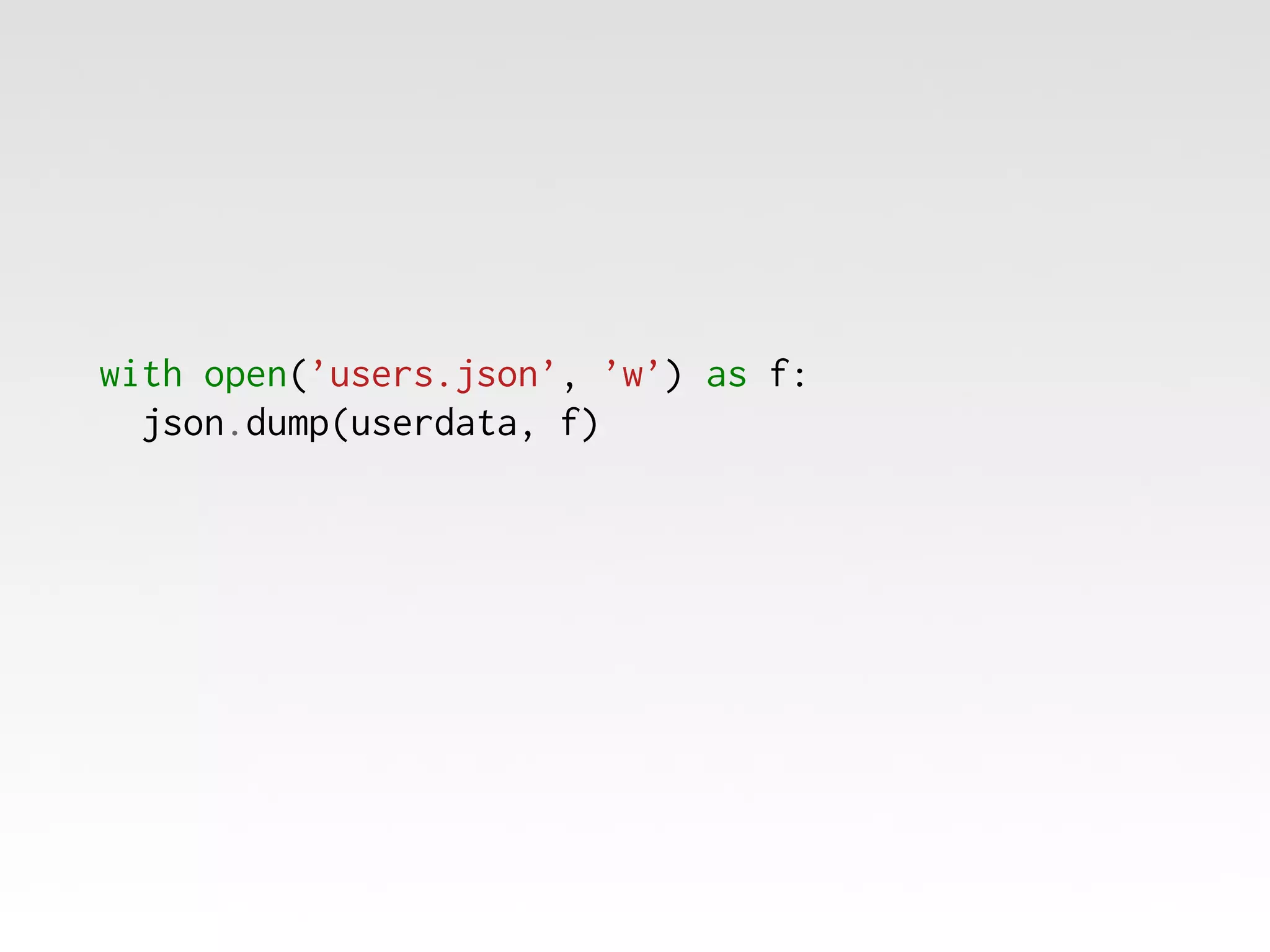
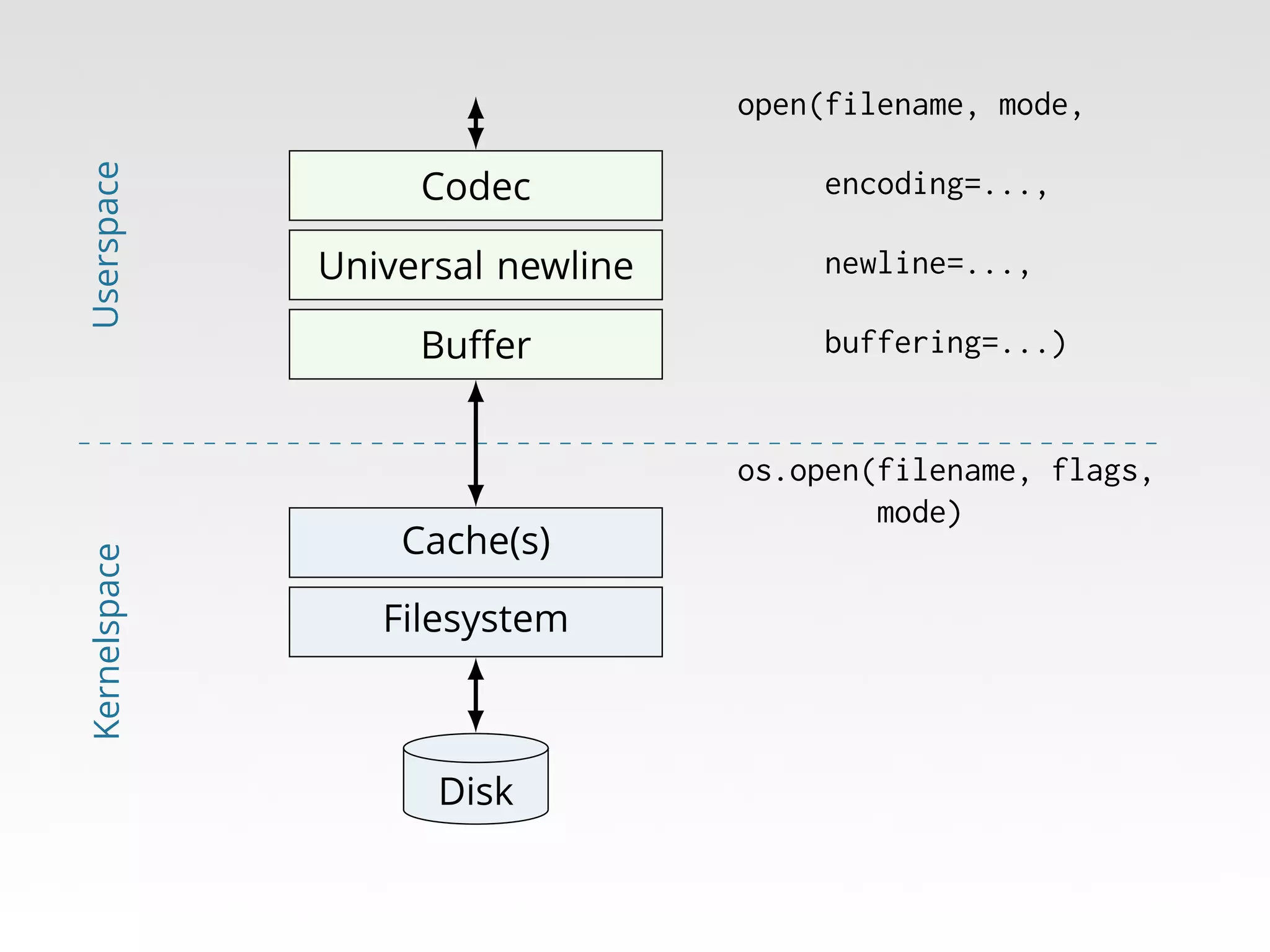
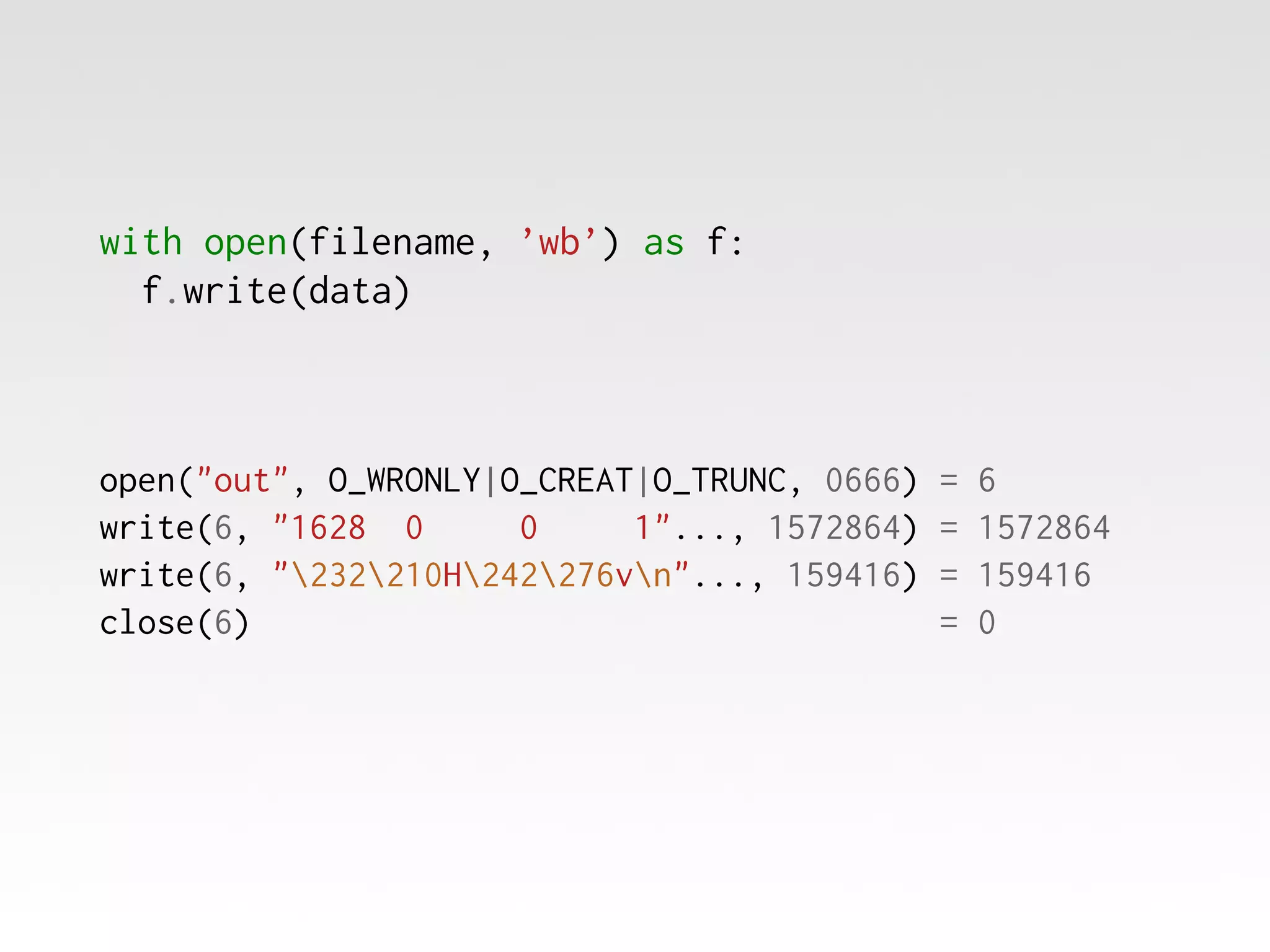
