Cv bank pa
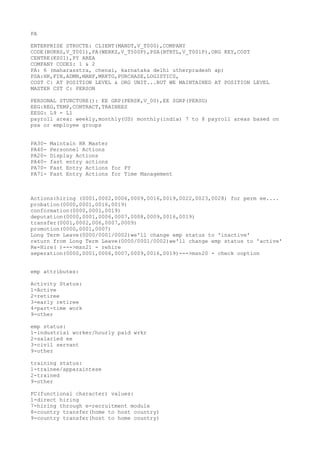
- 1. PA ENTERPRISE STRUCTE: CLIENT(MANDT,V_T000),COMPANY CODE(BUKRS,V_T001),PA(WERKS,V_T500P),PSA(BTRTL,V_T001P),ORG KEY,COST CENTRE(KS01),PY AREA COMPANY CODES: 1 & 2 PA: 6 (maharasstra, chenai, karnataka delhi utherpradesh ap) PSA:HR,FIN,ADMN,MANF,MRKTG,PURCHASE,LOGISTICS, COST C: AT POSITION LEVEL & ORG UNIT...BUT WE MAINTAINED AT POSITION LEVEL MASTER CST C: PERSON PERSONAL STURCTURE(): EE GRP(PERSK,V_00),EE SGRP(PERSG) EEG:REG,TEMP,CONTRACT,TRAINEES EESG: L9 - L1 payroll area: weekly,monthly(US) monthly(india) 7 to 8 payroll areas based on psa or employee groups PA30- Maintain HR Master PA40- Personnel Actions PA20- Display Actions PA40- fast entry actions PA70- Fast Entry Actions for PY PA71- Fast Entry Actions for Time Management Actions:hiring (0001,0002,0006,0009,0016,0019,0022,0023,0028) for perm ee.... probation(0000,0001,0016,0019) conformation(0000,0001,0019) deputation(0000,0001,0006,0007,0008,0009,0016,0019) transfer(0001,0002,006,0007,0009) promotion(0000,0001,0007) Long Term Leave(0000/0001/0002)we'll change emp status to 'inactive' return from Long Term Leave(0000/0001/0002)we'll change emp status to 'active' Re-Hire( )--->msn21 - rehire seperation(0000,0001,0006,0007,0009,0016,0019)--->msn20 - check ooption emp attributes: Activity Status: 1-Active 2-retiree 3-early retiree 4-part-time work 9-other emp status: 1-industrial worker/hourly paid wrkr 2-salaried ee 3-civil servant 9-other training status: 1-trainee/apparaintese 2-trained 9-other FC(functional character) values: 1-direct hiring 7-hiring through e-recruitment module 8-country transfer(home to host country) 9-country transfer(host to home country)
- 2. 0-other employment status: 0-withdrawn 1-inactive 2-retiree 3-active special payment status: 0-no payment 1-std payment(all regular employees) 2-special payment(ceo,director..etc) organizational key(VDSK1) role authorization structural authorization(field) Q: diff b/w transfer deputation? A:transefer is shifting the employee parmanetly to other locations of client/company deputation is shifting the employee for the specific short period of time FC functional character of step 00-for indipendent of the current function carried out 02-change 04-create 06change+ create 08-delete 10 change and delete 12-create and delete Dynamic Actions: maintained at IT, Sub type and field level.(table T588z) step indicator: P- check condition I- maintain Infotype record W- set default values when creating a new record v- ref to other step F- call routine m- send mail Screen Modification (feature p&IT) Module pool Mp000100 Variabe key Scenario:0021 should tigger after as soon as employee update his status like (marriage, children) marrital status in infotype 0002 then his spouse or children details should be mandaterly mentain because we need that info for dependent coverage... S2: As soon as we run Deputation, probation actions: 0041 date specification infotype should be triggered so tat the start date of the employee should be changed to deputation start date IT0016 should be maintained in hiring action so tat to....after the 6 months of deputation/probation completed,then he should be transfered prmanently to his current deputed location,then 0019 will b triggered,so tat a custom field should be maintained to trigger a notification 4 the end-user through 0128IT(notifications) with the help of abaper,we have to write dynamic action which include call
