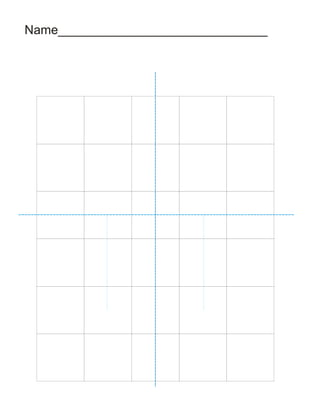
Face grid
•
0 likes•342 views
This is a worksheet which appeared in the Proportions of the Human Form presentation. I've uploaded this for easier download. It's a grid on which students practise drawing a face.
Report
Share
Report
Share
Download to read offline
Recommended
ITC hr policies

ITC Ltd. is an Indian conglomerate founded in 1910 as Imperial Tobacco Company. It has grown significantly over 100 years and now has a turnover of $6 billion annually. The document outlines ITC's human rights policies which uphold international standards and prohibit discrimination and human rights abuses. Key policies discussed include preventing discrimination in hiring and promotion, ensuring freedom of association for employees, prohibiting child labor and forced labor, and requiring consultation with employees on workplace changes. Compliance with the policies is monitored by HR and business unit heads.
Fs3610481053

International Journal of Engineering Research and Applications (IJERA) is an open access online peer reviewed international journal that publishes research and review articles in the fields of Computer Science, Neural Networks, Electrical Engineering, Software Engineering, Information Technology, Mechanical Engineering, Chemical Engineering, Plastic Engineering, Food Technology, Textile Engineering, Nano Technology & science, Power Electronics, Electronics & Communication Engineering, Computational mathematics, Image processing, Civil Engineering, Structural Engineering, Environmental Engineering, VLSI Testing & Low Power VLSI Design etc.
Flatstanley2

Tatajuba Oasis Flecheiras is a proposed 120 hectare luxury eco-resort development located behind Flecheiras and Guajiru beaches in Brazil. It aims to provide guests with the best of both worlds, allowing them to enjoy a luxurious hideaway experience while also being immersed in nature. The development will include four styles of accommodations - rustic, neo-colonial, modern-chic, and contemporary - all designed authentically, luxuriously, and sustainably.
Hagamos papel reciclado 

Este documento proporciona instrucciones detalladas para realizar una actividad de papel reciclado en el aula. La actividad se divide en dos sesiones de 1 hora cada una y requiere materiales como papel de desecho, una licuadora, agua y una prensa casera. El objetivo es enseñar a los estudiantes a reutilizar el papel y cuidar el medio ambiente mientras se divierten con un proceso creativo.
Ana benitez powerpoint

La seguridad informática se refiere a proteger la confidencialidad, integridad y disponibilidad de sistemas informáticos. Esto implica proteger el hardware, software y datos de amenazas como virus, malware y ataques cibernéticos mediante medidas como contraseñas, firewalls, copias de seguridad y actualizaciones de software.
Globalization And Customer Expectations

Globalization has increased economic integration and interconnectedness between countries through increased trade, foreign investment, and spread of technology. This has lowered trade barriers through agreements like GATT and WTO and increased flows of goods, capital, labor, and ideas globally. However, it has also increased cultural diffusion and competition. Customers now expect consistent high quality service, clear communication, options, consulting, and a seamless relationship from companies as competition has increased in the globalized marketplace. Building customer loyalty through meeting these expectations is key to business success.
Bond cars 2

James Bond is known for driving cars with extraordinary and dangerous gadgets. His Aston Martin DB5 featured hidden machine guns and smoke screens as well as an ejector seat and changing license plates. His Lotus Esprit submarine could launch missiles, torpedoes, and mines while his Aston Martin V8 had rocket launchers, spiked tires, and could even fly briefly with a rocket motor, and it too had a self-destruct function.
Residencial jessé cavalcanti

Este documento presenta el plano de un residencial que incluye dos salas, tres cuartos, dos baños, un patio de juegos, una piscina y detalles sobre el tamaño de las plantas. La dirección es Rua General Gustavo Cordeiro de Farias N° 96 en Ribeira, Brasil.
Recommended
ITC hr policies

ITC Ltd. is an Indian conglomerate founded in 1910 as Imperial Tobacco Company. It has grown significantly over 100 years and now has a turnover of $6 billion annually. The document outlines ITC's human rights policies which uphold international standards and prohibit discrimination and human rights abuses. Key policies discussed include preventing discrimination in hiring and promotion, ensuring freedom of association for employees, prohibiting child labor and forced labor, and requiring consultation with employees on workplace changes. Compliance with the policies is monitored by HR and business unit heads.
Fs3610481053

