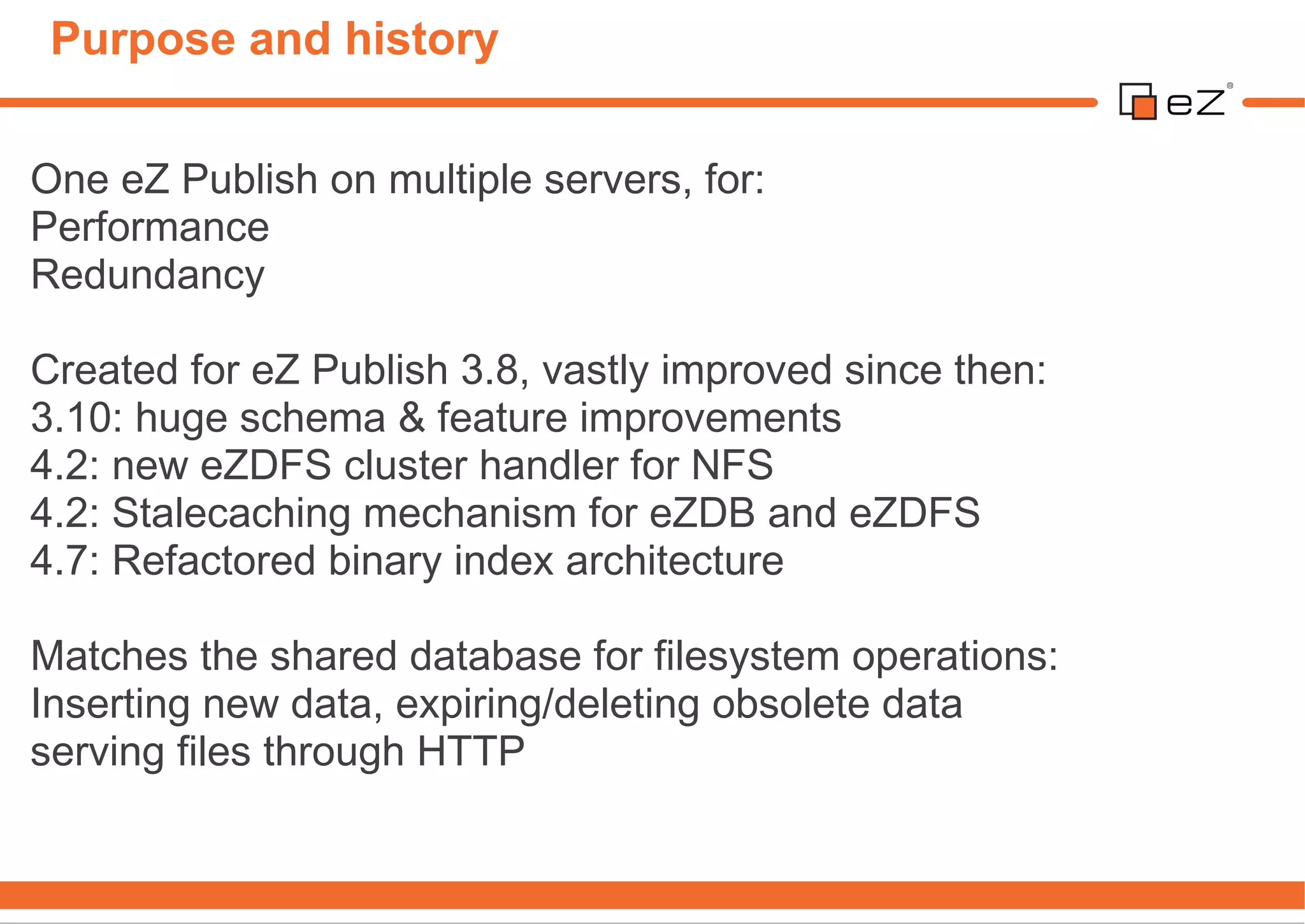
eZ Cluster allows running an eZ Publish installation on multiple servers for improved performance, redundancy, and scalability. It matches the database storage for metadata with either database or network file system storage for content files. The cluster handlers store metadata in the database and files either in the database or on an NFS server. Configuration involves setting the cluster handler, storing files on the database or NFS, moving existing files to the cluster, rewriting URLs, and indexing binary files. The cluster API provides methods for reading, writing, and caching files while handling concurrency and stale caching.
