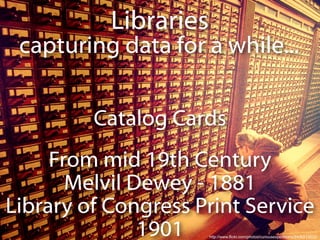
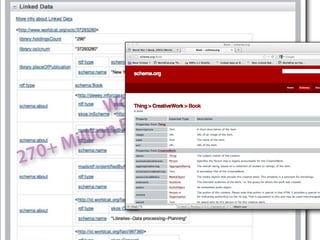
The document discusses the history of libraries capturing data from handwritten catalog cards in the 19th century to the development of machine-readable cataloging formats like MARC. It then describes how libraries are now publishing data as linked open data on the web using standards like Schema.org and RDFa, with over 270 million resources available. The talk encourages libraries to stop just copying data and instead start linking to other data sources to fully leverage the potential of the semantic web.