Cyber Security for Oil and Gas
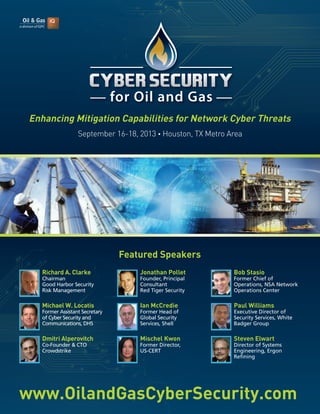
- 1. www.OilandGasCyberSecurity.com September 16-18, 2013 • Houston, TX Metro Area Richard A. Clarke Chairman Good Harbor Security Risk Management Michael W. Locatis Former Assistant Secretary of Cyber Security and Communications, DHS Dmitri Alperovitch Co-Founder & CTO Crowdstrike Jonathan Pollet Founder, Principal Consultant Red Tiger Security Ian McCredie Former Head of Global Security Services, Shell Mischel Kwon Former Director, US-CERT Bob Stasio Former Chief of Operations, NSA Network Operations Center Paul Williams Executive Director of Security Services, White Badger Group Steven Elwart Director of Systems Engineering, Ergon Refining Enhancing Mitigation Capabilities for Network Cyber Threats Featured Speakers
- 2. Who you will meet: Security managers, IT strategy implementers, and industry partners will gather to network, share best practices and explore potential paths to mitigate the threat of energy- focused attacks from cyber adversaries. Dear Colleague, As the Obama administration and other key figures in the government continue to stress the critical nature of cyber security and the dangers/implications of cyber attacks, critical industries like energy are seeking to update their cyber threat mitigation efforts in regards to network security. With the range and breadth of cyber threats on the rise, many of which are specifically targeting energy facilities, operations and companies, this urgent issue must be addressed at the highest levels. Because recent attacks ranging from Operation Night Dragon to Shamoon have redefined the security reality for the energy sector, Oil & Gas iQ’s Cyber Security for Oil and Gas conference serves as the central meeting point for oil and gas network security personnel who strive to significantly impact the landscape of cyber security in their organizations and sector at-large. At this event you will have the unique opportunity to interact and network with senior-level professionals with the following expertise: • Tactical Cyber Security Planning • Data Management and Security • Information Analysis and Dissemination • Critical Infrastructure Network Operations • Information Technology and Sharing • Assessing Adversary Capability and Intentions • Interagency Cooperation • Information Security • National Security • Training and Doctrine In-depth briefings and presentations from Washington insiders including Richard Clarke, Michael Locatis and Mischel Kwon will give you the latest on current government initiatives targeting cybersecurity. Understand the evolving nature of this cyber threat as it pertains to the oil and gas industry and operations specifically through comprehensive analysis of attacks and adversaries by leading cybersecurity experts such as Dmitri Alperovitch, Adam Meyers, Bob Stasio and Jonathan Pollet. These cybersecurity specialists will address the rise of cyber attacks against the energy sector, the evolution of the cyber threat from random hacking to advanced persistent threats, the issues associated with fighting a nation-state adversary with unlimited funding and resources, and the future of cyber security for energy network infrastructures. You will also be briefed on sector-wide outreach and partnership initiatives by your peers who are working to promote the energy sector’s cybersecurity interests and raise awareness on this key issue at the sector level. Don’t miss the chance to take part in this exclusive discussion with key leaders and experts from the oil and gas sector, policy administration, and cyber security technology and innovations community. Reserve your place as a part of this unique event by calling 1.800.882.8684 or visiting www.OilandGasCyberSecurity.com! I look forward to welcoming you to this exciting event, Saxon H. Burke Lead Producer, Oil & Gas iQ 2 Creating Cyber ‘Surgeons’: Thinking Like the Adversary September 16-18, 2013 Houston, TX Metro Area ‘Cyber Warriors’ are unique, highly-trained individuals, who’s skill set is honed on how cyber adversaries operate. Like surgeons, it takes an immense amount of work and training to master the cyber profession. The following interview with Bob Stasio, Former Chief of Operations at the NSA Network Operations Center, explores the development of American ‘Cyber Soldiers’, personal experiences in ‘Ethical Hacking’, and a discussion on the need for drastic action and increased cyber security in light of ever-present and destructive threats (including April’s ‘Spamhaus’ attack). Interview questions include: • Tell us about the development of American ‘Cyber Soldiers’ – what are the goals, the aims, and the reality? • Tell us about your work as a ‘Ethical Hacker’. What does this mean, how is the intelligence applied for cyber advantage? • How easy it for hackers to bypass ‘secured networks’ in order to extract critical and confidential information? In your opinion, do enough organizations have well equipped cyber security measures in place? • With Cyber so heavily on the agenda of the federal government, we are seeing daily news alerts of cyber attacks (including the ‘Spamhaus’ Dutch attack this week) – what do cases like this highlight about the ever present and evolving nature of cyber attacks, and the need for drastic action and increased cyber security? • Software vs. human intelligence – what is your take on the value and role of each for cyber security? To read the complete interview visit www.OilandGasCyberSecurity.com www.OilandGasCyberSecurity.com • 1-800-882-8684 Why attend: Oil and Gas iQ’s Cyber Security for Oil and Gas event will bring together relevant stakeholders to discuss the most pressing cyber security issues facing the oil and gas sector. What you will hear: Presentations will examine threat trends, identify immediate and long-term needs, and reveal up-and-coming technologies for use in evolving threat environments. P.S. Don’t miss the full-day workshop on September 16 by Dmitri Alperovitch on the targeted energy sector attack, Operation Night Dragon!
