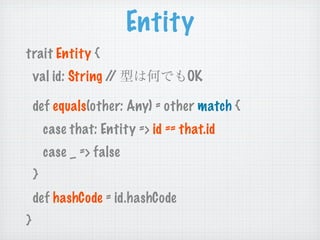
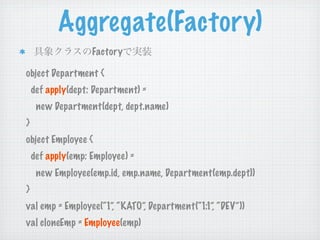
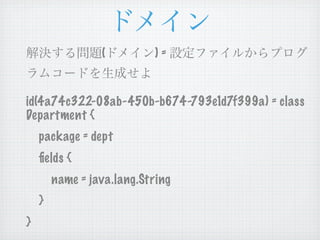
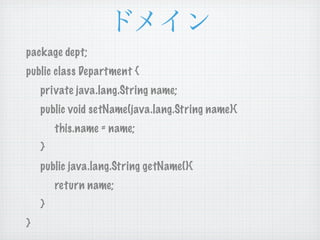
The document includes various Scala programming examples, demonstrating the language's syntax and features such as case classes, methods, and collection operations. It also covers topics like entity and repository patterns, cloning, and functional programming aspects like higher-order functions and patterns matching. The examples illustrate the creation and manipulation of classes, including user-defined types and their interactions.
![Hello, World!!
object HelloWorld{
def main(args: Array[String]):Unit = {
println(“Hello, World!!”)
}
}](https://image.slidesharecdn.com/dddscala-110410065033-phpapp02/85/ddd-scala-7-320.jpg)

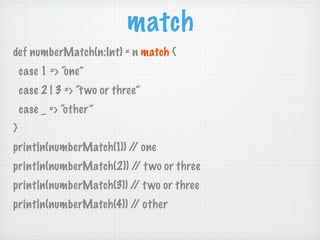
![match
val pattern = """([a-z]+)""".r case Array(1,2,3) => println(“
def matchTest(word: Any) = word 1,2,3 ”)
match {
case _ => throw new
case “ABC” => println(“ABC ”) IllegalArgumentException
case pattern(s) => println(" }
= "+s) matchTest(“ABC”) / ABC
/
case s: String => println(“ matchTest("aaaa") // =
= (%s)”.format(s)) (aaaa)
case n: Int if (n >= 2) => println(“2 matchTest(10) / 2
/
”)
matchTest(Array(1,2,3)) //
1,2,3](https://image.slidesharecdn.com/dddscala-110410065033-phpapp02/85/ddd-scala-19-320.jpg)



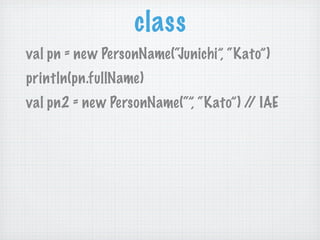
![ValueObject Builder
case class PersonName(firstName: String, lastName:
String)
class PersonNameBuilder extends
ValueObjectBuidler[PersonName, PersonNameBuilder] { ... }
VO
val personName1 = new
PersonNameBuilder().withFirstName("Junichi").withLastNa
me("Kato").build
val personName2 = new
PersonNameBuilder().withLastName(lastName.toUpperCase
).build(personName1)](https://image.slidesharecdn.com/dddscala-110410065033-phpapp02/85/ddd-scala-36-320.jpg)
![Aggregate(Cloneable)
@cloneable }
class Department(val id: String, var name: override def clone = { / (4)
/
String) extends Entity {
val result =
override def clone = super.clone.asInstanceOf[Employee]
super.clone.asInstanceOf[Department]
result.dpt = dpt.clone
}
}
@cloneable
}
class Employee(val id:String, var
val dept = Department(“1:1”, “DEV”)
name:String, _dpt: Department) extends
Entity { val emp = Employee(“1”, “KATO”, dept) / (1)
/
private var dpt = _dpt.clone / (1)
/ dept.name = “SALES”
def dept = dpt.clone / getDept
/ (2) val dept = emp.dept / (2)
/
def dept_= (value: Deaprtment) { // dept.name = “SALES”
setDept emp.dept = Department(“1:1”, “SALES”) / (3)
/
dpt = value.clone / (3)
/ val cloneEmp = emp.clone / (4)
/](https://image.slidesharecdn.com/dddscala-110410065033-phpapp02/85/ddd-scala-40-320.jpg)
![Aggregate(clone)
clone Mix-in
@cloneable
trait EntityCloneable[T <: Entity] {
this: Entity =>
override def clone: T =
super.clone.asInstanceOf[T]
}](https://image.slidesharecdn.com/dddscala-110410065033-phpapp02/85/ddd-scala-41-320.jpg)
![Aggregate(clone)
class Employee
(val id: String,
var name: String)
extends Entity with
EntityCloneable[Employee]
val emp = Employee(“1”, “Kato”)
