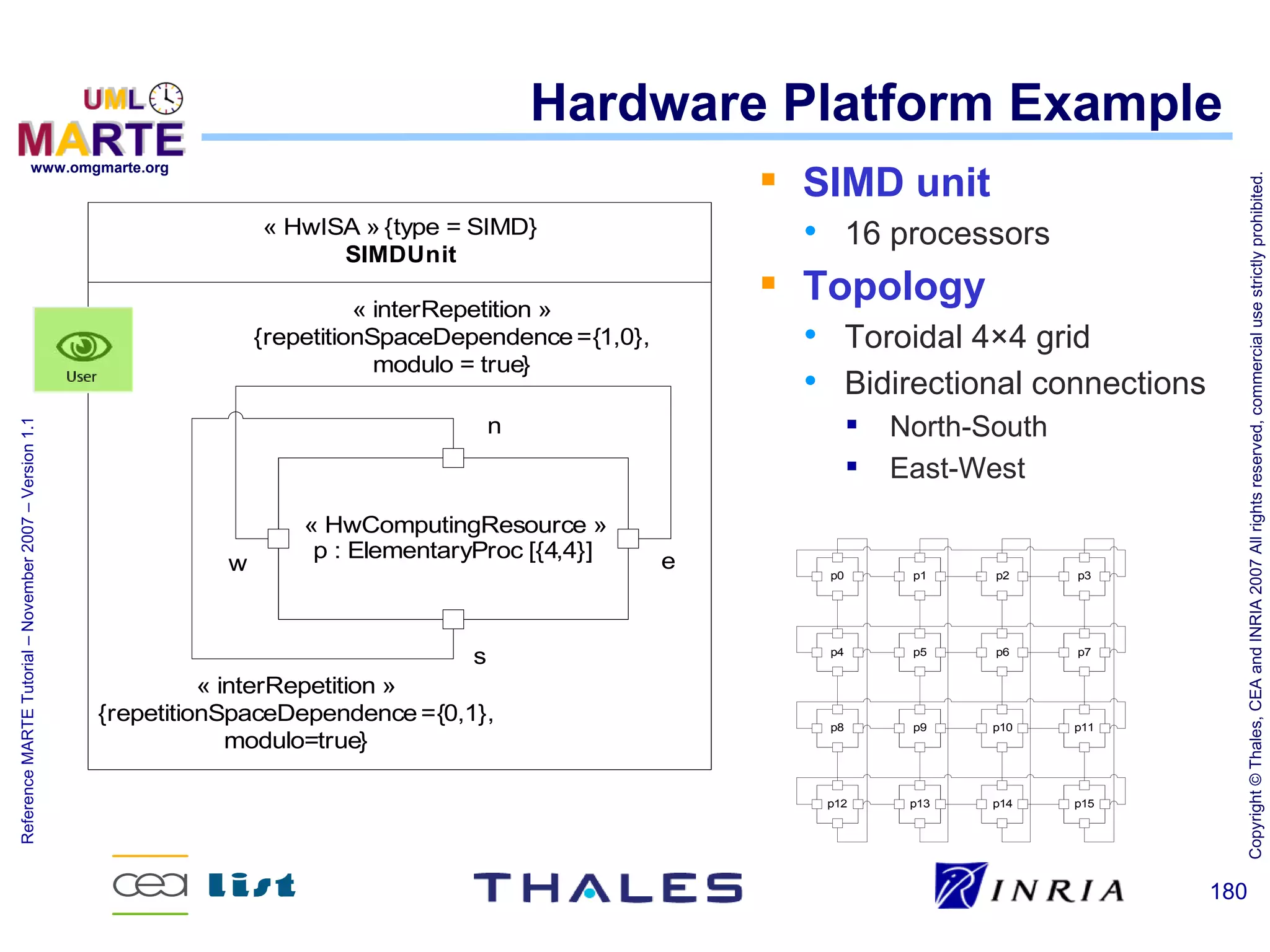
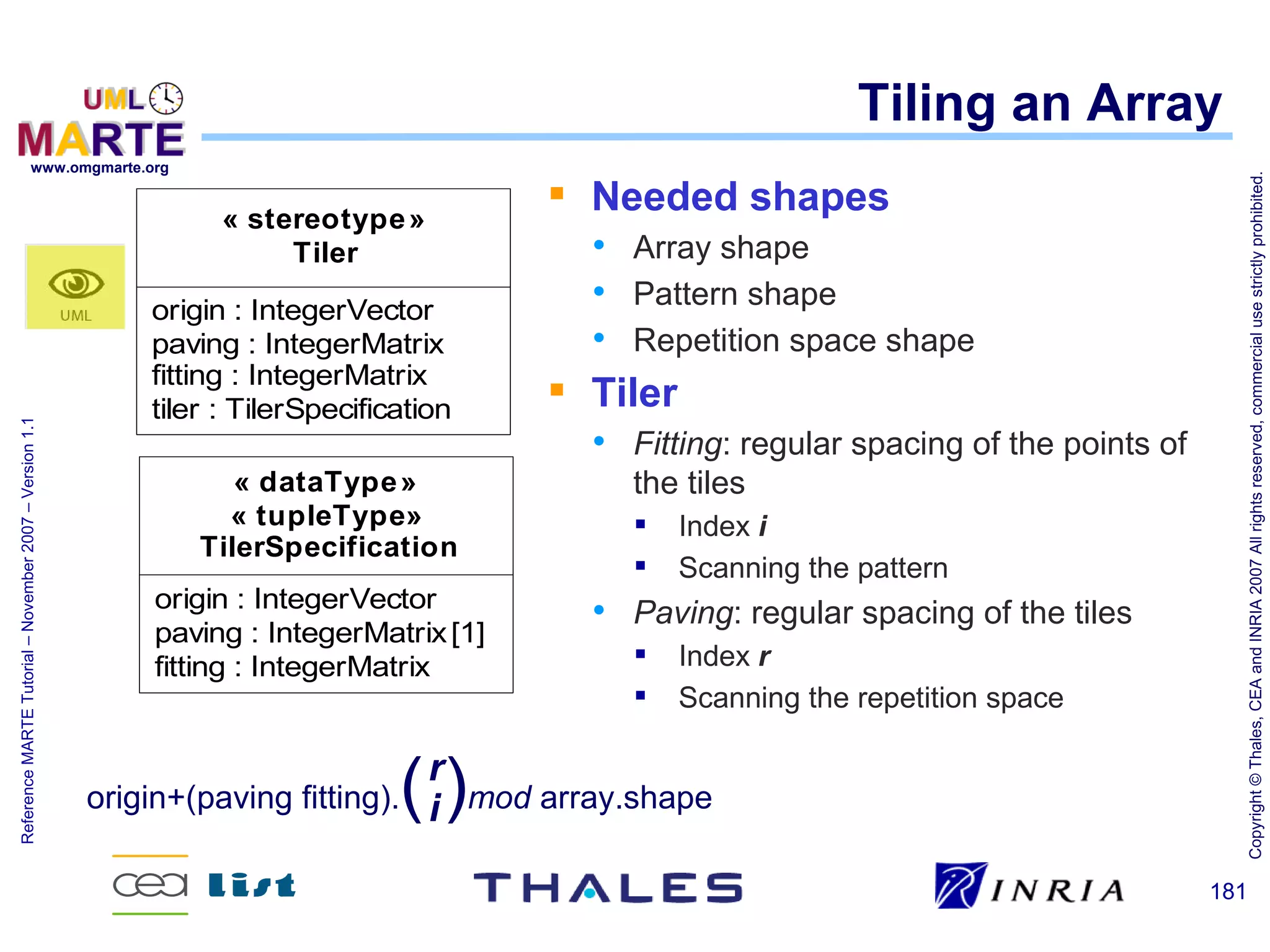
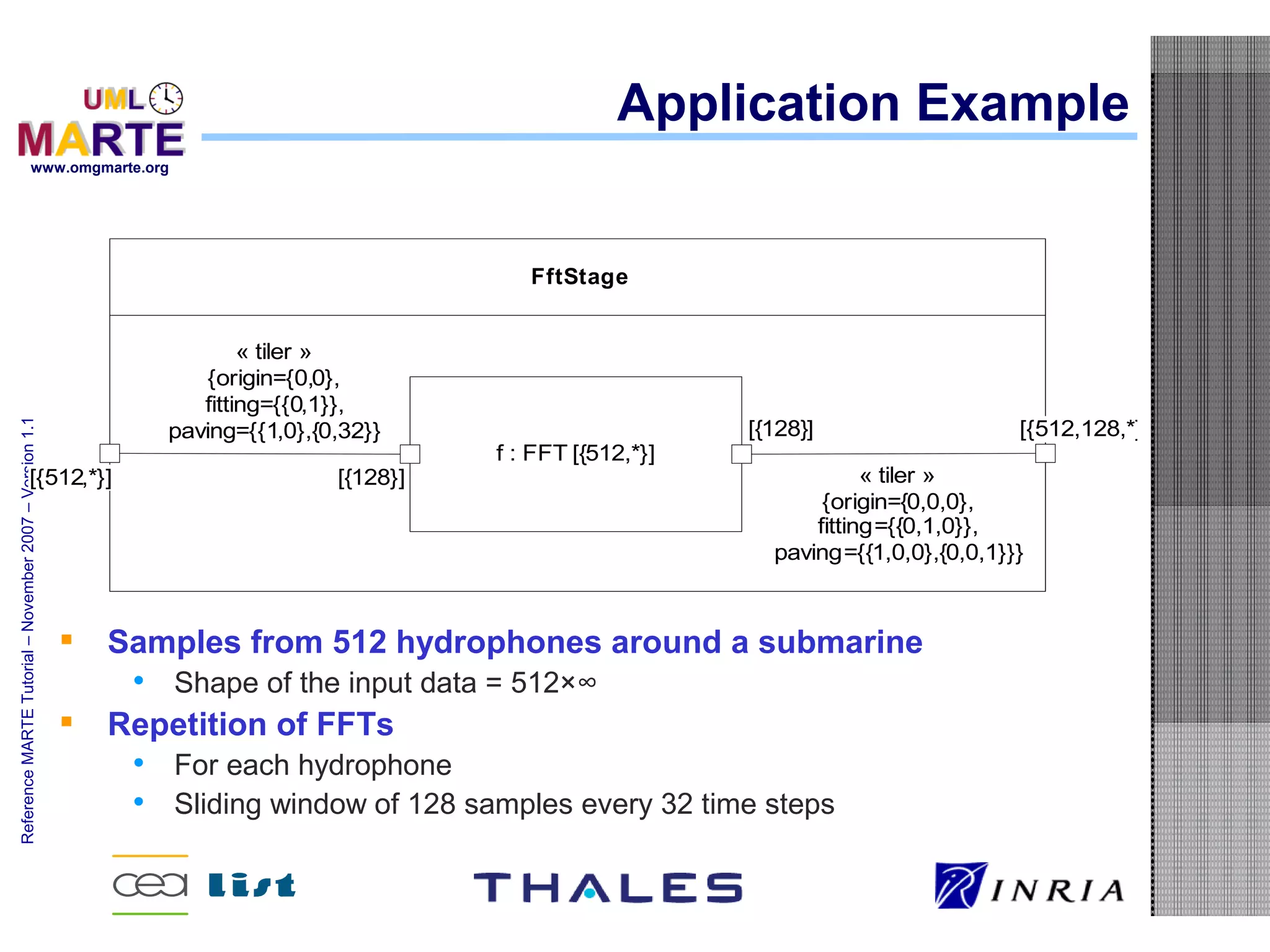
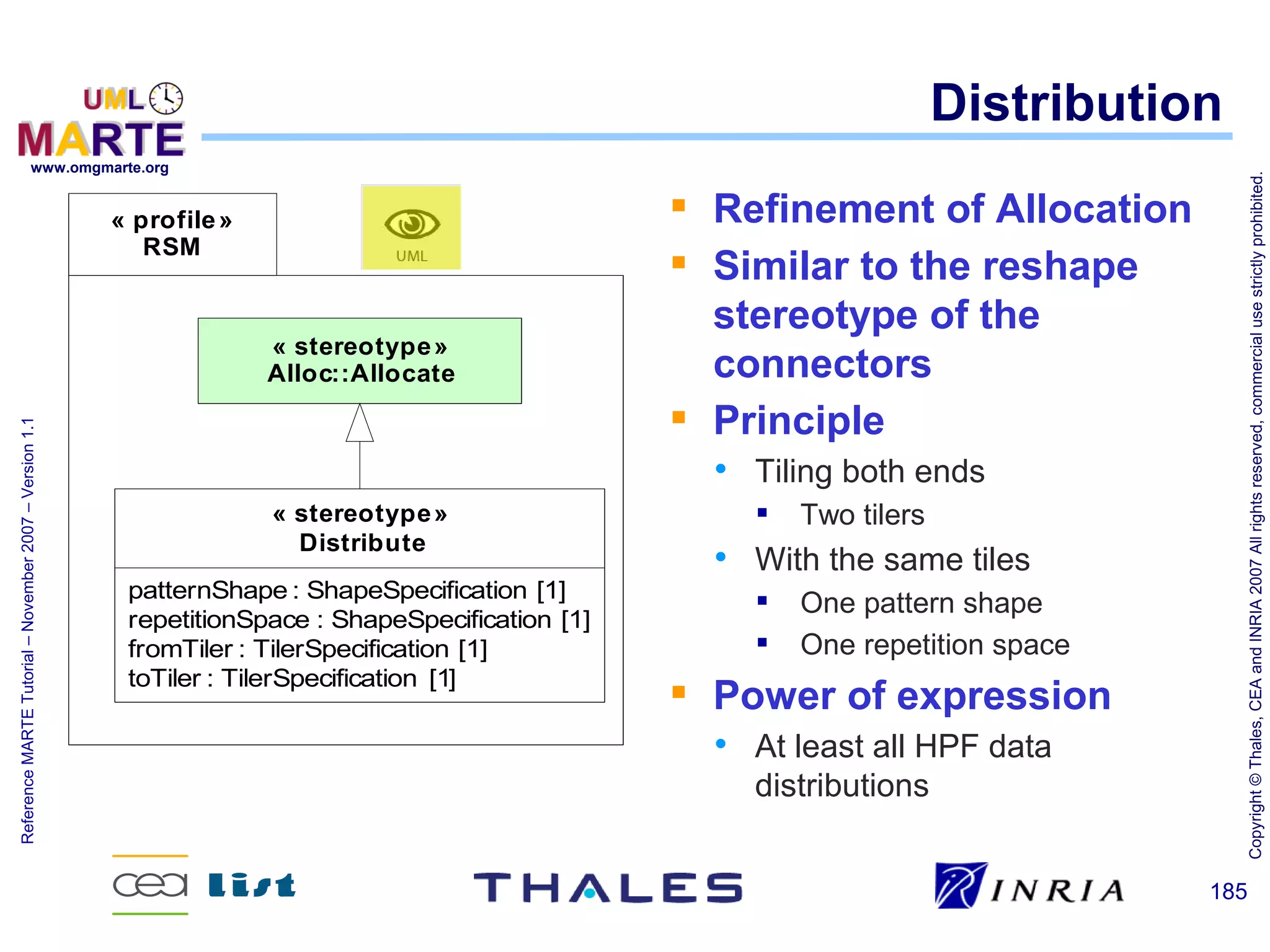
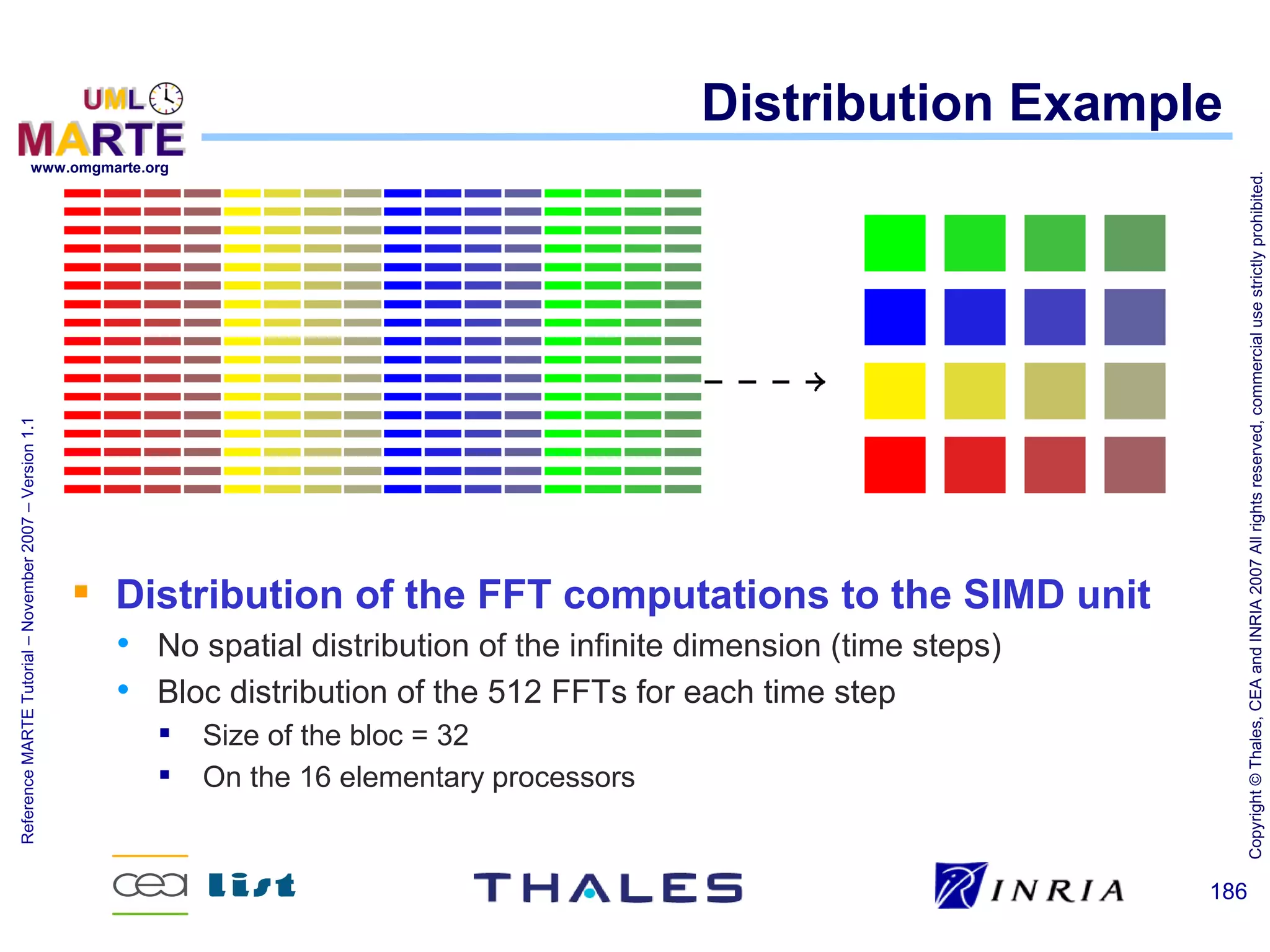
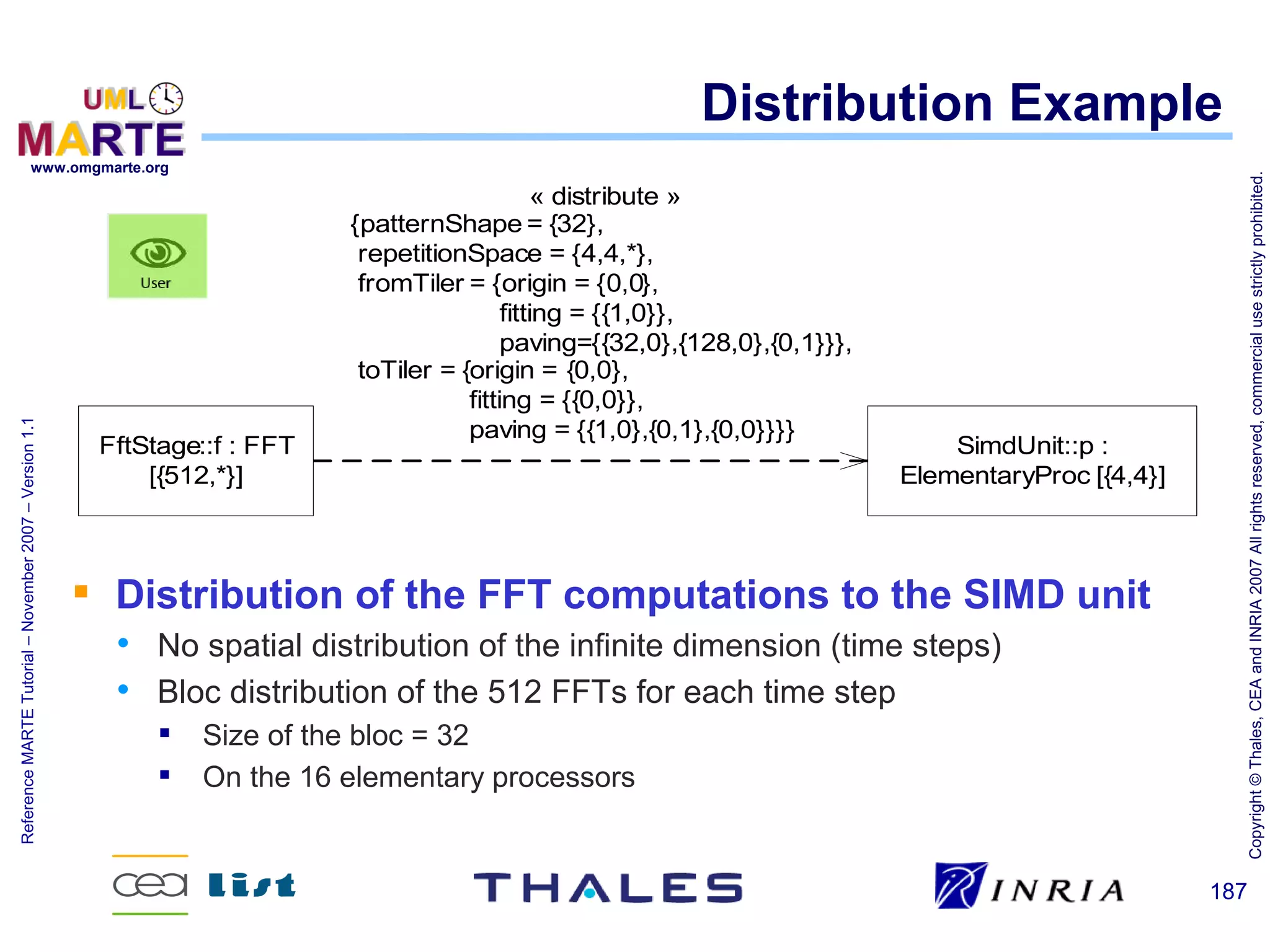