- 3. ESPIONAGE AND ENERGY FOCUS DAY Monday, September 16, 2013 3www.OilandGasCyberSecurity.com • 1-800-882-8684 FACILITATOR: Dmitri Alperovitch, Co-Founder and CTO, Crowdstrike Dmitri Alperovitch is the Co-Founder and CTO of CrowdStrike Inc., leading its Intelligence, Research and Engineering teams. A renowned computer security researcher, he is a thought-leader on cybersecurity policies and state tradecraft. Prior to founding CrowdStrike, Dmitri was a Vice President of Threat Research at McAfee, where he led the company’s global Internet threat intelligence analysis. With more than a decade of experience in the field of information security, Alperovitch is an inventor of ten patented and sixteen patent-pending technologies and has conducted extensive research on reputation systems, spam detection, web security, public-key and identity-based cryptography, malware and intrusion detection and prevention. “The Obama administration plans to boost U.S. spending on computer network security, including a 21 percent increase at the Pentagon, after reports of rising cyber attacks and electronic theft of secrets linked to China.” -Bloomberg News, April 2013 Did You Know? The energy sector was the target of more than 40 percent of all reported cyberattacks on critical infrastructure networks last year, according to the Department of Homeland Security (DHS). According to cybersecurity professionals, malicious software unintentionally downloaded by offshore oil workers has incapacitated computer networks on some rigs and platforms, exposing gaps in security that could pose serious risks to people and the environment. As the number of cyber-attacks increase, realization of the financial implications of persistent cyber threats will boost cybersecurity spending in this field during the forecasted period. Spending is set to pick up considerably from 2014 onwards. ABI Research calculates that cybersecurity spending on the oil & gas critical infrastructure will reach $1.87 billion by 2018. This includes spending on IT networks, industrial control systems and data security; counter measures; and policies and procedures. 9:30 Registration and Breakfast 10:00 Uncovering Operation Night Dragon: Lessons Learned for the Energy Sector • Attack discovery methodology and process • Key exploits and hallmarks of the attack that inform the future • Why energy companies? The importance of the energy sector to hackers and nation-state adversaries 11:30 BREAK 11:45 Watching You: Espionage Intentions and Adversary Capabilities • Detecting unsophisticated but dangerous compromises • Knowing your information’s value: what is it worth to the adversary? • Once a target, always a target: waiting for the right time to attack 1:00 LUNCH 1:45 Avoiding Transfers of Wealth and Loss of Proprietary Data from Cyber Intrusions • Configuring intrusion detection systems to discover backdoors • Trojan components: what types of information they are seeking • Avoiding being compromised by the use of Remote Administration Tools (RATs) 3:00 END OF ESPIONAGE AND ENERGY FOCUS DAY 1 2 3
- 4. 4www.OilandGasCyberSecurity.com • 1-800-882-8684 7:30 Registration and Coffee 8:15 Chairperson’s Welcome & Opening Remarks 8:30 Addressing the Evolving Cyber Threat • Bridging the transition between cyber national security priorities • Threat vectors and motivations affecting global business operations • Conducting multi-discipline, all-source intelligence collections on cyber adversaries 9:15 Situational Awareness for the Energy Sector on the President’s Cyber Security Agenda • Understanding the Cyber Security Executive Order ramifications for the energy sector • Increasing situational awareness for future implementation requirements • Working with public-private coalitions on incident management and information sharing Michael Locatis Former Assistant Secretary of Cyber Security and Communications DHS 10:00 Networking Break 10:45 Identifying New Trends in Warfare: Cyber v. Kinetic • Examining homeland security in light of new warfare trends • Countering nation-state threats against private sector entities • Developing a risk profile for an energy company and the energy sector Richard A. Clarke Chairman Good Harbor Security Risk Management 11:30 Working With Washington – Cooperation and Implementation • Ensuring a flexible response via informal and informal groups from government and the private sector • How can private sector cooperation enhance IC capabilities? • Secure and effective information sharing between the government and the private sector Mischel Kwon Former Director, US-CERT