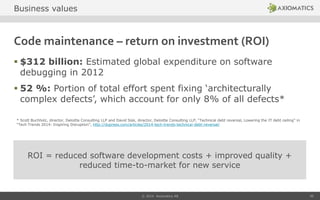
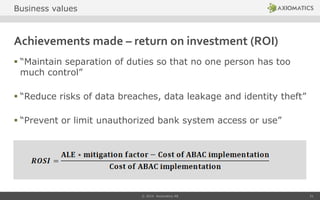
The document discusses the business case for Attribute Based Access Control (ABAC), highlighting its advantages over legacy access controls in dynamic and collaborative environments. It emphasizes ABAC's ability to enhance security, enable efficient information sharing, and ensure compliance with regulatory standards. The presentation also outlines the return on investment (ROI) from implementing ABAC and its role in reducing risks, improving software development processes, and maintaining governance.




![Example from NIST report
“This flexibility [of ABAC] provides the greatest breadth of subjects to access
the greatest breadth of objects without specifying individual relationships
between each subject and each object”
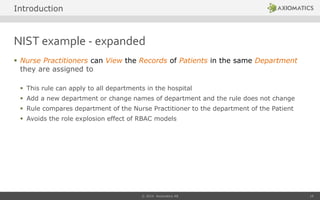
Nurse Practitioners in the Cardiology Department can View the Records of
Heart Patients
Variables in the policy language enable very efficient policy structures – reducing the
maintenance load
Management of heart patient records is part of the business application – not an IT
function
Multiple attributes must be available for policy evaluation – either as part of the access
request or retrieved from source
© 2014 Axiomatics AB 9
Introduction](https://image.slidesharecdn.com/abacbuscasedraftfinalversion-140404051456-phpapp02/85/Do-you-have-a-business-case-for-Attribute-Based-Access-Control-ABAC-9-320.jpg)



![Using ABAC to overcome the RBAC weakness
Solution:
To authorize a Service Entry and Release, enforce the following XACML rule:
PERMIT Service Entry and Release for users with Cost Center Signature
Authority for Purchase Orders of their own Cost Centers providing they were
not previously involved in the creation, editing or approval of the related
Purchase Order or the corresponding Vendor or Service provider account.
Result:
Multiple attributes combined [cost center, PO and Vendor approver etc.] –
not just the role of the user – are considered to minimize the risk
(in our example the risk of individuals releasing service entries for their own
fraudulent purchase orders.)
© 2014 Axiomatics AB 20
Business challenge](https://image.slidesharecdn.com/abacbuscasedraftfinalversion-140404051456-phpapp02/85/Do-you-have-a-business-case-for-Attribute-Based-Access-Control-ABAC-20-320.jpg)
![Achievements made – return on investment (ROI)
“[…] is a multi-national company and must comply with
financial regulations in multiple jurisdictions. […]
Application-external authorization must ensure applications
at all times comply with changing and country specific
regulations.”
© 2014 Axiomatics AB 25
ROI=Avoiding fines, avoiding reputational damage
Business values](https://image.slidesharecdn.com/abacbuscasedraftfinalversion-140404051456-phpapp02/85/Do-you-have-a-business-case-for-Attribute-Based-Access-Control-ABAC-25-320.jpg)