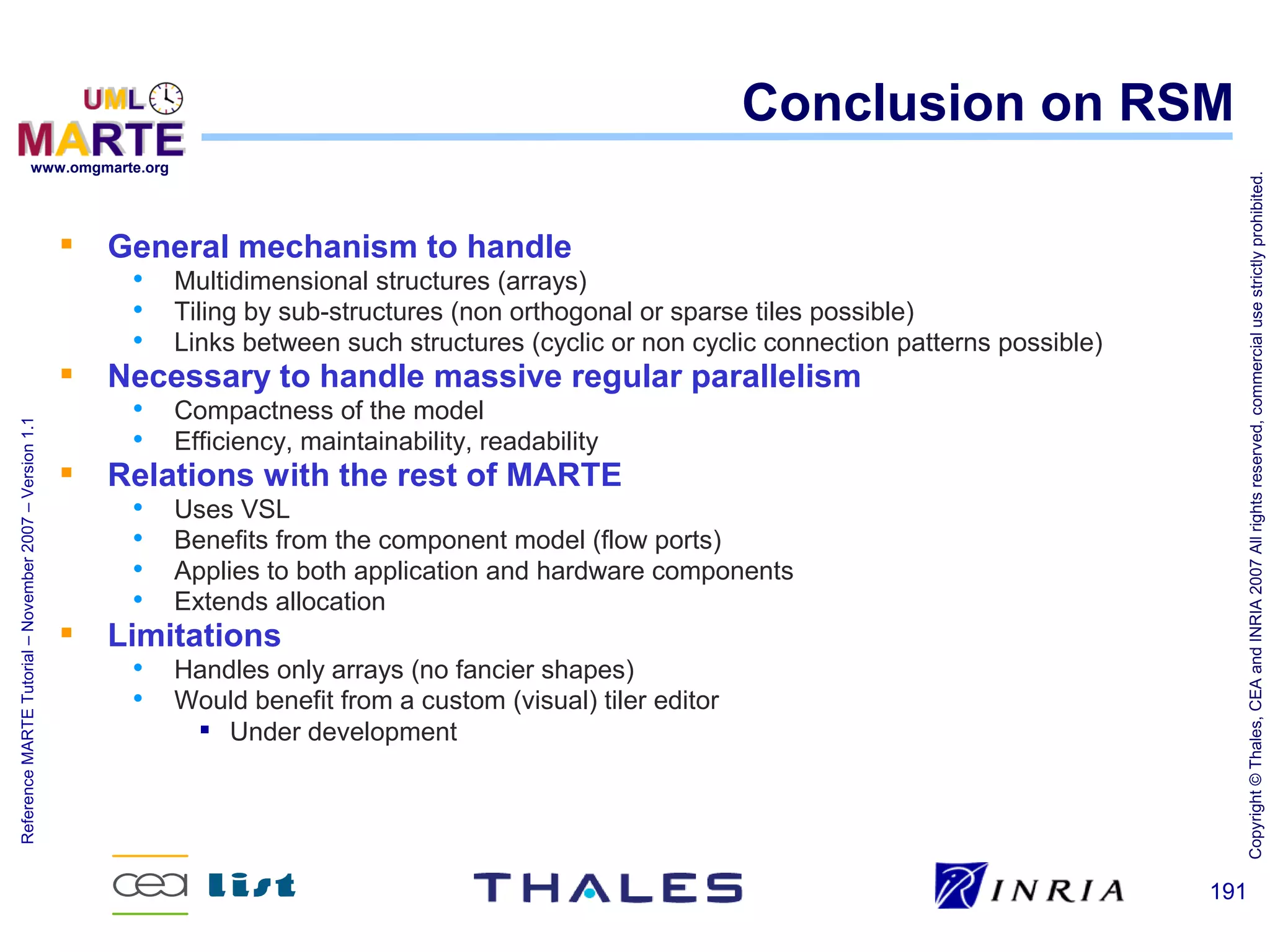
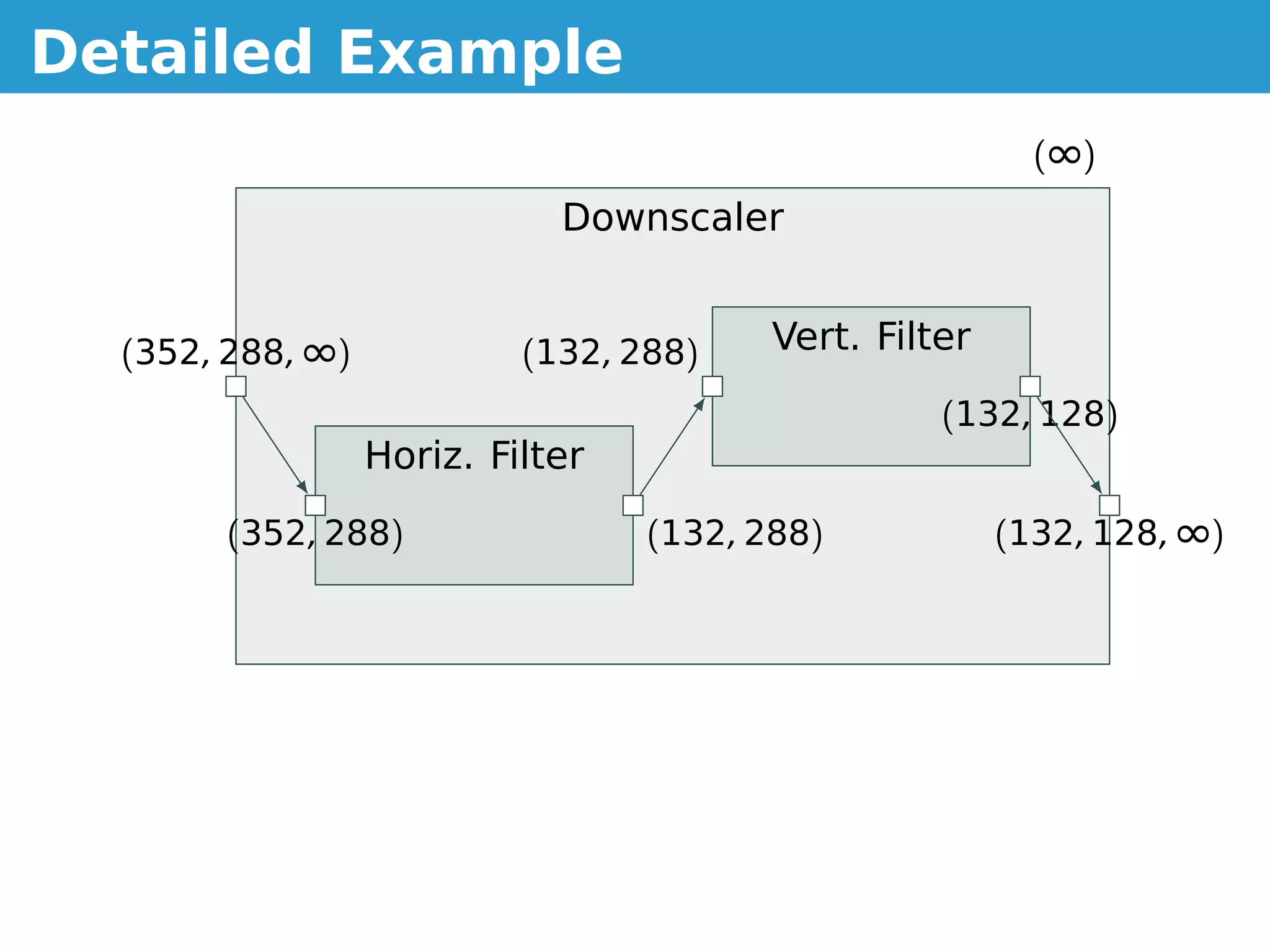
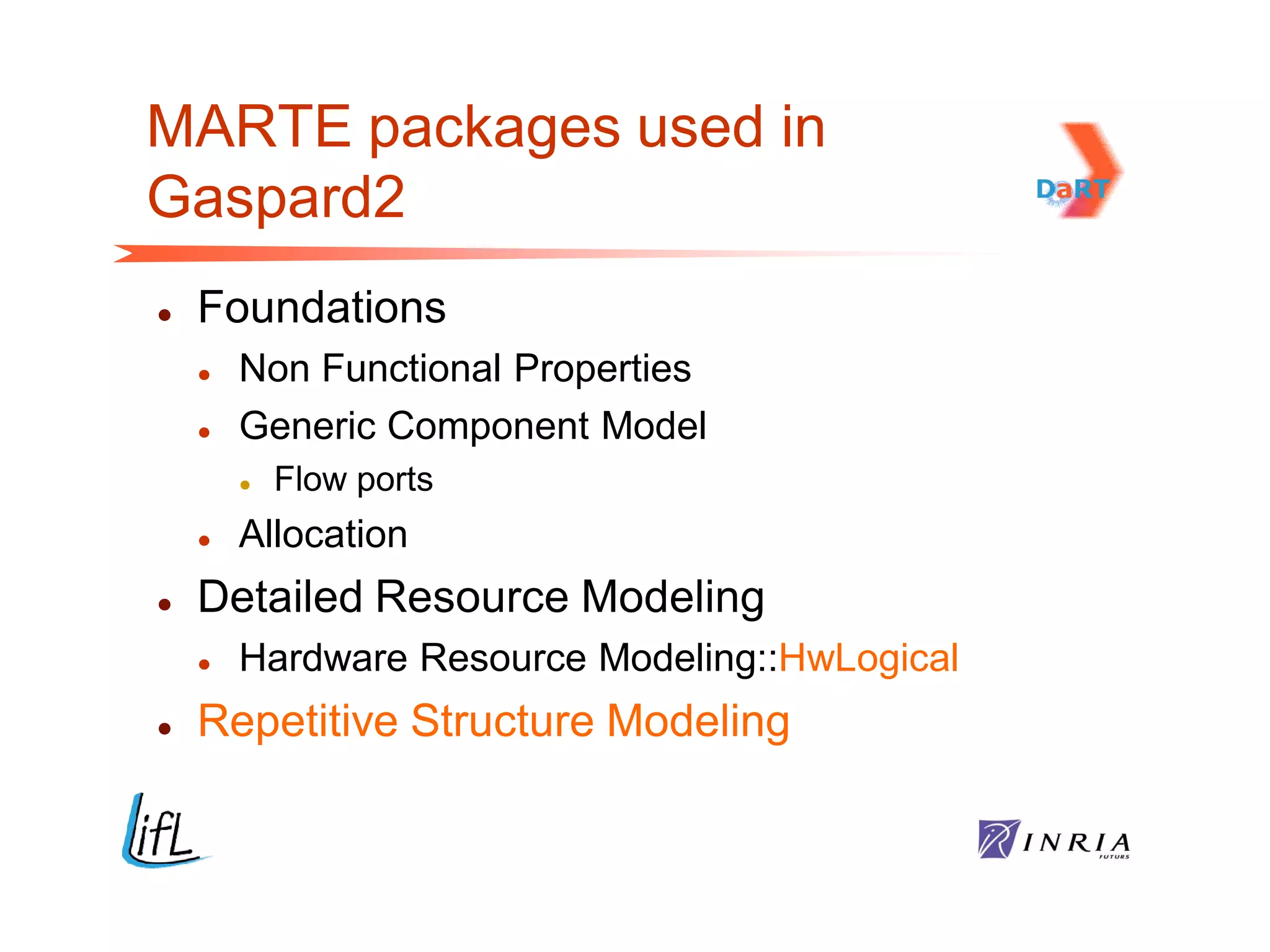
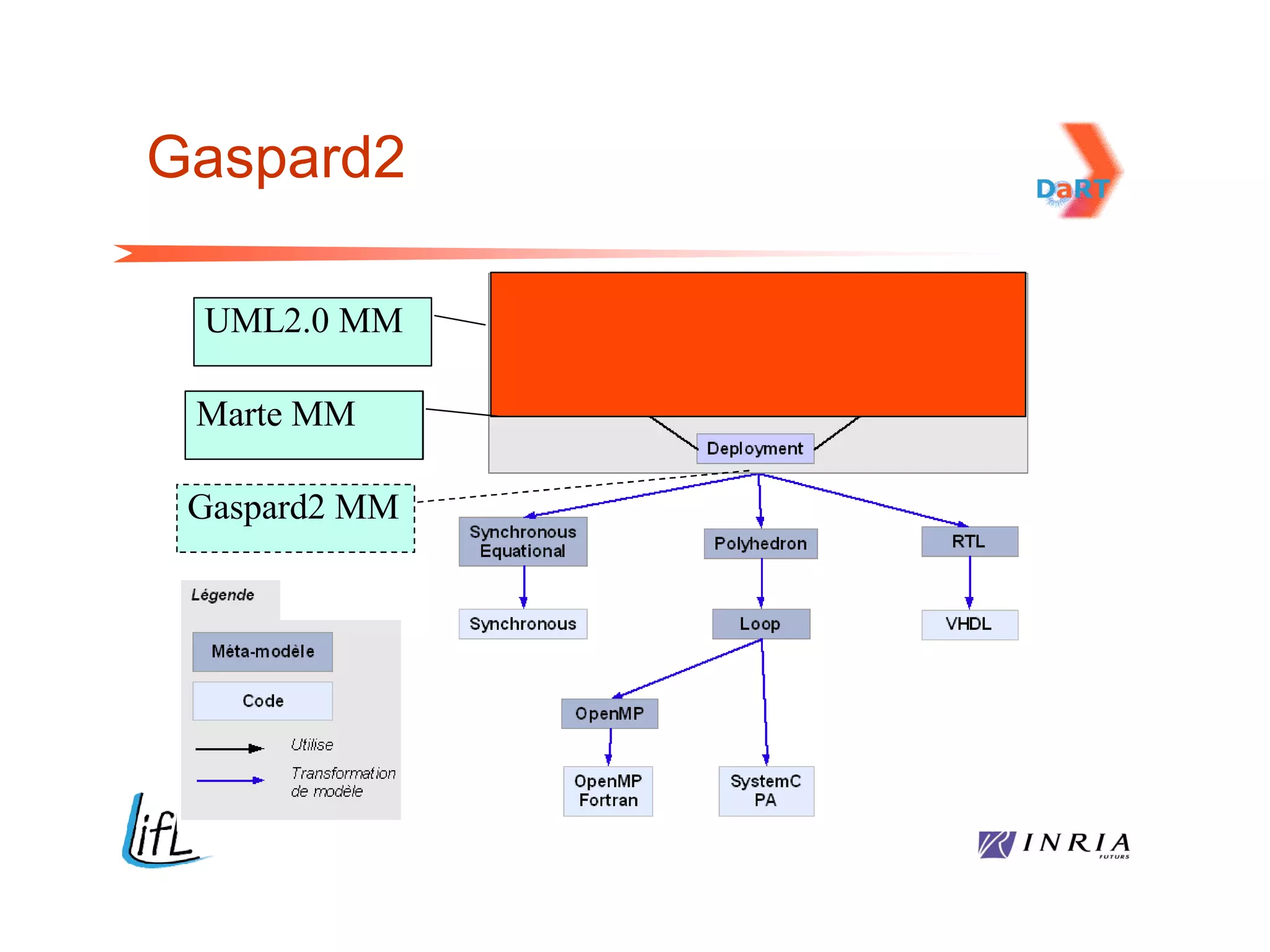
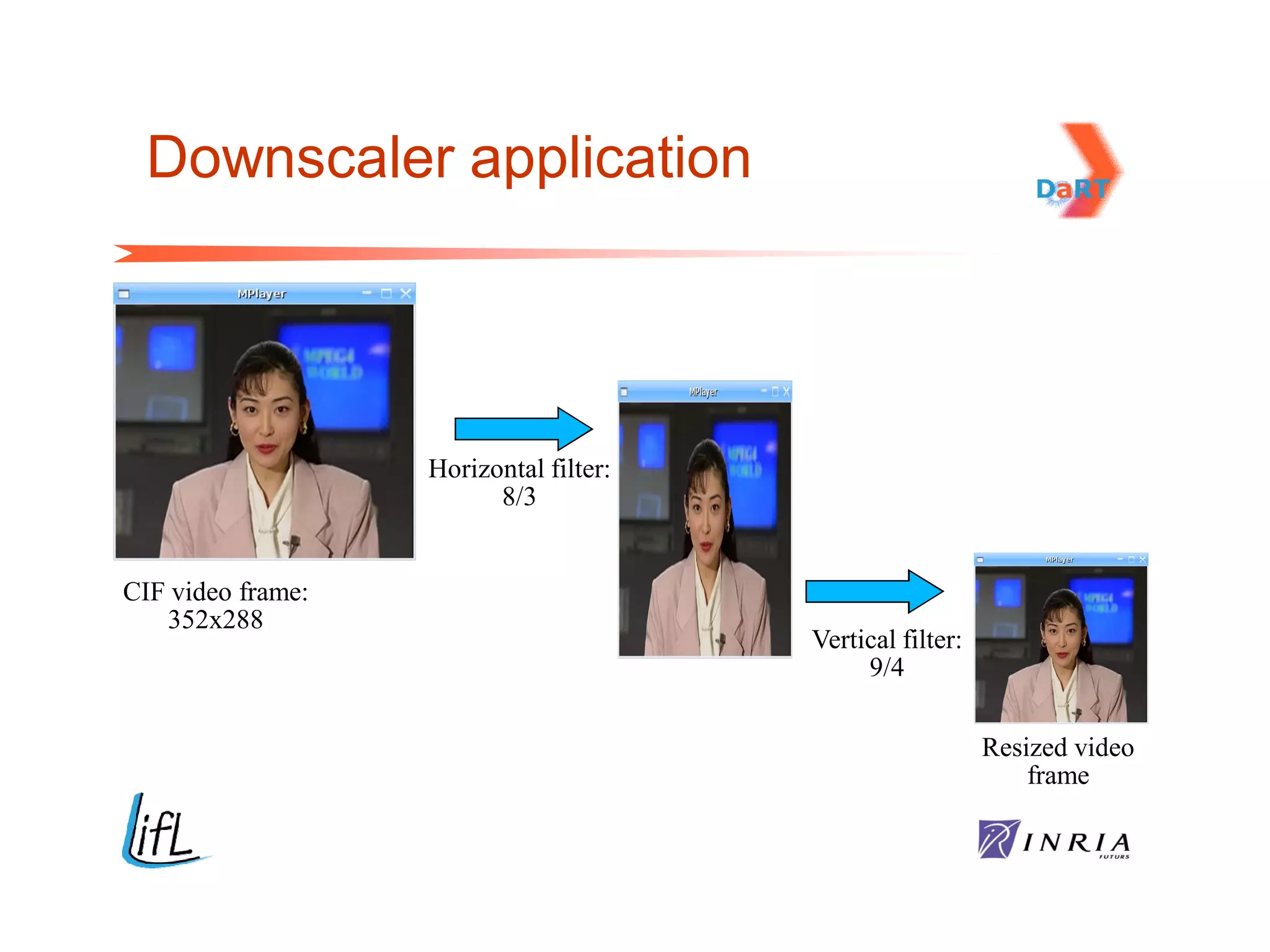
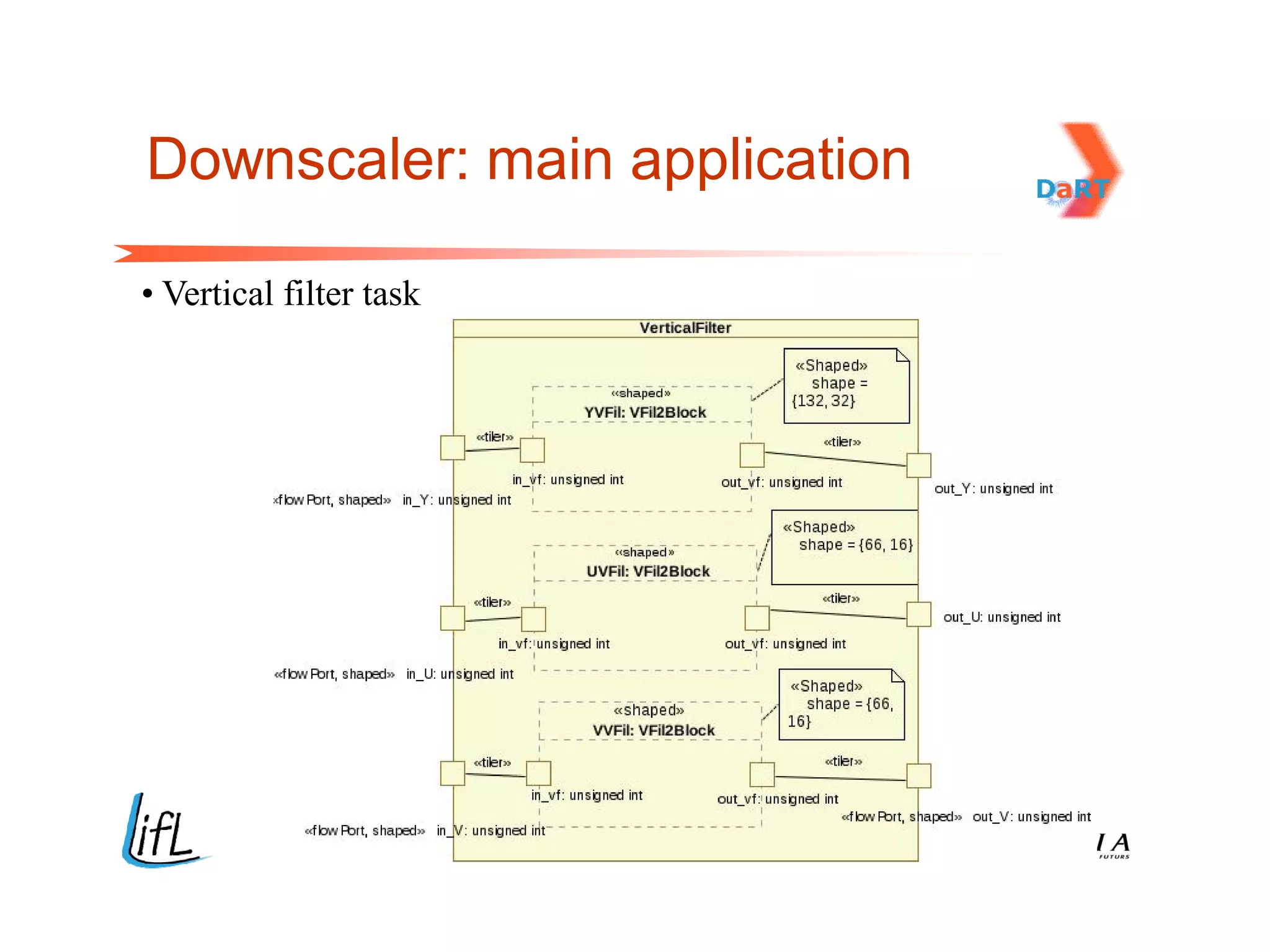
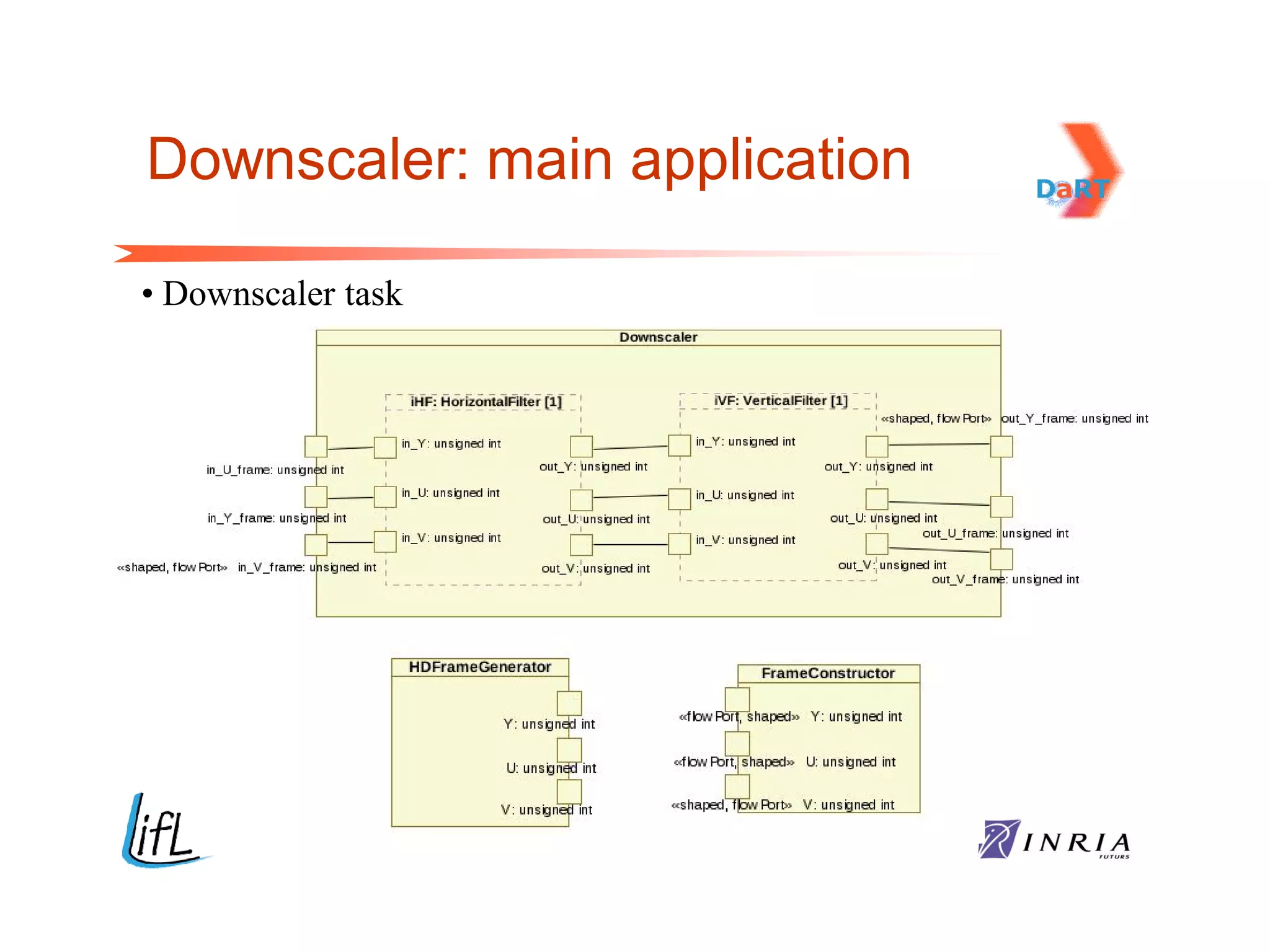