International Journal of Engineering Research and Applications (IJERA) is an open access online peer reviewed international journal that publishes research and review articles in the fields of Computer Science, Neural Networks, Electrical Engineering, Software Engineering, Information Technology, Mechanical Engineering, Chemical Engineering, Plastic Engineering, Food Technology, Textile Engineering, Nano Technology & science, Power Electronics, Electronics & Communication Engineering, Computational mathematics, Image processing, Civil Engineering, Structural Engineering, Environmental Engineering, VLSI Testing & Low Power VLSI Design etc.
Flatstanley2

Tatajuba Oasis Flecheiras is a proposed 120 hectare luxury eco-resort development located behind Flecheiras and Guajiru beaches in Brazil. It aims to provide guests with the best of both worlds, allowing them to enjoy a luxurious hideaway experience while also being immersed in nature. The development will include four styles of accommodations - rustic, neo-colonial, modern-chic, and contemporary - all designed authentically, luxuriously, and sustainably.
Hagamos papel reciclado 

Este documento proporciona instrucciones detalladas para realizar una actividad de papel reciclado en el aula. La actividad se divide en dos sesiones de 1 hora cada una y requiere materiales como papel de desecho, una licuadora, agua y una prensa casera. El objetivo es enseñar a los estudiantes a reutilizar el papel y cuidar el medio ambiente mientras se divierten con un proceso creativo.
Ana benitez powerpoint

La seguridad informática se refiere a proteger la confidencialidad, integridad y disponibilidad de sistemas informáticos. Esto implica proteger el hardware, software y datos de amenazas como virus, malware y ataques cibernéticos mediante medidas como contraseñas, firewalls, copias de seguridad y actualizaciones de software.
Globalization And Customer Expectations

Globalization has increased economic integration and interconnectedness between countries through increased trade, foreign investment, and spread of technology. This has lowered trade barriers through agreements like GATT and WTO and increased flows of goods, capital, labor, and ideas globally. However, it has also increased cultural diffusion and competition. Customers now expect consistent high quality service, clear communication, options, consulting, and a seamless relationship from companies as competition has increased in the globalized marketplace. Building customer loyalty through meeting these expectations is key to business success.
Bond cars 2

James Bond is known for driving cars with extraordinary and dangerous gadgets. His Aston Martin DB5 featured hidden machine guns and smoke screens as well as an ejector seat and changing license plates. His Lotus Esprit submarine could launch missiles, torpedoes, and mines while his Aston Martin V8 had rocket launchers, spiked tires, and could even fly briefly with a rocket motor, and it too had a self-destruct function.
Residencial jessé cavalcanti

Este documento presenta el plano de un residencial que incluye dos salas, tres cuartos, dos baños, un patio de juegos, una piscina y detalles sobre el tamaño de las plantas. La dirección es Rua General Gustavo Cordeiro de Farias N° 96 en Ribeira, Brasil.
Network security

This document discusses network security and firewalls. It explains that network security aims to create a secure computing platform and protect systems from hackers through devices like firewalls. Firewalls examine incoming and outgoing messages on a network and block those that do not meet security criteria. They can filter network traffic using packet filtering, proxy services, or stateful inspection. Firewalls are customizable and can filter based on IP addresses, domains, protocols, and other conditions to control network access and traffic flow.
Resumen del tema se seguridad

Este documento describe las diferentes formas de proteger los equipos electrónicos, incluyendo hardware, software y datos, de amenazas como malware, hackers y virus. Explica que hay que usar contraseñas, mantener los sistemas actualizados y controlar los permisos de acceso, y que existen diferentes tipos de antivirus y programas de seguridad para proteger los ordenadores. También recomienda realizar copias de seguridad periódicas de los archivos importantes.
Nacionalismo en un Mundo Descentrado

El documento discute cómo la globalización ha descentrado la construcción social de la subjetividad y el sujeto, que ya no se refiere principalmente a los estados nacionales. Esto marca un cambio fundamental respecto de la modernidad, donde los estados nacionales eran la instancia central de producción de subjetividad. Ahora, debido a las tecnologías de la información y la cosmopolitización, la subjetividad puede referirse a casi cualquier lugar o tiempo. Por lo tanto, los estados nacionales deben resignificar su papel y no oponerse
Cine

The document discusses going to see a movie. It mentions that John and Sally decided to see the new action film playing at the local cinema. They arrived at 7pm to get good seats for the 8pm showing. After the movie ended around 10pm, they discussed how much they enjoyed it over a late dinner.
Il Decalogo della Comunicazione Low Cost

CRAP Adv presenta il Manifesto. Le 10 Regole d'oro della Comunicazione Pubblicitaria Low Cost.
Persuasiveadverts

Advertisers use packaging to influence consumer choices and purchases. They design packaging to attract attention and highlight product benefits. Manufacturers also consider recyclability when developing packaging to appeal to environmentally conscious customers. The document discusses how advertising and packaging aim to persuade consumers through promotional items, colorful graphics, and innovative product packaging designs.
Hunter s

Hunter is a very short document consisting of a single word. The document provides no context or details, containing only the word "Hunter".
Do you Wiki?

