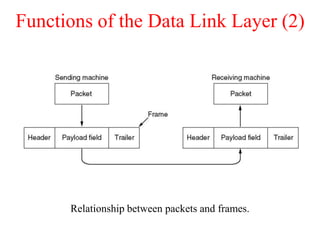
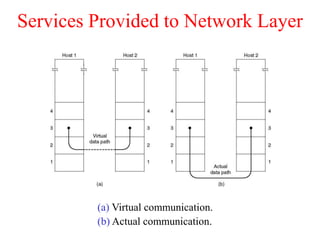
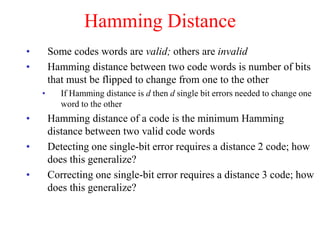
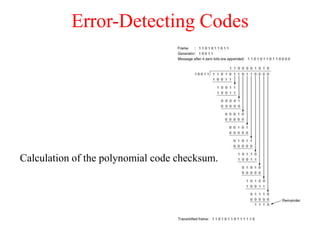
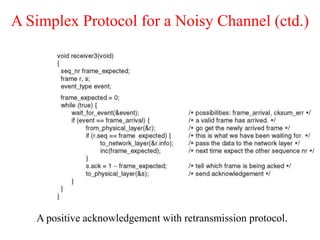
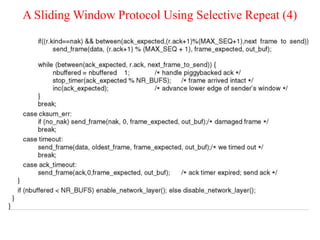
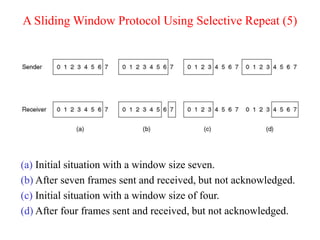
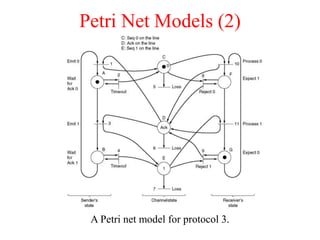
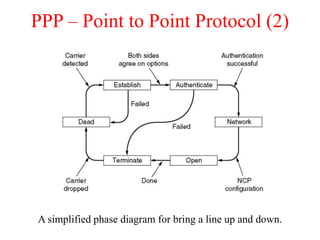
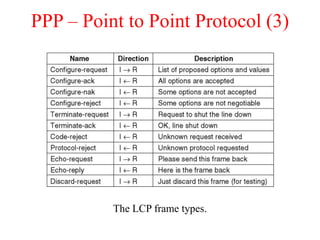
The document summarizes key concepts about the data link layer, including the services it provides to the network layer, such as error control and flow control. It describes functions of the data link layer like framing, error detection, and flow control. Specific data link protocols are also discussed, including HDLC, PPP, and protocols used for Ethernet and the Internet. Error detection techniques like parity checks and CRC are explained. Sliding window protocols including stop-and-wait, go-back-N, and selective repeat are covered.