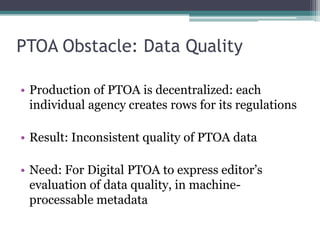
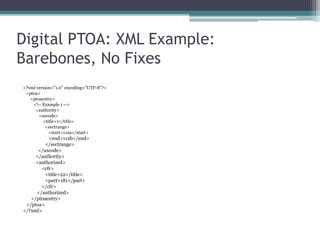
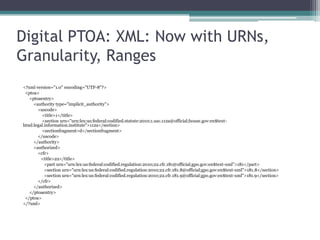
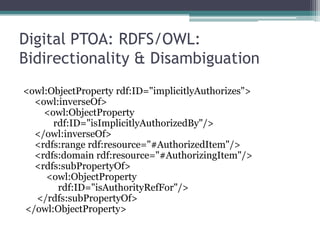
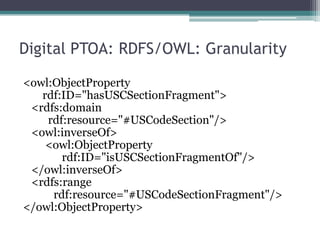
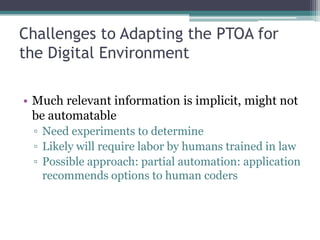
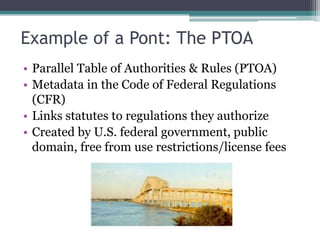
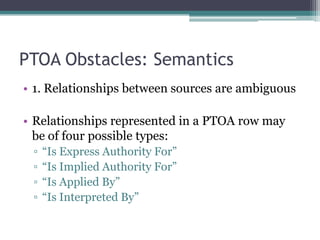
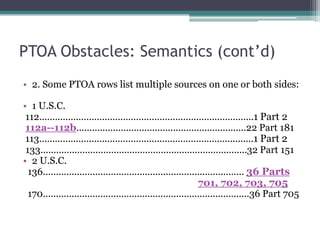
The document discusses adapting the Parallel Table of Authorities (PTOA) from the U.S. Code of Federal Regulations for use in a digital environment. The PTOA currently exists as specialized legal metadata that links statutes to related regulations but has several obstacles to being processed by software, including ambiguous relationships, lack of granularity, directionality issues, and inconsistent data quality. The document proposes addressing these issues by expressing the PTOA in XML or RDF/OWL to make the relationships explicit and machine-readable in order to enable new uses and applications of the PTOA in the digital domain.
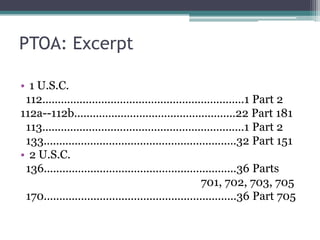
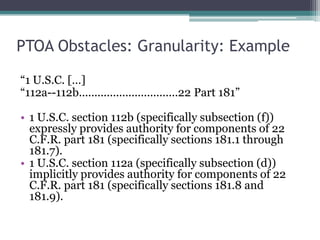
![PTOA Obstacles: Granularity: Example“1 U.S.C. […]“112a--112b................................22 Part 181”1 U.S.C. section 112b (specifically subsection (f)) expressly provides authority for components of 22 C.F.R. part 181 (specifically sections 181.1 through 181.7). 1 U.S.C. section 112a (specifically subsection (d)) implicitly provides authority for components of 22 C.F.R. part 181 (specifically sections 181.8 and 181.9).](https://image.slidesharecdn.com/dgopresentationrichardsfinal-110615090911-phpapp01/85/Bruce-T-R-and-Richards-R-C-2011-Examples-of-Specialized-Legal-Metadata-Adapted-to-the-Digital-Environment-from-The-U-S-Code-of-Federal-Regulations-18-320.jpg)
![PTOA Obstacles: DirectionalityIn PTOA, retrieval and discovery can only occur in one direction: from statute to regulation1 U.S.C. […] 112a--112b................................22 Part 181](https://image.slidesharecdn.com/dgopresentationrichardsfinal-110615090911-phpapp01/85/Bruce-T-R-and-Richards-R-C-2011-Examples-of-Specialized-Legal-Metadata-Adapted-to-the-Digital-Environment-from-The-U-S-Code-of-Federal-Regulations-20-320.jpg)