This document discusses blogs and wikis and their use in 21st century classrooms. It begins with an introduction to blogs and wikis, explaining that blogs allow for ownership, audience, and organization of information while wikis enable ownership and collaboration. Examples are then provided of how blogs and wikis have been used for classroom websites, journals, book clubs, and paperless assignments. The document concludes by providing examples of wikis created by classes and encouraging the creation of a new wiki to facilitate 21st century learning.
Cs416 08 09a

This document discusses virtual memory concepts including:
1. Paging and segmentation allow processes to have portions not currently in main memory by using page/segment tables and bringing pieces into memory on demand via interrupts.
2. Locality of reference and intelligent prepaging of nearby pages can improve efficiency by reducing interrupt overhead from paging.
3. Hardware and OS software support is needed for virtual memory through memory management units, page/segment tables, and algorithms for fetch, placement, and replacement policies.
4. Common policies discussed include demand paging, first/next fit placement, and LRU, clock, and optimal page replacement.
3 presentación virus grupo mmc

Este documento resume diferentes tipos de amenazas cibernéticas como PC Zombi, Spam, Ramsomware, Phishing y Scam. Explica brevemente qué son, cómo funcionan y ofrece consejos para protegerse de ellas como mantener actualizado el antivirus, no visitar páginas desconocidas y desconfiar de comportamientos extraños.
Etiquetas en Html

Este documento explica las etiquetas básicas en HTML. Describe que los archivos HTML contienen etiquetas y texto, y que las etiquetas indican la estructura y formato del documento. Explica etiquetas comunes como <HTML>, <HEAD>, <BODY>, <B>, <I>, <H1-H6> y <HR> y cómo estas afectan la presentación del texto y la estructura de la página. También menciona que el formato del archivo no afecta el resultado mostrado por el navegador.
Athena

Athena was the Greek goddess of wisdom, handicraft, and strategic warfare. She was one of the most important and widely worshipped deities in the pantheon. As the patron goddess of Athens, Athena helped inspire the city's early development and was an important figure in Greek mythology.
Performance vision Version 3.0 - What's New

This document describes the new features and improvements in Performance Vision version 3.0. Key additions include in-depth database transaction analysis for Oracle, SQL Server, MySQL and PostgreSQL; multi-node packet capture for distributed environments; and links between network flows and database transactions for root cause analysis. The update also includes performance optimizations, additional metrics and views, improved interface design, and support for new protocols. System impacts are expected to be minimal with a low database migration time and no major changes to existing metrics.
Investigación 3 pc zombie

PC Zombie se refiere a ordenadores infectados por malware que pueden ser controlados por terceros sin el conocimiento del usuario. Spim es un simulador de lenguaje ensamblador MIPS disponible para Windows, Mac y Linux. Ramsomware es un malware que cifra archivos y pide un rescate para descifrarlos. Spam son mensajes no solicitados enviados masivamente que perjudican al receptor. Phishing intenta robar información confidencial haciéndose pasar por una empresa legítima. Scam son estafas a través de correos electrónicos fraudulentos que pret
Trabajo de investigacion zulmi Perez y Carlos Salguero

Este documento resume diferentes tipos de amenazas cibernéticas como PC Zombie, SPIM, ransomware, spam, phishing y scam. Describe sus características, cómo funcionan, formas de prevención y tecnologías de detección. En particular, explica que un PC Zombie es un ordenador infectado y controlado remotamente sin el conocimiento del usuario, mientras que el spam, phishing y scam usan técnicas de ingeniería social para robar información confidencial o dinero. El documento también proporciona consejos sobre software y medidas de seguridad para proteger
AJAX

AJAX is a technique for creating faster and more interactive web applications by exchanging small amounts of data with the server asynchronously in the background without interfering with the display and behavior of the existing page. It allows for updating parts of a web page rather than reloading the entire page by making use of a combination of technologies including JavaScript, XML, and HTML and HTTP requests. Some common applications that use AJAX include Google Maps, Facebook Chat, and Flickr.
We are the champions picture story

Lesson explanation, post-lesson reflection, etc: http://dogmediaries.wordpress.com/2013/08/02/we-are-the-champions-using-songs-in-the-classroom
We are the champions lesson plan

Lesson explanation, post-lesson reflection, etc: http://dogmediaries.wordpress.com/2013/08/02/we-are-the-champions-using-songs-in-the-classroom
Handout 1 guided discovery of passives