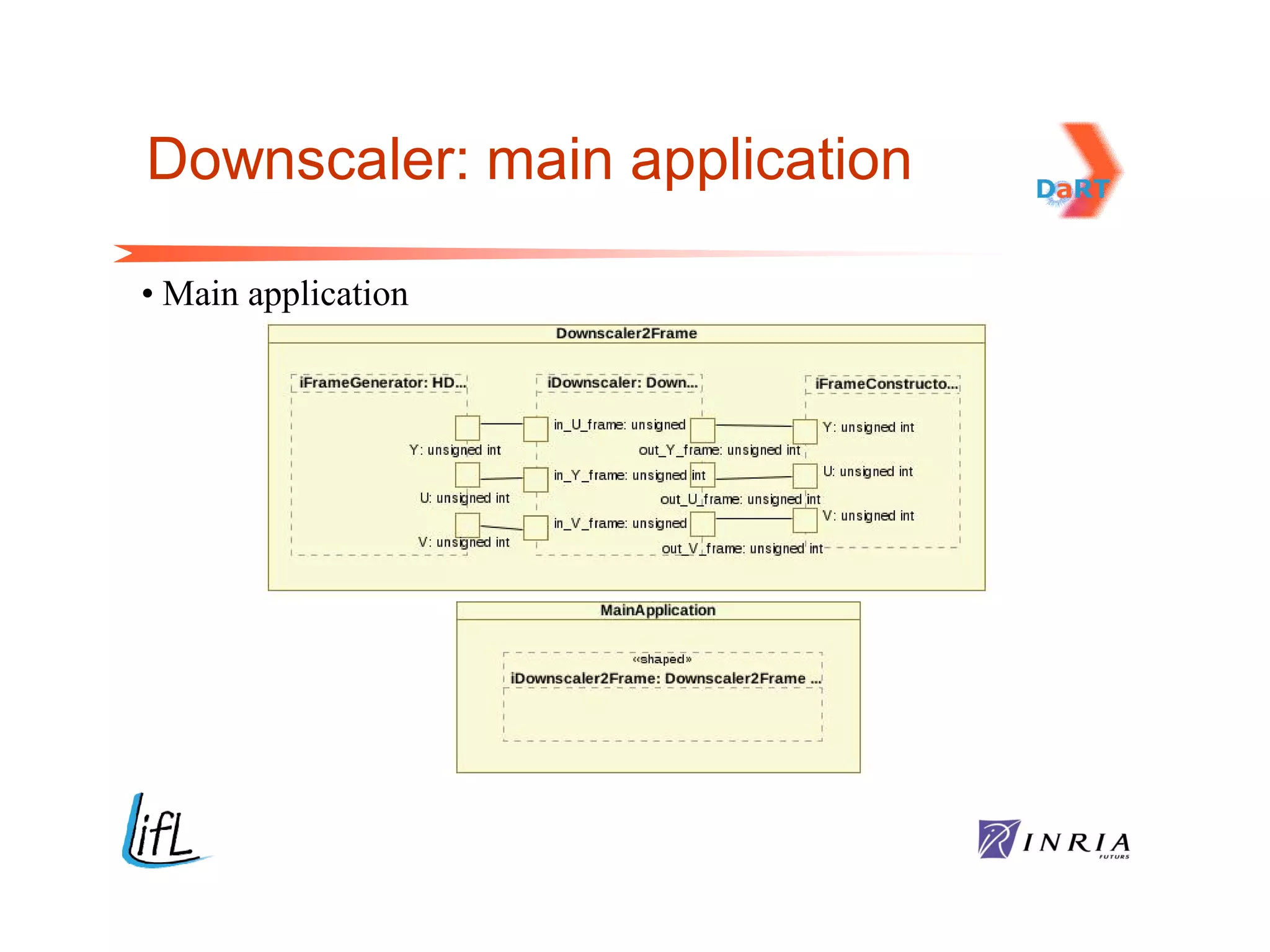
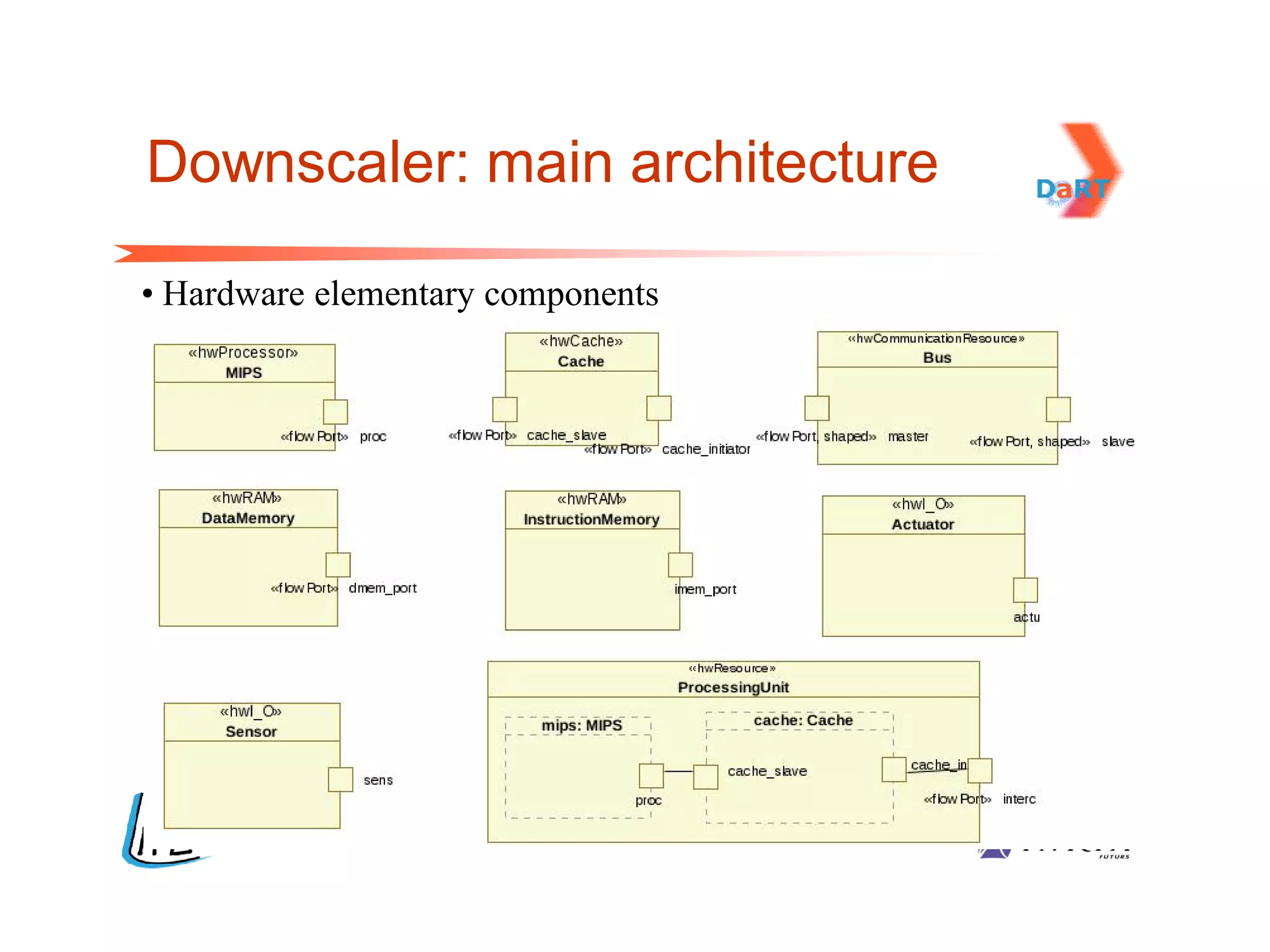
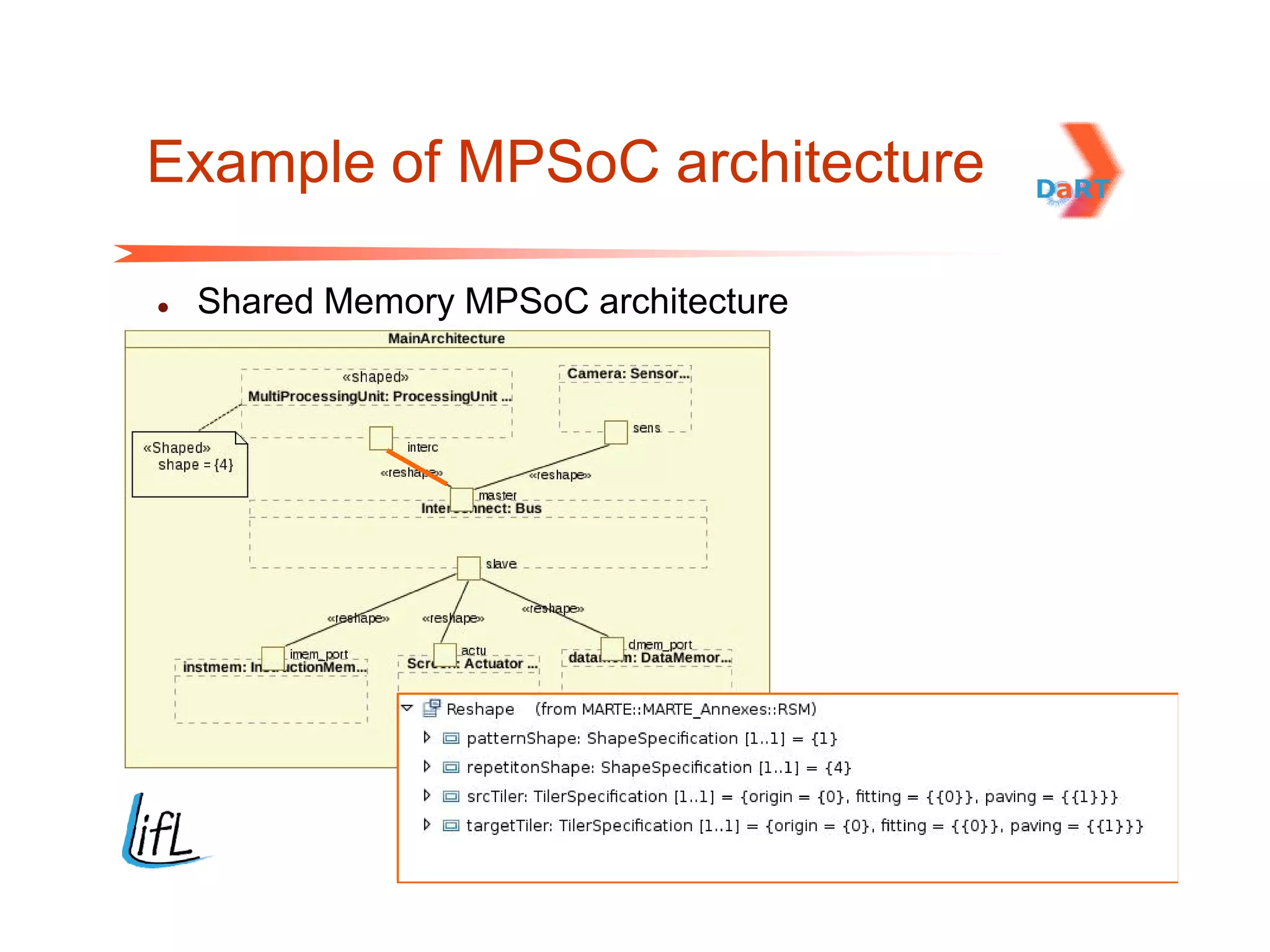
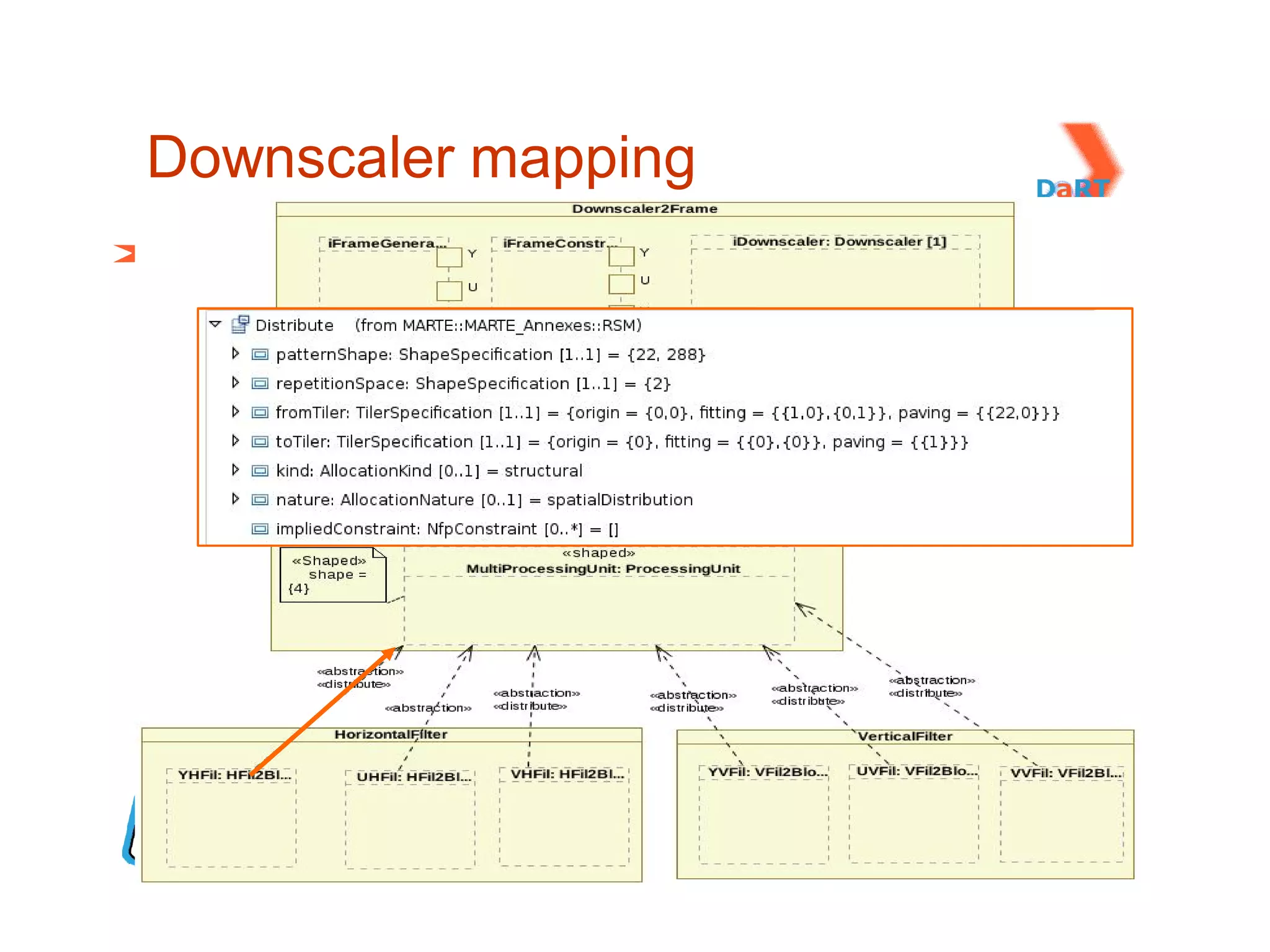
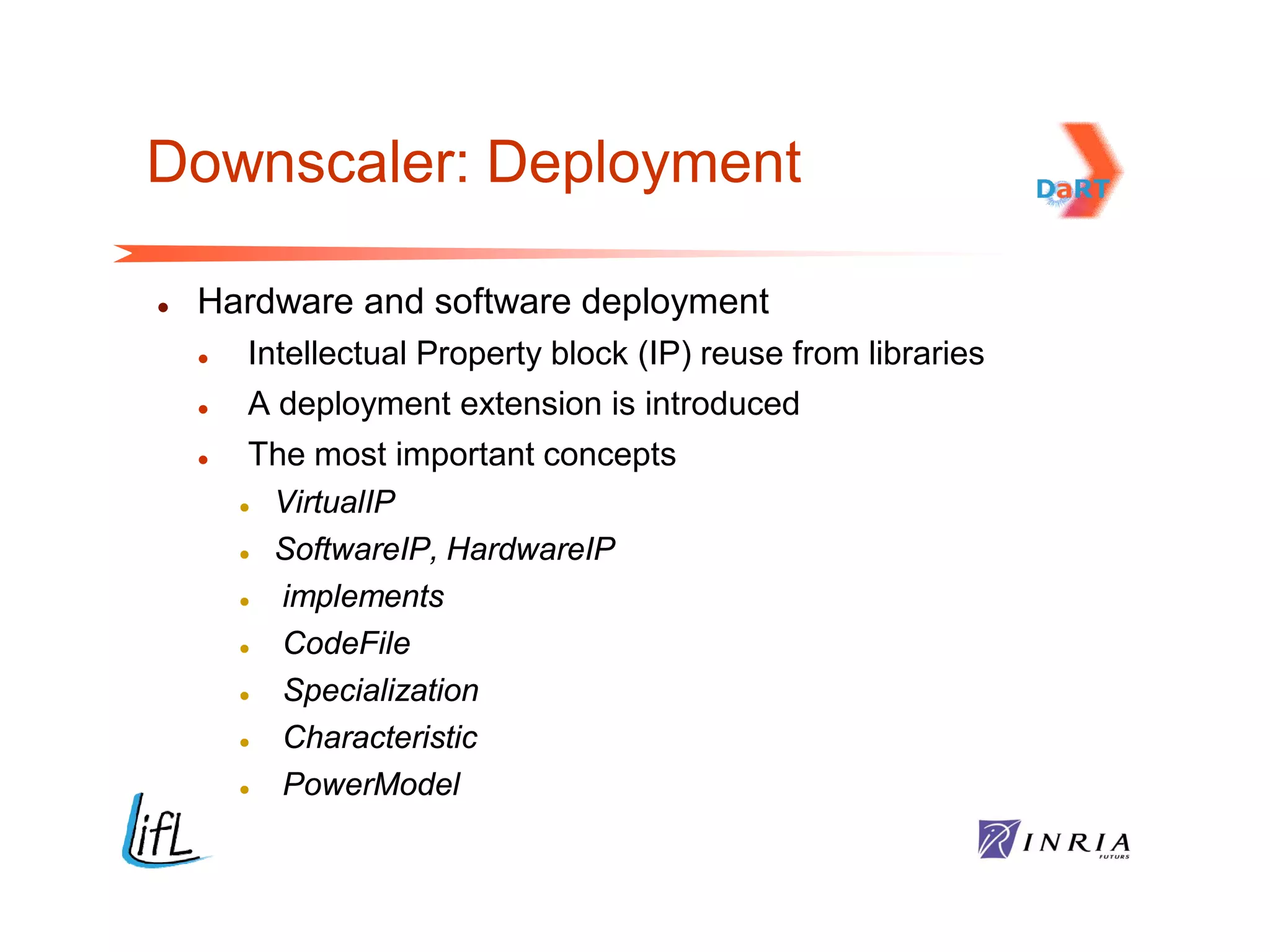
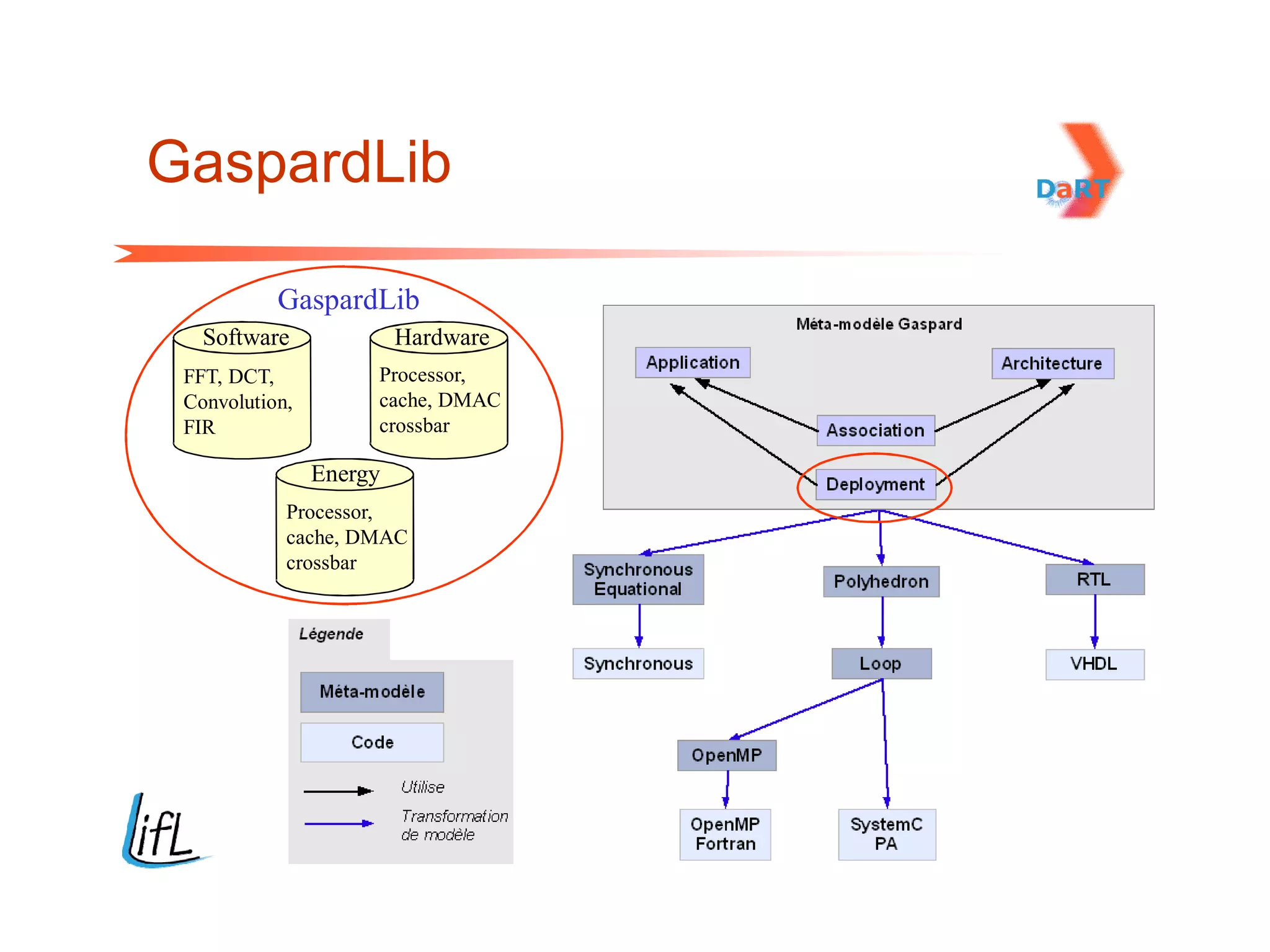
