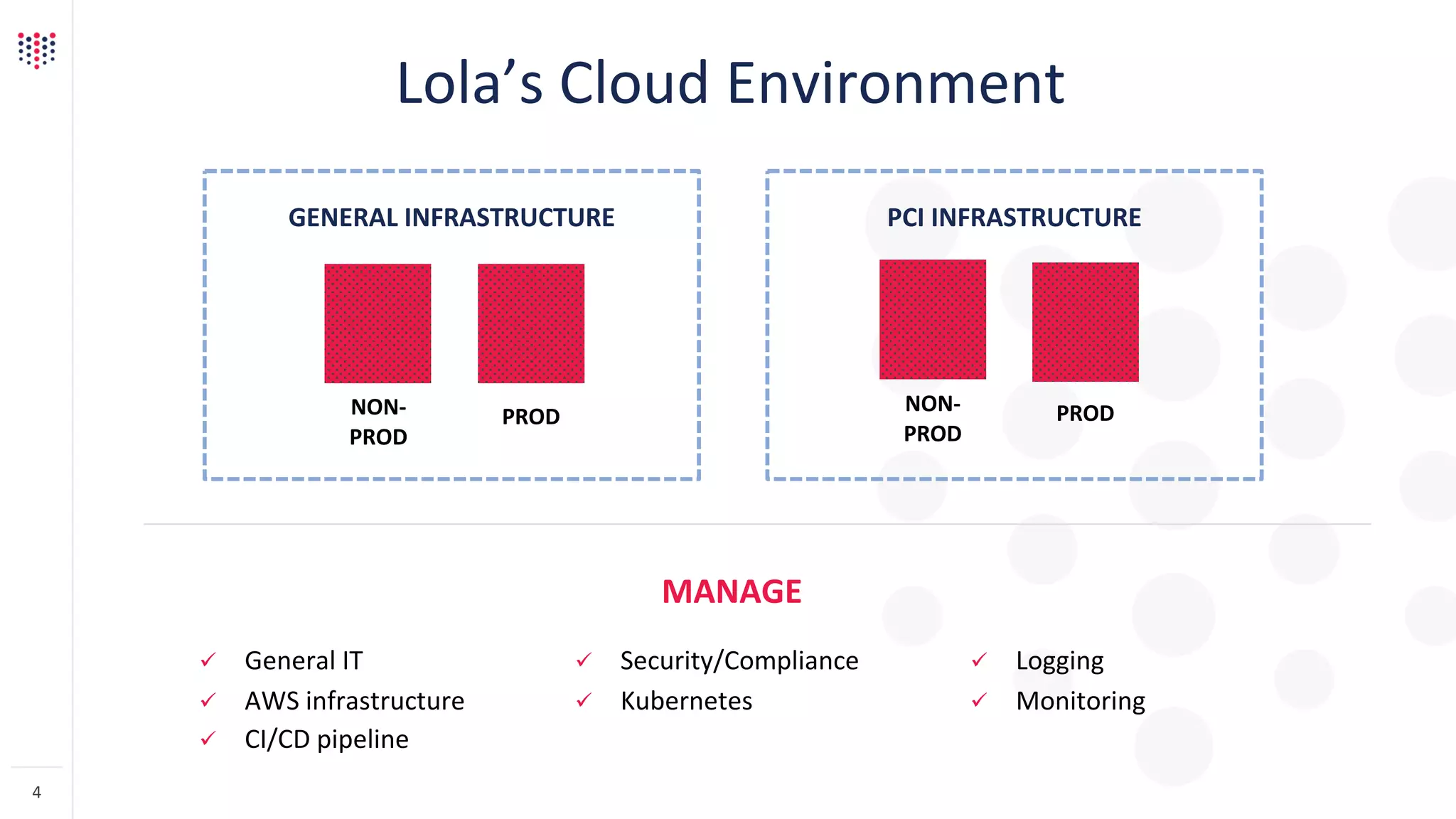
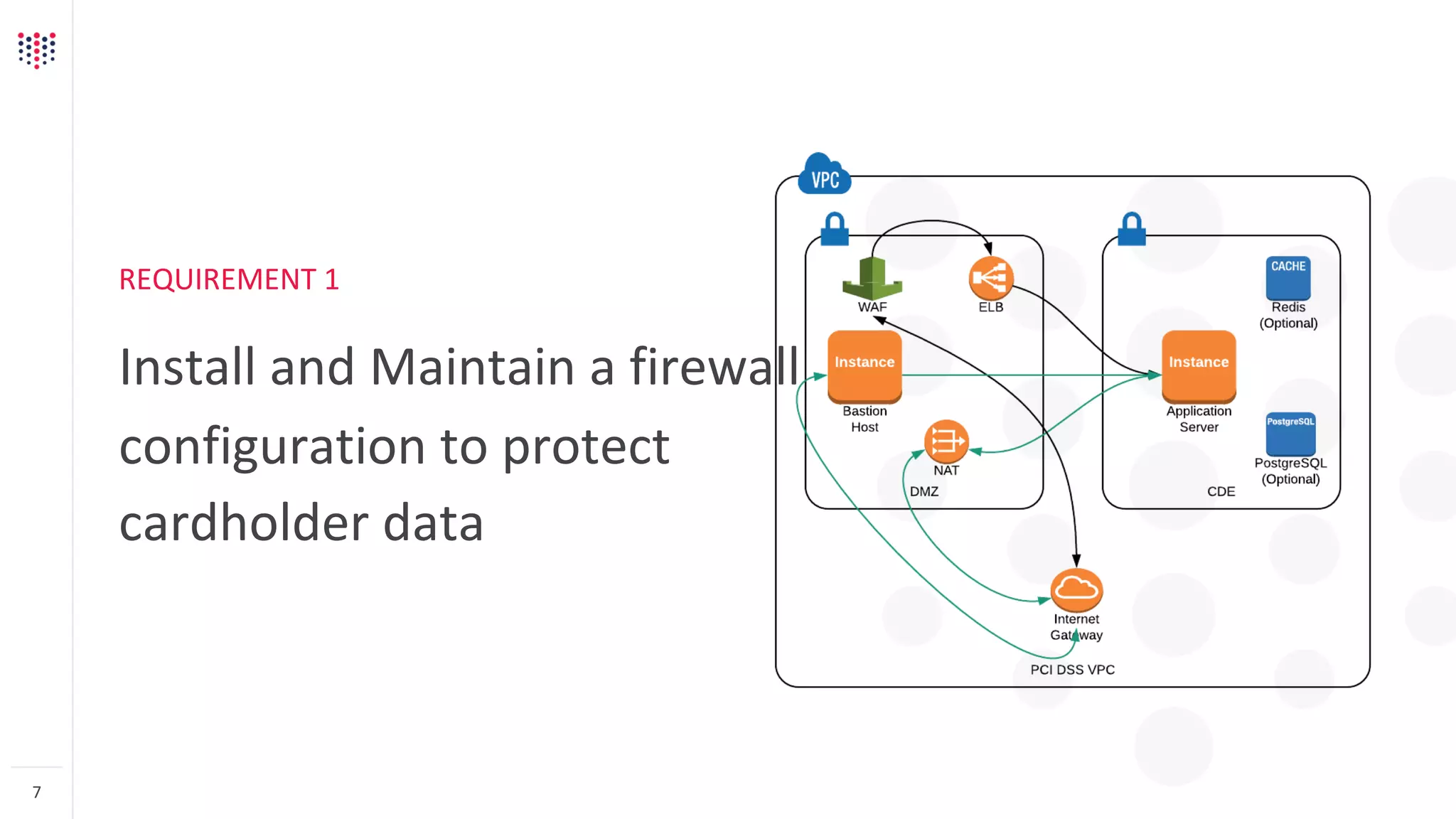
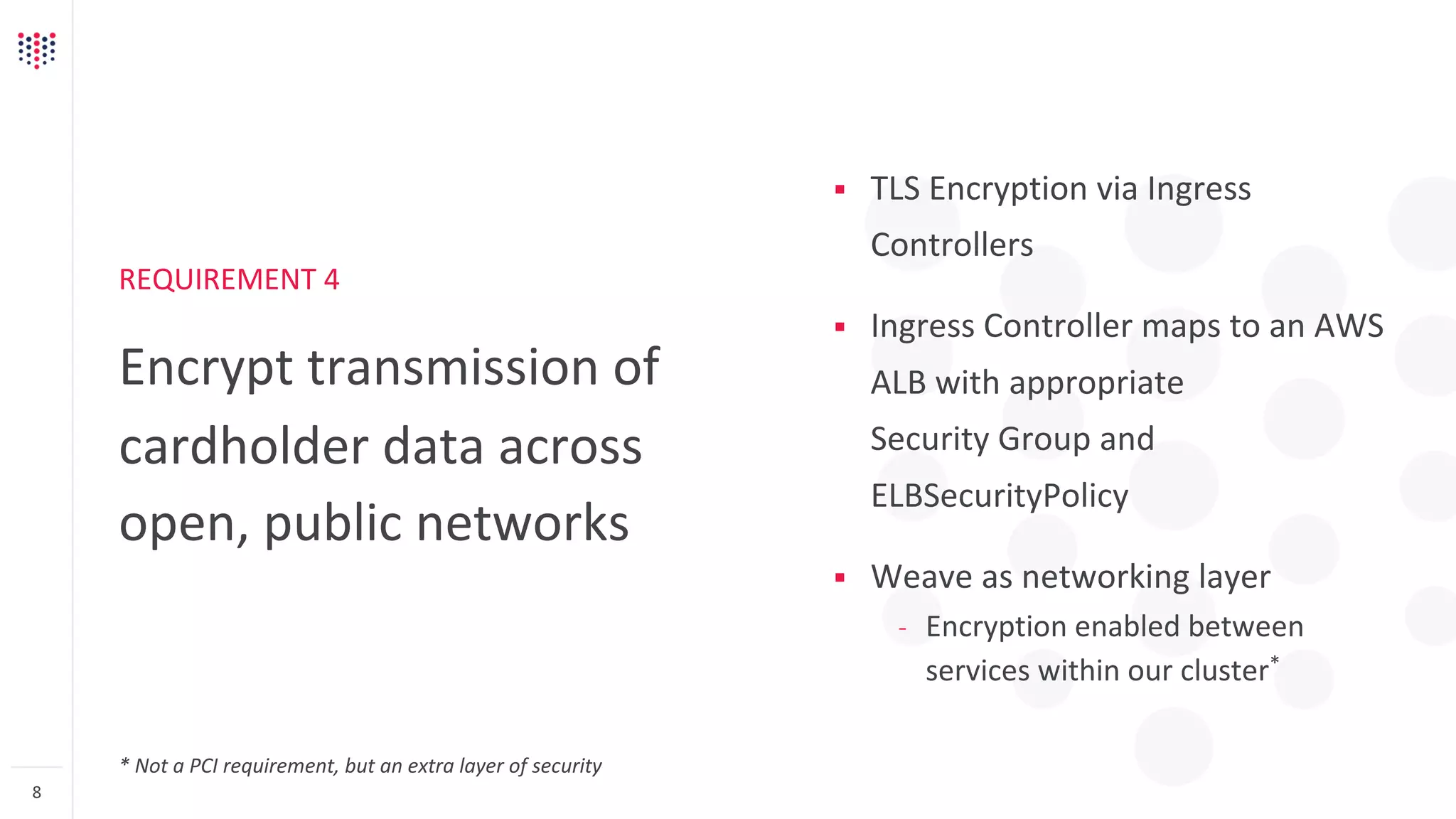
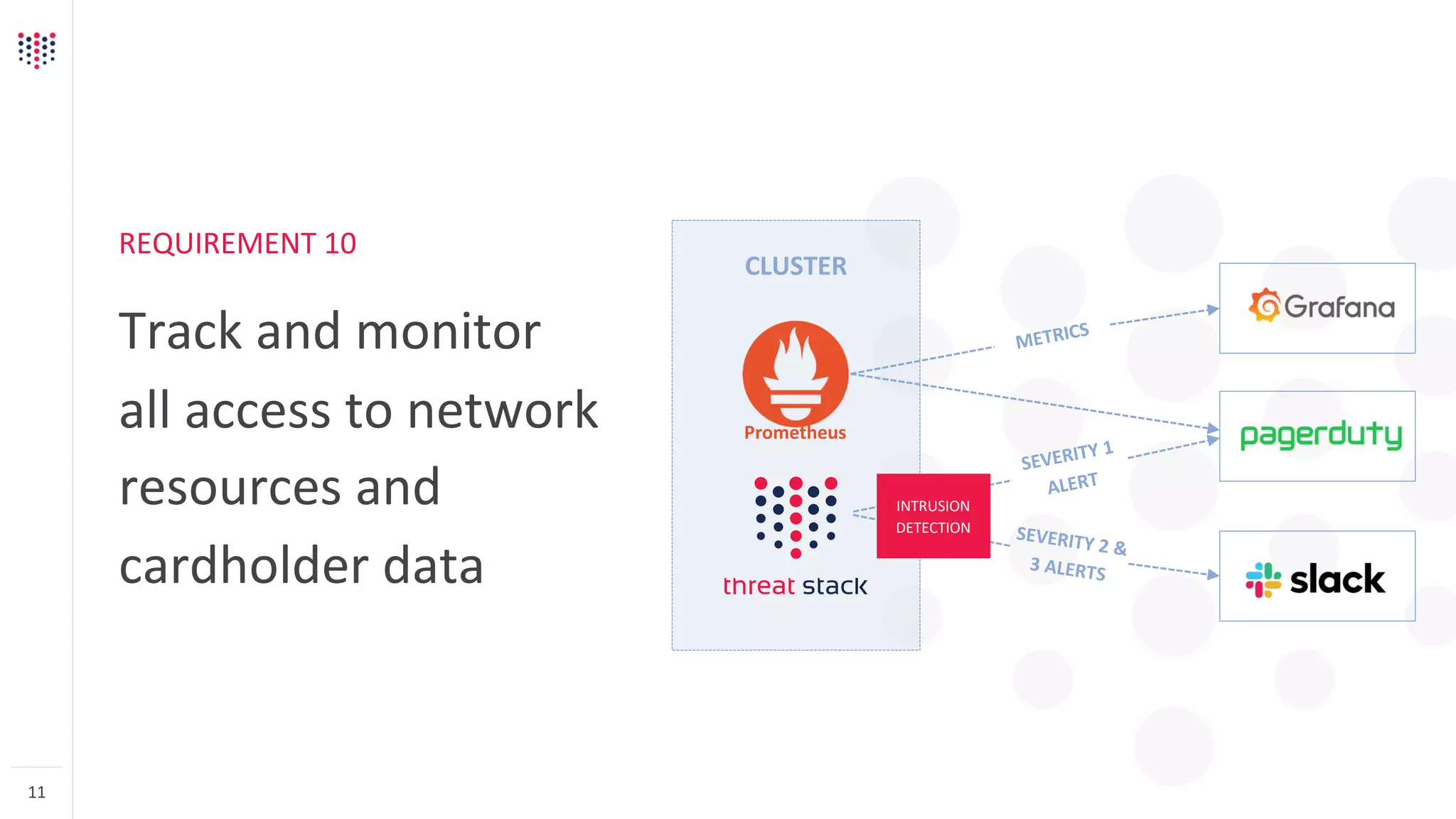