![Configuration #1: file.ini
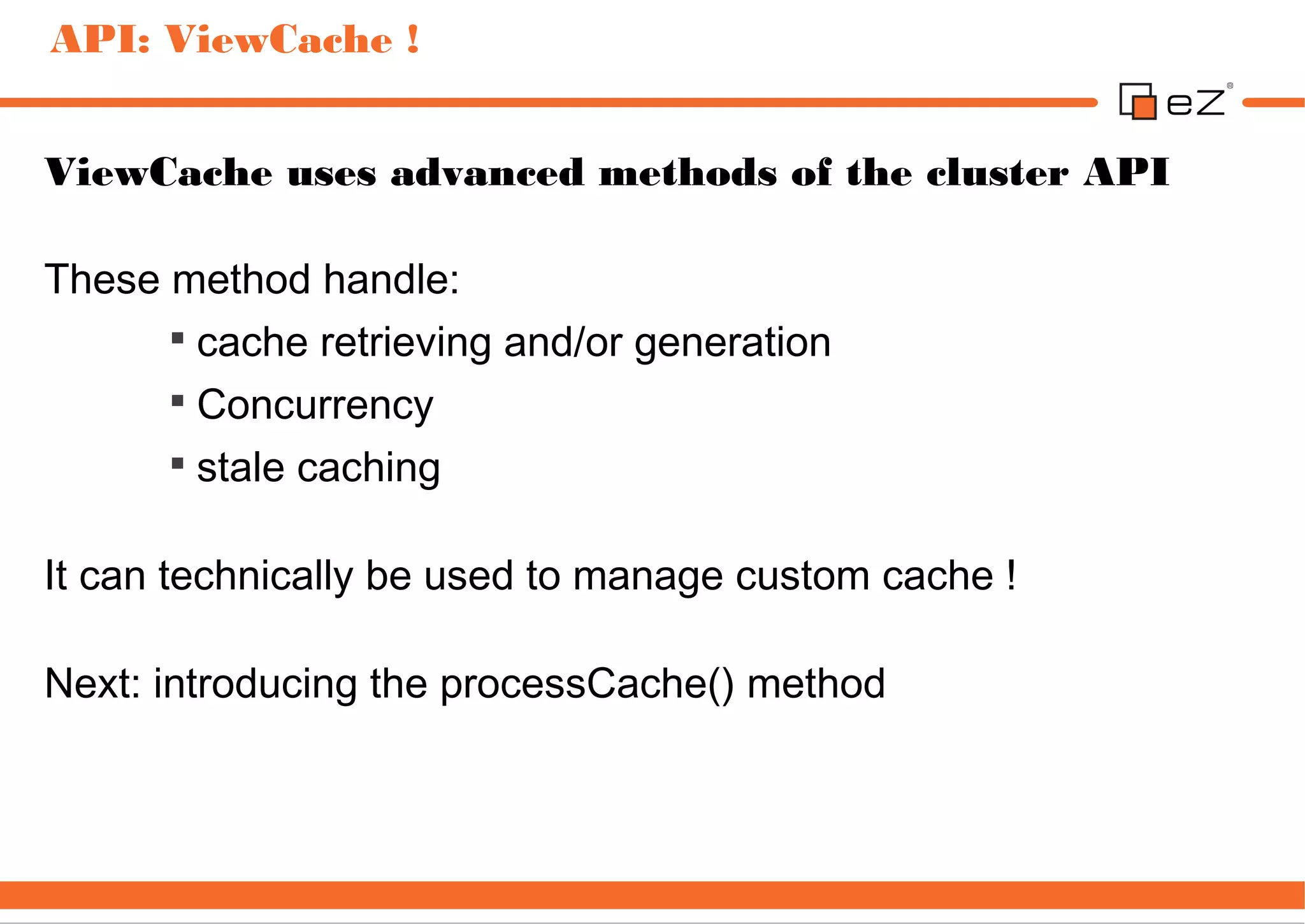
A cluster handler must be configured in a file.ini override:
1.[ClusteringSettings]
2.FileHandler=eZDFSFileHandler
1.# DFS Cluster Handler settings
2.[eZDFSClusteringSettings]
3.MountPointPath=var/nfs
4.DBBackend=eZDFSFileHandlerMySQLBackend
5.DBHost=localhost
6.DBName=labs_ezpublish_trunk_cluster
