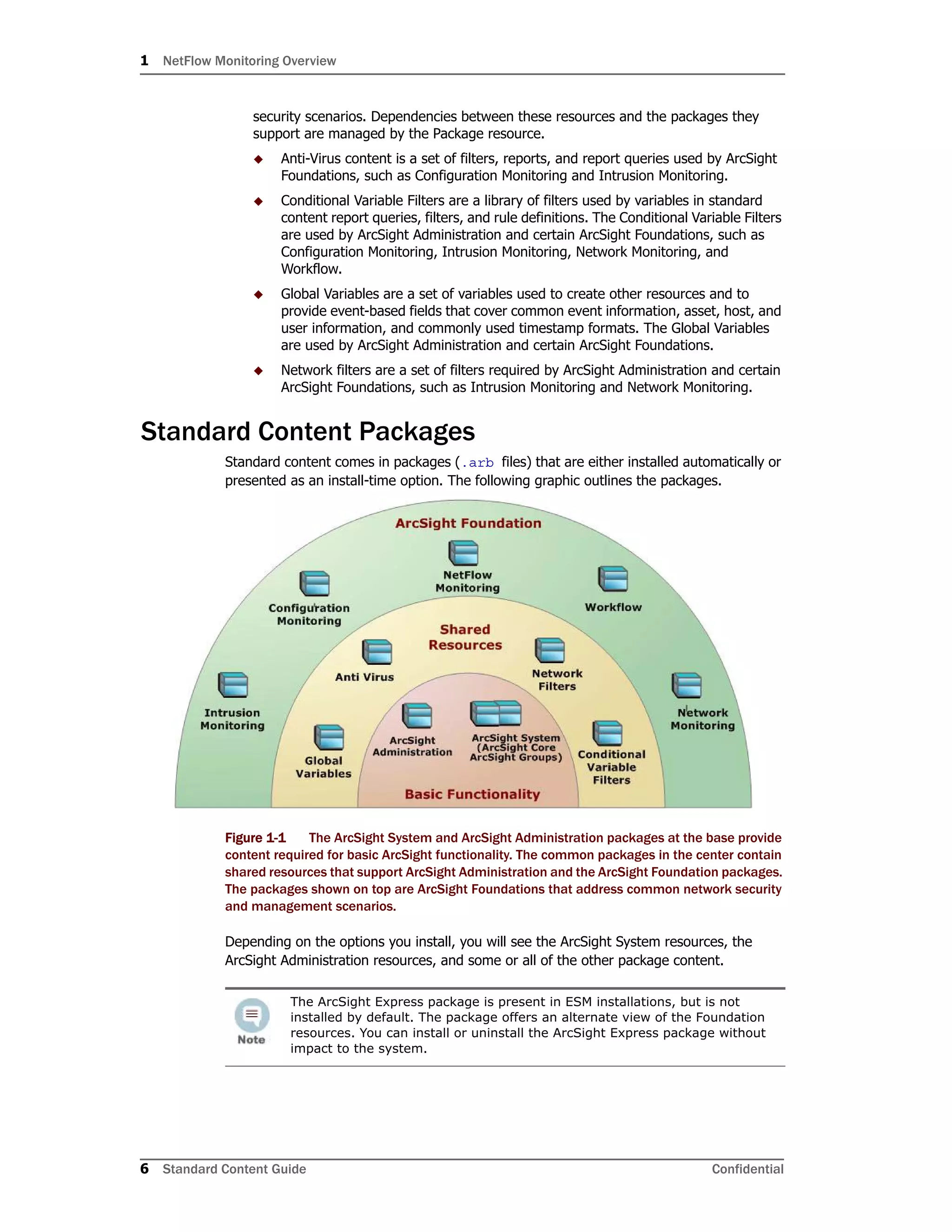
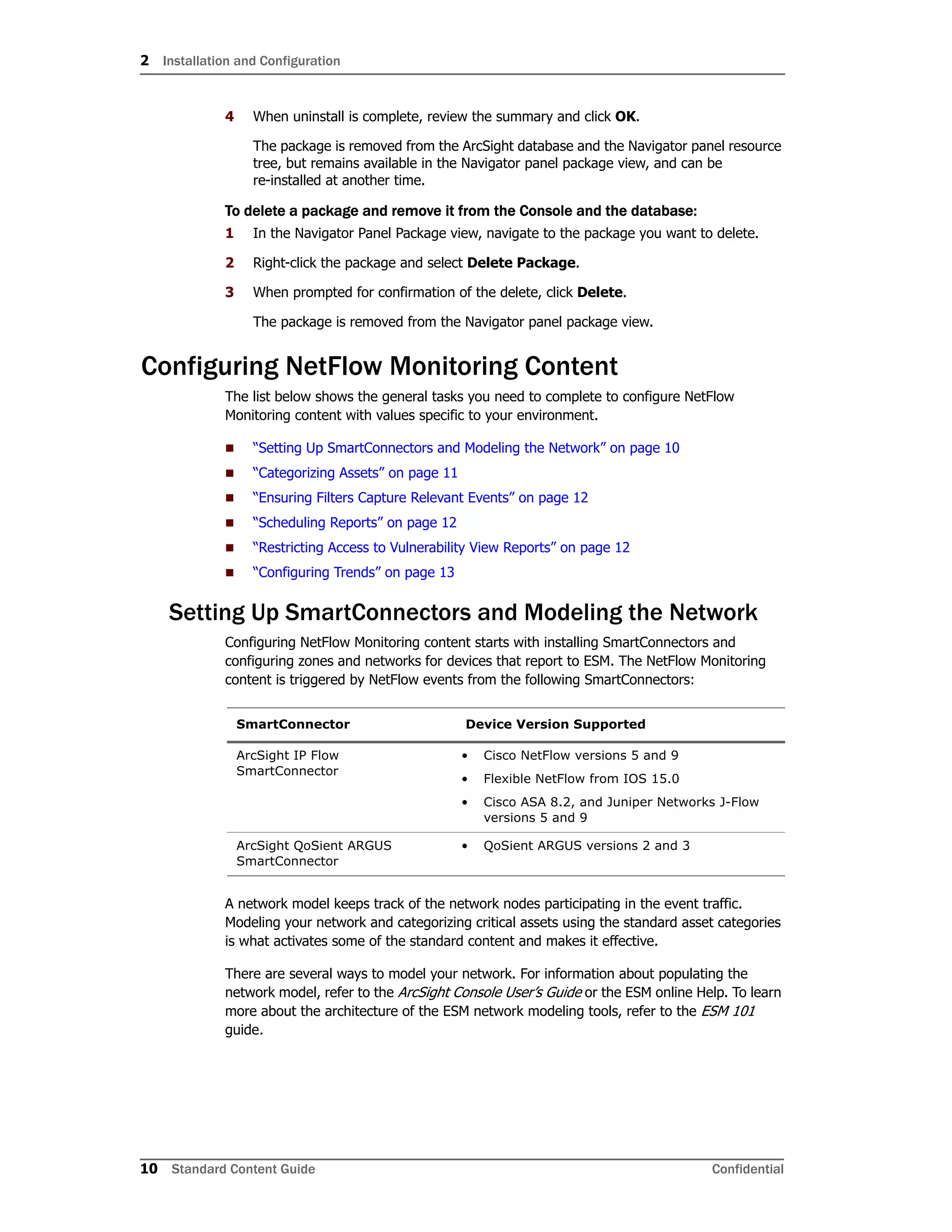
