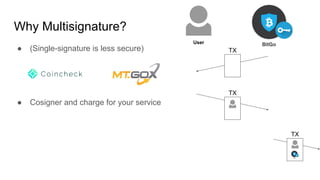
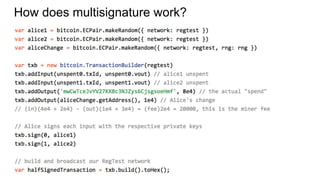
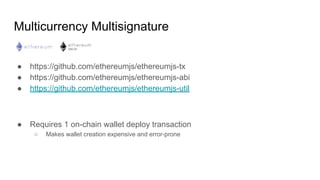
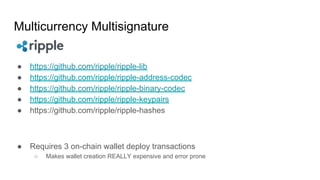
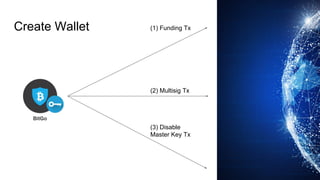
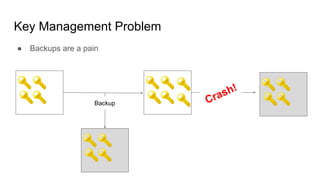
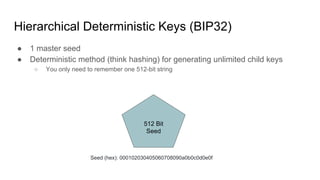
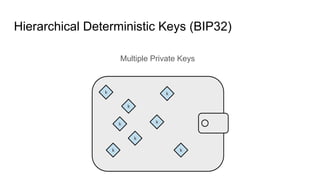
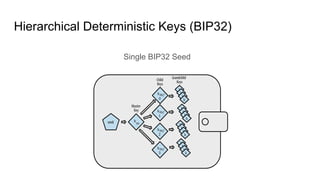
The document discusses the development of a multicurrency, multisignature wallet, emphasizing the security advantages of multisignature over single-signature wallets. It outlines the complexities involved in wallet creation, particularly the expensive and error-prone nature of on-chain transactions required for multisignature setup. Key management is highlighted as a critical issue, advocating for the use of hierarchical deterministic keys (BIP32) to simplify backups and enhance security.