val cloneEmp = emp.clone](https://image.slidesharecdn.com/dddscala-110410065033-phpapp02/85/ddd-scala-42-320.jpg)
![Repository
trait EntityResolver[T <: Entity] extends Iterable[T]
{
def resolve(id: String): T
def apply(id: String) = resolve(id)
def contains(id: String): Boolean = exists(_.id == id)
def contains(entity: T): Boolean = exists(_ == entity)
}](https://image.slidesharecdn.com/dddscala-110410065033-phpapp02/85/ddd-scala-44-320.jpg)
![Repository
class EmployeeResolver extends val er = new EmployeeResolver
EntityResolver[Employee] {
val employee = er.resolve(id)
private val employees =
val employee = er(id) / er.apply
/
Map(“1” -> Employee(“1”,
-> resolve
“KATO”, Department(“1:1”,
“DEV”))) val employee = er.contains(id)
def resolve(id: String) = val exists = er.exists(_.name ==
employees(id) “KATO”)
def iterator = val employees =
employees.map(e => er.filter(_.name.startWith(“K”))
e._2.clone).iterator
er.foreach(println)
}](https://image.slidesharecdn.com/dddscala-110410065033-phpapp02/85/ddd-scala-45-320.jpg)
![Repository
trait Repository[T <: Entity] extends
EntityResolver[T] {
def store(entity: T)
def update(identifier: Identifier, entity:T) =
store(entity)
def delete(identity: Identifier)
def delete(entity: T)
}](https://image.slidesharecdn.com/dddscala-110410065033-phpapp02/85/ddd-scala-46-320.jpg)
![Repository
class EmployeeRepository / resolve, iterator ...
/
extends
Repository[Employee] { }
private val employees = val er = new
collection.mutalble.Map.emp EmployeeRepository
ty[String, Employee] val emp = Employee(id,
def store(emp: Employee) = “KATO”, Department(“DEV))
employees += (emp.id -> emp) er.store(emp)
def delete(id: String) = er(id) = emp
employee -= emp.id
er.delete(id)
def delete(emp: Employee) =
delete(emp.id) er.delete(emp)](https://image.slidesharecdn.com/dddscala-110410065033-phpapp02/85/ddd-scala-47-320.jpg)
![codegen -h
codegen -c sample.config -t template -e export
codegen -c [4a74c322-08ab-450b-
b674-793e1d7f399a]@sample.config -t
template -e export](https://image.slidesharecdn.com/dddscala-110410065033-phpapp02/85/ddd-scala-52-320.jpg)
![ClassMeta Entity
package codegen.domain
class ClassMeta
(@BeanProperty val identifier: Identifier, @BeanProperty val name:
String,
val packageName: Option[String], val fieldMetas: List[FieldMeta])
extends Entity {
override def toString: String = "ClassMeta(%s, %s, %s,
%s)".format(identifier, name, packageName, fieldMetas)
def getPackageName(): String = if (packageName.isEmpty) null else
packageName.get
def getFieldMetas(): java.util.List[FieldMeta] = fieldMetas.asJava
}](https://image.slidesharecdn.com/dddscala-110410065033-phpapp02/85/ddd-scala-54-320.jpg)
![ClassMeta Object
object ClassMeta {
def apply(identifier: Identifier, name: String, packageName: Option[String],
fieldMetas: List[FieldMeta]) =
new ClassMeta(identifier, name, packageName, fieldMetas)
def apply(name: String, packageName: Option[String], fieldMetas:
List[FieldMeta]): ClassMeta =
apply(Identifier(), name, packageName, fieldMetas)
def apply(classMeta: ClassMeta): ClassMeta =