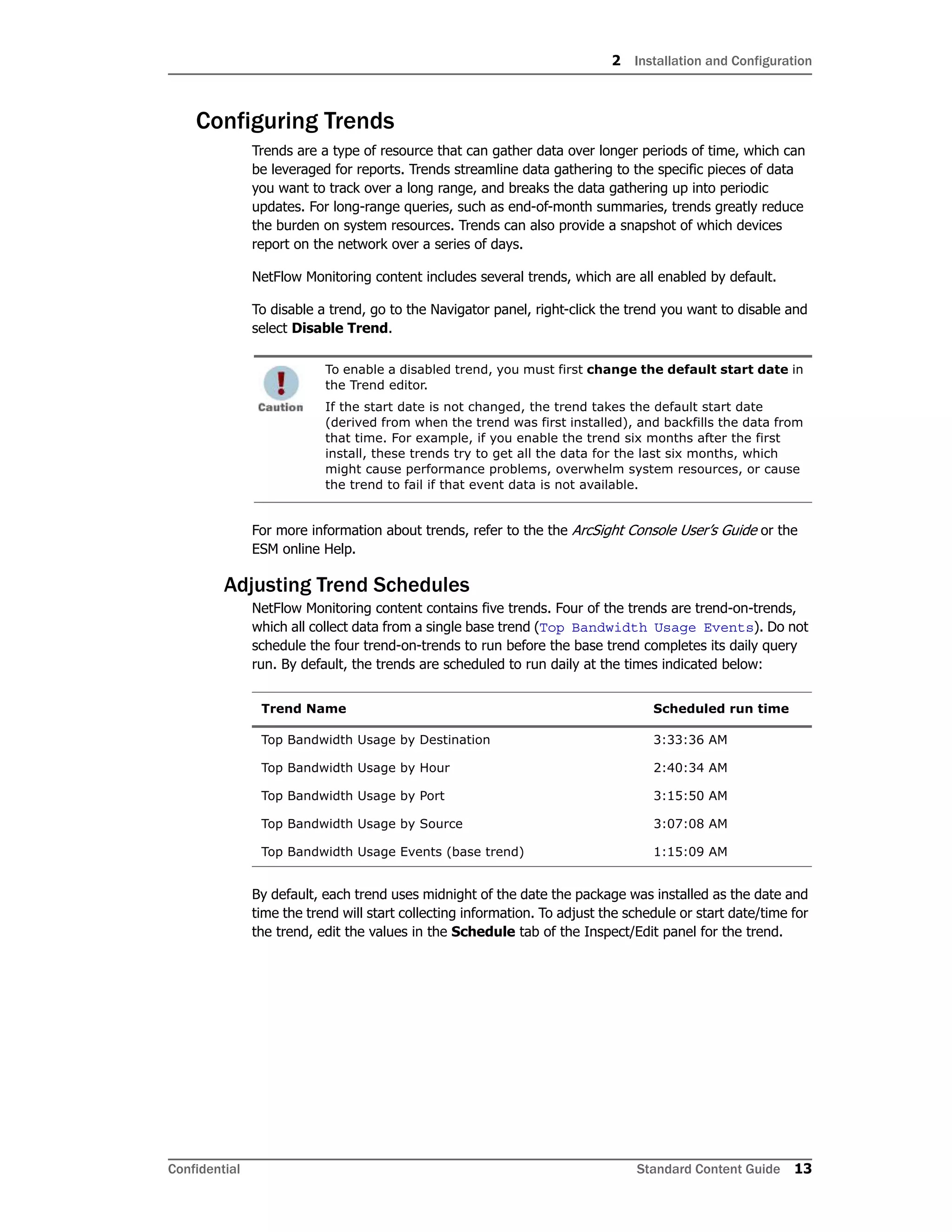
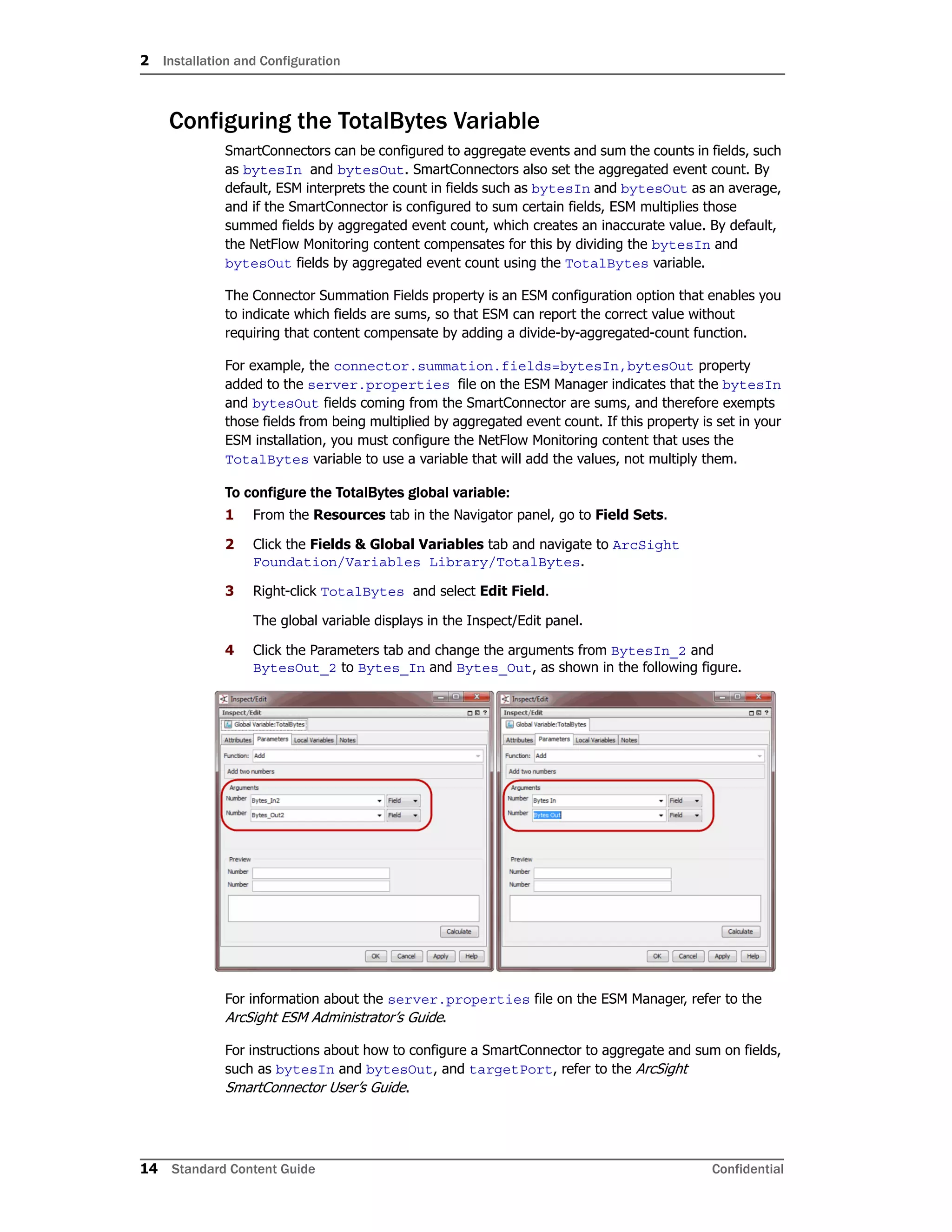
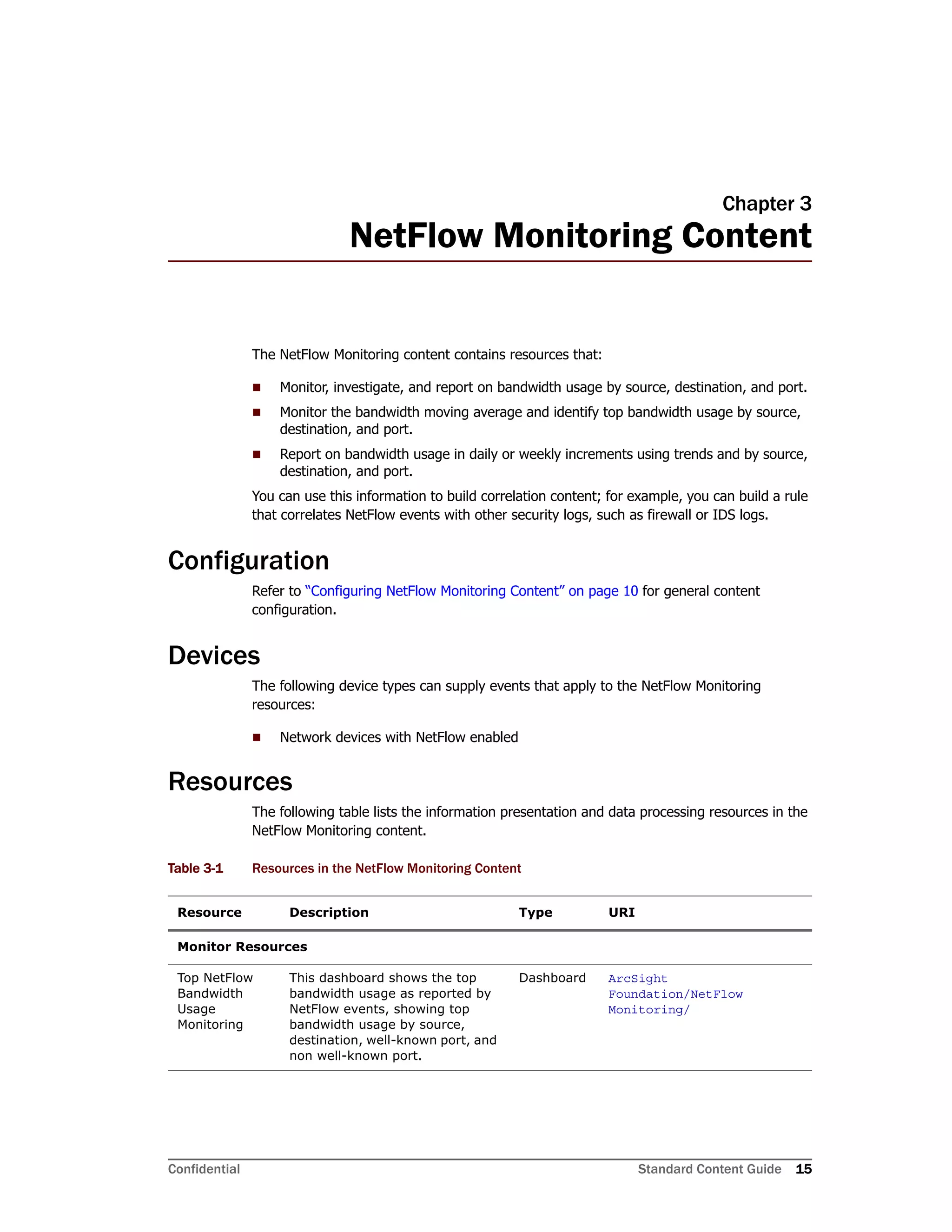
