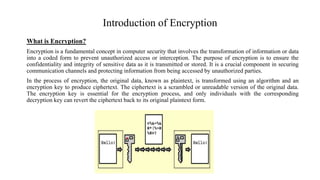
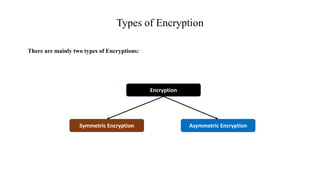
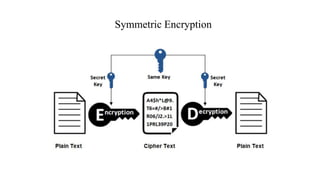
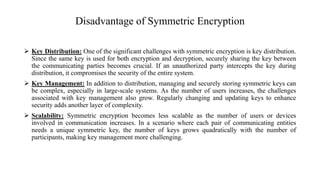
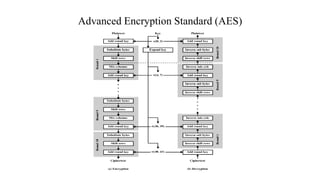
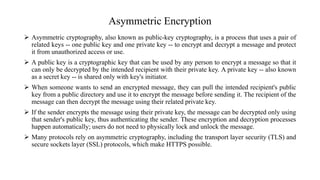
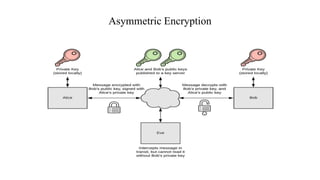
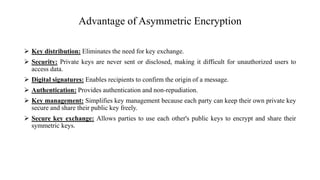
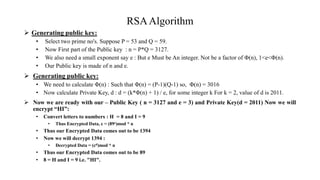
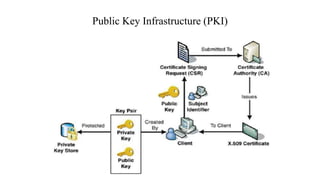
The document provides an overview of encryption, detailing its importance in securing data confidentiality and integrity through transformations into coded forms. It explains the main types of encryption: symmetric and asymmetric, highlighting their processes, advantages, and disadvantages. Additionally, it discusses the RSA algorithm, digital certificate management, and the role of Public Key Infrastructure (PKI) in facilitating secure communications.