The document provides examples of active and passive voice sentences and exercises for converting between the two. It begins by filling in blanks to complete sentences in both active and passive voice. It then provides rules for forming passive voice, including that the subject of an active sentence becomes the object of a passive sentence. Examples are given of converting between active and passive voice, including changing the focus from the actor to the action.
Example of a CELTA lesson plan

This is an example of a lesson plan done during a CELTA course. For my reflections on the course, visit: http://celtaconfessions.wordpress.com/
Example of a CELTA stage plan

This is an example of a simple stage plan done during a CELTA course. For my reflections on the course, visit: http://celtaconfessions.wordpress.com/
Wordle: Your imagination's the limit!

Different ways of using Wordle in the classroom. Make it even more visual than it already is!
Go here to see how these have been done: http://aclil2climb.blogspot.com/2011/12/two-for-price-of-none.html
More Related Content
Viewers also liked
Network security

This document discusses network security and firewalls. It explains that network security aims to create a secure computing platform and protect systems from hackers through devices like firewalls. Firewalls examine incoming and outgoing messages on a network and block those that do not meet security criteria. They can filter network traffic using packet filtering, proxy services, or stateful inspection. Firewalls are customizable and can filter based on IP addresses, domains, protocols, and other conditions to control network access and traffic flow.
Resumen del tema se seguridad

Este documento describe las diferentes formas de proteger los equipos electrónicos, incluyendo hardware, software y datos, de amenazas como malware, hackers y virus. Explica que hay que usar contraseñas, mantener los sistemas actualizados y controlar los permisos de acceso, y que existen diferentes tipos de antivirus y programas de seguridad para proteger los ordenadores. También recomienda realizar copias de seguridad periódicas de los archivos importantes.
Nacionalismo en un Mundo Descentrado

El documento discute cómo la globalización ha descentrado la construcción social de la subjetividad y el sujeto, que ya no se refiere principalmente a los estados nacionales. Esto marca un cambio fundamental respecto de la modernidad, donde los estados nacionales eran la instancia central de producción de subjetividad. Ahora, debido a las tecnologías de la información y la cosmopolitización, la subjetividad puede referirse a casi cualquier lugar o tiempo. Por lo tanto, los estados nacionales deben resignificar su papel y no oponerse
Cine

The document discusses going to see a movie. It mentions that John and Sally decided to see the new action film playing at the local cinema. They arrived at 7pm to get good seats for the 8pm showing. After the movie ended around 10pm, they discussed how much they enjoyed it over a late dinner.
Il Decalogo della Comunicazione Low Cost

CRAP Adv presenta il Manifesto. Le 10 Regole d'oro della Comunicazione Pubblicitaria Low Cost.
Persuasiveadverts

Advertisers use packaging to influence consumer choices and purchases. They design packaging to attract attention and highlight product benefits. Manufacturers also consider recyclability when developing packaging to appeal to environmentally conscious customers. The document discusses how advertising and packaging aim to persuade consumers through promotional items, colorful graphics, and innovative product packaging designs.
Hunter s

Hunter is a very short document consisting of a single word. The document provides no context or details, containing only the word "Hunter".
Do you Wiki?

This document discusses blogs and wikis and their use in 21st century classrooms. It begins with an introduction to blogs and wikis, explaining that blogs allow for ownership, audience, and organization of information while wikis enable ownership and collaboration. Examples are then provided of how blogs and wikis have been used for classroom websites, journals, book clubs, and paperless assignments. The document concludes by providing examples of wikis created by classes and encouraging the creation of a new wiki to facilitate 21st century learning.
Cs416 08 09a

This document discusses virtual memory concepts including:
1. Paging and segmentation allow processes to have portions not currently in main memory by using page/segment tables and bringing pieces into memory on demand via interrupts.
2. Locality of reference and intelligent prepaging of nearby pages can improve efficiency by reducing interrupt overhead from paging.
3. Hardware and OS software support is needed for virtual memory through memory management units, page/segment tables, and algorithms for fetch, placement, and replacement policies.
4. Common policies discussed include demand paging, first/next fit placement, and LRU, clock, and optimal page replacement.
3 presentación virus grupo mmc

Este documento resume diferentes tipos de amenazas cibernéticas como PC Zombi, Spam, Ramsomware, Phishing y Scam. Explica brevemente qué son, cómo funcionan y ofrece consejos para protegerse de ellas como mantener actualizado el antivirus, no visitar páginas desconocidas y desconfiar de comportamientos extraños.
Etiquetas en Html