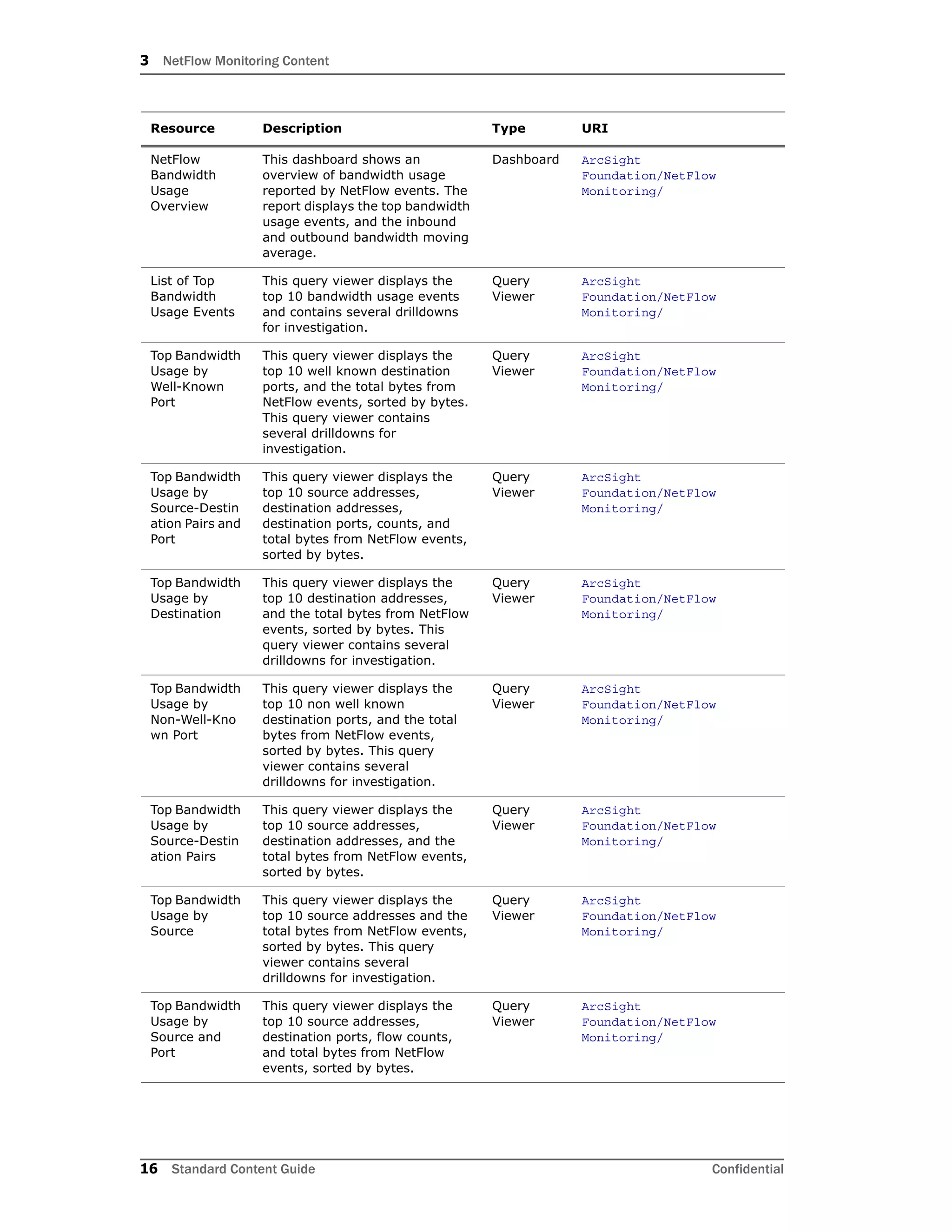
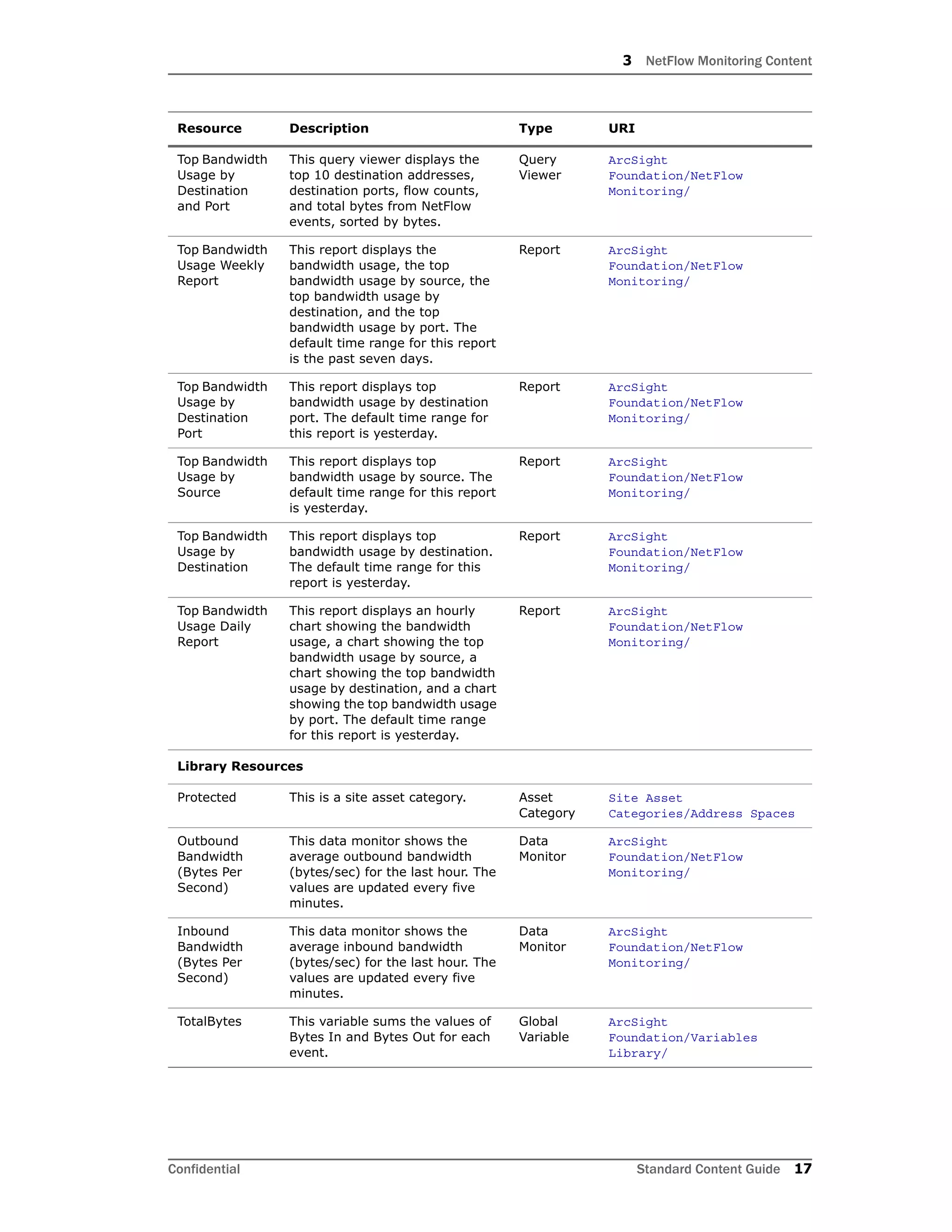