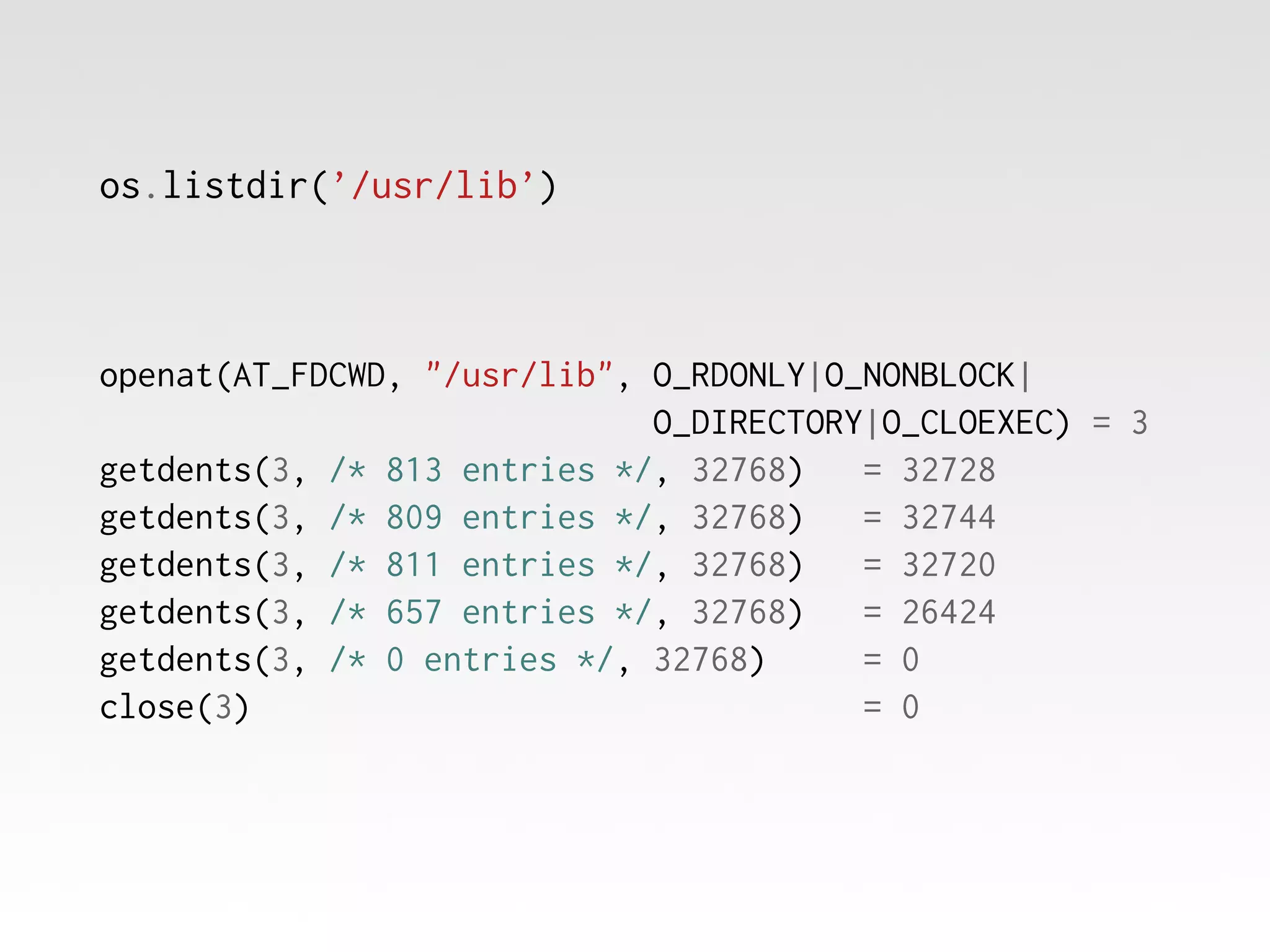
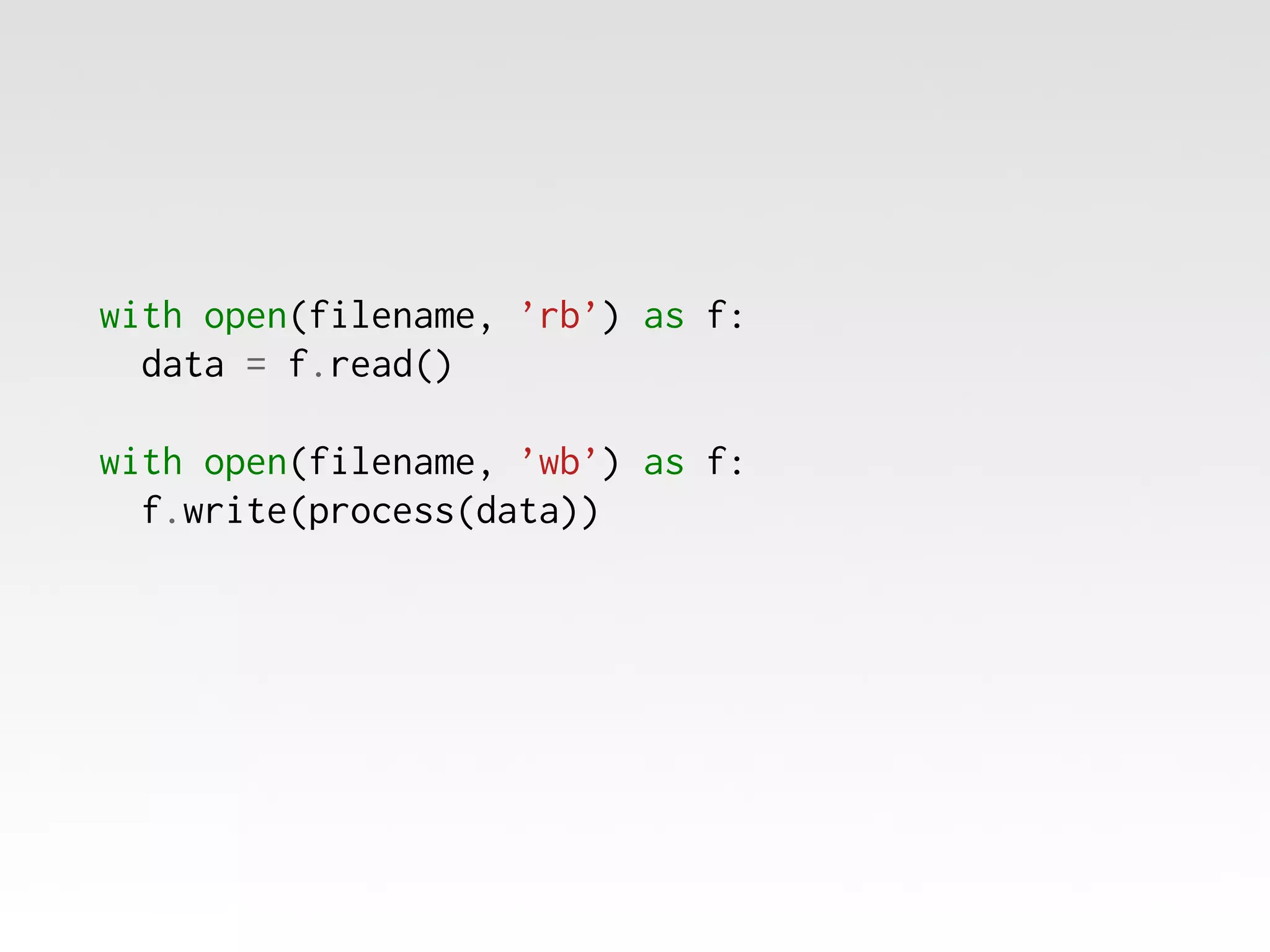
