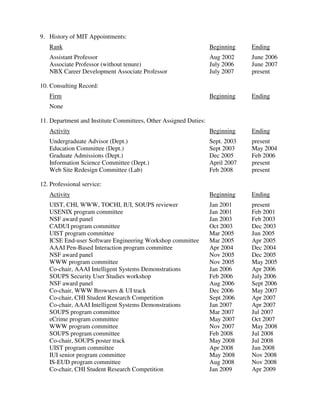
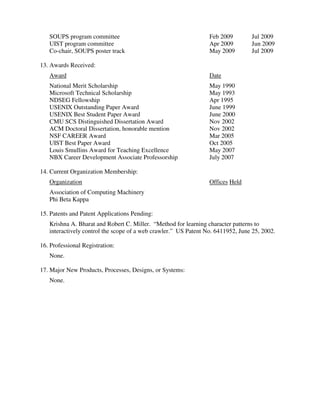
Robert C. Miller is an Associate Professor in the Department of Electrical Engineering and Computer Science at MIT. His areas of research include human-computer interaction, user interfaces, software engineering, end-user programming, and web browsing automation. He received his PhD from Carnegie Mellon University in 2002. He has received several awards for his research and teaching, including an NSF CAREER Award and the Louis Smullins Award for Teaching Excellence.