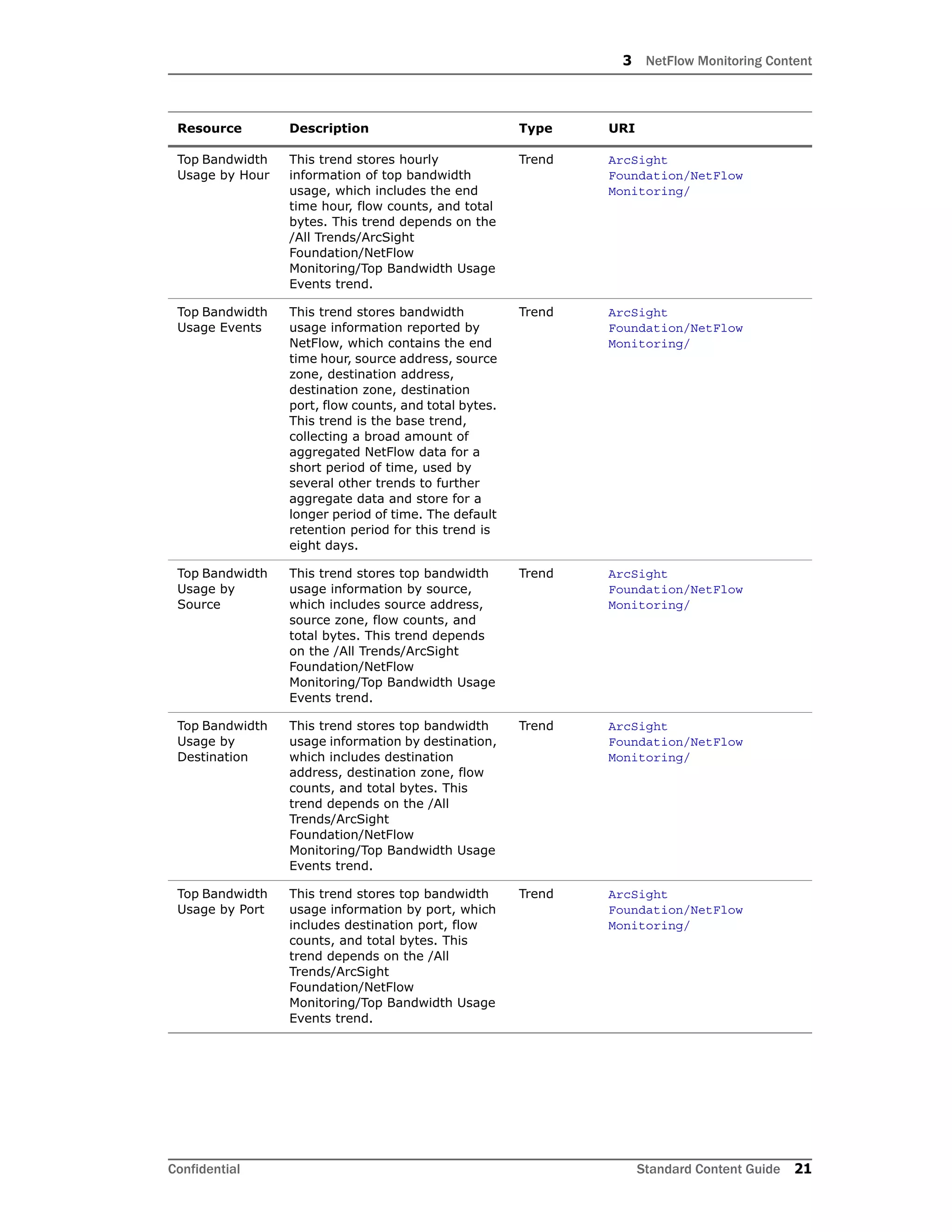
The document provides instructions for configuring NetFlow monitoring content in ArcSight ESM, including installing the NetFlow monitoring package, modeling the network, categorizing assets, ensuring filters capture relevant events, scheduling reports, restricting access to vulnerability reports, and configuring trends.