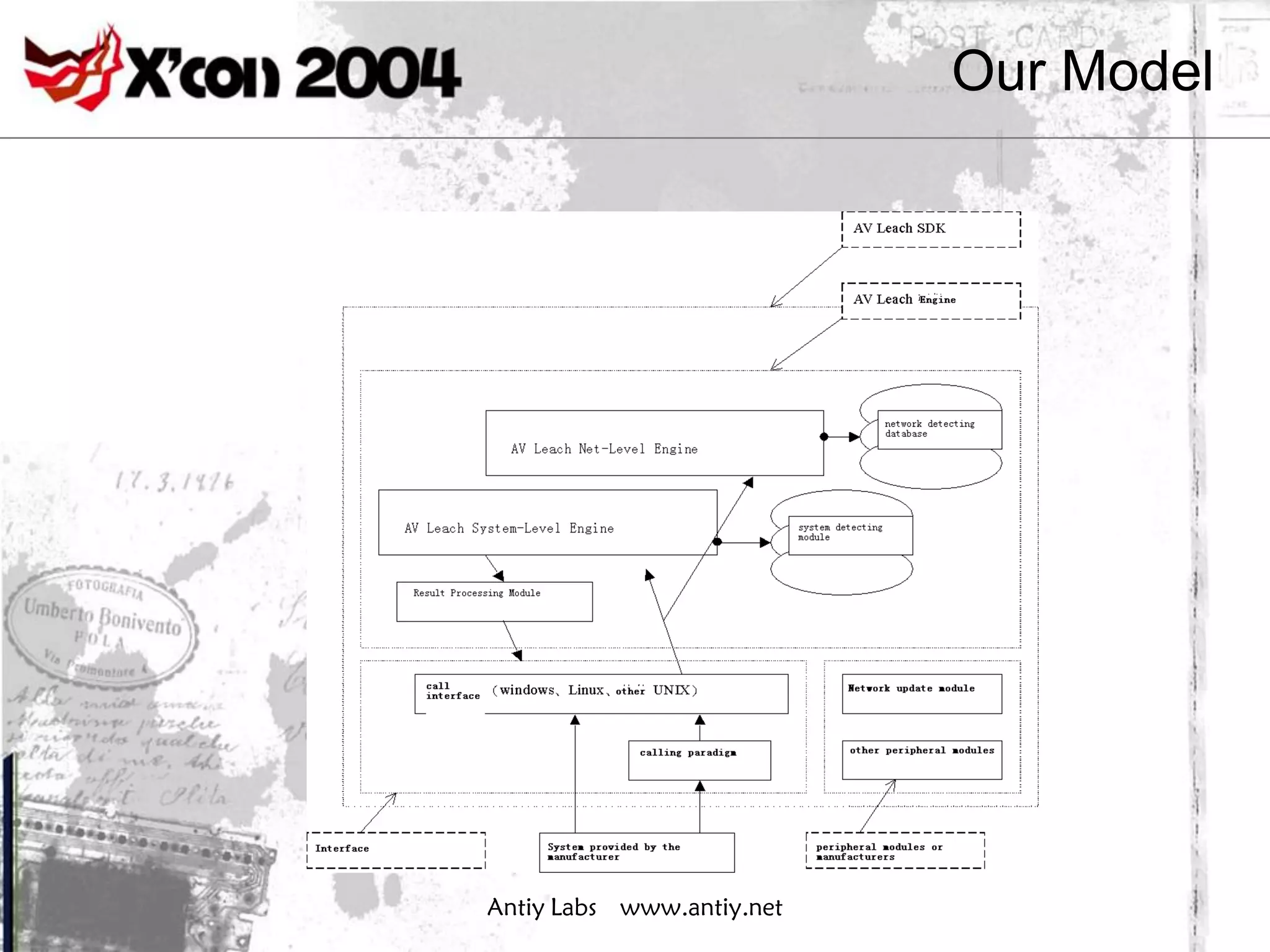
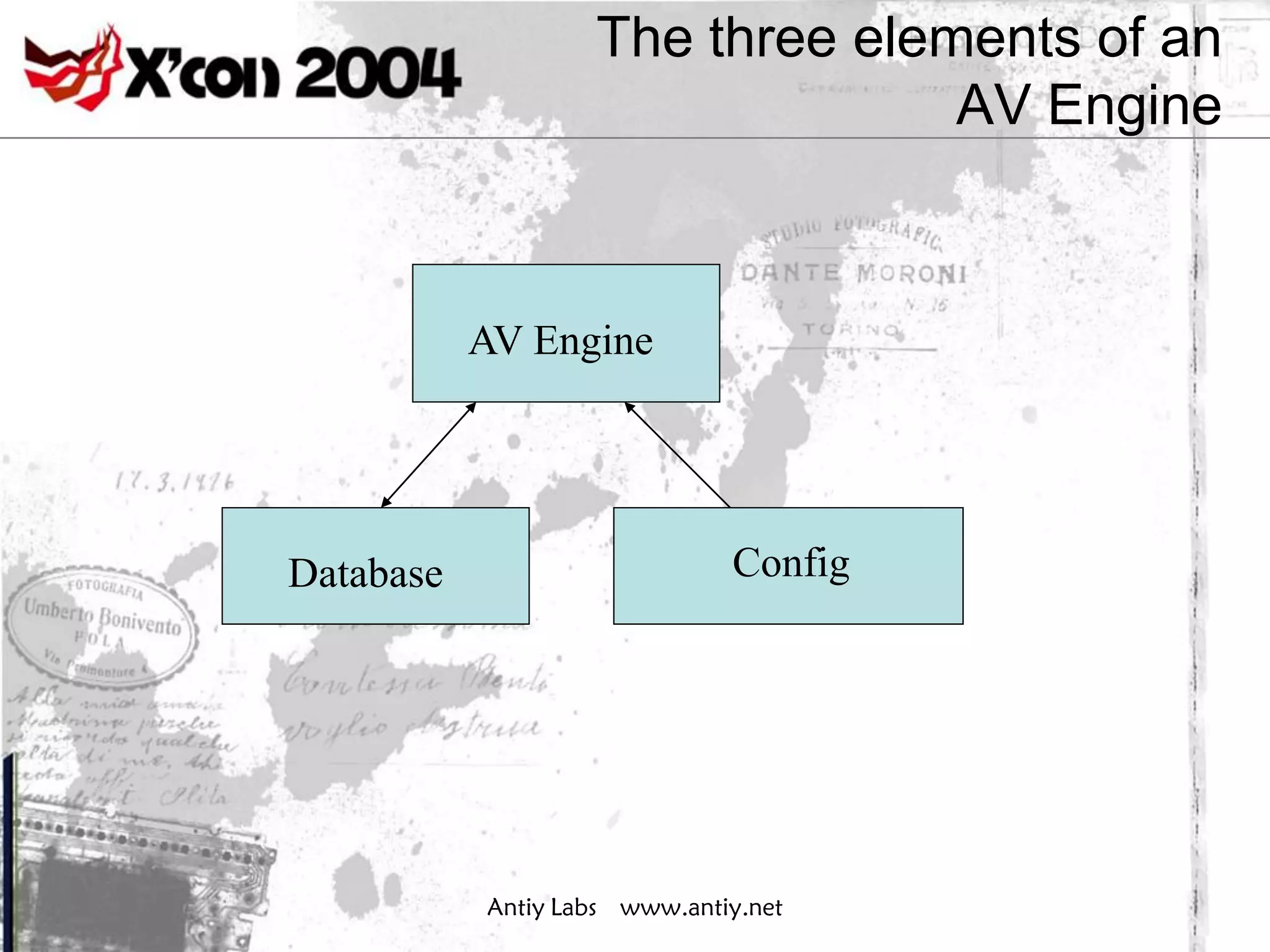
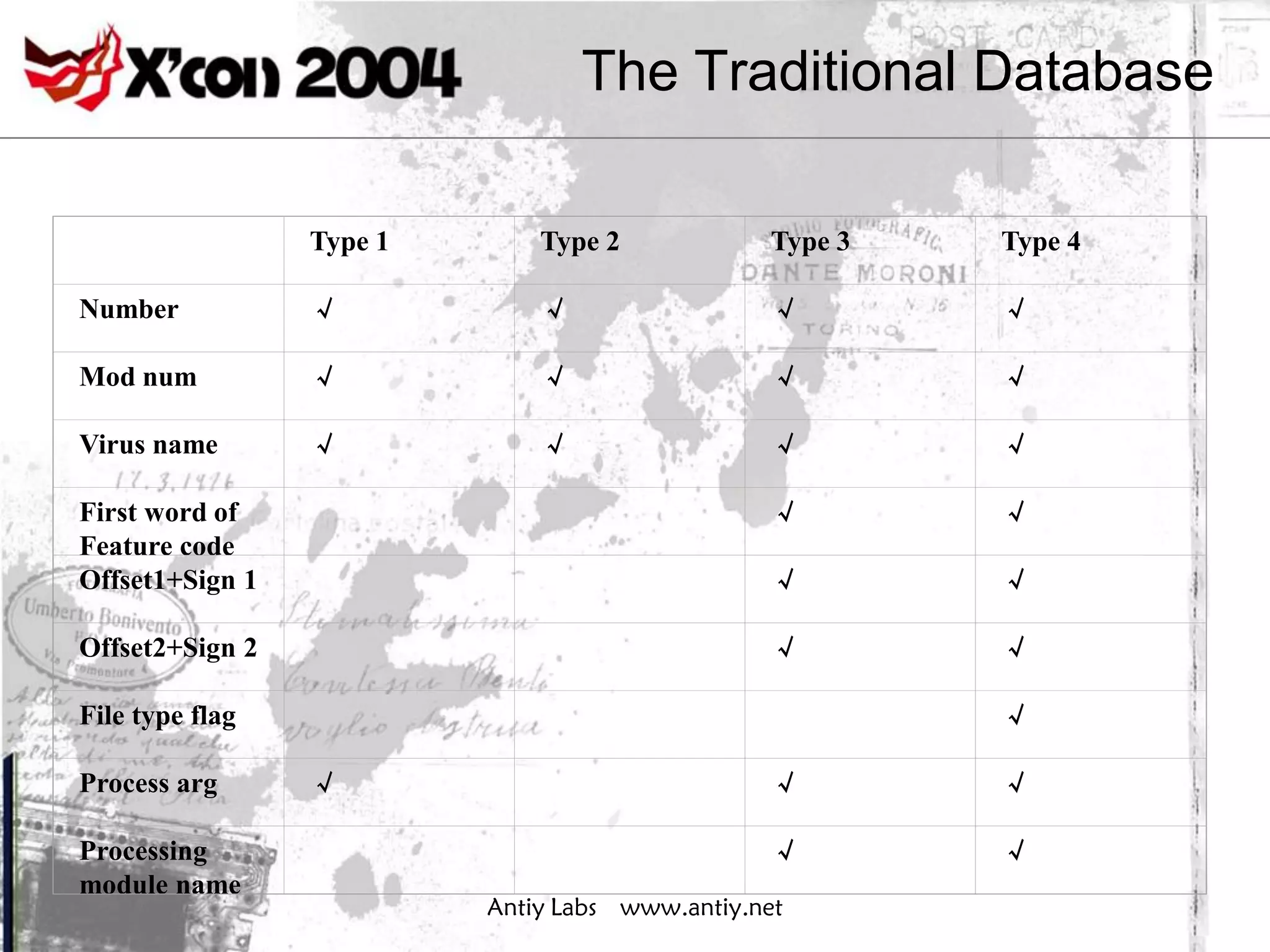
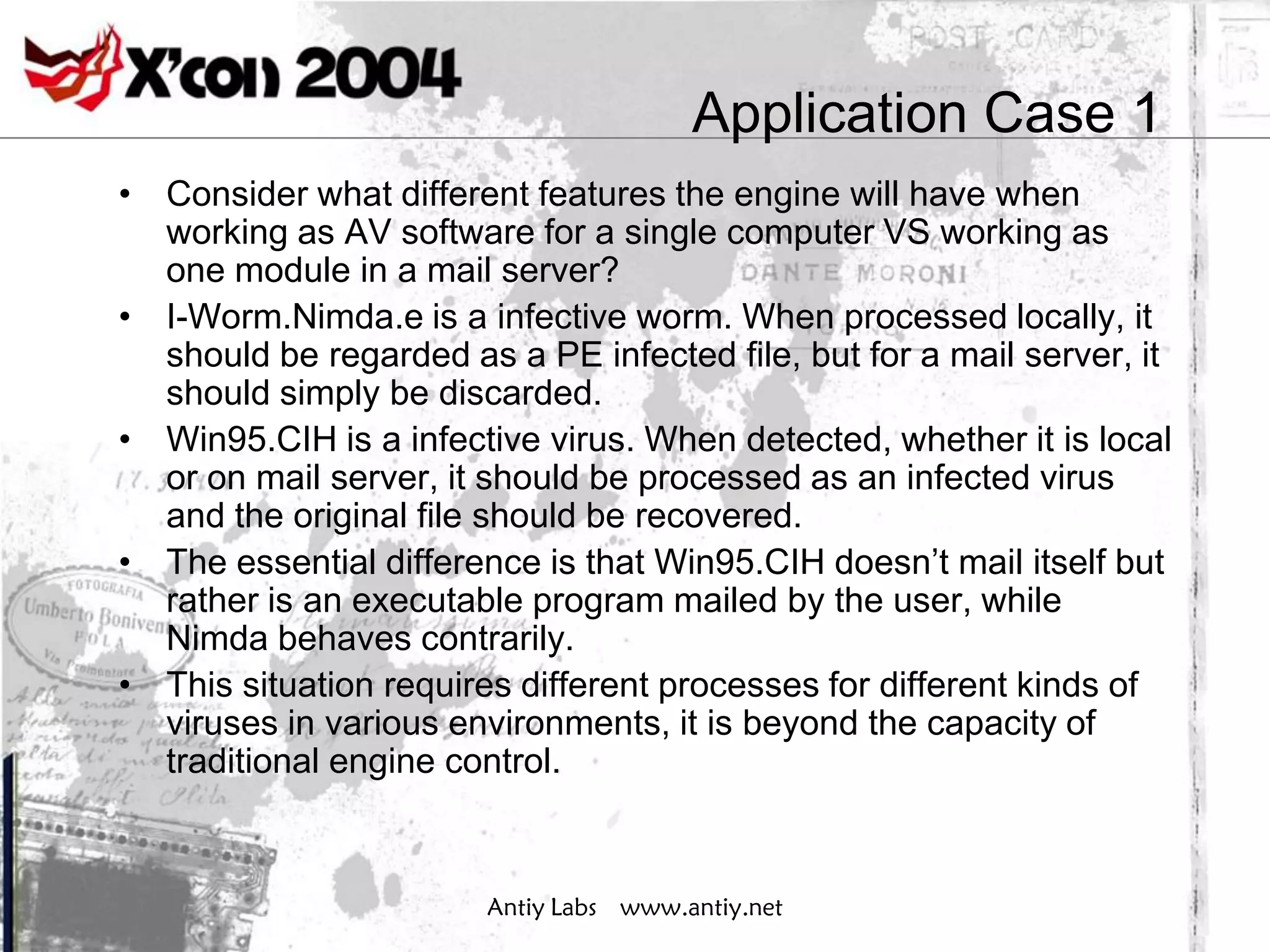