7.DBUser=root
8.DBPassword=root](https://image.slidesharecdn.com/ezsc2012-clustering-techniques-2-120911024904-phpapp02/75/eZ-Publish-cluster-unleashed-revisited-6-2048.jpg)
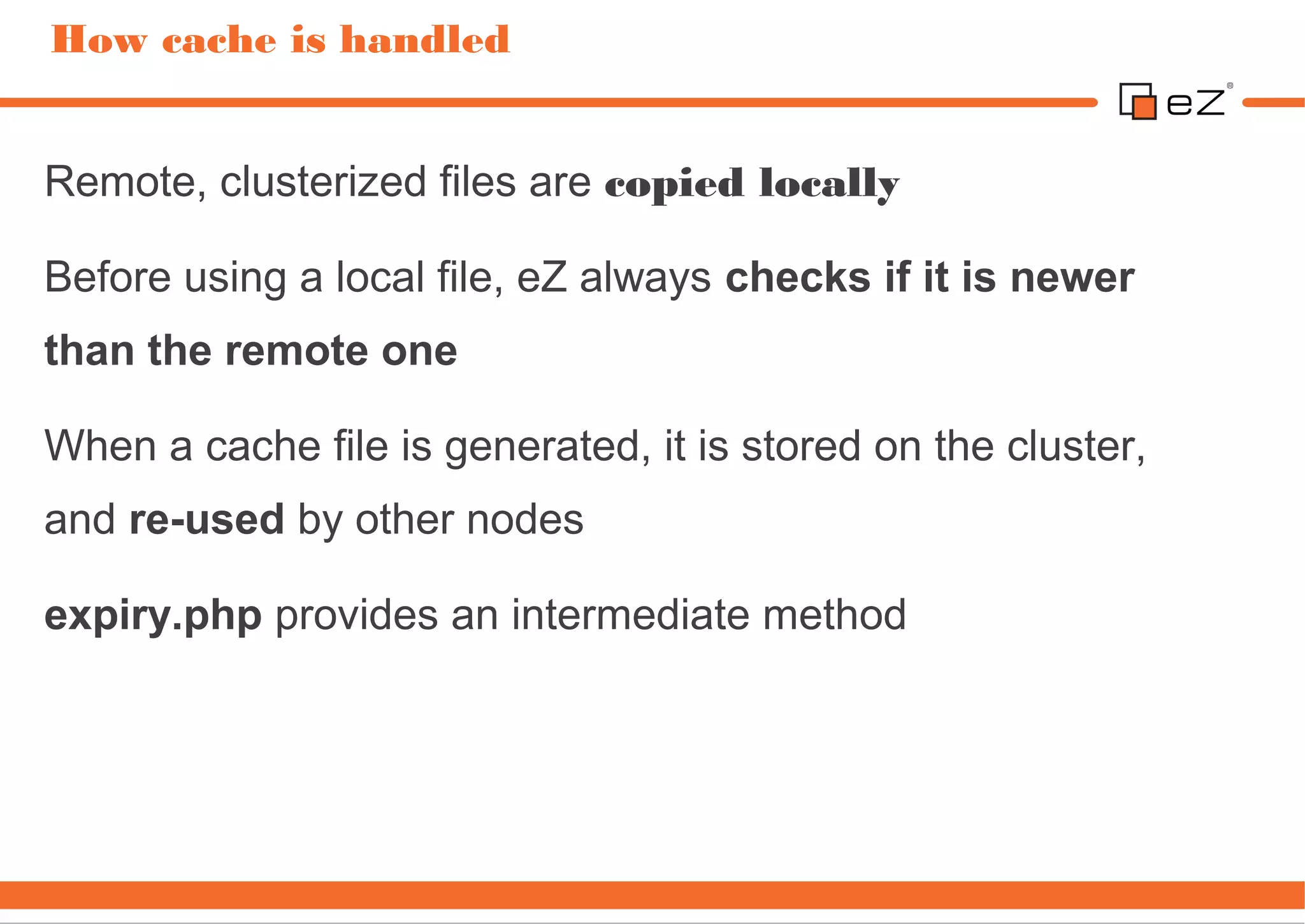
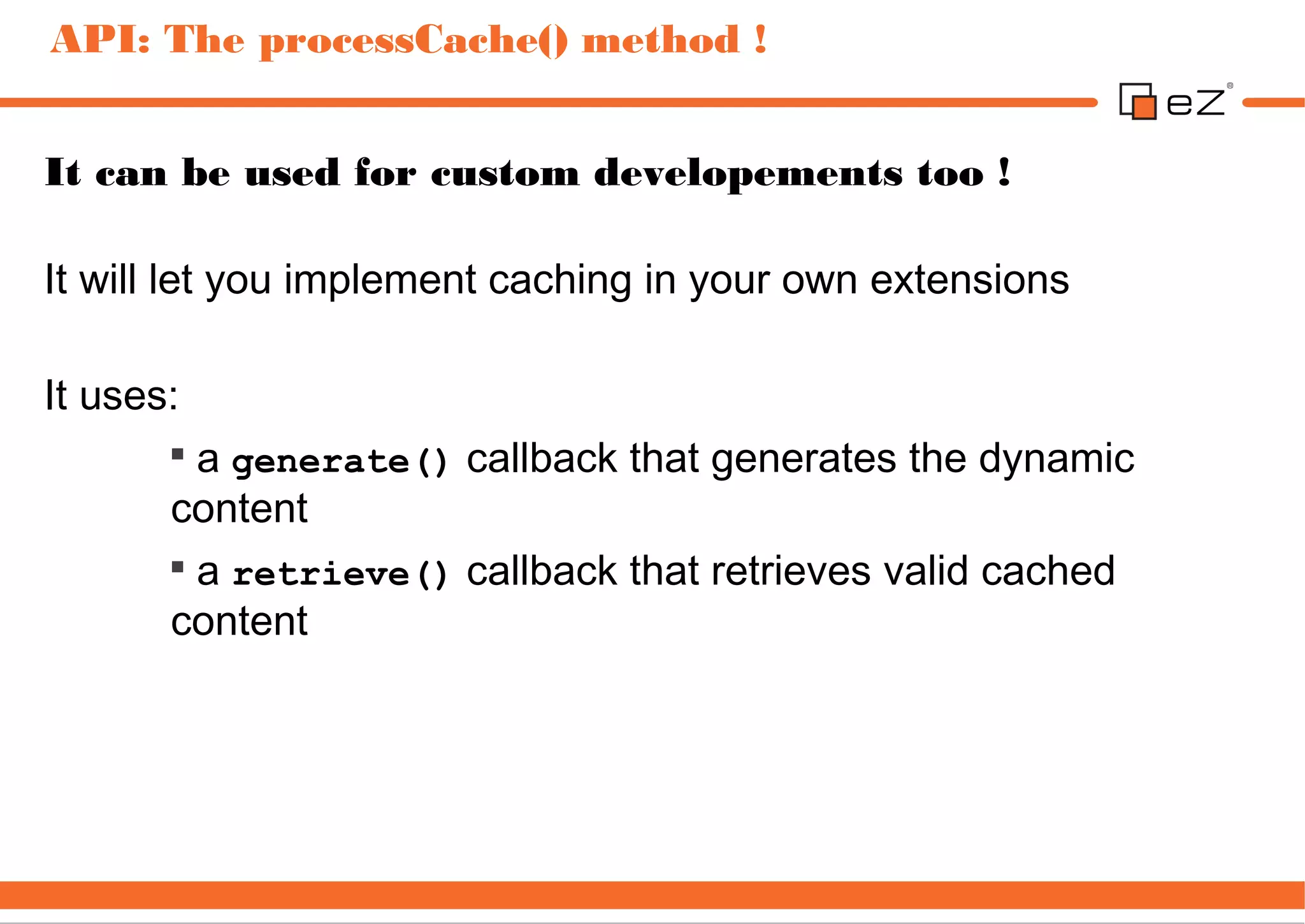
![Configuration #4: binary URLs rewriting
URL rewriting is required to "stream" clusterized binary files to