Este documento explica las etiquetas básicas en HTML. Describe que los archivos HTML contienen etiquetas y texto, y que las etiquetas indican la estructura y formato del documento. Explica etiquetas comunes como <HTML>, <HEAD>, <BODY>, <B>, <I>, <H1-H6> y <HR> y cómo estas afectan la presentación del texto y la estructura de la página. También menciona que el formato del archivo no afecta el resultado mostrado por el navegador.
Athena

Athena was the Greek goddess of wisdom, handicraft, and strategic warfare. She was one of the most important and widely worshipped deities in the pantheon. As the patron goddess of Athens, Athena helped inspire the city's early development and was an important figure in Greek mythology.
Performance vision Version 3.0 - What's New

This document describes the new features and improvements in Performance Vision version 3.0. Key additions include in-depth database transaction analysis for Oracle, SQL Server, MySQL and PostgreSQL; multi-node packet capture for distributed environments; and links between network flows and database transactions for root cause analysis. The update also includes performance optimizations, additional metrics and views, improved interface design, and support for new protocols. System impacts are expected to be minimal with a low database migration time and no major changes to existing metrics.
Investigación 3 pc zombie

PC Zombie se refiere a ordenadores infectados por malware que pueden ser controlados por terceros sin el conocimiento del usuario. Spim es un simulador de lenguaje ensamblador MIPS disponible para Windows, Mac y Linux. Ramsomware es un malware que cifra archivos y pide un rescate para descifrarlos. Spam son mensajes no solicitados enviados masivamente que perjudican al receptor. Phishing intenta robar información confidencial haciéndose pasar por una empresa legítima. Scam son estafas a través de correos electrónicos fraudulentos que pret
Trabajo de investigacion zulmi Perez y Carlos Salguero

Este documento resume diferentes tipos de amenazas cibernéticas como PC Zombie, SPIM, ransomware, spam, phishing y scam. Describe sus características, cómo funcionan, formas de prevención y tecnologías de detección. En particular, explica que un PC Zombie es un ordenador infectado y controlado remotamente sin el conocimiento del usuario, mientras que el spam, phishing y scam usan técnicas de ingeniería social para robar información confidencial o dinero. El documento también proporciona consejos sobre software y medidas de seguridad para proteger
AJAX

AJAX is a technique for creating faster and more interactive web applications by exchanging small amounts of data with the server asynchronously in the background without interfering with the display and behavior of the existing page. It allows for updating parts of a web page rather than reloading the entire page by making use of a combination of technologies including JavaScript, XML, and HTML and HTTP requests. Some common applications that use AJAX include Google Maps, Facebook Chat, and Flickr.
Viewers also liked (16)
Trabajo de investigacion zulmi Perez y Carlos Salguero

Trabajo de investigacion zulmi Perez y Carlos Salguero
More from Chiew Pang
We are the champions picture story

Lesson explanation, post-lesson reflection, etc: http://dogmediaries.wordpress.com/2013/08/02/we-are-the-champions-using-songs-in-the-classroom
We are the champions lesson plan

Lesson explanation, post-lesson reflection, etc: http://dogmediaries.wordpress.com/2013/08/02/we-are-the-champions-using-songs-in-the-classroom
Handout 1 guided discovery of passives

The document provides examples of active and passive voice sentences and exercises for converting between the two. It begins by filling in blanks to complete sentences in both active and passive voice. It then provides rules for forming passive voice, including that the subject of an active sentence becomes the object of a passive sentence. Examples are given of converting between active and passive voice, including changing the focus from the actor to the action.
Example of a CELTA lesson plan

This is an example of a lesson plan done during a CELTA course. For my reflections on the course, visit: http://celtaconfessions.wordpress.com/
Example of a CELTA stage plan

This is an example of a simple stage plan done during a CELTA course. For my reflections on the course, visit: http://celtaconfessions.wordpress.com/
Wordle: Your imagination's the limit!

Different ways of using Wordle in the classroom. Make it even more visual than it already is!
Go here to see how these have been done: http://aclil2climb.blogspot.com/2011/12/two-for-price-of-none.html
Presentation1Bridging the Gap Between Digital Natives and Immigrants/Foreigners

This document discusses bridging the gap between digital natives and digital immigrants/foreigners in education. It notes that students are being prepared for jobs that don't yet exist using technologies that haven't been invented to solve problems we can't yet foresee. It suggests incorporating more technology like blogs, videos and games into education to better engage digital native students and prepare them for an increasingly digital future. A variety of free and easy to use digital tools are presented that teachers can use to incorporate more technology into their lessons.
Basic Art Material

Because of the animations used in this presentation, it will have to be downloaded for the presentation to make any sense. I've had cases of people giving me one-star for presentations because they can't make head or tail out of them. Well, if they can't read...
http://aclil2climb.blogspot.com
How To Draw Cartoon Characters - Basic Instructions