Mischel Kwon & Associates 12:15 Lunch 1:15 Informing Your Organization: Key Takeaways for Educating your Boss • Preparing senior management for the effects of Washington cybersecurity focus • Strategizing the road ahead for merging known threats with your valuable Intellectual Property • Developing a way-ahead for resource allocation in terms of strategic intelligence John Felker Vice President, Cyber Programs SCI Consulting 2:00 Thinking Like the Adversary: Hacker Techniques and Tools • Extracting critical and confidential information via social engineering • Implementing back doors for long-term data acquisition • Targeting outsourced service providers for network access through trusted connections Bob Stasio Former Chief of Operations, NSA Network Operations Center 2:45 Networking Break 3:30 Understanding the Human Factor: Insider Threats and Vulnerabilities • The realities of your insider threat and the human element in securing your information • Understanding and qualifying threats and vulnerabilities from within your organization • Evaluating and designing proactive defense strategies to effectively counter the Insider Threat Michelle Moore Founder MyM Solutions 4:15 Situational Awareness: the Importance of Oil and Gas Network Monitoring Systems in Cyberspace Domains • Next generation intruder detection through more than simple scans • Benefits of monitoring systems and pitfalls to be aware of • What now? Incident management following the discovery of an extant threat Jonathan Pollet Founder/Principal Consultant Red Tiger Security 5:00 End of Main Conference Day One MAIN CONFERENCE DAY ONE Tuesday, September 17, 2013
- 5. 5www.OilandGasCyberSecurity.com • 1-800-882-8684 7:30 Registration and Coffee 8:15 Chairperson’s Opening Remarks 8:30 Hallmarks and Lessons Learned from Energy- Specific Attacks • Shamoon: intrusions directed at energy companies • Duku: Control operating systems as key focus areas for intruders • Stuxnet: Facts and lessons learned for energy systems operations managers and implementers Adam Meyers Director of Intelligence Crowdstrike 9:15 Evaluating Legal Implications of System Intrusions for Energy Companies • Post incident liability mitigation for BCP • Reasonable steps to prevent attacks and which technologies are best to document incidents • Strategizing the best approach to mitigate company exposures after an incident Scott Weber Partner Patton Boggs LLP 10:00 Networking Break 10:45 Optimizing Business Success in a Hostile Cyber Environment • Strategies for high-value target companies sharing information in an assumed compromised environment • Implementing strong policies to counterbalance weaknesses in systems and behaviors • Strategies for knowledge sharing with non-security employees involved in business negotiations Ian McCredie Former Head of Global Security Services Shell 11:30 Case Study for Energy Targeting: Operation Shady RAT and Operation Aurora • Training and doctrine for enhanced data protection through successful monitoring of common operating networks • Emerging technologies for enhanced system resilience • Leveraging Cloud technology without sacrificing network security fundamentals Dmitri Alperovitch Co-Founder and CTO Crowdstrike 12:15 Lunch 1:15 Resolving Back Doors Between Business Networks and SCADA Systems • Prioritizing network common elements and operations networks simultaneously • Supporting system security holistically through critical infrastructure tie-ins • Resolving IT priorities with the realities of operations networks to foster security measure effectiveness Sponsorship Opportunities Available Contact Marc Zamarin IDGA 1-877-886-0722 or sponsorship@idga.org 2:00 Enhancing SmartDevice Security: Protecting Critical Information in the Field • Cybercriminal capabilities and your exposure to data theft from lost mobile devices • How to build an app store that ensures a quality brand • Guidelines for building more secure smartphones using only commercial software and hardware Jeff Voas Computer Scientist US National Institute for Standards and Technology 2:45 Networking Break 3:30 Panel Session: Producing Actionable Intelligence Through Knowledge Sharing • Cyber security awareness lessons learned for avoiding operational hazards across industry • Best practices in system monitoring for same-day attack data assessment • Leveraging knowledge transfer through information sharing to better support IT security personnel Steven Elwart Director of Systems Engineering Ergon Refining Denise Anderson Vice President, Government and Cross-Sector Programs Financial Services Information Sharing and Analysis Center (FS-ISAC) 4:15 Maintaining Critical Information Fidelity in a Venture Partnership Environment • Strategizing information exchange for security-conscious business enterprises • Developing effective countermeasures against information leaks and loss • Addressing security breaches with partner companies Paul Williams Executive Director of Security Services White Badger Group 5:00 End of Main Conference Day Two MAIN CONFERENCE DAY TWO Wednesday, September 18, 2013
