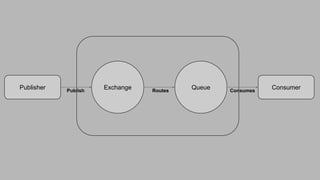
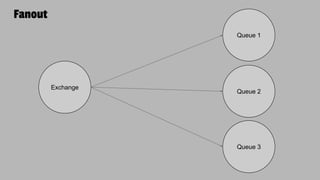
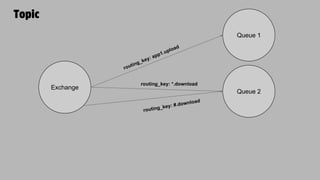
This document discusses AMQP (Advanced Message Queuing Protocol) and how it can be used with PHP. AMQP is a messaging broker protocol that is platform agnostic and runs on port 5672. It provides advantages like asynchronous messaging, load balancing, system integrations, and retry capabilities. The core AMQP components discussed are exchanges, message queues, bindings, channels, and virtual hosts. Code examples and references are provided to help understand how to implement AMQP messaging with PHP.