The document provides instructions for drawing cartoon characters in 4 steps: 1) Draw a stick figure, 2) Add ovals over the lines, 3) Draw in hair, hands, and shoes, and 4) Dress the character. It also suggests drawing a running stick figure for action and doodling to create imaginary characters. The creative commons license allows sharing and adapting for non-commercial purposes with attribution.
How to draw cartoon characters - Basic Instructions

The document provides instructions for drawing cartoon characters in 4 steps: 1) Draw a stick figure, 2) Add ovals over the lines, 3) Draw in hair, hands, and shoes, and 4) Dress the character. It also suggests drawing a running stick figure for action and doodling to create imaginary characters. The creative commons license allows sharing and adapting for non-commercial purposes with attribution.
Textures and Patterns (updated)

This document provides information about textures and patterns, including definitions and examples. It discusses natural versus artificial textures visually and by touch. Artists and designers use textures and patterns to engage audiences without changing colors. The document also provides instructions for making a small book of textures, including collecting texture samples, transferring textures to paper, and assembling pages. An example book from a student shows various materials used for textures.
Proportions of the human form

http://aclil2climb.blogspot.com/2010/04/art-proportions-of-human-form-how-to.html
Presentation on human proportions.
Tutorial on how to draw a face.
Worksheets.
To fully appreciate the contents, especially the tutorial, in this presentation, it has to be downloaded and viewed as such.
Cooking Verbs Word search KEY

The document is a word search puzzle containing 20 hidden words related to cooking. The words are placed horizontally, vertically, or diagonally forwards or backwards in the grid. The player's task is to locate each word in the puzzle and circle it. A list of the 20 hidden words is provided at the bottom.
ICT Word Search (Key)

This word search puzzle contains 20 technology-related words hidden horizontally, vertically, or diagonally. The document provides a grid of letters and lists the hidden words at the bottom. The goal is to locate the words in the grid and circle them.
ICT Word Search

This word search puzzle contains 20 technology-related words hidden horizontally, vertically, or diagonally. The document provides the word search grid and the list of hidden words. The goal is to locate each word in the puzzle by circling it.
ICT Crossword (Key)

This document contains a crossword puzzle with clues related to computer terms. The crossword grid has 18 numbered squares to fill in with correct words from across and down clues. The clues define terms such as software, encryption, virus, bandwidth, startup, megabyte, backup, byte, default, bit, pixel, cookie, and resolution.
ICT Crossword

This document contains a crossword puzzle with clues related to computer terms. The crossword grid has 18 numbered squares to fill in with correct words from across and down clues. The clues define terms such as software, encryption, virus, bandwidth, reboot, megabyte, backup, byte, default, bit, pixel, cookie, and resolution.
Jobs Word Search (Keys)

This document provides instructions for a word search puzzle. It contains a grid of letters with 33 hidden words from different occupations listed at the bottom that are hidden horizontally, vertically, or diagonally in the grid. The goal is to locate each word in the grid and circle it.
Jobs Crossword (Key)

This crossword puzzle contains clues for occupations. It provides definitions for 32 different jobs across various industries like law enforcement, healthcare, transportation, construction, entertainment, science, and more. Solvers are tasked with using the clue definitions to correctly fill in the corresponding job titles in the crossword grid.
Jobs Crossword

This crossword puzzle contains clues for occupations. It provides definitions for 32 different jobs across various industries like law enforcement, healthcare, transportation, construction, entertainment, science, and more. Solvers are tasked with using the clue definitions to correctly fill in the corresponding job titles in the crossword grid.
More from Chiew Pang (20)
Presentation1Bridging the Gap Between Digital Natives and Immigrants/Foreigners

Presentation1Bridging the Gap Between Digital Natives and Immigrants/Foreigners
How To Draw Cartoon Characters - Basic Instructions

How To Draw Cartoon Characters - Basic Instructions
How to draw cartoon characters - Basic Instructions

How to draw cartoon characters - Basic Instructions
Recently uploaded
Advanced Java[Extra Concepts, Not Difficult].docx![Advanced Java[Extra Concepts, Not Difficult].docx](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Advanced Java[Extra Concepts, Not Difficult].docx](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
This is part 2 of my Java Learning Journey. This contains Hashing, ArrayList, LinkedList, Date and Time Classes, Calendar Class and more.
Philippine Edukasyong Pantahanan at Pangkabuhayan (EPP) Curriculum