- 6. Web: www.OilandGasCyberSecurity.com Email: info@idga.org Phone: 1-800-882-8684 or 1-646-378-6026 Fax: 646-378-6025, 24 hours a day Mail: IDGA 535 5th Avenue, 8th Floor New York, NY 10017 Ways to Register 1 2 3 4 5 Register & Pay Register & Pay Standard by 06/28/13 by 07/26/13 Price All-Access Pass (Save $400) (Save $200) $1,252 $1,452 $1,652 Main Conference (Save $400) (Save $200) $890 $1,090 $1,290 Focus Day $775 each Dress Code: Business casual MAKE CHECKS PAYABLE TO: IDGA A $99 processing charge will be assessed to all registrations not accompanied by credit card payment at the time of registration. * CT residents or people employed in the state of CT must add 6.35% sales tax. Details for making payment via EFT or wire transfer: JPMorgan Chase Penton Learning Systems LLC dba IDGA: 162525760 ABA/Routing #: 021000021 Reference: Please include the name of the attendee(s) and the event number: 22785.001 Payment Policy: Payment is due in full at the time of registration and includes lunches and refreshments. Your registration will not be confirmed until payment is received and may be subject to cancellation. Please refer to www.idga.org/cancellation for cancellation, postponement and substitution policy Special Dietary Needs: If you have a dietary restriction, please contact Customer Service at 1-800-882-8684 to discuss your specific needs. ©2013 IDGA. All Rights Reserved. The format, design, content and arrangement of this brochure constitute a trademark of IDGA. Unauthorized reproduction will be actionable under the Lanham Act and common law principles. Location & Lodging This event will be held in the Houston, TX. As soon as a specific venue is confirmed we will post the information online. If you would like to be notified via email as soon as the information becomes available please email maria.guillen@idga.org with the following in the subject line: "Cyber Security for Oil and Gas Venue Request". Sponsorship and Exhibition Opportunities Sponsorships and Exhibits are excellent opportunities for your company to showcase its products and services to high-level, targeted decision makers attending the Cyber Security for Oil and Gas event. For sponsorship opportunities, please contact Marc Zamarin at 1-877-886-0722 or sponsorship@idga.org. * Discounts apply to registrations submitted together, at the same time. Cannot be combined with any other discount. Team Discounts+ Number of Attendees Savings of: 3 to 4 15% 5 to 6 20% 7 or more 25% 6www.OilandGasCyberSecurity.com • 1-800-882-8684 Name _____________________________________________________________________________________________________________________ Job Title ____________________________________________________________________________________________________________________ Organization ________________________________________________________________________________________________________________ Address _____________________________________________________________________________________________________________________ City _____________________________________________ State _________________ County _____________________ Zip Code ______________ Phone __________________________________________________________ Fax _________________________________________ E-Mail _____________________________________________________________________________________________________________________ Approving Manager ___________________________________________________________________________________________________________ Please register me for: K All Access K Two Day Main Conference K Workshop Only Day KPlease keep me informed via email about this and other related events. KCheck enclosed for $______________(Payable in U.S. Dollars to IDGA) KAmEx KVisa KMaster Card KDiscover KDiscover Card #_______________________________________________________________________________ Exp Date:_______/________CVM Code:______ * GROUP DISCOUNTS AVAILABLE! Contact Customer Service at 1-800-882-8684 * PLEASE PHOTOCOPY THIS FORM FOR TEAM REGISTRATIONS 22785.001/MG Yes! Please register me: REGISTRATION & VENUE