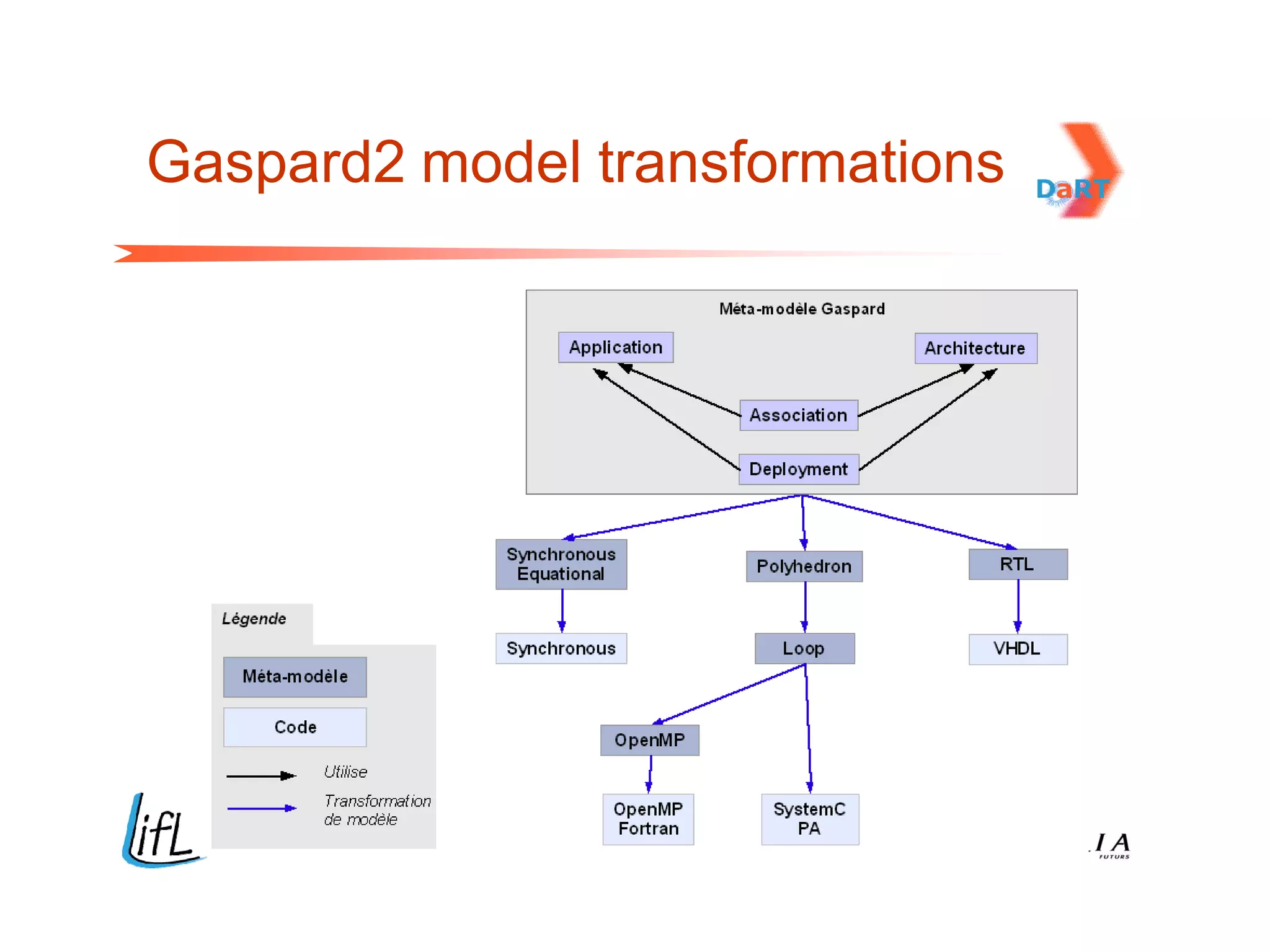
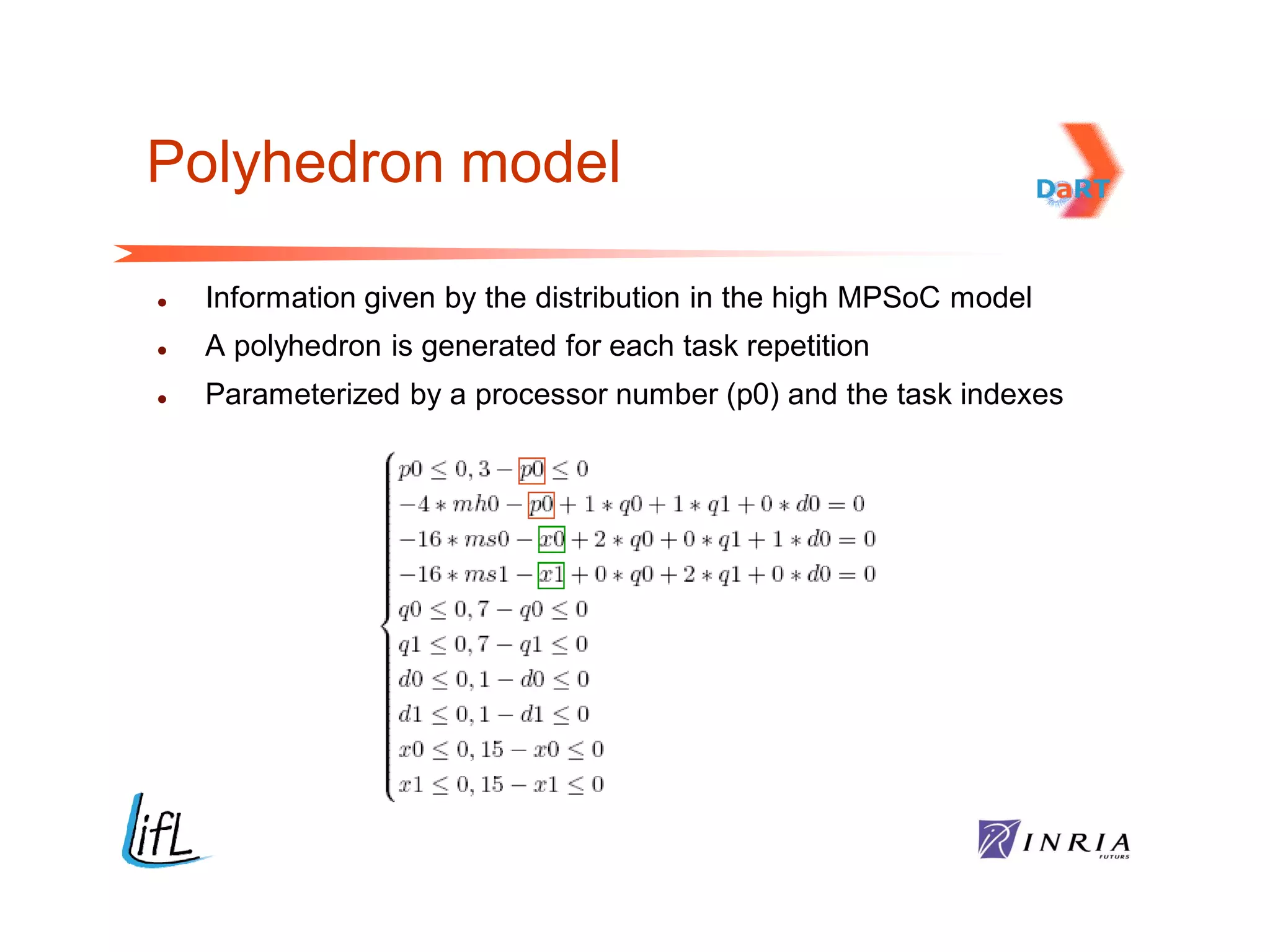
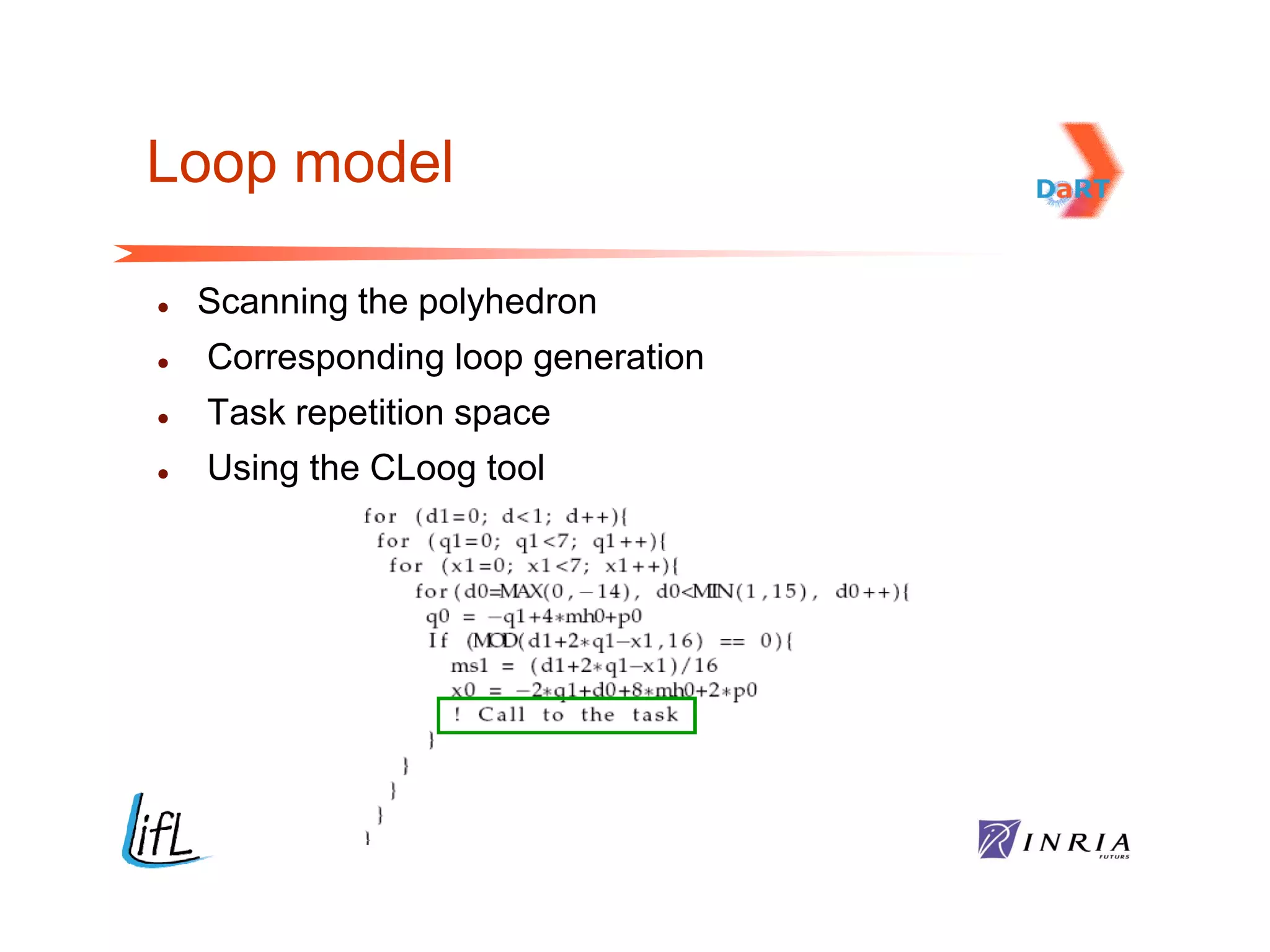
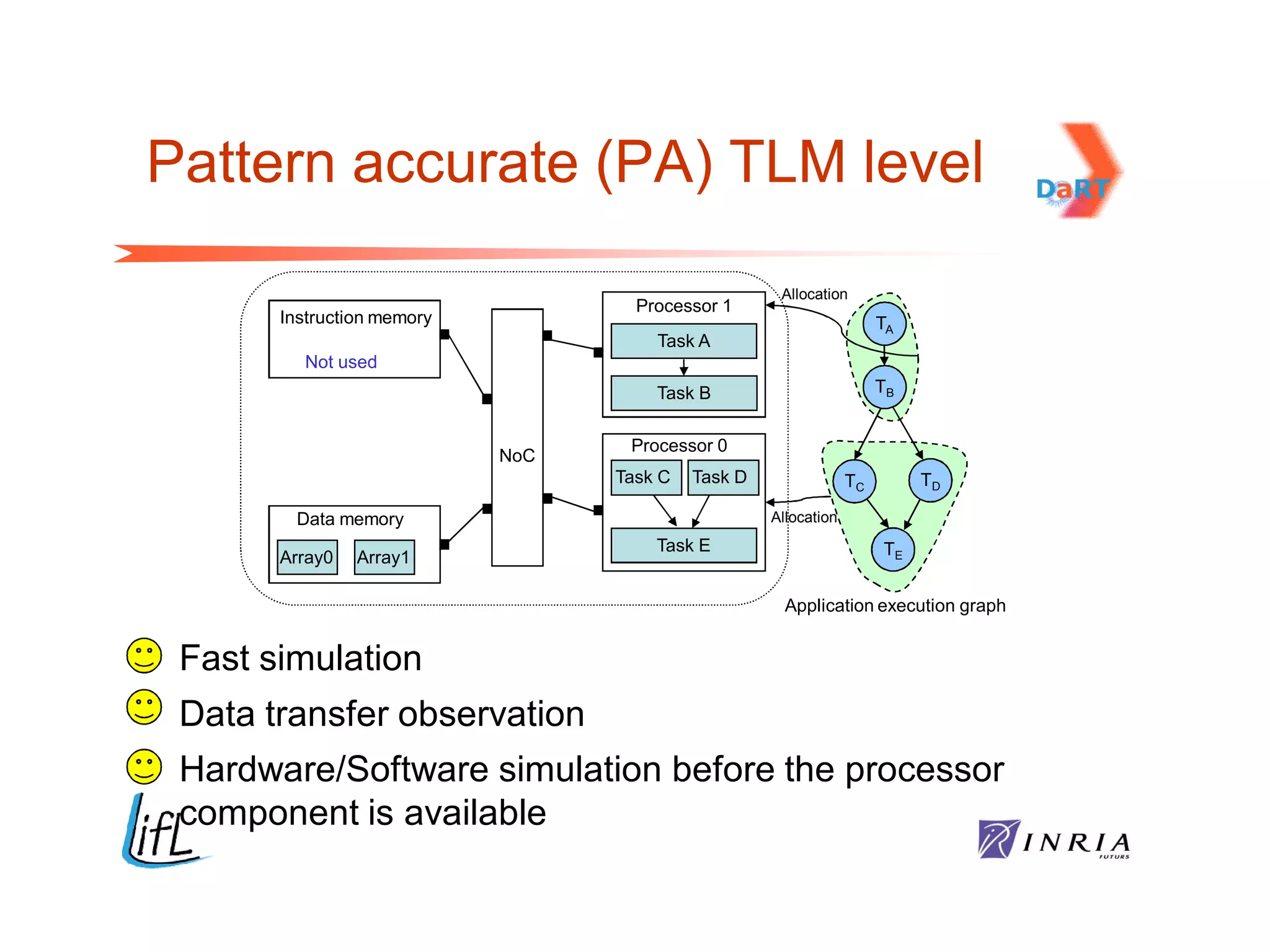
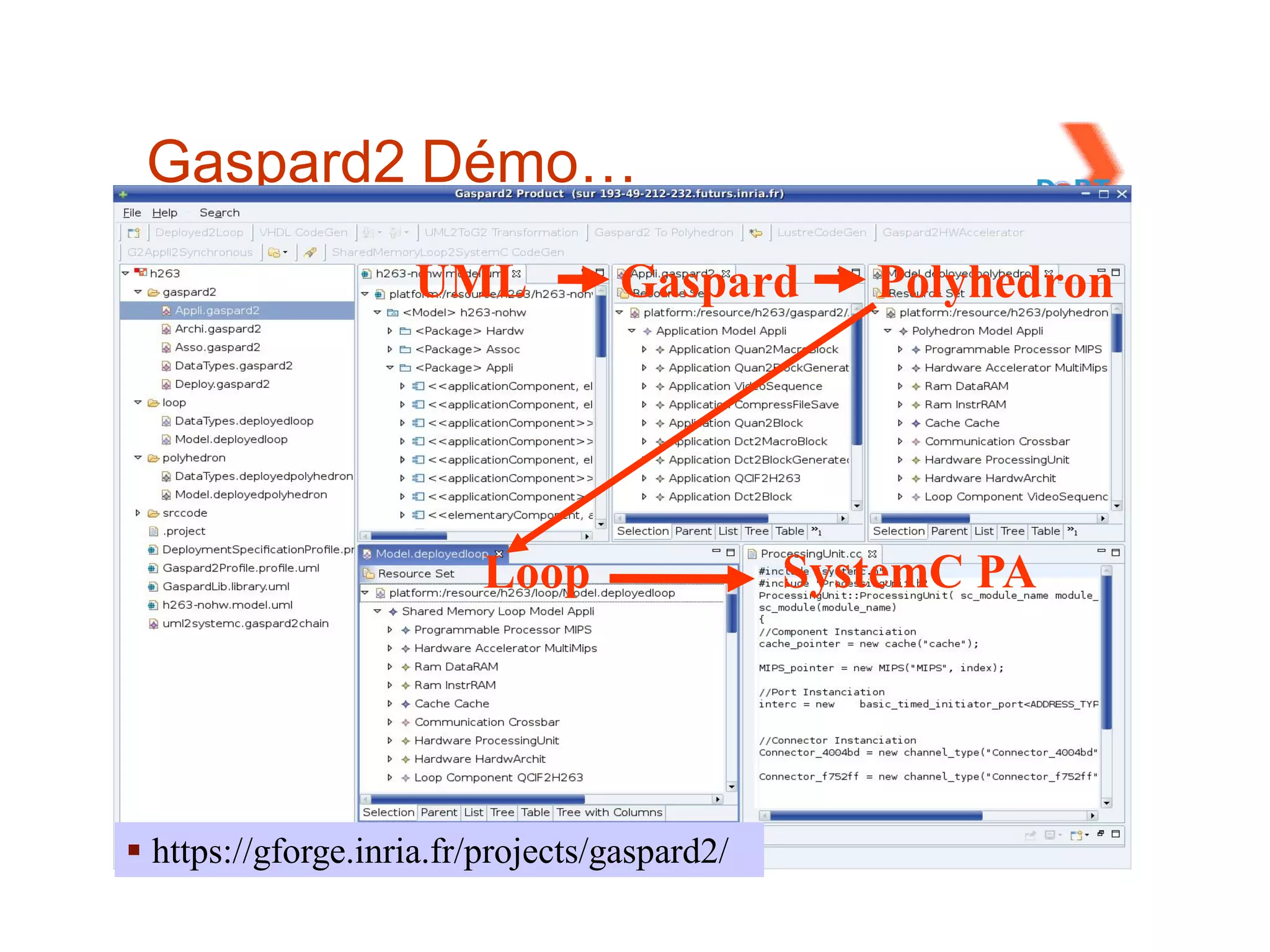
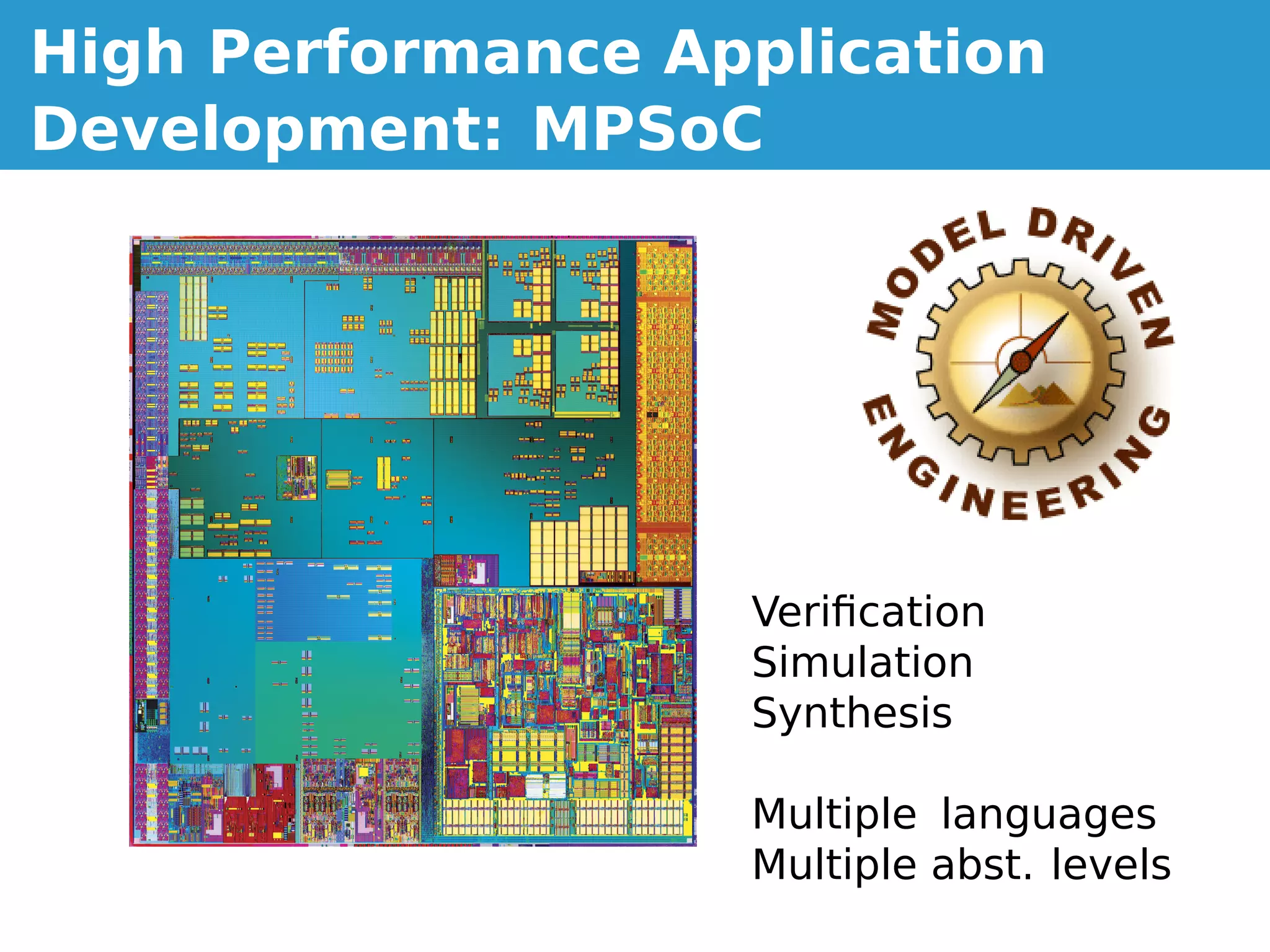