(𝐓𝐋𝐄 𝟏𝟎𝟎) (𝐋𝐞𝐬𝐬𝐨𝐧 𝟏)-𝐏𝐫𝐞𝐥𝐢𝐦𝐬
𝐃𝐢𝐬𝐜𝐮𝐬𝐬 𝐭𝐡𝐞 𝐄𝐏𝐏 𝐂𝐮𝐫𝐫𝐢𝐜𝐮𝐥𝐮𝐦 𝐢𝐧 𝐭𝐡𝐞 𝐏𝐡𝐢𝐥𝐢𝐩𝐩𝐢𝐧𝐞𝐬:
- Understand the goals and objectives of the Edukasyong Pantahanan at Pangkabuhayan (EPP) curriculum, recognizing its importance in fostering practical life skills and values among students. Students will also be able to identify the key components and subjects covered, such as agriculture, home economics, industrial arts, and information and communication technology.
𝐄𝐱𝐩𝐥𝐚𝐢𝐧 𝐭𝐡𝐞 𝐍𝐚𝐭𝐮𝐫𝐞 𝐚𝐧𝐝 𝐒𝐜𝐨𝐩𝐞 𝐨𝐟 𝐚𝐧 𝐄𝐧𝐭𝐫𝐞𝐩𝐫𝐞𝐧𝐞𝐮𝐫:
-Define entrepreneurship, distinguishing it from general business activities by emphasizing its focus on innovation, risk-taking, and value creation. Students will describe the characteristics and traits of successful entrepreneurs, including their roles and responsibilities, and discuss the broader economic and social impacts of entrepreneurial activities on both local and global scales.
Beyond Degrees - Empowering the Workforce in the Context of Skills-First.pptx

Iván Bornacelly, Policy Analyst at the OECD Centre for Skills, OECD, presents at the webinar 'Tackling job market gaps with a skills-first approach' on 12 June 2024
Mule event processing models | MuleSoft Mysore Meetup #47

Mule event processing models | MuleSoft Mysore Meetup #47
Event Link:- https://meetups.mulesoft.com/events/details/mulesoft-mysore-presents-mule-event-processing-models/
Agenda
● What is event processing in MuleSoft?
● Types of event processing models in Mule 4
● Distinction between the reactive, parallel, blocking & non-blocking processing
For Upcoming Meetups Join Mysore Meetup Group - https://meetups.mulesoft.com/mysore/YouTube:- youtube.com/@mulesoftmysore
Mysore WhatsApp group:- https://chat.whatsapp.com/EhqtHtCC75vCAX7gaO842N
Speaker:-
Shivani Yasaswi - https://www.linkedin.com/in/shivaniyasaswi/
Organizers:-
Shubham Chaurasia - https://www.linkedin.com/in/shubhamchaurasia1/
Giridhar Meka - https://www.linkedin.com/in/giridharmeka
Priya Shaw - https://www.linkedin.com/in/priya-shaw
ANATOMY AND BIOMECHANICS OF HIP JOINT.pdf

it describes the bony anatomy including the femoral head , acetabulum, labrum . also discusses the capsule , ligaments . muscle that act on the hip joint and the range of motion are outlined. factors affecting hip joint stability and weight transmission through the joint are summarized.
How to Make a Field Mandatory in Odoo 17

In Odoo, making a field required can be done through both Python code and XML views. When you set the required attribute to True in Python code, it makes the field required across all views where it's used. Conversely, when you set the required attribute in XML views, it makes the field required only in the context of that particular view.
Gender and Mental Health - Counselling and Family Therapy Applications and In...

A proprietary approach developed by bringing together the best of learning theories from Psychology, design principles from the world of visualization, and pedagogical methods from over a decade of training experience, that enables you to: Learn better, faster!
বাংলাদেশ অর্থনৈতিক সমীক্ষা (Economic Review) ২০২৪ UJS App.pdf

বাংলাদেশের অর্থনৈতিক সমীক্ষা ২০২৪ [Bangladesh Economic Review 2024 Bangla.pdf] কম্পিউটার , ট্যাব ও স্মার্ট ফোন ভার্সন সহ সম্পূর্ণ বাংলা ই-বুক বা pdf বই " সুচিপত্র ...বুকমার্ক মেনু 🔖 ও হাইপার লিংক মেনু 📝👆 যুক্ত ..
আমাদের সবার জন্য খুব খুব গুরুত্বপূর্ণ একটি বই ..বিসিএস, ব্যাংক, ইউনিভার্সিটি ভর্তি ও যে কোন প্রতিযোগিতা মূলক পরীক্ষার জন্য এর খুব ইম্পরট্যান্ট একটি বিষয় ...তাছাড়া বাংলাদেশের সাম্প্রতিক যে কোন ডাটা বা তথ্য এই বইতে পাবেন ...
তাই একজন নাগরিক হিসাবে এই তথ্য গুলো আপনার জানা প্রয়োজন ...।
বিসিএস ও ব্যাংক এর লিখিত পরীক্ষা ...+এছাড়া মাধ্যমিক ও উচ্চমাধ্যমিকের স্টুডেন্টদের জন্য অনেক কাজে আসবে ...
BÀI TẬP DẠY THÊM TIẾNG ANH LỚP 7 CẢ NĂM FRIENDS PLUS SÁCH CHÂN TRỜI SÁNG TẠO ...

