The document summarizes a student group's proposal presentation for their final year project (FYP) on designing and implementing a wireless ad hoc network for disaster management. The key points are:
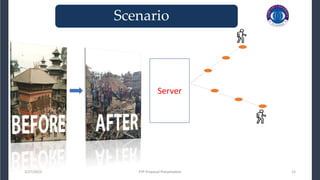
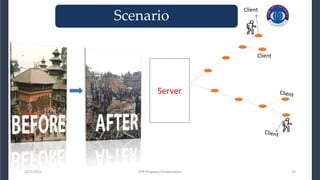
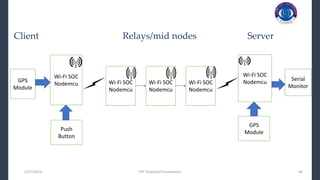
1) The project aims to develop a wireless ad hoc network using NodeMCU modules to enable victims to communicate with rescue teams when normal communication infrastructure is down during disasters.
2) The presentation outlines the objectives, literature review, research questions, system design, and methodology to be used in the project.
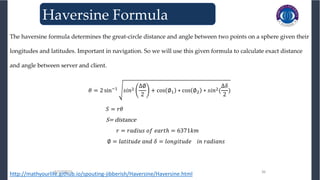
3) Mathematical models like the Haversine formula will be used to calculate distances between nodes based on GPS coordinates to determine the network topology.
![3/27/2023 FYP Proposal Presentation 5
During these disasters, communication infrastructure goes
down. It is therefore, necessary to build up a Ad hoc
wireless communication system to let rescue teams
communicate with victims to ensure their safety. [1]
3/27/2023 FYP Proposal Presentation 5
_______________________________
_______________________________
Problem Statement
When disaster occurs, it becomes very critical to rescue
survivals as soon as possible and guarantee the safety of
rescuers.](https://image.slidesharecdn.com/evaluation2-230327194411-cd51115b/85/evaluation2-pptx-5-320.jpg)
![8
Literature review
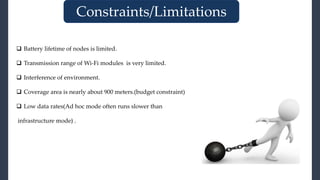
Ref Proposed Approach Outcome Comments
[2] Design and Deployment of
Infrastructure-
Independent D2D Networks
Without Centralized
Coordination
Infrastructure independent
wireless network that
connects different end
devices directly without
centralized coordination.
Various types of end devices GPS, camera,
sensors and transceivers communicate with
each without centralized coordination. TDMA is
used to assign a specific slot to each device for
communication purpose.
[3] Rapid Deployment of
Wireless Ad Hoc Backbone
Networks for Public Safety
Incident Management
Two types of control
information for the
deployment of relay.
Relay deployment is triggered either because
the mobile user detects link quality degradation,
or because it receives an explicit deployment
request from its neighbors.
[4] Performance Analysis of
Highly Available Ad Hoc
Surveillance Networks Based
on Dropped Units
A threshold for triggering a
deployment event is set.
Once the link quality drops below this threshold,
the user must drop a new relay.
[5] An Automatic, Robust, and
Efficient Multi-User
Breadcrumb System for
Emergency Response
Applications
Automatic breadcrumb
dispenser is proposed
An algorithm attempts to optimize the trade-off
between the improvement to the
communication link accomplished by deploying
a new relay and the number of remaining relays.
Literature Review](https://image.slidesharecdn.com/evaluation2-230327194411-cd51115b/85/evaluation2-pptx-8-320.jpg)
![Literature review
Ref Proposed Approach Outcome Comments
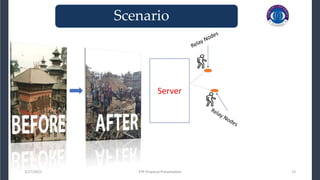
[6] Unmanned Ground Vehicle
Radio Relay Deployment
System for Non-Line-of-
Sight Operations
Mobile relays adjust their
own locations on demand.
The relays follow a robot leader one after the
other, forming a line. When the degradation in
the RSSI reaches a certain threshold, the
farthest relay in the line will stop and convert
into a static relay. This process is repeated until
all relays have become static nodes.
[7] Using Mobile Robots to
Establish Mobile Wireless
Mesh Networks and Increase
Network Throughput
Two AP’s outside each other
transmission range are
connected via mobile relays.
All relays are initially placed close to the first AP.
Then, the relay leader moves forward until it
finds the second AP. Each time the RSSI value
falls below a given threshold, a follower relay
will move to maintain the connectivity between
the first AP and the leader; this follower will
pursue the node ahead of it, creating a chain.
Once the leader reaches the second AP, it will
stop.