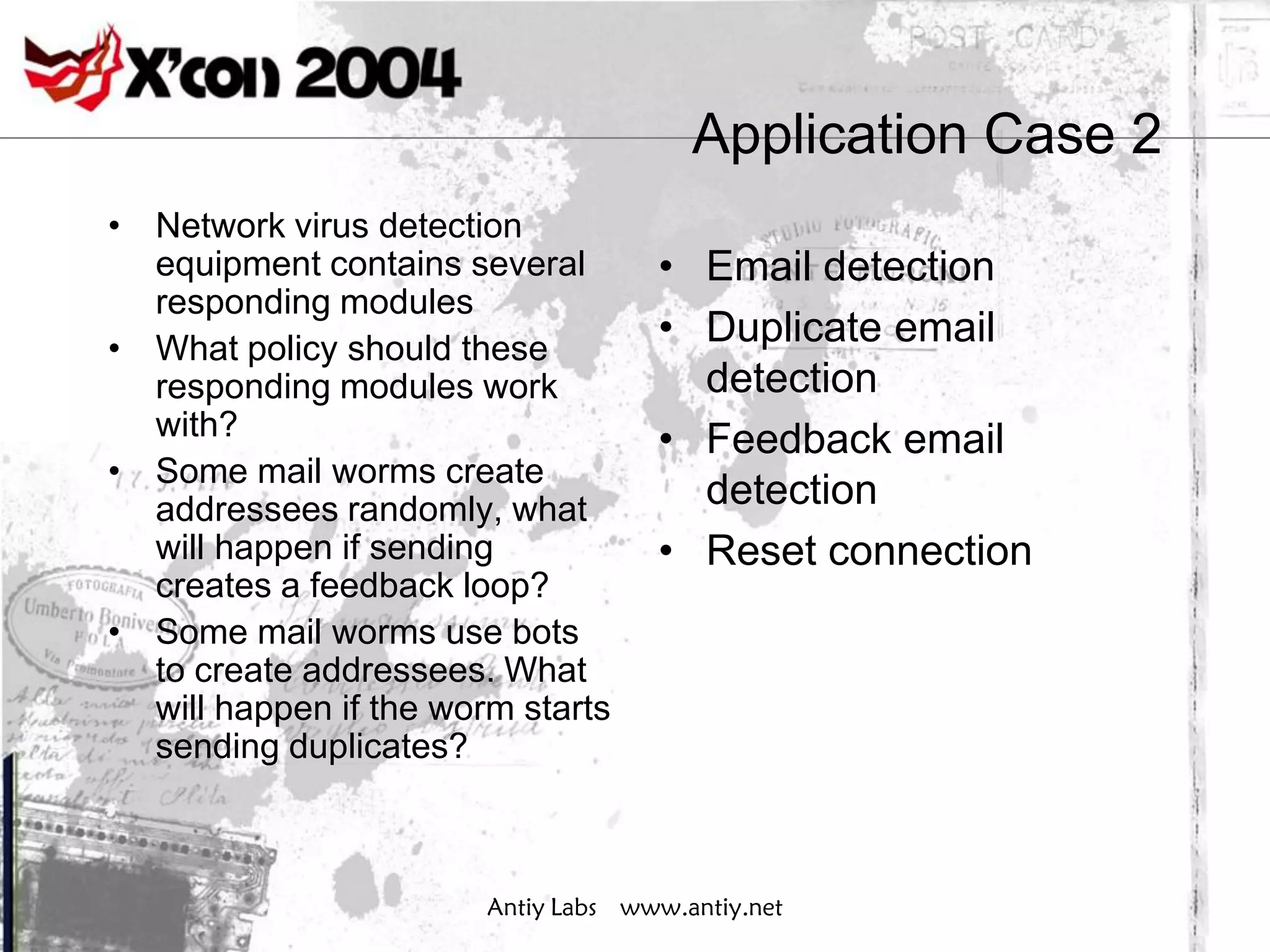
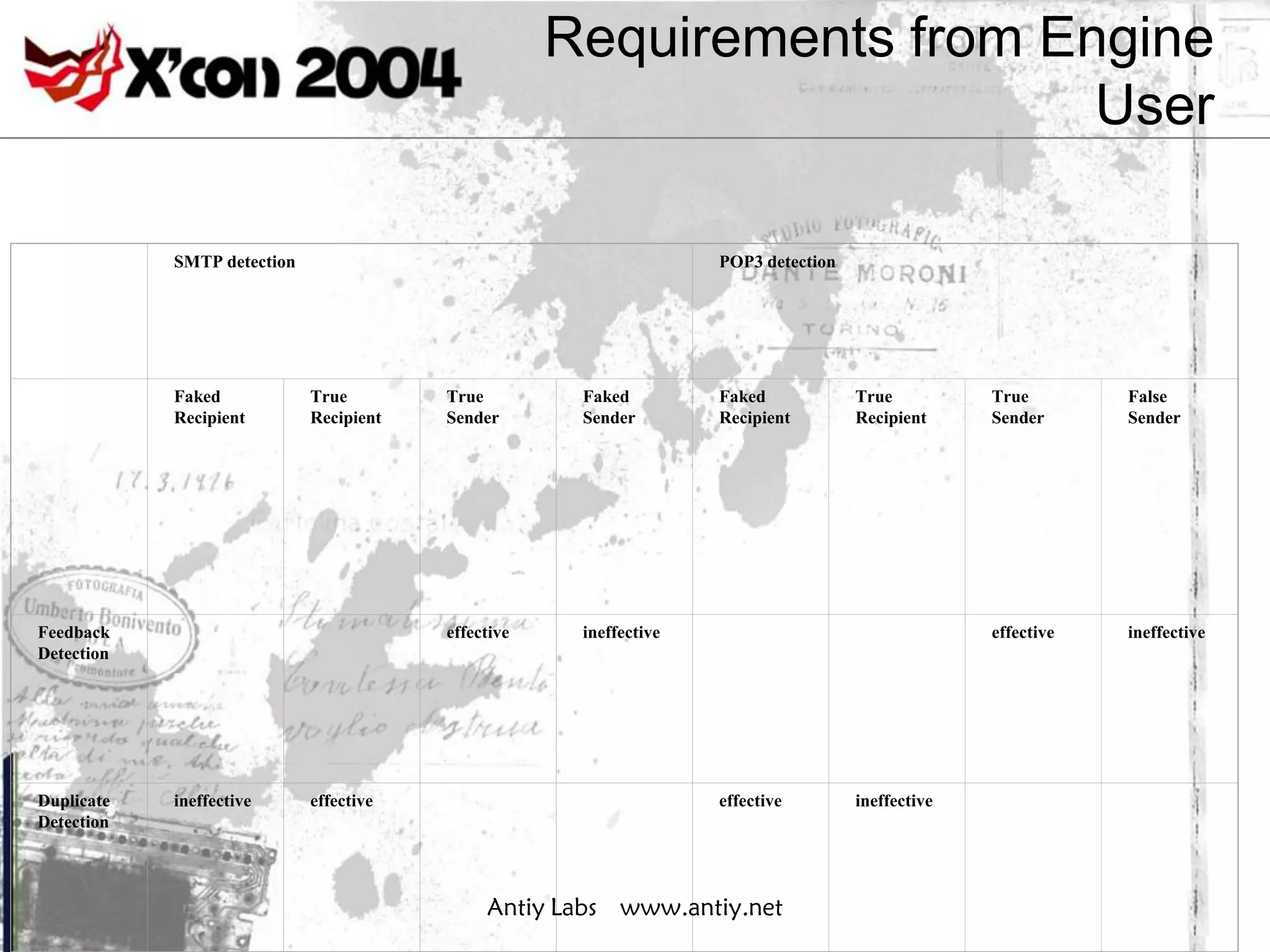
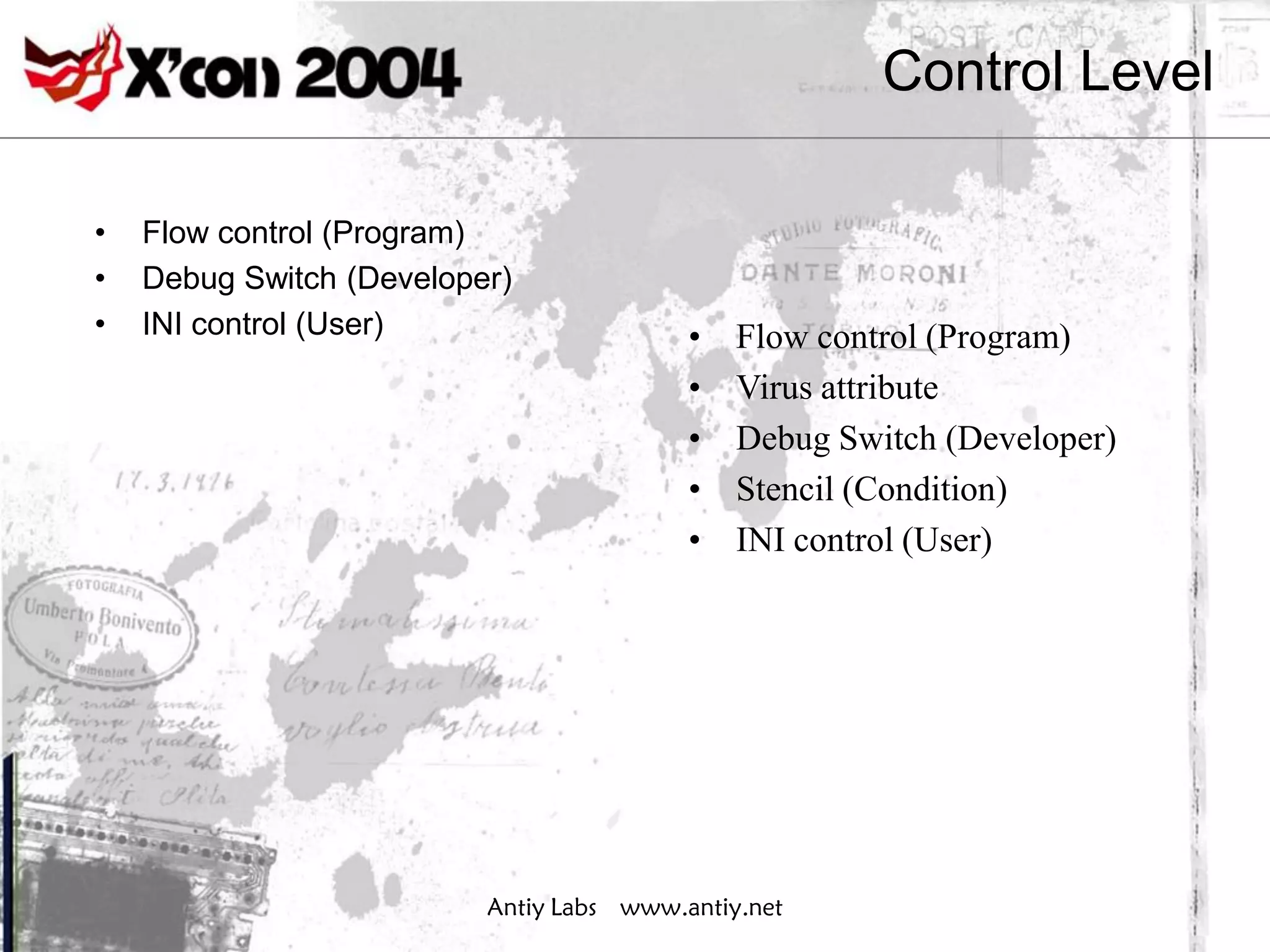
The document discusses challenges to traditional antivirus principles from developments in technology, proposes a framework with high granularity processing for an embeddable antivirus engine, and analyzes how the engine, database, and configuration can be improved to address these challenges. It identifies problems with established criteria for detecting viruses and responsibilities for cleanup, and advocates for more adaptive approaches.
![Traditional Database V.S. High
Granularity Database
struct vxdb struct tgvxdb
{ {
char name[255]; char name[255];
char fword[4]; char fword[4];
char offset1[4]; char offset1[4];
char crc1[8]; char crc1[8];
char offset2[4]; char offset2[4];
char crc2[8]; char crc2[8];
… …
}; int vxattribute ;
};
Antiy Labs www.antiy.net](https://image.slidesharecdn.com/embedded-av-engine-120806030706-phpapp02/75/Embeddable-Antivirus-engine-with-high-granularity-43-2048.jpg)