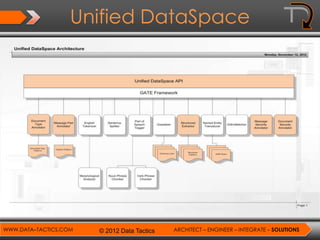
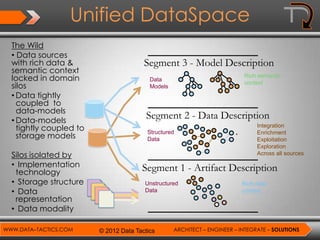
Data Tactics provides systems engineering and integration services focused on big data architecture and unified data spaces. They have experience architecting solutions managing petabytes of data across multiple security enclaves and domains. Their unified data space approach aims to break down data silos by incorporating rich semantic context and metadata across structured, unstructured, and multi-modal data sources to enable integration, enrichment, and exploration of data.



![Data Description Framework
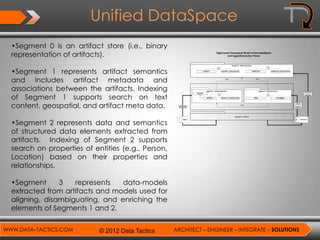
• DDF – looks at data in the following ways
– Mention: A chunk of data, either physically located within a tangible artifact,
or contained within an analyst’s mind
• “Washington” at offset x in file Y
– Sign: A representation of all disambiguated mentions that are identical except
for their indexicality
• E.g., “Washington”
– Concept: An abstract idea, defined explicitly or implicitly by a source data-
model
• E.g., City, Person, Name, Address, Photo
– Predicate: An abstract idea used to express a relationship between “things”
• E.g., isCity, isPerson, hasName, hasAddress, hasPhoto
– Term: A disambiguated sign abstracted from the source artifact or asserting
analyst
• E.g., Washington Person; Washington Location
– Statement: Encodes a binary relationship between a subject (term) and an
object mediated by a predicate
• E.g.,[Washington, Person] hasPhoto [GeorgeWashingtonImage.jpg]
WWW.DATA–TACTICS.COM © 2012 Data Tactics ARCHITECT – ENGINEER – INTEGRATE – SOLUTIONS](https://image.slidesharecdn.com/datatacticsunifieddataspacearchitectureanddescription-130305093631-phpapp02/85/Data-Tactics-Unified-Dataspace-Architecture-and-Description-10-320.jpg)