Literature Review
9](https://image.slidesharecdn.com/evaluation2-230327194411-cd51115b/85/evaluation2-pptx-9-320.jpg)


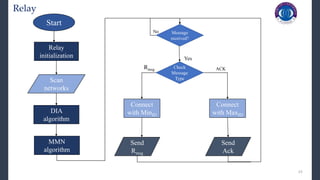
![24
DIA Algorithm
Dynamic ID Assignment
Input: AVBnet (Available networks)
Output: IDassigned (Assigned ID)
Procedure:
Step 1: defining and initialising variables
Arrayid = Array containing available networks IDs
Findex = First index of Arrayid
Sindex = Second index of Arrayid
Step 2: Assigning ID to relay
- Store AVBnet in Arrayid
- Sort Arrayid in Ascending Order
- IDassigned = Arrayid [Findex]
𝒊𝒇 𝐼𝐷𝑎𝑠𝑠𝑖𝑔𝑛𝑒𝑑 = −1
- IDassigned = Arrayid [Sindex]
- End if
- ID assigned = ID assigned + 1](https://image.slidesharecdn.com/evaluation2-230327194411-cd51115b/85/evaluation2-pptx-24-320.jpg)
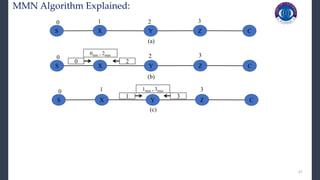
![26
MMN Algorithm:
MMN Algorithm
Input: AVBnet (Available networks)
Output: MinID and MaxID
Procedure:
Step 1: defining and initialising variables
Arrayid = Array containing available networks IDs
Findex = First index of Arrayid
Lindex = Last index of Arrayid
Step 2: Finding Minimum and Maximum IDs
- Store AVBnet in Arrayid
- Sort Arrayid in Ascending Order
- MinID = Arrayid [Findex]
- MaxID = Arrayid [Lindex]](https://image.slidesharecdn.com/evaluation2-230327194411-cd51115b/85/evaluation2-pptx-26-320.jpg)
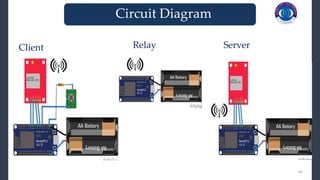
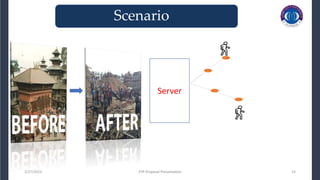
![3/27/2023 37
3/27/2023 37
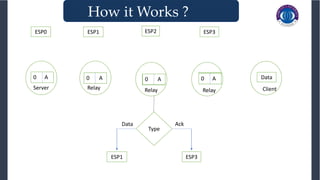
How it Works ?
Server
ESP0
Relay
ESP1
Relay
ESP2
Relay
ESP3
Relay
ESP4
Algorithm for assigning SSID to relays
1. Initialize SSID (Service Set Identifier) of each node with “ESP”.
2. Each node will scan for available “n” networks .
3. If n>0 then store SSIDS of available networks in array p[n].
4. P[n] = {ESP3,ESP2,ESP4,ESP,1}
5. Then Sort array P[n] in ascending order.
6. Select P[0] and add 1 to assign SSID to current node.](https://image.slidesharecdn.com/evaluation2-230327194411-cd51115b/85/evaluation2-pptx-37-320.jpg)
![3/27/2023 FYP Proposal Presentation 46
[1] Z. C. P. L. Junbo Wang, Song Guo and J. Wu, Optimization of deployable-base stations with guaranteed qoe in
disaster scenarios," IEE Proceedings. Nanobiotechnology, vol. 13(9), pp. 1{16, 2016}.
[2] H. Li, Lin Shan, T. Matsuda and R. Miura, "Design and deployment of infrastructure-independent D2D networks
without centralized coordination," International Symposium on Wireless Communication Systems (ISWCS), Brussels, 2015,
pp. 376-380.
3] J. Q. Bao and W. C. Lee, “Rapid Deployment of Wireless Ad Hoc Backbone Networks for Public Safety Incident
management,” Proc. Global Communications Conference (GLOBECOM), Nov. 2007, pp. 1217–21.
[4] A. Wolff, S. Subik, and C. Wietfeld, “Performance Analysis of Highly Available Ad Hoc Surveillance Networks Based
on Dropped Units,” Proc. IEEE Conf. Technologies for Homeland Security, Waltham, MA, USA, May 2008, pp. 123–28.
[5] H. Liu et al., “An Automatic, Robust, and Effi cient Multi-User Breadcrumb System for Emergency Response
Applications,” IEEE Trans. Mobile Computing, vol. 13, no. 4, April 2014, pp. 723–36.
[6] N. Pezeshkian, H. G. Nguyen, and A. Burmeister, “Unmanned Ground Vehicle Radio Relay Deployment System for
Non-Line-of-Sight Operations,” Proc. 13th IASTED Int’l. Conf. Robotics and Applications, Würzburg, Germany, 2007, pp.
501–06.
[7] C. Q. Nguyen et al., “Using Mobile Robots to Establish Mobile Wireless Mesh Networks and Increase Network
Throughput,” Int’l. J. Distributed Sensor Networks (IJDSN), vol. 2012, 2012, pp. 1–13.
3/27/2023 FYP Proposal Presentation 46
_______________________________
_______________________________
References](https://image.slidesharecdn.com/evaluation2-230327194411-cd51115b/85/evaluation2-pptx-46-320.jpg)