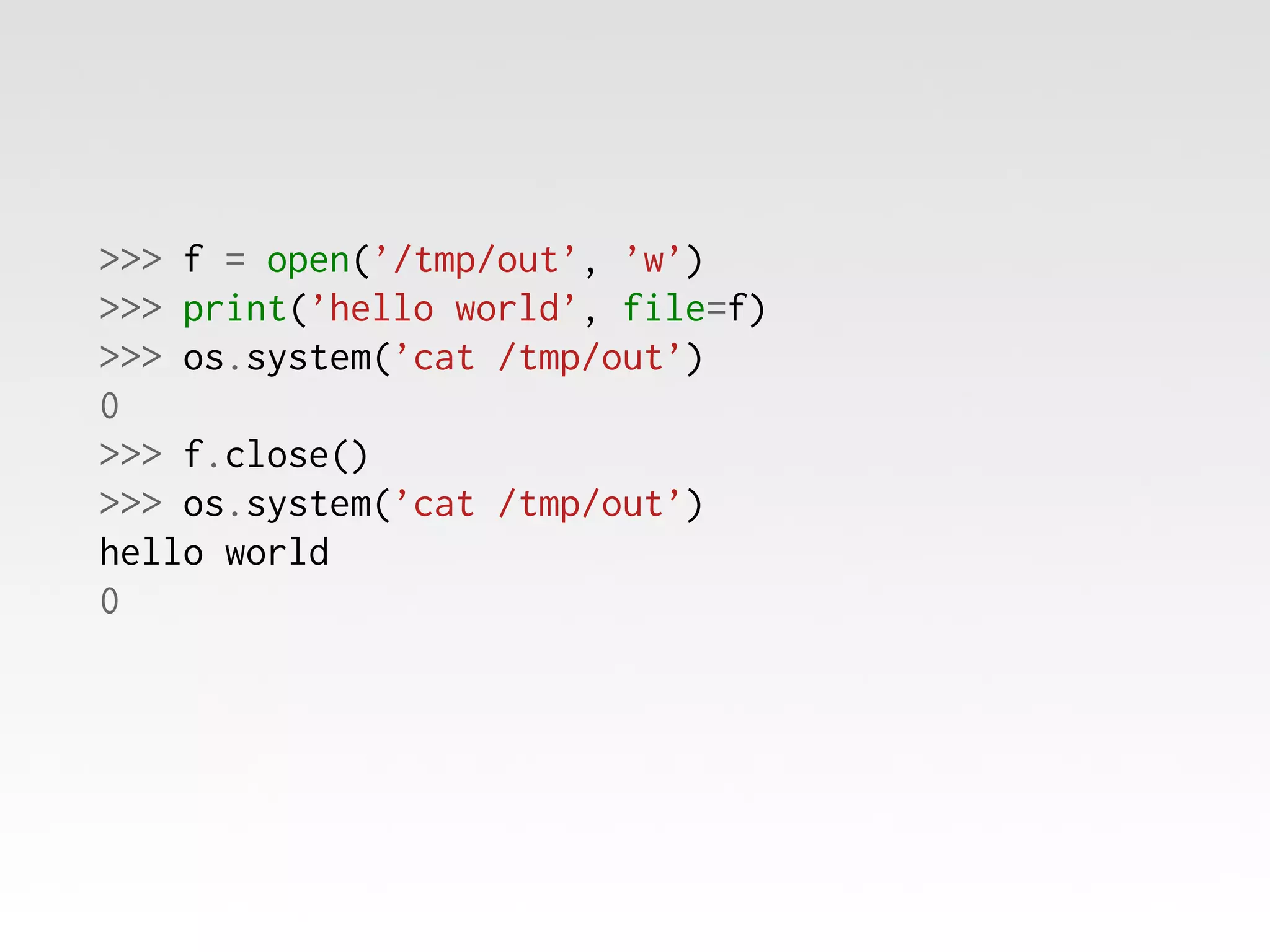
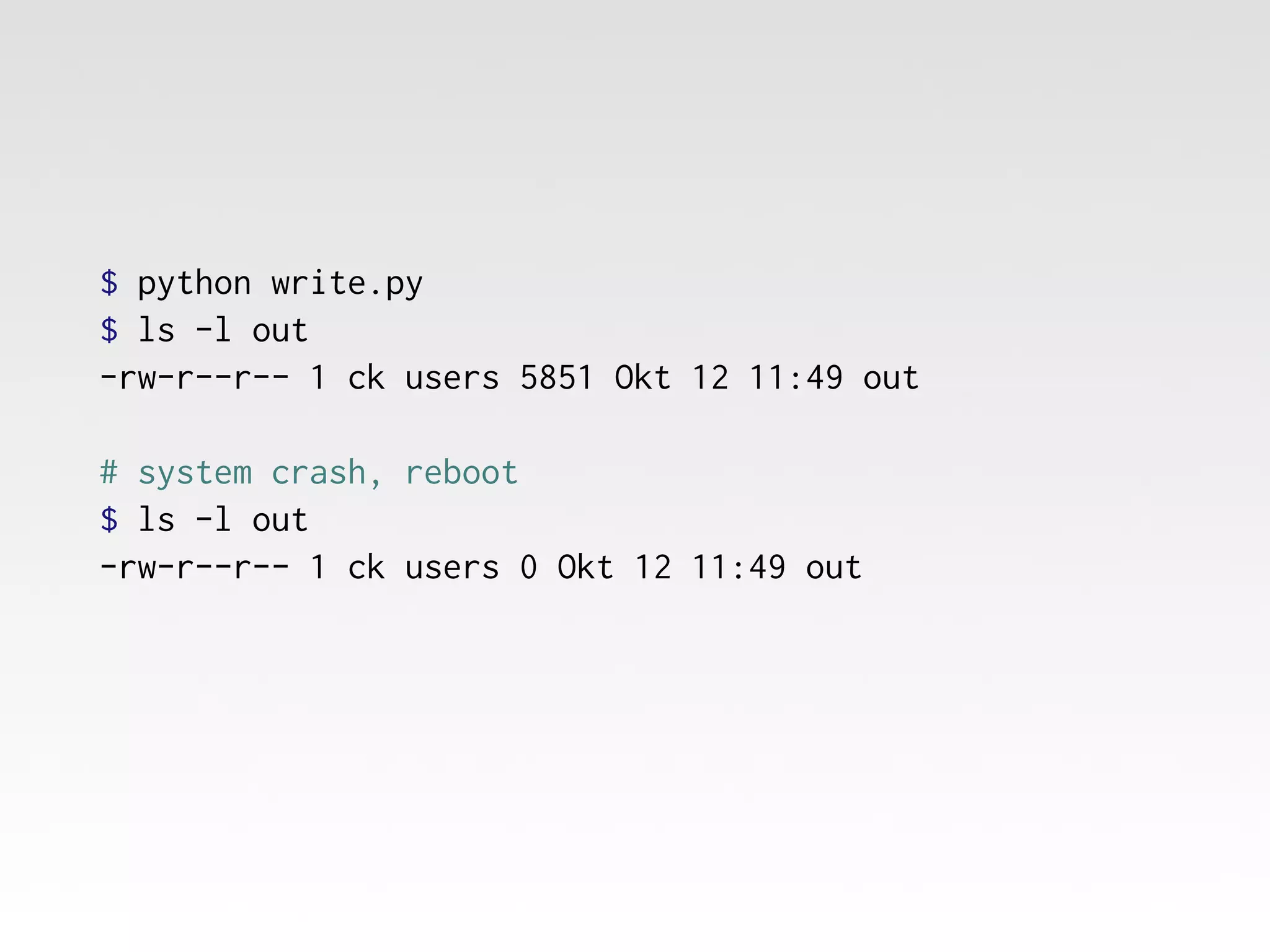
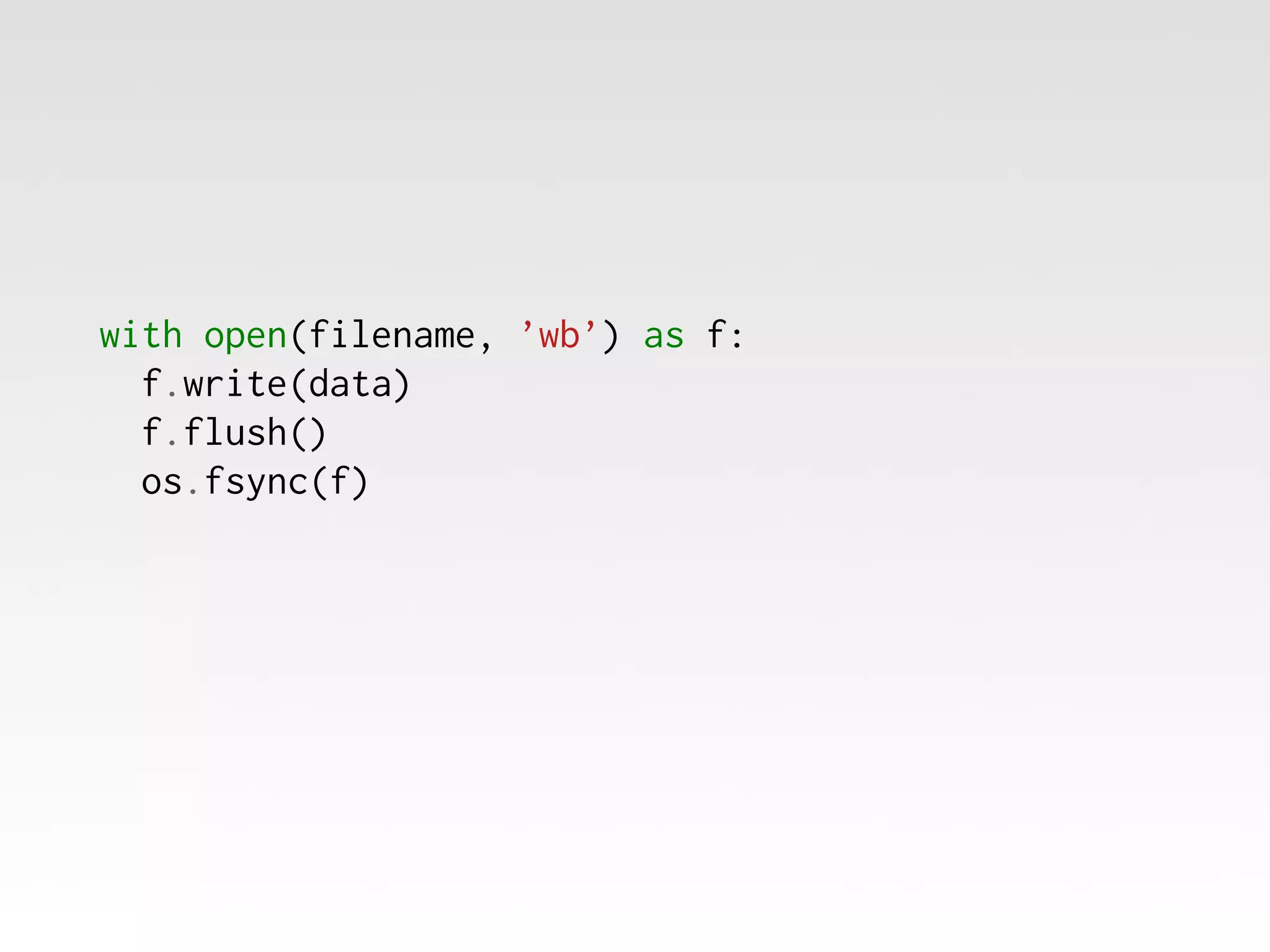
