Embed presentation
Download as PDF, PPTX












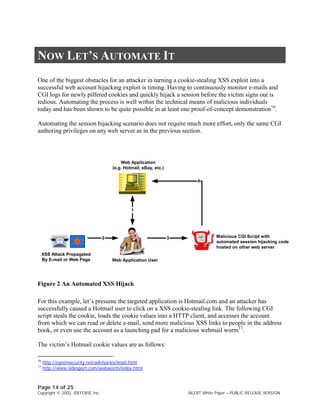


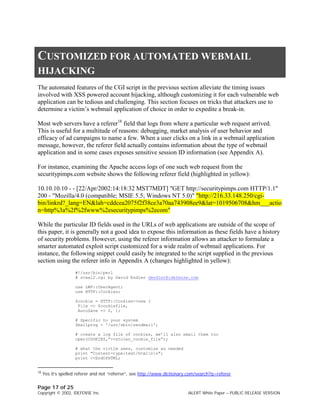







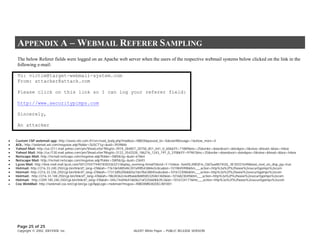
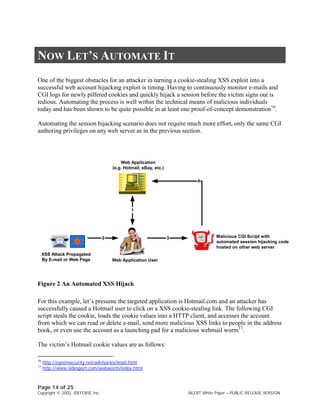
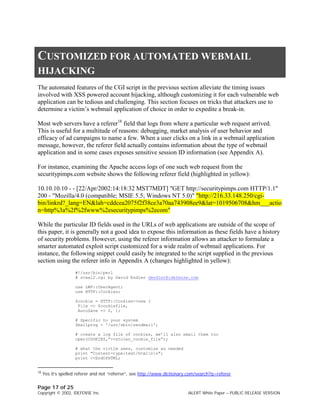
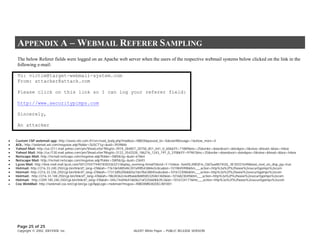
Cross-site scripting (XSS) attacks have evolved over time to become more sophisticated and harmful. XSS was originally used to steal cookies and hijack user sessions but now attackers use it to spread malware, steal personal information, and conduct distributed denial-of-service attacks. As XSS attacks advanced, defenses needed to improve to protect against the new threats.