apply(classMeta.identifier, classMeta.name, classMeta.packageName,
classMeta.fieldMetas)
def unapply(classMeta: ClassMeta) =
Some(classMeta.identifier, classMeta.name, classMeta.packageName,
classMeta.fieldMetas)
}](https://image.slidesharecdn.com/dddscala-110410065033-phpapp02/85/ddd-scala-55-320.jpg)
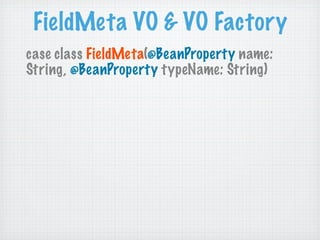
![ClassMetaRepository
package codegen.domain
class ClassMetaRepository(configSource: BufferedSource)
extends EntityResolver[ClassMeta] {
private val classMetas = new
ModelParser().parse(configSource)
private val classMetaMap = classMetas.map(classMeta =>
(classMeta.identifier, classMeta)).toMap
def iterator: Iterator[ClassMeta] =
classMetaMap.map(classMeta => ClassMeta(_._2)).iterator
def resolve(identifier: Identifier): ClassMeta =
ClassMeta(classMetaMap(identifier))
}](https://image.slidesharecdn.com/dddscala-110410065033-phpapp02/85/ddd-scala-57-320.jpg)
![CodeGenSer vice
package codegen.domain val exportClassDir =
getExportClassDir(classMeta)
object CodeGenSer vice{
exportClassDir.mkdirs
def generate(exportDir: File, templateDir: File,
classMetas: List[ClassMeta], using(new FileWriter(new
File(exportClassDir, classMeta.name + ".java"))) {
beginHandler: Option[(ClassMeta) => Unit],
fileWriter =>
endHandler: Option[(ClassMeta) => Unit] ) = {
template.process(rootMap.asJava,
val configuration = new Configuration fileWriter);
fileWriter.flush();
configuration.setDirectoryForTemplateLoading(te
mplateDir) } / using
/
val template = / ...
/
configuration.getTemplate("java.ftl")
} / foreach
/
classMetas.foreach {
}
classMeta =>
/ ...
/
/ ...
/
}
val rootMap = Map("classMeta" ->
classMeta)](https://image.slidesharecdn.com/dddscala-110410065033-phpapp02/85/ddd-scala-58-320.jpg)
![Application
package codegen.application getExportDir(parameters),
object Application extends Logging { getIdList(parameters))
def main(args: Array[String]) { }
try {
val commandLine = new } catch {
CommandLineParser().parse(args.mkSt
ring(" ")) case e:
CommandLineParseException =>
commandLine match { println("
case Help() => println("""-c ")
[[id1,id2]@]file.config [-t templateDir]
[-e exportDir]""") }
case parameters: Parameters => }
generate(getConfigFile(parameters),
getTemplateDir(parameters), }](https://image.slidesharecdn.com/dddscala-110410065033-phpapp02/85/ddd-scala-59-320.jpg)
![Application
private def generate(configFile: File, CodeGenSer vice.generate(exportDir, templateDir,
targets,
templateDir: File,
Some({
exportDir: File,
c => info("id(%s) : class %s
ids: List[String]) {
".format(c.identifier.value, c.name))
info("
= %s, = %s, }),
= %s".format(configFile, templateDir, Some({
exportDir)) c => info("id(%s) : class %s
val repos = new ".format(c.identifier.value, c.name))
ClassMetaRepository(Source.fromFile(configFile))
}))
val targets = ids match {
info(" ")
case Nil => repos.toList
case xs => xs.map { } catch {
e => repos.resolve(Identifier(e)) case e: Exception => error("
} ", e)
} }
try { }](https://image.slidesharecdn.com/dddscala-110410065033-phpapp02/85/ddd-scala-60-320.jpg)