BÀI TẬP DẠY THÊM TIẾNG ANH LỚP 7 CẢ NĂM FRIENDS PLUS SÁCH CHÂN TRỜI SÁNG TẠO ...Nguyen Thanh Tu Collection
https://app.box.com/s/qhtvq32h4ybf9t49ku85x0n3xl4jhr15Leveraging Generative AI to Drive Nonprofit Innovation

In this webinar, participants learned how to utilize Generative AI to streamline operations and elevate member engagement. Amazon Web Service experts provided a customer specific use cases and dived into low/no-code tools that are quick and easy to deploy through Amazon Web Service (AWS.)
Traditional Musical Instruments of Arunachal Pradesh and Uttar Pradesh - RAYH...

Traditional Musical Instruments of Arunachal Pradesh and Uttar Pradesh
Main Java[All of the Base Concepts}.docx

This is part 1 of my Java Learning Journey. This Contains Custom methods, classes, constructors, packages, multithreading , try- catch block, finally block and more.
Walmart Business+ and Spark Good for Nonprofits.pdf

"Learn about all the ways Walmart supports nonprofit organizations.
You will hear from Liz Willett, the Head of Nonprofits, and hear about what Walmart is doing to help nonprofits, including Walmart Business and Spark Good. Walmart Business+ is a new offer for nonprofits that offers discounts and also streamlines nonprofits order and expense tracking, saving time and money.
The webinar may also give some examples on how nonprofits can best leverage Walmart Business+.
The event will cover the following::
Walmart Business + (https://business.walmart.com/plus) is a new shopping experience for nonprofits, schools, and local business customers that connects an exclusive online shopping experience to stores. Benefits include free delivery and shipping, a 'Spend Analytics” feature, special discounts, deals and tax-exempt shopping.
Special TechSoup offer for a free 180 days membership, and up to $150 in discounts on eligible orders.
Spark Good (walmart.com/sparkgood) is a charitable platform that enables nonprofits to receive donations directly from customers and associates.
Answers about how you can do more with Walmart!"
Recently uploaded (20)
Philippine Edukasyong Pantahanan at Pangkabuhayan (EPP) Curriculum

Philippine Edukasyong Pantahanan at Pangkabuhayan (EPP) Curriculum
Beyond Degrees - Empowering the Workforce in the Context of Skills-First.pptx

Beyond Degrees - Empowering the Workforce in the Context of Skills-First.pptx
NEWSPAPERS - QUESTION 1 - REVISION POWERPOINT.pptx

NEWSPAPERS - QUESTION 1 - REVISION POWERPOINT.pptx
Mule event processing models | MuleSoft Mysore Meetup #47

Mule event processing models | MuleSoft Mysore Meetup #47
B. Ed Syllabus for babasaheb ambedkar education university.pdf

B. Ed Syllabus for babasaheb ambedkar education university.pdf
Gender and Mental Health - Counselling and Family Therapy Applications and In...

Gender and Mental Health - Counselling and Family Therapy Applications and In...
বাংলাদেশ অর্থনৈতিক সমীক্ষা (Economic Review) ২০২৪ UJS App.pdf

বাংলাদেশ অর্থনৈতিক সমীক্ষা (Economic Review) ২০২৪ UJS App.pdf
Film vocab for eal 3 students: Australia the movie

Film vocab for eal 3 students: Australia the movie
BÀI TẬP DẠY THÊM TIẾNG ANH LỚP 7 CẢ NĂM FRIENDS PLUS SÁCH CHÂN TRỜI SÁNG TẠO ...

BÀI TẬP DẠY THÊM TIẾNG ANH LỚP 7 CẢ NĂM FRIENDS PLUS SÁCH CHÂN TRỜI SÁNG TẠO ...
Leveraging Generative AI to Drive Nonprofit Innovation

Leveraging Generative AI to Drive Nonprofit Innovation
Traditional Musical Instruments of Arunachal Pradesh and Uttar Pradesh - RAYH...

Traditional Musical Instruments of Arunachal Pradesh and Uttar Pradesh - RAYH...
IGCSE Biology Chapter 14- Reproduction in Plants.pdf

IGCSE Biology Chapter 14- Reproduction in Plants.pdf
Walmart Business+ and Spark Good for Nonprofits.pdf

Walmart Business+ and Spark Good for Nonprofits.pdf