- 3. routine prog as well as we maintain step indicator & concerned person's user id in tat. for conformation action: we need to maintain IT0000/01/02/16/19/41...for this, we need to maintain it16/19/41 in intial hiring action of CONTRACT EMPLOYEES mandatarily NUMKR: ON THE basis eeg level...number ranges: reg: temp: contract:more trainees: abkrs:i dont maintain this...as we hav both perm & contract in every ee grp...we'll maintain in 0001 wen we hire an ee pinch:pa/time/payroll...assigned to emp groups and otherwise...blank(us)....will b assigned to company code(india) TIME MAGT ways of creation of holidays: with fixed date 4(Jan 26th, Aug 15th OCt 2nd. Dec 25th) July 4th for US with a fixed day frm date (Good firiday) Colombus day Thanks Giving day for us Boxingday distance from easter easter sunday floating public holiday (Sankranthri PH Class 0-not a public holiday 1-public holiday 2- Halif day PH 3 -9 Custom Specific PH Work Schedule: Clarifies a particular emp going to work in a day for how many working hours break schedules PWS. DWS confirms weather a day is working day for day off, and working hours and breaks.(5 ind) Break Schedule: (4 breaks) Fixed Flexible Dynamic DWS Class Clarifies weather a particular day is working day or day off DWS CLass 0- Day Off DWS Class 1-9 Working Day What r the parameters to define work schedule rule Ans: ES grouping. Holiday Calender ID and PS grouping. SCHKZ feature which is going to default the WsR iN IT 0007 DWS: General shift(GDWS) -> 09:00 - 18:00 BREAKS -> 10:30-10:45, 13:30-14:00, 15:30-15-45 Morning Shift(MDWS) -> 06:00 - 14:00 BREAKS -> 07:30-07:45, 10:30-14:00, 15:30-15:45 Afternoon Shift(ADWS) -> 14:00 - 22:00 BREAKS -> 15:30-15:45, 18:00-18:30, 20:00-20:15
- 4. Night Shift(NDWS) -> 22:00 - 06:00 BREAKS -> 23:30-23:45, 01:30-02:00, 04:00-04:15 Day off(ODWS) -> 0 PWS: General Shift Rotation Shift1:WK1:MRNG WK2:AFTN WK3:NGNT Rotation Shift2:WK1:AFTN WK2:NGNT WK3:MRNG Rotation shift3:WK1:NGNT WK2:MRNG WK3:AFTN Work Schedules rules: GSWSR MSWSR ASWSR NSWSR DAY TYPES 0-WORK/PAID 1-NO WORK/NO PAY 2-NO WORK/PAY 3-CUSTOMER SPECIFIC A)COMPANY ANNIVERSARY DAY,ORPHANAGE CHARITY VISIT, AUDIT TRAIL FOR EVERY THREE MONTHS PS GRPNGS:01 ES GRPNGS:01(MANF STAFF) 02(OTHER STAFF) ABSENCE QUOTAS: ANNUAL LEAVE: 12 DAYS SICK LEAVE: 10 DAYS CASUAL LEAVES: 10 - (INDIA ONLY sCHEMA INFOTYPES CLUSTER TMSTA WITH OUT TE: PRTQTA00 -- -- 0 WITH TE +VE: TM00, TM01 0050, 2011 B2 1 OR 7 RPTIME00 -VE: TM04 2001 B2 9 PROCESSING TYPES: PAIR TYPES: S - PLANNED WORKING HRS 0- not worked not recorded M - OVER TIME 1- worked/ recorded P - WORKING HRS 2- absence with approval K - BREAKS 3- worked @external A - ABSENCE TIME TYPES:
- 5. T555Z T555Y 0090 0094 TIME WAGE TYPE FOR PAYROLL INTEGREATION(M007, M008) T.CODE: SCHEMA/ SUB SCHEMA - PE01 PCR - PE02 OPERATIONS/ FUNCTIONS - PE04 FEATURE - PE03 ATTENDANCE: OVER TIME: TM04(SCHBSCHEMA), TW15(SUB SCHEMA), TO01(PCR FOR CALCULATE OT HRS), TO02(pcr FOR STORE OT HRS) COMP-OFF: PCR- TR11 SCHEMA- TM04 TABLES: T555A/Y/Z The importent operation in to01 pcr: Hrs operation:this operation can be used to store the number of working hours and it can be used to compare other values Varst:this operation can be used to query/retrive general status field from the bankend tables under varst sub oprations:dayty-daytype holcl:holiday class free:daily work schedule off daypg:daily work schedule Curmo: current time evalution period curyr:current year Reday:relative day ofthe time evalution period ADDDB operation: this operation add number of hours to time type The importent operation in to02 pcr: outtp operation:this operation will process time pair imp sub operations:ptype-pair tipe vtype-processing type abtype-absence type prtype-attendence type for possitve time mgt operations: brtype-time event type at start time of time pair ertype-time event type at end time of time pair bterm-begin terminal id eterm-end terminal id Colop operation:this oeration transfer the data from tip to top table whenever i dont wantcaliculation then i will to tip to tip entry
- 6. Gentp operation:seperating time pair data Fillp operation: enter the status and time data for time pair eg:v-processing type m:overtime
- 7. Gentp operation:seperating time pair data Fillp operation: enter the status and time data for time pair eg:v-processing type m:overtime