visitors:
Images
Binary files
They only affect known path for these types of files
To stream different files, new rules must be added
RewriteEngine On
Rewriterule ^/var/([^/]+/)?storage/original/.* /index_cluster.php [L]
Rewriterule ^/var/([^/]+/)?storage/images/.* /index_cluster.php [L]
# Standard eZ Publish rewrite rules
# ...](https://image.slidesharecdn.com/ezsc2012-clustering-techniques-2-120911024904-phpapp02/75/eZ-Publish-cluster-unleashed-revisited-9-2048.jpg)
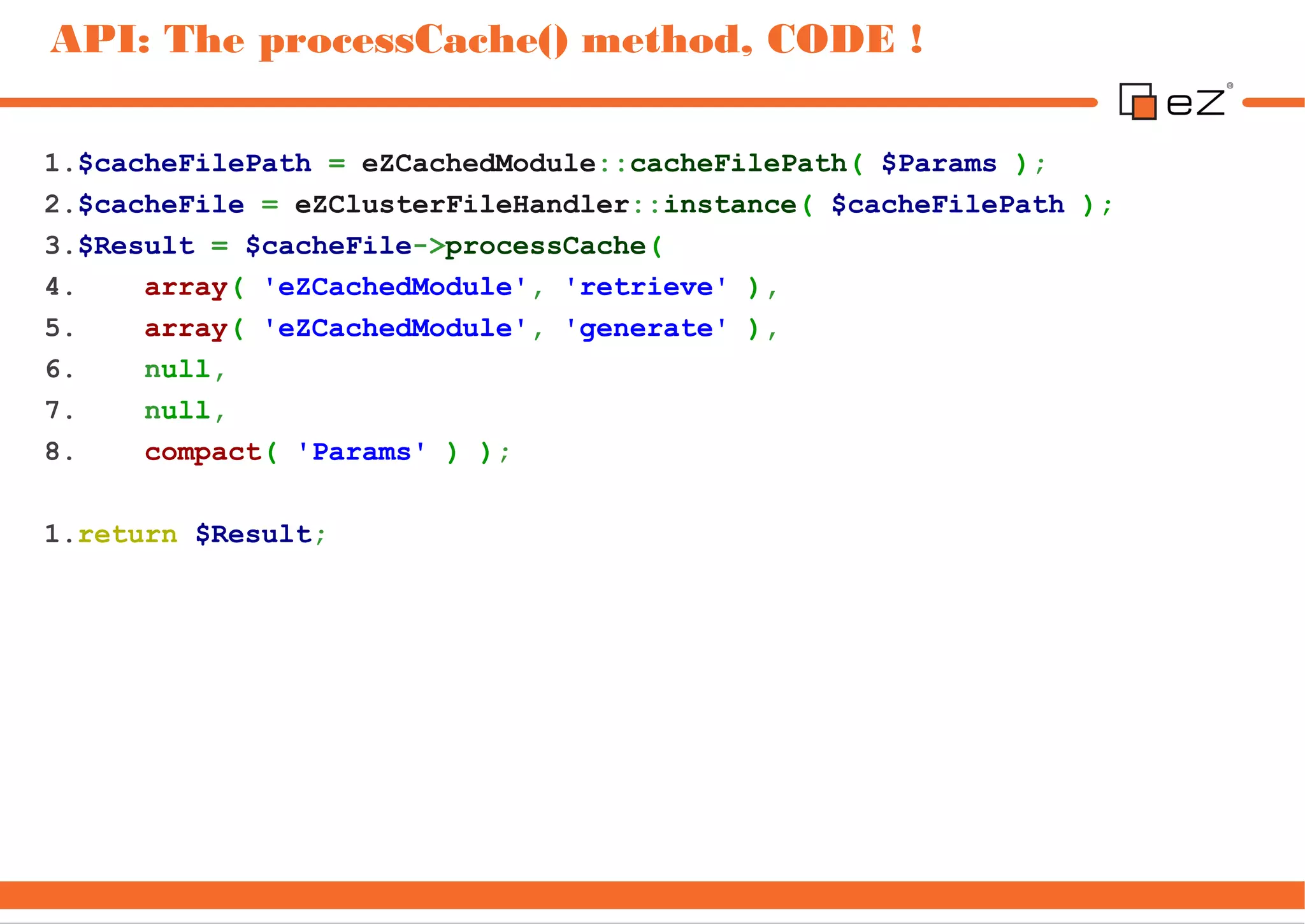
![API: The processCache() method, callback
Let's review an example that caches the whole output
($Result) of a module.
It has a configurable TTL, and provides a custom cache key
that can be used to invalidate cache.