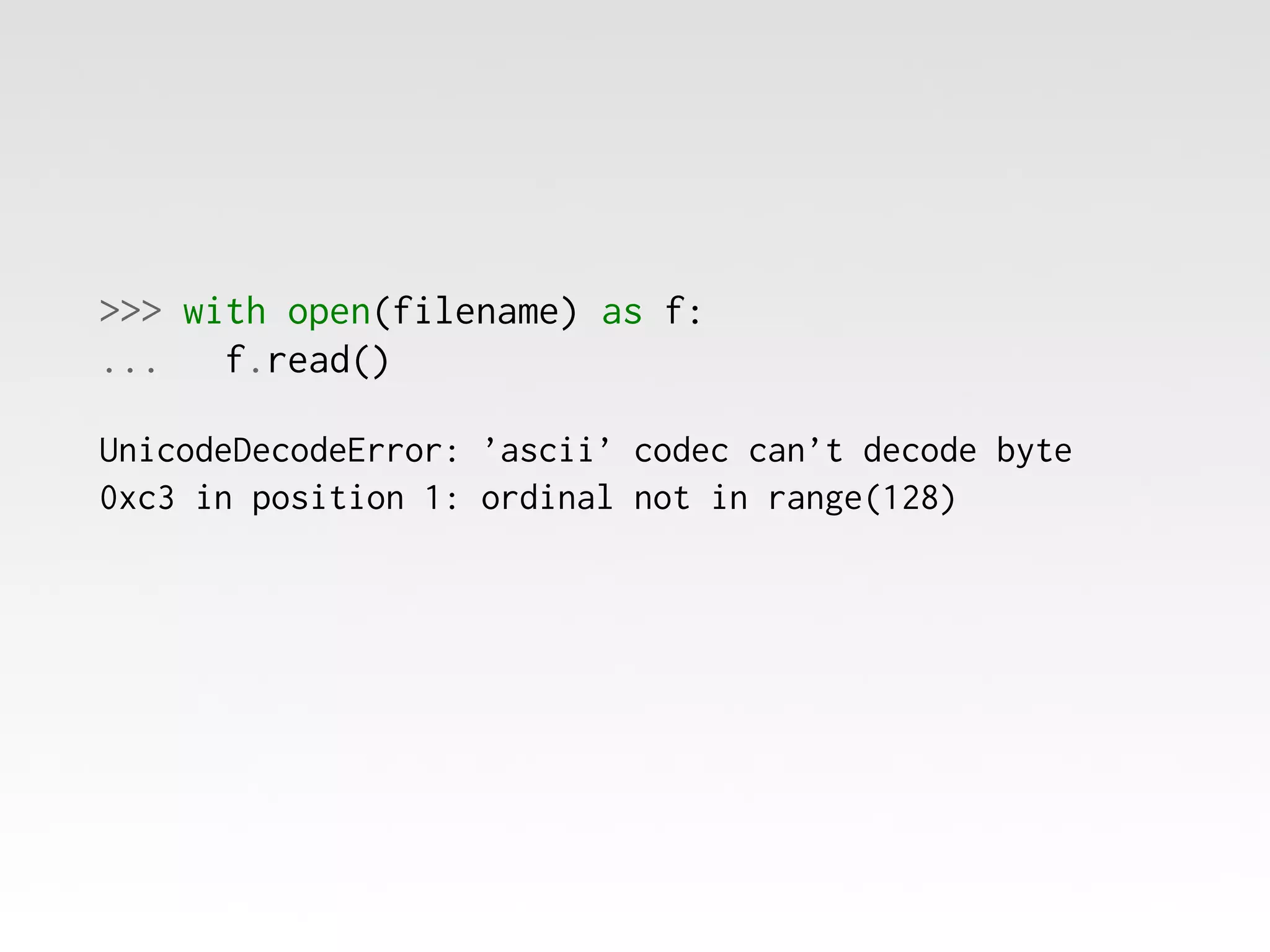
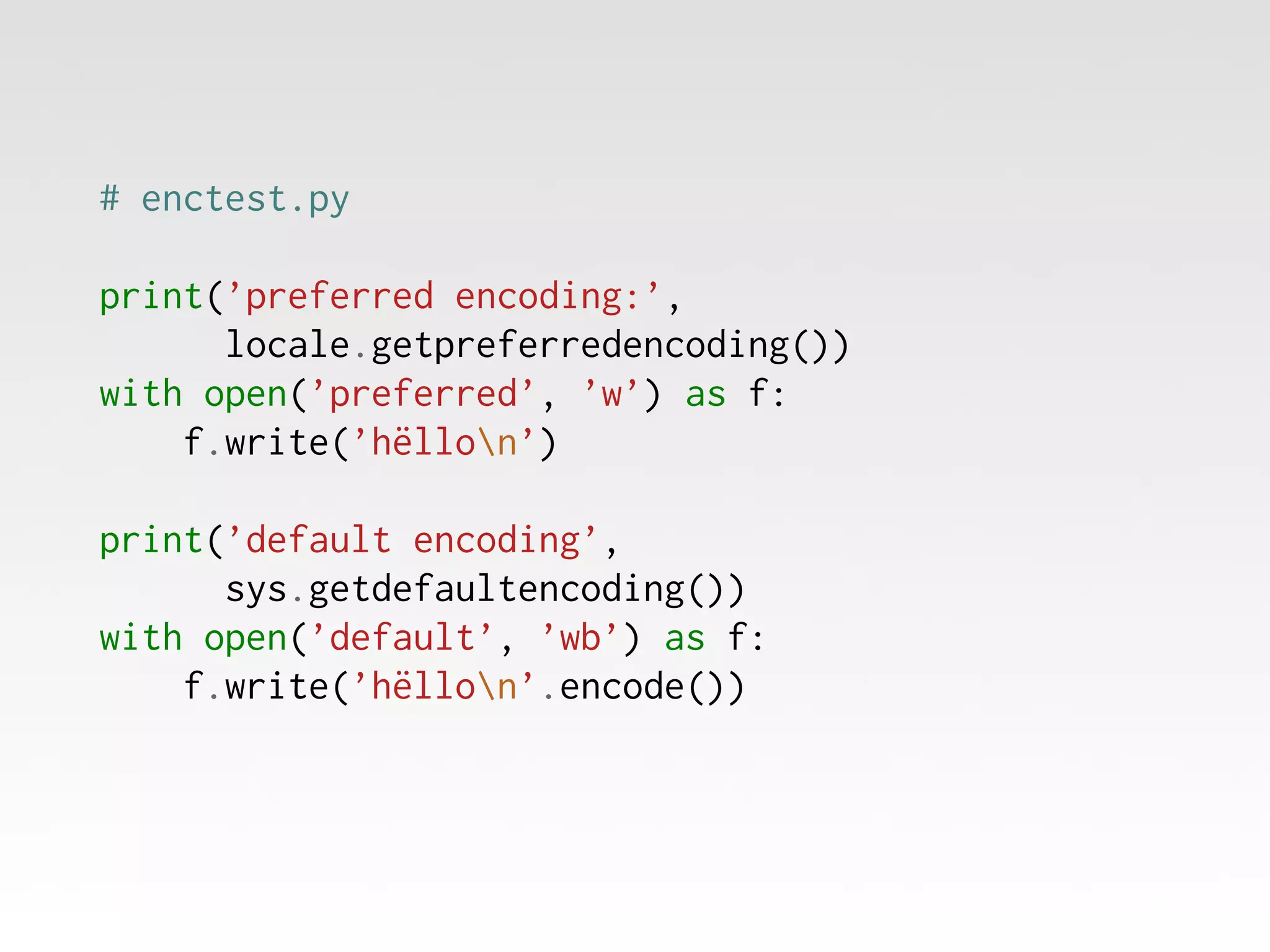
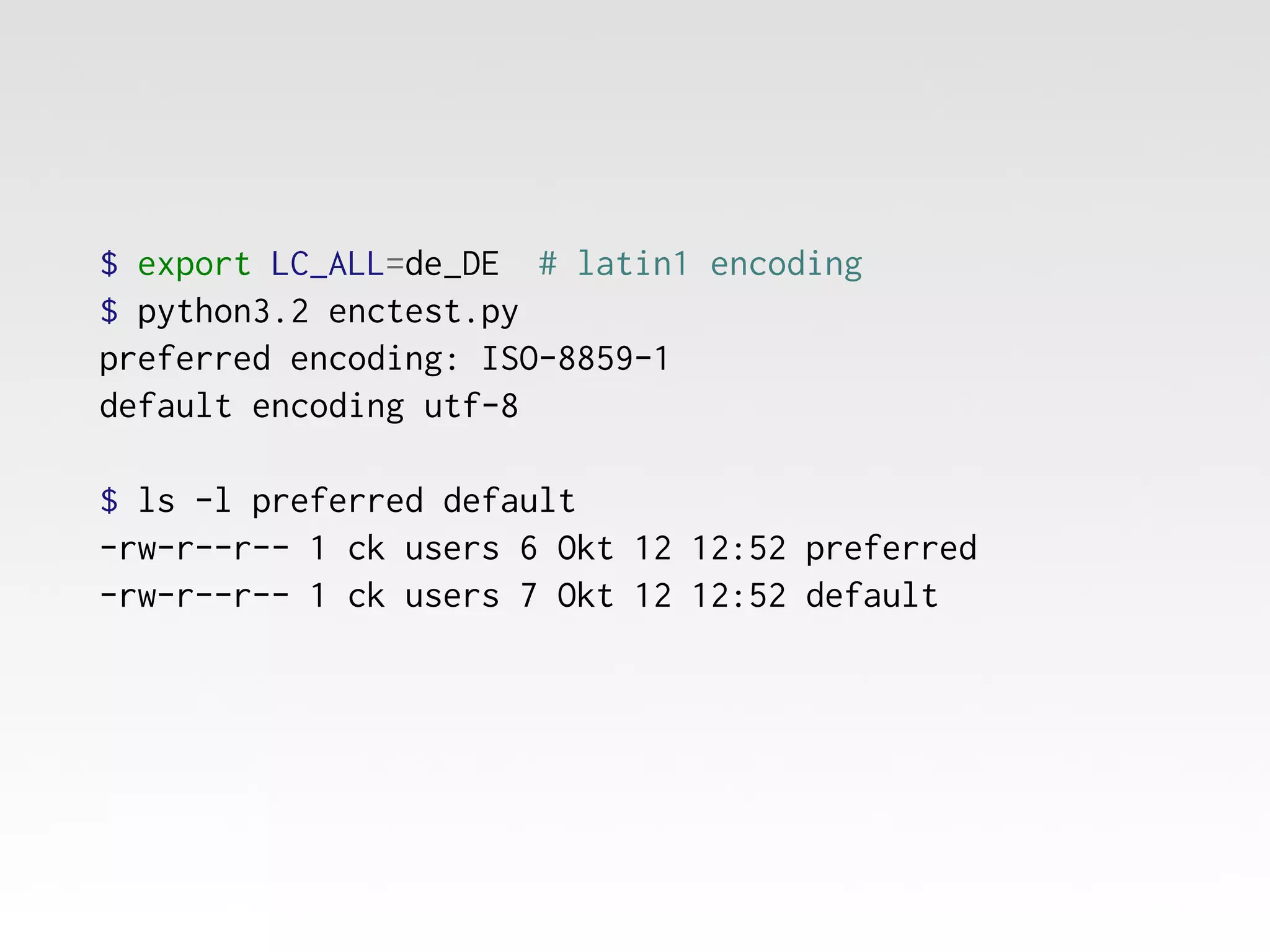