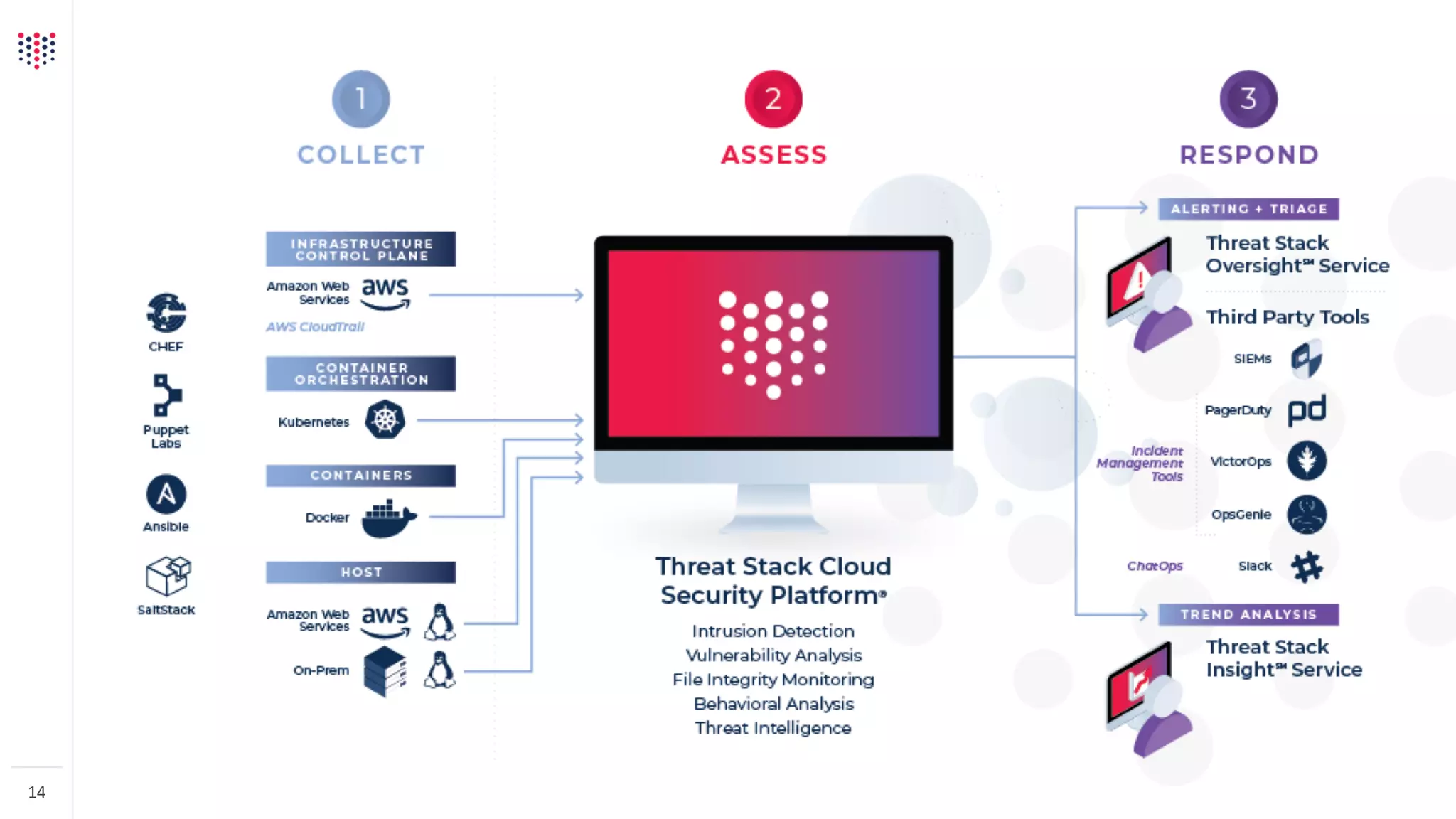
This document discusses Lola's deployment of compliant Kubernetes to meet PCI DSS requirements. Lola stores credit card details on behalf of users but does not directly process payments, requiring Level 1 PCI compliance. It outlines how Lola uses technologies like TLS encryption with Ingress controllers, IAM authentication for Kubernetes, and Prometheus for cluster monitoring to meet requirements for firewalls, encryption, secure systems, and access control. The document advises engaging auditors technically rather than treating Kubernetes as a black box, and leveraging open source tools and communities for pre-built applications to simplify compliance tasks like authentication, monitoring, and logging.