Embed presentation
Download to read offline
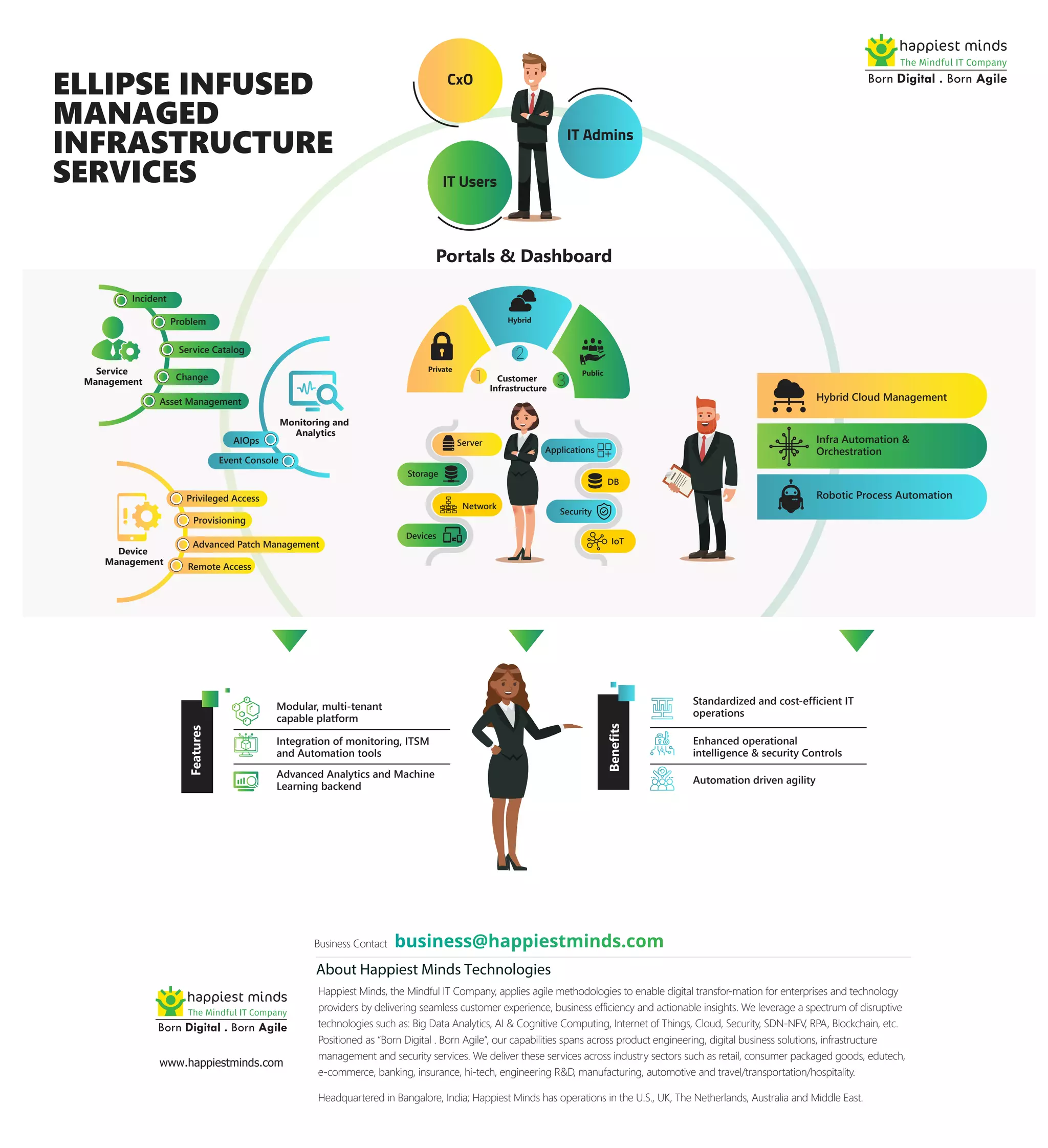

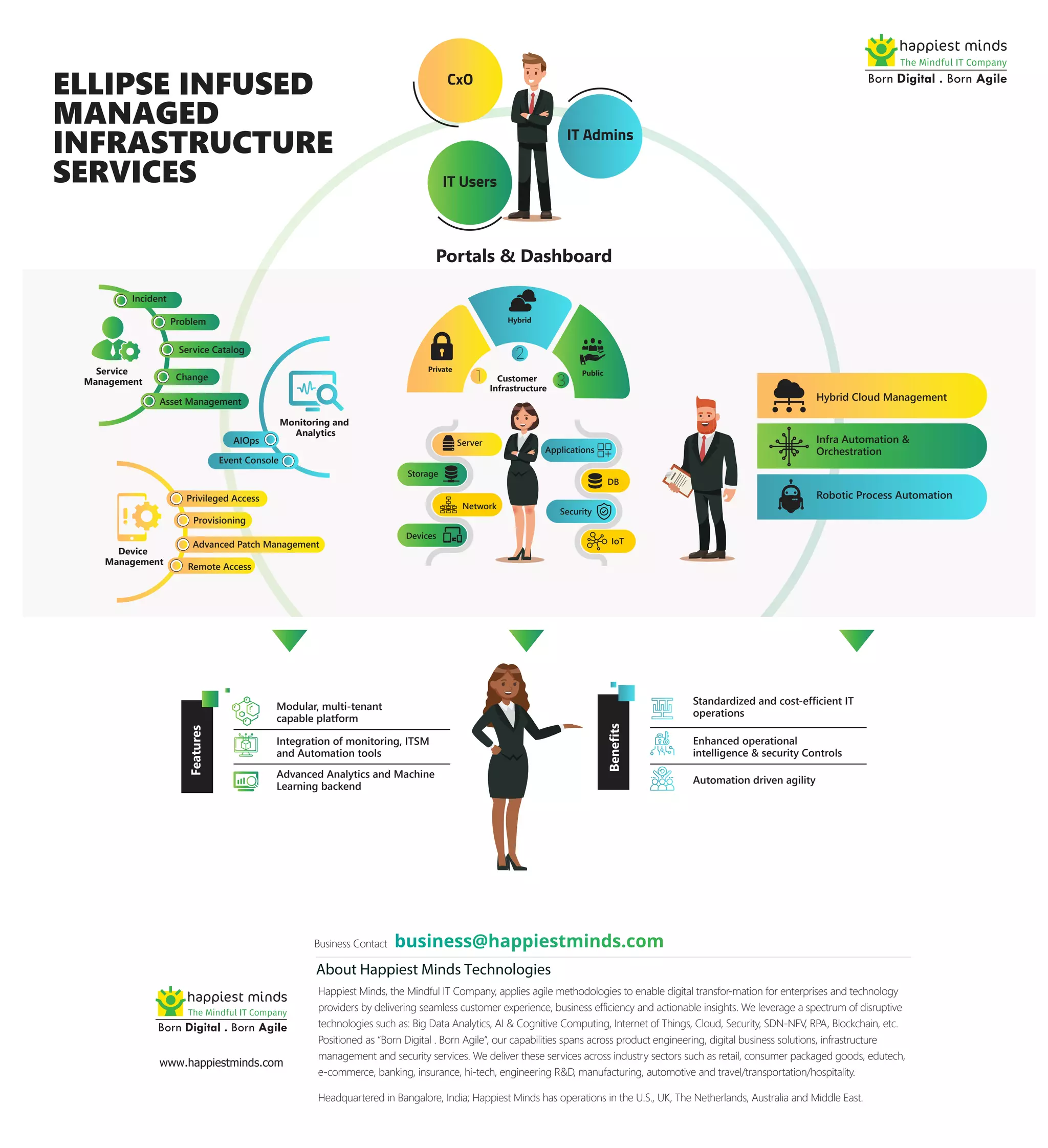
The document describes Ellipse Infused Managed Infrastructure Services, which provides a modular, multi-tenant platform that integrates monitoring, IT service management, and automation tools. It offers advanced analytics, machine learning, standardized and cost-efficient IT operations, enhanced security controls, and automation-driven agility. The platform includes portals and dashboards, service management, monitoring and analytics, asset management, device management, and advanced patch management for managing hybrid cloud infrastructure including servers, storage, networks, databases, IoT devices and applications.