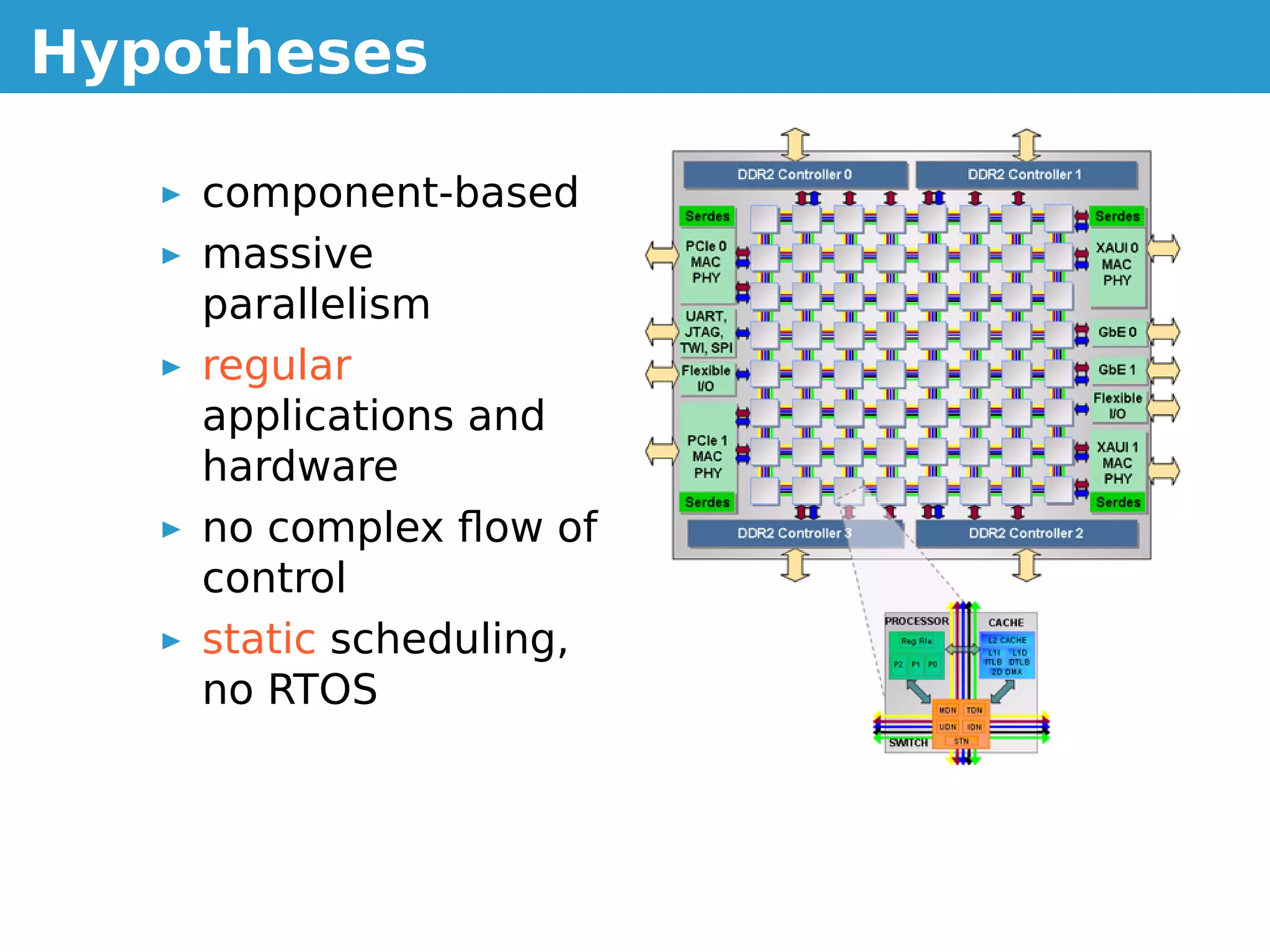
The document provides an overview of the Gaspard2 modeling language and framework for modeling dataflow-oriented applications, with an emphasis on signal processing systems. It describes the key concepts in Gaspard2 including its component-based design, support for parallelism, use of UML profiles, and ability to model applications and hardware. The document also outlines the MARTE standards used in Gaspard2 and provides examples of modeling constructs for tasks, dataflow and allocation.





![!
!! ! # $
% %''(
) !! *
) ++
C!C
D))0-EEFFFGH*,,1448,5(5*,HDG1,IE
AB
,
J;$/KL9$M$H1#)*H)-$(5*()35#GI5,*,+NH5*G2,O
PQ*(H*,$;(03#1R*S$LT*()35#$'T,*,+S$L*21Q*#$9*D*$*#+$V,T+T,3H$9D1:*(G$$
KW7K$MH1#)*H)-$715,)GX5Y(3:1#5N(10D3*G3#,3*G2,O
A
JD*,45($#+,TS$715,)$+5$L3:1#5S$Z35,,5$[1Q45)
9D*45($979$MH1#)*H)-$/*Q,5#)G,31QN)D*45(I,1Q0GH1:O
@
*+5453#5$V*QI],5S$/*Q,5#)$731QS$L5*()35#$X5:*)D35Q
?](https://image.slidesharecdn.com/gaspardtut-111004074701-phpapp02/75/Gaspard-tutorial-10-2048.jpg)