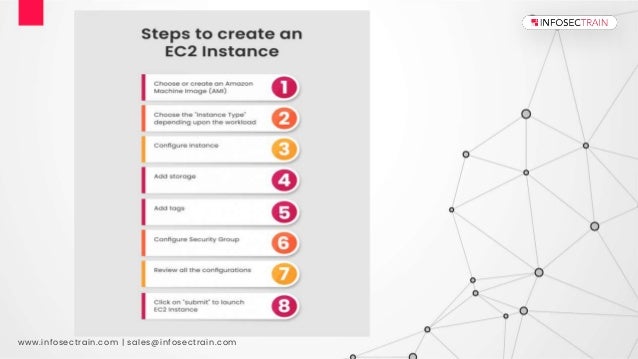
Amazon EC2 (Elastic Compute Cloud) is a web service that allows users to rent virtual machines, enabling flexible and scalable cloud computing without the need for physical hardware. It simplifies infrastructure management and offers various components like virtual private clouds, instances, and storage solutions, all on a pay-as-you-go pricing model. Infosectrain offers training programs to help individuals learn about AWS EC2 and its integration with other AWS services.