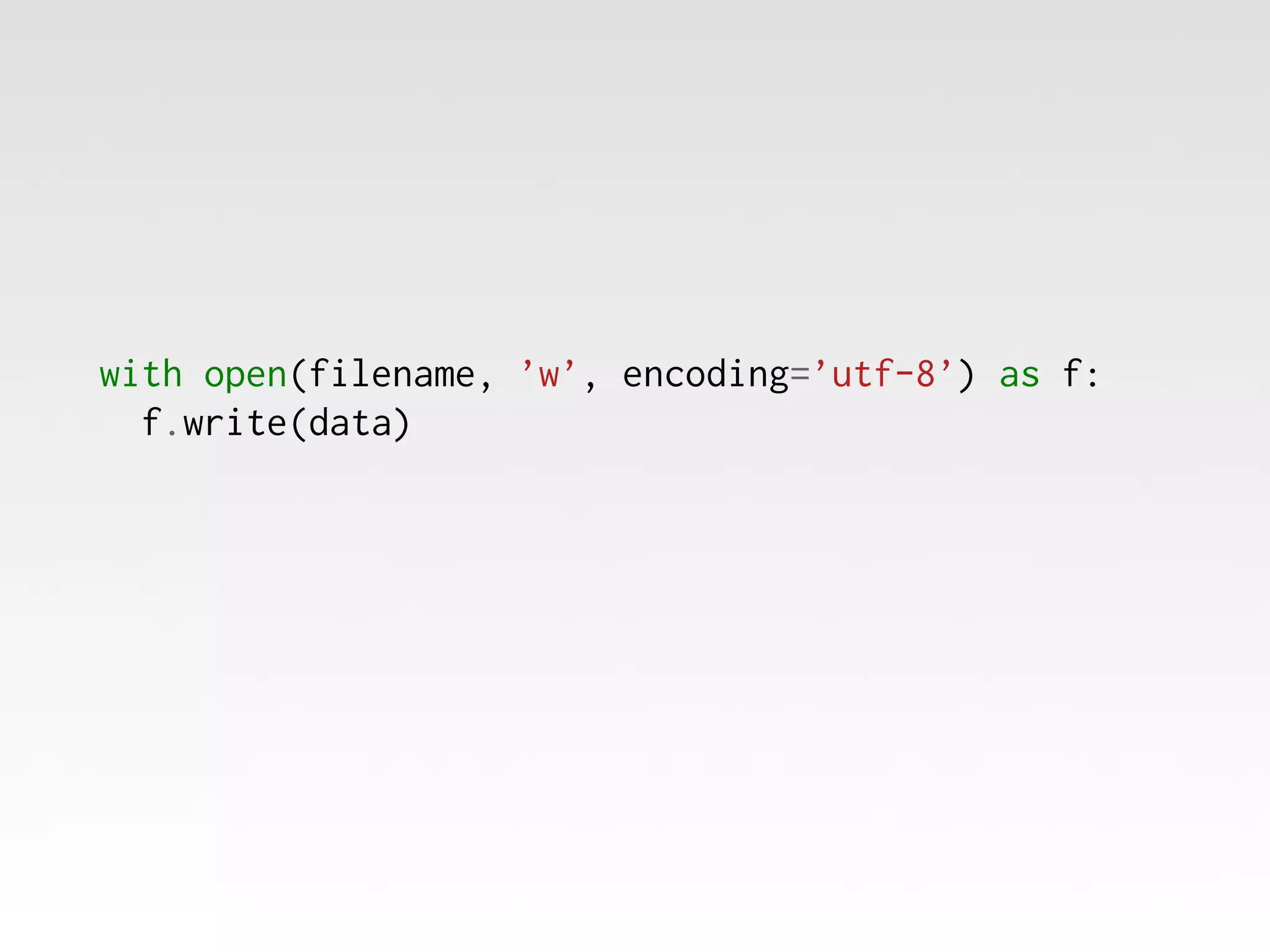
The document discusses file input/output (I/O) operations in programming, particularly in Python. It covers various aspects such as file opening modes, data abstraction, and character encoding while providing examples of reading and writing data to files. The document emphasizes the simplicity of file I/O while highlighting potential complexities like encoding issues.