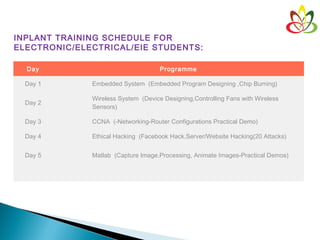
This document provides information about Venkatesan Prabu Jayakantham (Venkat), the Managing Director of KAASHIVINFOTECH, a software company in Chennai. It outlines Venkat's experience in Microsoft technologies and certifications. It also describes KAASHIVINFOTECH's inplant training programs for students in fields like engineering, electronics, and mechanical. The training focuses on developing technical skills through hands-on demos and projects.