1. Get the code from github:
git clone git://gist.github.com/3635993.git extension/ezcachedmodule
2. enable the extension in site.ini
ActiveExtensions[]=ezcachedmodule
3. and do not forget to regenerate the extensions autoload:
Php bin/php/ezpgenerateautoloads.php –extension](https://image.slidesharecdn.com/ezsc2012-clustering-techniques-2-120911024904-phpapp02/75/eZ-Publish-cluster-unleashed-revisited-18-2048.jpg)
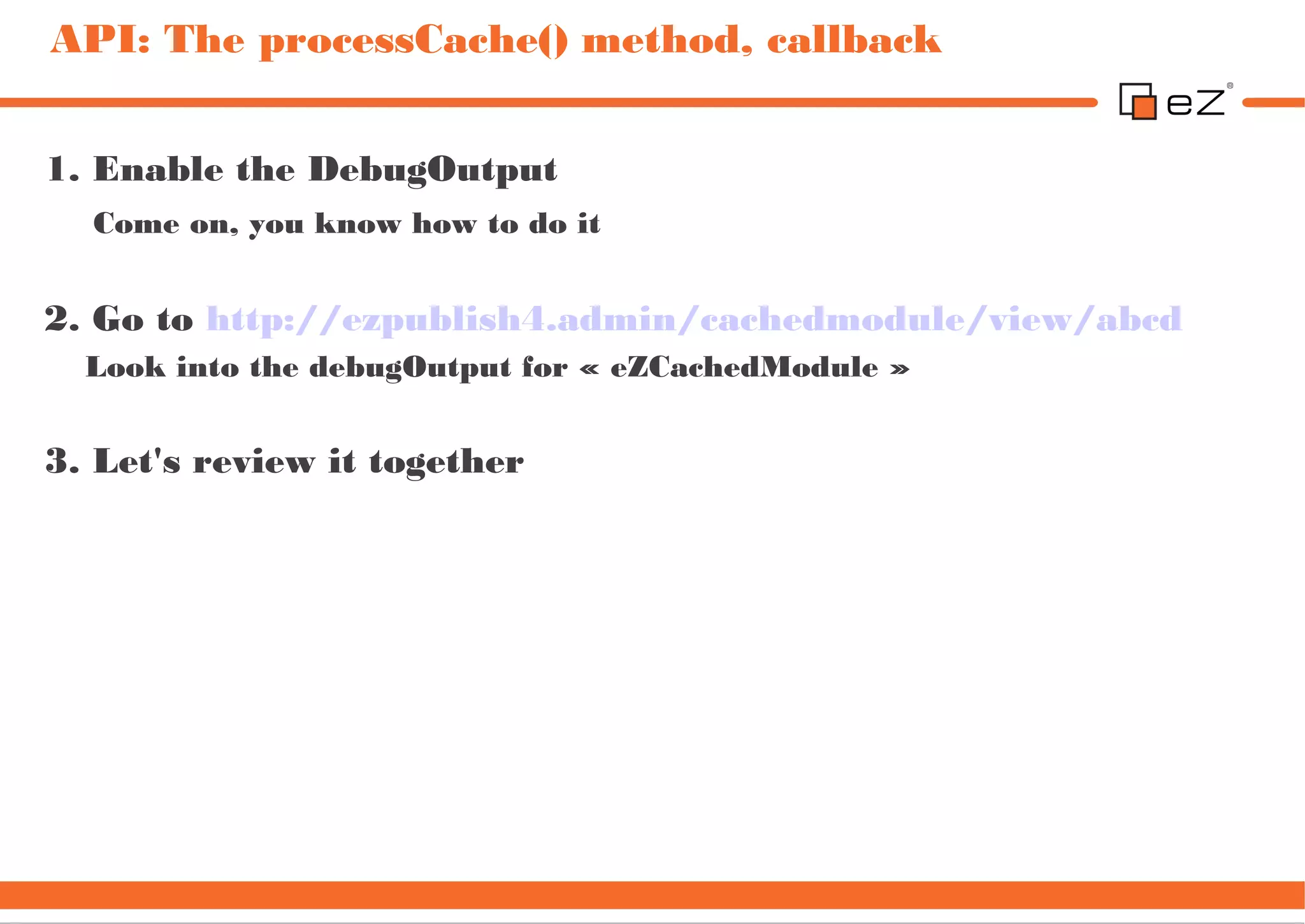
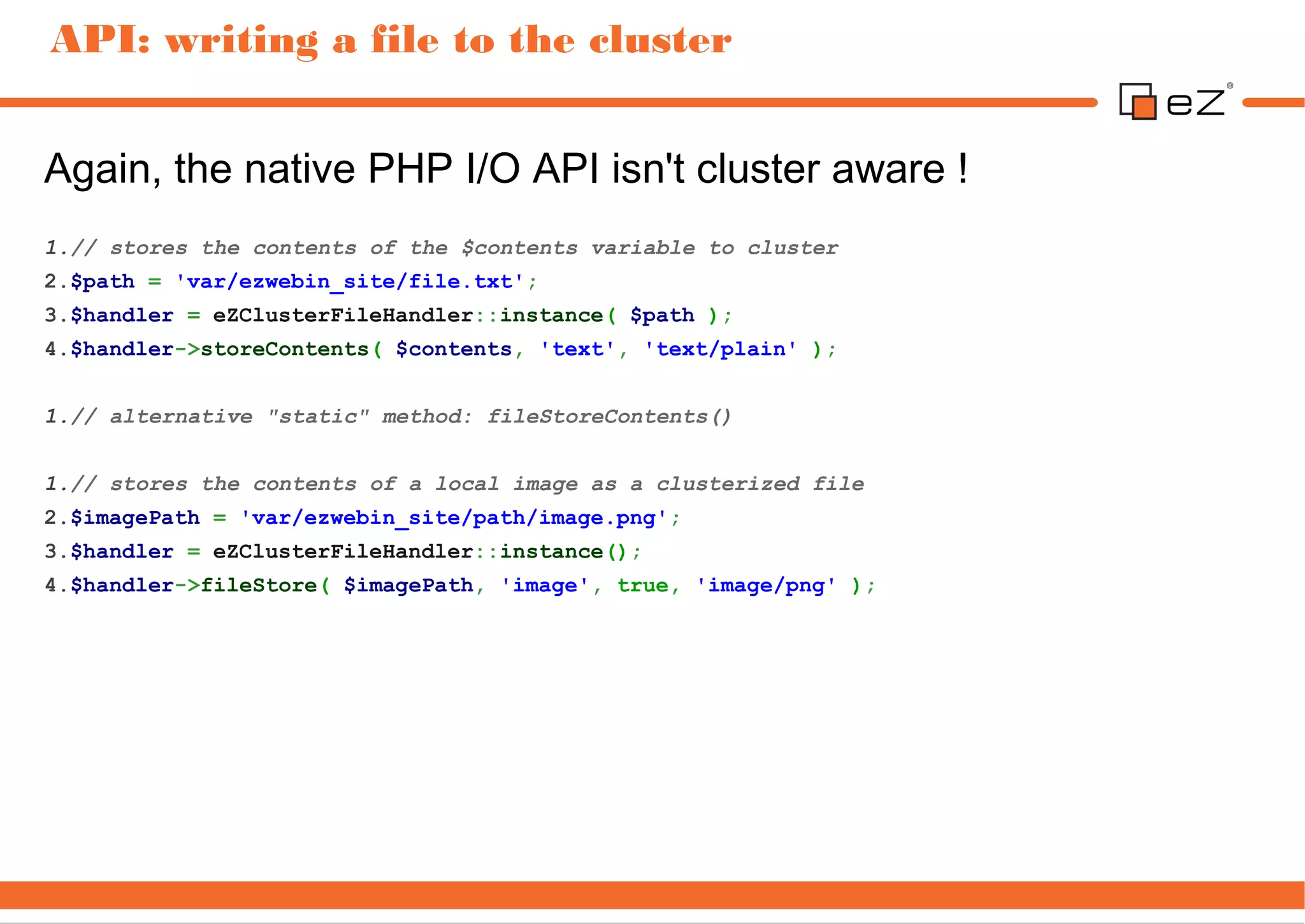
![API: The processCache() method, callback
Let's review an example that caches the whole output
($Result) of a module.
It has a configurable TTL, and provides a custom cache key
that can be used to invalidate cache.
1. Get the code from github:
git clone git://gist.github.com/3635993.git extension/ezcachedmodule
2. enable the extension in site.ini
ActiveExtensions[]=ezcachedmodule
3. and do not forget to regenerate the extensions autoload:
Php bin/php/ezpgenerateautoloads.php –extension](https://image.slidesharecdn.com/ezsc2012-clustering-techniques-2-120911024904-phpapp02/75/eZ-Publish-cluster-unleashed-revisited-20-2048.jpg)